The Directed Subgraph Homeomorphism Problem*
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Efficient Algorithms with Asymmetric Read and Write Costs
Efficient Algorithms with Asymmetric Read and Write Costs Guy E. Blelloch1, Jeremy T. Fineman2, Phillip B. Gibbons1, Yan Gu1, and Julian Shun3 1 Carnegie Mellon University 2 Georgetown University 3 University of California, Berkeley Abstract In several emerging technologies for computer memory (main memory), the cost of reading is significantly cheaper than the cost of writing. Such asymmetry in memory costs poses a fun- damentally different model from the RAM for algorithm design. In this paper we study lower and upper bounds for various problems under such asymmetric read and write costs. We con- sider both the case in which all but O(1) memory has asymmetric cost, and the case of a small cache of symmetric memory. We model both cases using the (M, ω)-ARAM, in which there is a small (symmetric) memory of size M and a large unbounded (asymmetric) memory, both random access, and where reading from the large memory has unit cost, but writing has cost ω 1. For FFT and sorting networks we show a lower bound cost of Ω(ωn logωM n), which indicates that it is not possible to achieve asymptotic improvements with cheaper reads when ω is bounded by a polynomial in M. Moreover, there is an asymptotic gap (of min(ω, log n)/ log(ωM)) between the cost of sorting networks and comparison sorting in the model. This contrasts with the RAM, and most other models, in which the asymptotic costs are the same. We also show a lower bound for computations on an n × n diamond DAG of Ω(ωn2/M) cost, which indicates no asymptotic improvement is achievable with fast reads. -

Tarjan Transcript Final with Timestamps
A.M. Turing Award Oral History Interview with Robert (Bob) Endre Tarjan by Roy Levin San Mateo, California July 12, 2017 Levin: My name is Roy Levin. Today is July 12th, 2017, and I’m in San Mateo, California at the home of Robert Tarjan, where I’ll be interviewing him for the ACM Turing Award Winners project. Good afternoon, Bob, and thanks for spending the time to talk to me today. Tarjan: You’re welcome. Levin: I’d like to start by talking about your early technical interests and where they came from. When do you first recall being interested in what we might call technical things? Tarjan: Well, the first thing I would say in that direction is my mom took me to the public library in Pomona, where I grew up, which opened up a huge world to me. I started reading science fiction books and stories. Originally, I wanted to be the first person on Mars, that was what I was thinking, and I got interested in astronomy, started reading a lot of science stuff. I got to junior high school and I had an amazing math teacher. His name was Mr. Wall. I had him two years, in the eighth and ninth grade. He was teaching the New Math to us before there was such a thing as “New Math.” He taught us Peano’s axioms and things like that. It was a wonderful thing for a kid like me who was really excited about science and mathematics and so on. The other thing that happened was I discovered Scientific American in the public library and started reading Martin Gardner’s columns on mathematical games and was completely fascinated. -

AN/N LOG N ALGORITHM for MINIMIZING STATES in Kf I N ITE AUTOMATON by JOHN HOPCROFT STAN-CS-71-190 January, 1971 COMPUTER SCIENC
AN/N LOG N ALGORITHM FOR MINIMIZING STATES IN kF I N ITE AUTOMATON BY JOHN HOPCROFT STAN-CS-71-190 January, 1971 COMPUTER SCIENCE DEPARTMENT School of Humanities and Sciences STANFORD UN IVERS ITY AN N LOG N ALGORITHM FOR MINIMIZING STATES IN A FINITE AUTOMATON John Hopcroft Abstract An algorithm is given for minimizing the number of states in a finite automaton or for determining if two finite automata are equivalent. The asymptotic running time of the algorithm is bounded by knlogn where k is some constant and n is the number of states. The constant k depends linearly on the size of the input alphabet. This research was supported by the National Science Foundation under grant number NSF-GJ-96, and the Office of Naval Research under grant number N-00014-67-A-0112-0057 NR 044-402. Reproduction in whole or in part is permitted for any purpose of the United States Government. AN n log n ALGORITHM FOR MINIMIZING STATES IN A FINITE AUTOMATON John Hopcroft Stanford University Introduction Most basic texts on finite automata give algorithms for minimizing the number of states in a finite automaton [l, 21. However, a worst case analysis of these algorithms indicate that they are n2 processes where n is the number of states. For finite automata with large numbers of states, these algorithms are grossly inefficient. Thus in this paper we describe an algorithm for minimizing the states in which the asymptotic running time in a worst case analysis grows as n log n . The constant of proportionality depends linearly on the number of input symbols. -

CS Cornell 40Th Anniversary Booklet
Contents Welcome from the CS Chair .................................................................................3 Symposium program .............................................................................................4 Meet the speakers ..................................................................................................5 The Cornell environment The Cornell CS ambience ..............................................................................6 Faculty of Computing and Information Science ............................................8 Information Science Program ........................................................................9 College of Engineering ................................................................................10 College of Arts & Sciences ..........................................................................11 Selected articles Mission-critical distributed systems ............................................................ 12 Language-based security ............................................................................. 14 A grand challenge in computer networking .................................................16 Data mining, today and tomorrow ...............................................................18 Grid computing and Web services ...............................................................20 The science of networks .............................................................................. 22 Search engines that learn from experience ..................................................24 -
Alan Mathison Turing and the Turing Award Winners
Alan Turing and the Turing Award Winners A Short Journey Through the History of Computer TítuloScience do capítulo Luis Lamb, 22 June 2012 Slides by Luis C. Lamb Alan Mathison Turing A.M. Turing, 1951 Turing by Stephen Kettle, 2007 by Slides by Luis C. Lamb Assumptions • I assume knowlege of Computing as a Science. • I shall not talk about computing before Turing: Leibniz, Babbage, Boole, Gödel... • I shall not detail theorems or algorithms. • I shall apologize for omissions at the end of this presentation. • Comprehensive information about Turing can be found at http://www.mathcomp.leeds.ac.uk/turing2012/ • The full version of this talk is available upon request. Slides by Luis C. Lamb Alan Mathison Turing § Born 23 June 1912: 2 Warrington Crescent, Maida Vale, London W9 Google maps Slides by Luis C. Lamb Alan Mathison Turing: short biography • 1922: Attends Hazlehurst Preparatory School • ’26: Sherborne School Dorset • ’31: King’s College Cambridge, Maths (graduates in ‘34). • ’35: Elected to Fellowship of King’s College Cambridge • ’36: Publishes “On Computable Numbers, with an Application to the Entscheindungsproblem”, Journal of the London Math. Soc. • ’38: PhD Princeton (viva on 21 June) : “Systems of Logic Based on Ordinals”, supervised by Alonzo Church. • Letter to Philipp Hall: “I hope Hitler will not have invaded England before I come back.” • ’39 Joins Bletchley Park: designs the “Bombe”. • ’40: First Bombes are fully operational • ’41: Breaks the German Naval Enigma. • ’42-44: Several contibutions to war effort on codebreaking; secure speech devices; computing. • ’45: Automatic Computing Engine (ACE) Computer. Slides by Luis C. -

Prof. John Hopcroft
静园 号院 前沿讲座 2 0 1 9 年第01号 An Introduction to AI and Deep Learning Prof. John Hopcroft 2019年1月19日 星期六 10:30-11:30 北京大学静园五院101 Abstract A major advance in AI occurred in 2012 when AlexNet won the ImageNet competition with a deep network. The success was sufficiently better than previous years that deep networks were applied in many applications with great success. However, there is little understanding of why deep learning works. This talk will give an introduction to machine learning and then illustrate current research directions in deep learning at a level for a general scientific audience. Biography John E. Hopcroft is the IBM Professor of Engineering and Applied Mathematics in Computer Science at Cornell University, and the Director of Center on Frontiers of Computing Studies at Peking University. From January 1994 until June 2001, he was the Joseph Silbert Dean of Engineering. After receiving both his M.S. and Ph.D. in electrical engineering from Stanford University, he spent three years on the faculty of Princeton University. He joined the Cornell faculty in 1967, was named professor in 1972 and the Joseph C. Ford Professor of Computer Science in 1985. He served as chairman of the Department of Computer Science from 1987 to 1992 and was the associate dean for college affairs in 1993. An undergraduate alumnus of Seattle University, Hopcroft was honored with a Doctor of Humanities Degree, Honoris Causa, in 1990. Hopcroft's research centers on theoretical aspects of computing, especially analysis of algorithms, automata theory, and graph algorithms. He has coauthored four books on formal languages and algorithms with Jeffrey D. -
A Self-Adjusting Search Tree
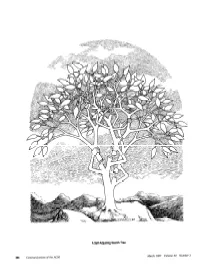
A Self-Adjusting Search Tree March 1987 Volume 30 Number 3 204 Communications of ifhe ACM WfUNGAWARD LECTURE ALGORITHM DESIGN The quest for efficiency in computational methods yields not only fast algorithms, but also insights that lead to elegant, simple, and general problem-solving methods. ROBERTE. TARJAN I was surprised and delighted to learn of my selec- computations and to design data structures that ex- tion as corecipient of the 1986 Turing Award. My actly represent the information needed to solve the delight turned to discomfort, however, when I began problem. If this approach is successful, the result is to think of the responsibility that comes with this not only an efficient algorithm, but a collection of great honor: to speak to the computing community insights and methods extracted from the design on some topic of my own choosing. Many of my process that can be transferred to other problems. friends suggested that I preach a sermon of some Since the problems considered by theoreticians are sort, but as I am not the preaching kind, I decided generally abstractions of real-world problems, it is just to share with you some thoughts about the these insights and general methods that are of most work I do and its relevance to the real world of value to practitioners, since they provide tools that computing. can be used to build solutions to real-world problems. Most of my research deals with the design and I shall illustrate algorithm design by relating the analysis of efficient computer algorithms. The goal historical contexts of two particular algorithms. -

Global Young Scientists Summit
GLOBAL YOUNG SCIENTISTS SUMMIT 2020 HIGHLIGHTS 3 GYSS 2020 6 PROGRAMME 30 YOUNG SCIENTISTS 34 SPEAKERS 38 GYSS COMMUNITY 2 // Global Young Scientists Summit 2020 3 // An international gathering of bright young researchers from all over the world in Singapore, who are mentored by award-winning scientists // Sparking conversations on the latest advances in science and technology, and how research can develop solutions to address major global challenges // Multi-disciplinary event covering the disciplines of chemistry, physics, biology, mathematics, computer science and engineering // Held from 14-17 January 2020 GYSS 2020 16 320 EMINENT SPEAKERS YOUNG SCIENTISTS 100 2 POSTERS PRESENTED PUBLIC LECTURES 4 // Global Young Scientists Summit 2020 5 PLENARY LECTURES // Speakers shared stories of their prize-winning discoveries PANEL DISCUSSIONS // Scientific leaders discussed thought-provoking issues of today, such as the future of medicine and science and society SMALL GROUP SESSIONS // Young scientists had the opportunity to be mentored by eminent scientists on more personal topics, such as their scientific careers PROGRAMME POSTER SESSION // Participants showcased their research projects, sparking interactions and conversations with peers on potential collaborations SITE VISITS // Visits to local universities and research institutes offered insight into Singapore’s research landscape PUBLIC LECTURES // Held all around Singapore, these lectures gave students and members of the public the chance to hear from eminent scientists 6 // Global Young -

Ron Rivest 2002 Recipient of the ACM Turing Award
Ron Rivest 2002 recipient of the ACM Turing Award Interviewed by: Roy Levin December 6, 2016 Mountain View, CA The production of this video was a joint project between the ACM and the Computer History Museum © 2016 ACM and Computer History Museum Oral History of Ron Rivest Levin: My name is Roy Levin, today is December 6th, 2016, and I’m at the Computer History Museum in Mountain View, California, where I will be interviewing Ron Rivest for the ACM’s Turing Award Winners Project. Good afternoon Ron, and thanks for taking the time to speak with me today. Rivest: Good afternoon. Levin: I want to start by talking about your background, and how you got into computing. When did you first get interested in computing? Rivest: Interesting story. So I grew up in Schenectady, New York, where my dad was an electrical engineer working at GE Research Labs, and in a suburb called Niskayuna, which is sort of a high-tech suburb of Schenectady. And they had a lot of interesting classes, both within the school and after school, and one of the classes I took, probably as a junior, was a computer programming class, back in about 1964, from a fellow that worked at the GE Research Labs -- I think his name was Marv Allison, who taught it. And he had a programming language he’d invented, and wanted to teach to the local high school students. And so he would come after high school, and we would sit around and hear about computer programming, and get these sheets, you know, with the marked squares for the letters, and write a program. -

The Halting Problem and Security's Language-Theoretic Approach
Computability Pre-press (2021) 1–18; The final publication is available at IOS Press through http://dx.doi.org/10.3233/COM-180217 1 IOS Press 1 1 2 2 3 The Halting Problem and Security’s Language-Theoretic Approach: 3 4 4 5 Praise and Criticism from a Technical Historian 5 6 6 ∗ 7 Edgar G. Daylight 7 8 School of Media and Information, Siegen University, Herrengarten 3, 57072 Siegen, 8 9 Germany 9 10 [email protected] 10 11 11 12 Abstract. The term ‘Halting Problem’ arguably refers to computer science’s most celebrated impossibility result and to the 12 core notion underlying the language-theoretic approach to security. Computer professionals often ignore the Halting Problem 13 13 however. In retrospect, this is not too surprising given that several advocates of computability theory implicitly follow Christopher 14 14 Strachey’s alleged 1965 proof of his Halting Problem (which is about executable — i.e., hackable — programs) rather than Martin 15 Davis’s correct 1958 version or his 1994 account (each of which is solely about mathematical objects). For the sake of conceptual 15 16 clarity, particularly for researchers pursuing a coherent science of cybersecurity, I will scrutinize Strachey’s 1965 line of reasoning 16 17 — which is widespread today — both from a charitable, historical angle and from a critical, engineering perspective. 17 18 18 19 Keywords: undecidability, halting problem, security, computability theory, Internet of Things 19 20 20 21 1. Introduction 21 22 Wireless networks, sensors, and software are transforming our societies into an Internet of Things. We are start- 22 23 ing to use Internet-connected drones, self-driving cars, and pacemakers designed to facilitate long-distance patient 23 24 monitoring by doctors. -

Award Recipients with Citations
IEEE JOHN VON NEUMANN MEDAL RECIPIENTS 2020 MICHAEL I. JORDAN “For contributions to machine learning and Professor, University of California, data science.” Berkeley, California, USA 2019 EVA TARDOS “For contributions to the field of algorithms, Jacob Gould Schurman Professor of including foundational new methods in Computer Science, Cornell optimization, approximation algorithms, and University, Ithaca, New York, USA algorithmic game theory.” 2018 PATRICK COUSOT “For introducing abstract interpretation, a Professor, New York University, powerful framework for automatically New York, New York, USA calculating program properties with broad application to verification and optimization.” 2017 VLADIMIR VAPNIK “For the development of statistical learning Professor, Columbia University and theory, the theoretical foundations for Facebook AI Research, New York, machine learning, and support vector New York, USA machines.” 2016 CHRISTOS HARILAOS "For providing a deeper understanding of PAPADIMITRIOU computational complexity and its implications Professor, University of California, for approximation algorithms, artificial Berkeley, Berkeley, California, USA intelligence, economics, database theory, and biology." 2015 JAMES A. GOSLING “For the Java programming language, Java Chief Software Architect, Liquid Virtual Machine, and other contributions to Robotics, Redwood, California, USA programming languages and environments.” 2014 CLEVE MOLER “For fundamental and widely used Chief Mathematician, MathWorks, contributions to numerical linear algebra -

Modularity Conserved During Evolution: Algorithms and Analysis
Modularity Conserved during Evolution: Algorithms and Analysis Luqman Hodgkinson Electrical Engineering and Computer Sciences University of California at Berkeley Technical Report No. UCB/EECS-2015-17 http://www.eecs.berkeley.edu/Pubs/TechRpts/2015/EECS-2015-17.html May 1, 2015 Copyright © 2015, by the author(s). All rights reserved. Permission to make digital or hard copies of all or part of this work for personal or classroom use is granted without fee provided that copies are not made or distributed for profit or commercial advantage and that copies bear this notice and the full citation on the first page. To copy otherwise, to republish, to post on servers or to redistribute to lists, requires prior specific permission. Acknowledgement This thesis presents joint work with several collaborators at Berkeley. The work on algorithm design and analysis is joint work with Richard M. Karp, the work on reproducible computation is joint work with Eric Brewer and Javier Rosa, and the work on visualization of modularity is joint work with Nicholas Kong. I thank all of them for their contributions. They have been pleasant collaborators with stimulating ideas and good designs. Our descriptions of the projects in this thesis overlap somewhat with our published descriptions in [Hodgkinson and Karp, 2011a], [Hodgkinson and Karp, 2011b], [Hodgkinson and Karp, 2012], and [Hodgkinson et al., 2012]. Modularity Conserved during Evolution: Algorithms and Analysis by Luqman Hodgkinson B.A. Hon. (Hiram College) 2003 M.S. (Columbia University) 2007 A dissertation submitted in partial satisfaction of the requirements for the degree of Doctor of Philosophy in Computer Science with Designated Emphasis in Computational and Genomic Biology in the GRADUATE DIVISION of the UNIVERSITY OF CALIFORNIA, BERKELEY Committee in charge: Professor Richard M.