Breaking the X86 ISA (PDF)
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
A Superscalar Out-Of-Order X86 Soft Processor for FPGA
A Superscalar Out-of-Order x86 Soft Processor for FPGA Henry Wong University of Toronto, Intel [email protected] June 5, 2019 Stanford University EE380 1 Hi! ● CPU architect, Intel Hillsboro ● Ph.D., University of Toronto ● Today: x86 OoO processor for FPGA (Ph.D. work) – Motivation – High-level design and results – Microarchitecture details and some circuits 2 FPGA: Field-Programmable Gate Array ● Is a digital circuit (logic gates and wires) ● Is field-programmable (at power-on, not in the fab) ● Pre-fab everything you’ll ever need – 20x area, 20x delay cost – Circuit building blocks are somewhat bigger than logic gates 6-LUT6-LUT 6-LUT6-LUT 3 6-LUT 6-LUT FPGA: Field-Programmable Gate Array ● Is a digital circuit (logic gates and wires) ● Is field-programmable (at power-on, not in the fab) ● Pre-fab everything you’ll ever need – 20x area, 20x delay cost – Circuit building blocks are somewhat bigger than logic gates 6-LUT 6-LUT 6-LUT 6-LUT 4 6-LUT 6-LUT FPGA Soft Processors ● FPGA systems often have software components – Often running on a soft processor ● Need more performance? – Parallel code and hardware accelerators need effort – Less effort if soft processors got faster 5 FPGA Soft Processors ● FPGA systems often have software components – Often running on a soft processor ● Need more performance? – Parallel code and hardware accelerators need effort – Less effort if soft processors got faster 6 FPGA Soft Processors ● FPGA systems often have software components – Often running on a soft processor ● Need more performance? – Parallel -

SIMD Extensions
SIMD Extensions PDF generated using the open source mwlib toolkit. See http://code.pediapress.com/ for more information. PDF generated at: Sat, 12 May 2012 17:14:46 UTC Contents Articles SIMD 1 MMX (instruction set) 6 3DNow! 8 Streaming SIMD Extensions 12 SSE2 16 SSE3 18 SSSE3 20 SSE4 22 SSE5 26 Advanced Vector Extensions 28 CVT16 instruction set 31 XOP instruction set 31 References Article Sources and Contributors 33 Image Sources, Licenses and Contributors 34 Article Licenses License 35 SIMD 1 SIMD Single instruction Multiple instruction Single data SISD MISD Multiple data SIMD MIMD Single instruction, multiple data (SIMD), is a class of parallel computers in Flynn's taxonomy. It describes computers with multiple processing elements that perform the same operation on multiple data simultaneously. Thus, such machines exploit data level parallelism. History The first use of SIMD instructions was in vector supercomputers of the early 1970s such as the CDC Star-100 and the Texas Instruments ASC, which could operate on a vector of data with a single instruction. Vector processing was especially popularized by Cray in the 1970s and 1980s. Vector-processing architectures are now considered separate from SIMD machines, based on the fact that vector machines processed the vectors one word at a time through pipelined processors (though still based on a single instruction), whereas modern SIMD machines process all elements of the vector simultaneously.[1] The first era of modern SIMD machines was characterized by massively parallel processing-style supercomputers such as the Thinking Machines CM-1 and CM-2. These machines had many limited-functionality processors that would work in parallel. -
Operating Guide
Operating Guide EPIA-P830 Mainboard EPIA-P830 Operating Guide Table of Contents Table of Contents .......................................................................................................................................................................................... i VIA EPIA-P830 overview.............................................................................................................................................................................1 VIA EPIA-P830 layout ..................................................................................................................................................................................2 VIA EPIA-P830 specifications ...................................................................................................................................................................3 VIA EPIA-P830 processor SKUs ...............................................................................................................................................................4 VIA VX900 chipset overview.....................................................................................................................................................................5 VIA EPIA-P830 and P830-A board dimensions.................................................................................................................................6 VIA P830-B board dimensions.................................................................................................................................................................7 -

Apparecchiature Medicali: Il Ruolo Delle Nanotecnologie
EO Medical APPAreCCHIAture MeDICALI: IL ruoLo DeLLe NANoteCNoLoGIe IN queSto NuMero III Mercati/Attualità VIII Stanford, in fase di sviluppo una ‘pelle elettronica’ X Dialisi direttamente a casa XII Affrontare richieste ad alte prestazioni per la visualizzazione di immagini mediche XIV Criteri di scelta per alimentatori conformi a Iec60601-1 3a edizione XVII News Foto: Future Electronics Murata MEMS Solutions for Medical and Healthcare Enabling MEMS Sensing Improved Care Elements (Dies) SCG12S and SCG14S In medical and healthcare applications Vertical Accelerometer Elements (Dies) Murata’s medical MEMS sensors enable • Size 3mm x 2.12mm x 1.95 or 1.25mm • Various measuring ranges possible (1 - 12g) improved care and a better quality of life • Proven capacitive 3D-MEMS Technology for patients and elderly people. Medical sensors increase the intelligence of life supporting SCG10X and SCG10Z Horizontal Accelerometer Elements (Dies) transplants, and they can be used in new types of patient • Size SCG10X: 2.55mm x 2.95mm x 1.91mm monitoring applications that allow patients to lead more • Size SCG10Z: 1.50mm x 1.70mm x 1.83mm independent lives. Detecting signals triggered by symptoms • Various measuring ranges possible (1 - 12g) • Proven capacitive 3D-MEMS Technology helps optimize medication and prevent serious attacks of illness. Murata’s unique MEMS design, which combines single SCB10H crystal silicon and glass, ensures exceptional reliability, Pressure Sensor Elements (Dies) unprecedented accuracy and excellent stability over time. The • Size 1.4mm x 1.4mm x 0.85mm • High pressure shock survival (> 200 bar) power requirements of these medical sensors are extremely • Various pressure ranges possible (1.2 - 25 bar) low, which gives them a significant advantage in small • Proven capacitive 3D-MEMS technology battery-operated devices. -

Professor Won Woo Ro, School of Electrical and Electronic Engineering Yonsei University the Intel® 4004 Microprocessor, Introdu
Professor Won Woo Ro, School of Electrical and Electronic Engineering Yonsei University The 1st Microprocessor The Intel® 4004 microprocessor, introduced in November 1971 An electronics revolution that changed our world. There were no customer‐ programmable microprocessors on the market before the 4004. It propelled software into the limelight as a key player in the world of digital electronics design. 4004 Microprocessor Display at New Intel Museum A Japanese calculator maker (Busicom) asked to design: A set of 12 custom logic chips for a line of programmable calculators. Marcian E. "Ted" Hoff Recognized the integrated circuit technology (of the day) had advanced enough to build a single chip, general purpose computer. Federico Faggin to turn Hoff's vision into a silicon reality. (In less than one year, Faggin and his team delivered the 4004, which was introduced in November, 1971.) The world's first microprocessor application was this Busicom calculator. (sold about 100,000 calculators.) Measuring 1/8 inch wide by 1/6 inch long, consisting of 2,300 transistors, Intel’s 4004 microprocessor had as much computing power as the first electronic computer, ENIAC. 2 inch 4004 and 12 inch Core™2 Duo wafer ENIAC, built in 1946, filled 3000‐cubic‐ feet of space and contained 18,000 vacuum tubes. The 4004 microprocessor could execute 60,000 operations per second Running frequency: 108 KHz Founders wanted to name their new company Moore Noyce. However the name sounds very much similar to “more noise”. "Only the paranoid survive". Moore received a B.S. degree in Chemistry from the University of California, Berkeley in 1950 and a Ph.D. -
Multiprocessing Contents
Multiprocessing Contents 1 Multiprocessing 1 1.1 Pre-history .............................................. 1 1.2 Key topics ............................................... 1 1.2.1 Processor symmetry ...................................... 1 1.2.2 Instruction and data streams ................................. 1 1.2.3 Processor coupling ...................................... 2 1.2.4 Multiprocessor Communication Architecture ......................... 2 1.3 Flynn’s taxonomy ........................................... 2 1.3.1 SISD multiprocessing ..................................... 2 1.3.2 SIMD multiprocessing .................................... 2 1.3.3 MISD multiprocessing .................................... 3 1.3.4 MIMD multiprocessing .................................... 3 1.4 See also ................................................ 3 1.5 References ............................................... 3 2 Computer multitasking 5 2.1 Multiprogramming .......................................... 5 2.2 Cooperative multitasking ....................................... 6 2.3 Preemptive multitasking ....................................... 6 2.4 Real time ............................................... 7 2.5 Multithreading ............................................ 7 2.6 Memory protection .......................................... 7 2.7 Memory swapping .......................................... 7 2.8 Programming ............................................. 7 2.9 See also ................................................ 8 2.10 References ............................................. -
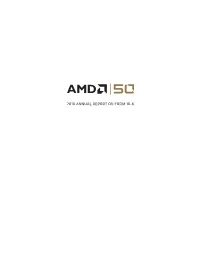
2018 Annual Report on Form 10-K
2018 ANNUAL REPORT ON FORM 10-K MARCH 2019 DEAR SHAREHOLDERS: From the industry’s first 1GHz CPU to the world’s first GPU delivering a teraflop of computing power, AMD has always stood for pushing the boundaries of what is possible. A few years ago, we made several big bets to accelerate our pace of innovation, strengthen our execution, and enable AMD to deliver a leadership portfolio of computing and graphics processors capable of increasing our share of the $75 billion high-performance computing market. In 2018, we saw those bets begin to pay off as we delivered our second straight year of greater than 20% annual revenue growth and significantly improved our gross margin and profitability from the previous year. REVENUE GROSS MARGIN % R&D INVESTMENT EXPENSE/REVENUE % $ Billions $ Billions $6.5B 38% $1.43B 34% $5.3B 34% 33% $4.3B $1.20B 23% $1.01B 31% 2016 2017 2018 2016 2017 2018 2016 2017 2018 2016 2017 2018 Added $2.2B in revenue Significantly improved gross Increased R&D by more than Significant improvement over the last 2 years margin over last 2 years based 40% over the last 2 years in OPEX leverage on new product portfolio Our newest Ryzen™, EPYC™ and datacenter GPU products contributed more than $1.2 billion of revenue in 2018 and helped us gain share across our priority markets. In 2018, we added 3.9% points of desktop processor unit share, 5.3% points of notebook processor unit share and met our goal of exiting the year with mid-single digit server processor market share. -

J7F3 Mini-ITX Motherboard Series
Mainboard Diagram J7F3 Mini-ITX Motherboard Series -SiS 741CX Northbridge + SiS 964 Southbridge Chipsets -Support Socket-462 AMD Geode NX processor -Support Front Side Bus 133MHz -Single Channel DDR2 400 Memory DIMM -Support 2 Serial ATA Devices with RAID 0, 1 -Support 2xAD Connector With Expansion Daughter-boards -Ethernet LAN Supported -AC’97 6 Channel Audio CODEC -VIA VT6307S IEEE1394a Controller for J7F3E -17 x 17CM Mini-ITX Form Factor Features and Benefits Support Socket 462 AMD Geode™ NX Processor The AMD Geode™ NX processor family gives product designers a wide range of options in low-power, high-performance processors. Based on Mobile AMD Athlon™ processor technology, AMD NX processors deliver superior computing performance for applications including thin-client, point-of-sale terminals, kiosks, high-end printers, and home media systems. AMD Geode Solutions have received new model numbers to better reflect total performance beyond just megahertz. This presentation of attributes gives designers greater understanding of the capabilities of AMD Geode Solutions. SiS 741CX Northbridge Chipset and SiS964 Southbridge Chipset The SiS741CX chipset can be combined with three different AMD Geode NX processors, including the AMD Geode™ NX 1250@6W processor*, AMD Geode™ NX 1500@6W processor** and AMD Geode™ NX 1750@14W processor***, enabling development of a wider variety of products for different market segments. The SiS741CX chipset supports the AMD Geode NX processor family, DDR266 front side bus, as well as high-speed DDR333 DRAM. Furthermore, the SiS741CX chipset incorporates SiS's revolutionary HyperStreaming™ Technology, which provides multiple divided pipelines for data, allows data to be sent concurrently, and separates data for easier memory retrieval, resulting in a remarkable reduction in latency versus traditional chipsets. -

Communication Theory II
Microprocessor (COM 9323) Lecture 2: Review on Intel Family Ahmed Elnakib, PhD Assistant Professor, Mansoura University, Egypt Feb 17th, 2016 1 Text Book/References Textbook: 1. The Intel Microprocessors, Architecture, Programming and Interfacing, 8th edition, Barry B. Brey, Prentice Hall, 2009 2. Assembly Language for x86 processors, 6th edition, K. R. Irvine, Prentice Hall, 2011 References: 1. Computer Architecture: A Quantitative Approach, 5th edition, J. Hennessy, D. Patterson, Elsevier, 2012. 2. The 80x86 Family, Design, Programming and Interfacing, 3rd edition, Prentice Hall, 2002 3. The 80x86 IBM PC and Compatible Computers, Assembly Language, Design, and Interfacing, 4th edition, M.A. Mazidi and J.G. Mazidi, Prentice Hall, 2003 2 Lecture Objectives 1. Provide an overview of the various 80X86 and Pentium family members 2. Define the contents of the memory system in the personal computer 3. Convert between binary, decimal, and hexadecimal numbers 4. Differentiate and represent numeric and alphabetic information as integers, floating-point, BCD, and ASCII data 5. Understand basic computer terminology (bit, byte, data, real memory system, protected mode memory system, Windows, DOS, I/O) 3 Brief History of the Computers o1946 The first generation of Computer ENIAC (Electrical and Numerical Integrator and Calculator) was started to be used based on the vacuum tube technology, University of Pennsylvania o1970s entire CPU was put in a single chip. (1971 the first microprocessor of Intel 4004 (4-bit data bus and 2300 transistors and 45 instructions) 4 Brief History of the Computers (cont’d) oLate 1970s Intel 8080/85 appeared with 8-bit data bus and 16-bit address bus and used from traffic light controllers to homemade computers (8085: 246 instruction set, RISC*) o1981 First PC was introduced by IBM with Intel 8088 (CISC**: over 20,000 instructions) microprocessor oMotorola emerged with 6800. -

Evolution Des X86befehlssatzes Und Seiner Erweiterungen
Technische Universität Dresden Evolution des x86-Befehlssatzes und seiner Erweiterungen Peter Ebert Dresden, 15.07.2009 Einführung · Überblick & Historie · Konkurrierende Befehlssatzarchitekture n · Befehlsarten · Registerstruktur · x87 15.07.2009 Evolution des x86-Befehlssatzes und seiner Erweiterungen 2/24 Übersicht & Historie · IBM 1981: erster PC · x86-Architektur verwendet einen CISC-Befehlssatz · alle Prozessoren seit dem Pentium Pro sind aber hybride CISC/RISC-Prozessoren 1978 1. Gen.: 8086 1982 2. Gen.: 80286 1985 3. Gen.: 80386 IA-32 1989 4. Gen.: 80486 1993 5. Gen.: Pentium MMX 1995 6. Gen.: P2, P3 3DNow!, SSE 1999 7. Gen.: Athlon (XP), P4 SSE2 2003 8. Gen.: Opteron x86-64 15.07.2009 Evolution des x86-Befehlssatzes und seiner Erweiterungen 3/24 Konkurrierende Befehlssatzarchitekturen · ARM (Acorn Risc Machine) RISC-Architektur 1983 vom englischen Computerhersteller Acorn. Einsatz vor allem im eingebetteten Bereich z.B.: Mobiltelefonen, PDAs, Routern, iPod, iPhone, Internet Tablets von Nokia und den neueren PDAs von ASUS, Konsolen wie der Nintendo DS, der GP2X und die Pandora. · PowerPC (Performance optimization with enhanced RISC Performance Chip) 1991 durch ein Konsortium aus Apple, IBM und Motorola. z.B.: Nintendo GameCube und Wii, Xbox 360 von Microsoft, Playstation 3 von Sony und in vielen eingebetteten Systemen. Auch benutzen PKW und Produkte in der Luft- und Raumfahrt · SPARC (Scalable Processor ARChitecture) Von Sun Microsystems entwickelt ab 1985 und vermarktete ab 1987, offene Architektur, 1995 64-Bit-Erweiterung (UltraSparc) 15.07.2009 Evolution des x86-Befehlssatzes und seiner Erweiterungen 4/24 Befehlsarten · Transferbefehlen werden Daten innerhalb des Systems bewegt. Die Daten werden dabei nur kopiert, d. h. bleiben an ihrem Quellort unverändert. -

Computer Architectures an Overview
Computer Architectures An Overview PDF generated using the open source mwlib toolkit. See http://code.pediapress.com/ for more information. PDF generated at: Sat, 25 Feb 2012 22:35:32 UTC Contents Articles Microarchitecture 1 x86 7 PowerPC 23 IBM POWER 33 MIPS architecture 39 SPARC 57 ARM architecture 65 DEC Alpha 80 AlphaStation 92 AlphaServer 95 Very long instruction word 103 Instruction-level parallelism 107 Explicitly parallel instruction computing 108 References Article Sources and Contributors 111 Image Sources, Licenses and Contributors 113 Article Licenses License 114 Microarchitecture 1 Microarchitecture In computer engineering, microarchitecture (sometimes abbreviated to µarch or uarch), also called computer organization, is the way a given instruction set architecture (ISA) is implemented on a processor. A given ISA may be implemented with different microarchitectures.[1] Implementations might vary due to different goals of a given design or due to shifts in technology.[2] Computer architecture is the combination of microarchitecture and instruction set design. Relation to instruction set architecture The ISA is roughly the same as the programming model of a processor as seen by an assembly language programmer or compiler writer. The ISA includes the execution model, processor registers, address and data formats among other things. The Intel Core microarchitecture microarchitecture includes the constituent parts of the processor and how these interconnect and interoperate to implement the ISA. The microarchitecture of a machine is usually represented as (more or less detailed) diagrams that describe the interconnections of the various microarchitectural elements of the machine, which may be everything from single gates and registers, to complete arithmetic logic units (ALU)s and even larger elements. -
SMBIOS Specification
1 2 Document Identifier: DSP0134 3 Date: 2019-10-31 4 Version: 3.4.0a 5 System Management BIOS (SMBIOS) Reference 6 Specification Information for Work-in-Progress version: IMPORTANT: This document is not a standard. It does not necessarily reflect the views of the DMTF or its members. Because this document is a Work in Progress, this document may still change, perhaps profoundly and without notice. This document is available for public review and comment until superseded. Provide any comments through the DMTF Feedback Portal: http://www.dmtf.org/standards/feedback 7 Supersedes: 3.3.0 8 Document Class: Normative 9 Document Status: Work in Progress 10 Document Language: en-US 11 System Management BIOS (SMBIOS) Reference Specification DSP0134 12 Copyright Notice 13 Copyright © 2000, 2002, 2004–2019 DMTF. All rights reserved. 14 DMTF is a not-for-profit association of industry members dedicated to promoting enterprise and systems 15 management and interoperability. Members and non-members may reproduce DMTF specifications and 16 documents, provided that correct attribution is given. As DMTF specifications may be revised from time to 17 time, the particular version and release date should always be noted. 18 Implementation of certain elements of this standard or proposed standard may be subject to third party 19 patent rights, including provisional patent rights (herein "patent rights"). DMTF makes no representations 20 to users of the standard as to the existence of such rights, and is not responsible to recognize, disclose, 21 or identify any or all such third party patent right, owners or claimants, nor for any incomplete or 22 inaccurate identification or disclosure of such rights, owners or claimants.