Analysis of the I2P Network Information Gathering and Attack Evaluations
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Cryptography
56 Protecting Information With Cryptography Chapter by Peter Reiher (UCLA) 56.1 Introduction In previous chapters, we’ve discussed clarifying your security goals, determining your security policies, using authentication mechanisms to identify principals, and using access control mechanisms to enforce poli- cies concerning which principals can access which computer resources in which ways. While we identified a number of shortcomings and prob- lems inherent in all of these elements of securing your system, if we re- gard those topics as covered, what’s left for the operating system to worry about, from a security perspective? Why isn’t that everything? There are a number of reasons why we need more. Of particular im- portance: not everything is controlled by the operating system. But per- haps you respond, you told me the operating system is all-powerful! Not really. It has substantial control over a limited domain – the hardware on which it runs, using the interfaces of which it is given control. It has no real control over what happens on other machines, nor what happens if one of its pieces of hardware is accessed via some mechanism outside the operating system’s control. But how can we expect the operating system to protect something when the system does not itself control access to that resource? The an- swer is to prepare the resource for trouble in advance. In essence, we assume that we are going to lose the data, or that an opponent will try to alter it improperly. And we take steps to ensure that such actions don’t cause us problems. -

A Generic Data Exchange System for F2F Networks
The Retroshare project The GXS system Decentralize your app! A Generic Data Exchange System for F2F Networks Cyril Soler C.Soler The GXS System 03 Feb. 2018 1 / 19 The Retroshare project The GXS system Decentralize your app! Outline I Overview of Retroshare I The GXS system I Decentralize your app! C.Soler The GXS System 03 Feb. 2018 2 / 19 The Retroshare project The GXS system Decentralize your app! The Retroshare Project I Mesh computers using signed TLS over TCP/UDP/Tor/I2P; I anonymous end-to-end encrypted FT with swarming; I mail, IRC chat, forums, channels; I available on Mac OS, Linux, Windows, (+ Android). C.Soler The GXS System 03 Feb. 2018 3 / 19 The Retroshare project The GXS system Decentralize your app! The Retroshare Project I Mesh computers using signed TLS over TCP/UDP/Tor/I2P; I anonymous end-to-end encrypted FT with swarming; I mail, IRC chat, forums, channels; I available on Mac OS, Linux, Windows. C.Soler The GXS System 03 Feb. 2018 3 / 19 The Retroshare project The GXS system Decentralize your app! The Retroshare Project I Mesh computers using signed TLS over TCP/UDP/Tor/I2P; I anonymous end-to-end encrypted FT with swarming; I mail, IRC chat, forums, channels; I available on Mac OS, Linux, Windows. C.Soler The GXS System 03 Feb. 2018 3 / 19 The Retroshare project The GXS system Decentralize your app! The Retroshare Project I Mesh computers using signed TLS over TCP/UDP/Tor/I2P; I anonymous end-to-end encrypted FT with swarming; I mail, IRC chat, forums, channels; I available on Mac OS, Linux, Windows. -

IPFS and Friends: a Qualitative Comparison of Next Generation Peer-To-Peer Data Networks Erik Daniel and Florian Tschorsch
1 IPFS and Friends: A Qualitative Comparison of Next Generation Peer-to-Peer Data Networks Erik Daniel and Florian Tschorsch Abstract—Decentralized, distributed storage offers a way to types of files [1]. Napster and Gnutella marked the beginning reduce the impact of data silos as often fostered by centralized and were followed by many other P2P networks focusing on cloud storage. While the intentions of this trend are not new, the specialized application areas or novel network structures. For topic gained traction due to technological advancements, most notably blockchain networks. As a consequence, we observe that example, Freenet [2] realizes anonymous storage and retrieval. a new generation of peer-to-peer data networks emerges. In this Chord [3], CAN [4], and Pastry [5] provide protocols to survey paper, we therefore provide a technical overview of the maintain a structured overlay network topology. In particular, next generation data networks. We use select data networks to BitTorrent [6] received a lot of attention from both users and introduce general concepts and to emphasize new developments. the research community. BitTorrent introduced an incentive Specifically, we provide a deeper outline of the Interplanetary File System and a general overview of Swarm, the Hypercore Pro- mechanism to achieve Pareto efficiency, trying to improve tocol, SAFE, Storj, and Arweave. We identify common building network utilization achieving a higher level of robustness. We blocks and provide a qualitative comparison. From the overview, consider networks such as Napster, Gnutella, Freenet, BitTor- we derive future challenges and research goals concerning data rent, and many more as first generation P2P data networks, networks. -

A Fog Storage Software Architecture for the Internet of Things Bastien Confais, Adrien Lebre, Benoît Parrein
A Fog storage software architecture for the Internet of Things Bastien Confais, Adrien Lebre, Benoît Parrein To cite this version: Bastien Confais, Adrien Lebre, Benoît Parrein. A Fog storage software architecture for the Internet of Things. Advances in Edge Computing: Massive Parallel Processing and Applications, IOS Press, pp.61-105, 2020, Advances in Parallel Computing, 978-1-64368-062-0. 10.3233/APC200004. hal- 02496105 HAL Id: hal-02496105 https://hal.archives-ouvertes.fr/hal-02496105 Submitted on 2 Mar 2020 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. November 2019 A Fog storage software architecture for the Internet of Things Bastien CONFAIS a Adrien LEBRE b and Benoˆıt PARREIN c;1 a CNRS, LS2N, Polytech Nantes, rue Christian Pauc, Nantes, France b Institut Mines Telecom Atlantique, LS2N/Inria, 4 Rue Alfred Kastler, Nantes, France c Universite´ de Nantes, LS2N, Polytech Nantes, Nantes, France Abstract. The last prevision of the european Think Tank IDATE Digiworld esti- mates to 35 billion of connected devices in 2030 over the world just for the con- sumer market. This deep wave will be accompanied by a deluge of data, applica- tions and services. -

PCI Assessment Evidence of PCI Policy Compliance
PCI Assessment Evidence of PCI Policy Compliance CONFIDENTIALITY NOTE: The information contained in this report document is for the Prepared for: exclusive use of the client specified above and may contain confidential, privileged and non-disclosable information. If the recipient of this report is not the client or Prospect or Customer addressee, such recipient is strictly prohibited from reading, photocopying, distributing or otherwise using this report or its contents in any way. Prepared by: Your Company Name Evidence of PCI Policy Compliance PCI ASSESSMENT Table of Contents 1 - Overview 1.1 - Security Officer 1.2 - Overall Risk 2 - PCI DSS Evidence of Compliance 2.1 - Install and maintain firewall to protect cardholder data 2.1.1.1 - Requirements for firewall at each Internet connections and between DMZ and internal network zone 2.1.1.2 - Business justification for use of all services, protocols and ports allowed 2.1.2 - Build firewall and router configurations that restrict connections between untrusted networks and the cardholder data environment 2.1.2.1 - Restrict inbound and outbound to that which is necessary for the cardholder data environment 2.1.2.3 - Do not allow unauthorized outbound traffic from the cardholder data environment to the Internet 2.1.2.4 - Implement stateful inspection (also known as dynamic packet filtering) 2.1.2.5 - Do not allow unauthorized outbound traffic from the cardholder data environment to the Internet 2.2 - Prohibition of vendor-supplied default password for systems and security parameters 2.2.1 -

Self-Encrypting Deception: Weaknesses in the Encryption of Solid State Drives
Self-encrypting deception: weaknesses in the encryption of solid state drives Carlo Meijer Bernard van Gastel Institute for Computing and Information Sciences School of Computer Science Radboud University Nijmegen Open University of the Netherlands [email protected] and Institute for Computing and Information Sciences Radboud University Nijmegen Bernard.vanGastel@{ou.nl,ru.nl} Abstract—We have analyzed the hardware full-disk encryption full-disk encryption. Full-disk encryption software, especially of several solid state drives (SSDs) by reverse engineering their those integrated in modern operating systems, may decide to firmware. These drives were produced by three manufacturers rely solely on hardware encryption in case it detects support between 2014 and 2018, and are both internal models using the SATA and NVMe interfaces (in a M.2 or 2.5" traditional form by the storage device. In case the decision is made to rely on factor) and external models using the USB interface. hardware encryption, typically software encryption is disabled. In theory, the security guarantees offered by hardware encryp- As a primary example, BitLocker, the full-disk encryption tion are similar to or better than software implementations. In software built into Microsoft Windows, switches off software reality, we found that many models using hardware encryption encryption and completely relies on hardware encryption by have critical security weaknesses due to specification, design, and implementation issues. For many models, these security default if the drive advertises support. weaknesses allow for complete recovery of the data without Contribution. This paper evaluates both internal and external knowledge of any secret (such as the password). -
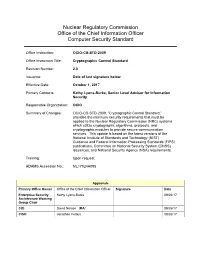
Cryptographic Control Standard, Version
Nuclear Regulatory Commission Office of the Chief Information Officer Computer Security Standard Office Instruction: OCIO-CS-STD-2009 Office Instruction Title: Cryptographic Control Standard Revision Number: 2.0 Issuance: Date of last signature below Effective Date: October 1, 2017 Primary Contacts: Kathy Lyons-Burke, Senior Level Advisor for Information Security Responsible Organization: OCIO Summary of Changes: OCIO-CS-STD-2009, “Cryptographic Control Standard,” provides the minimum security requirements that must be applied to the Nuclear Regulatory Commission (NRC) systems which utilize cryptographic algorithms, protocols, and cryptographic modules to provide secure communication services. This update is based on the latest versions of the National Institute of Standards and Technology (NIST) Guidance and Federal Information Processing Standards (FIPS) publications, Committee on National Security System (CNSS) issuances, and National Security Agency (NSA) requirements. Training: Upon request ADAMS Accession No.: ML17024A095 Approvals Primary Office Owner Office of the Chief Information Officer Signature Date Enterprise Security Kathy Lyons-Burke 09/26/17 Architecture Working Group Chair CIO David Nelson /RA/ 09/26/17 CISO Jonathan Feibus 09/26/17 OCIO-CS-STD-2009 Page i TABLE OF CONTENTS 1 PURPOSE ............................................................................................................................. 1 2 INTRODUCTION .................................................................................................................. -

Unlocking the Fifth Amendment: Passwords and Encrypted Devices
Fordham Law Review Volume 87 Issue 1 Article 9 2018 Unlocking the Fifth Amendment: Passwords and Encrypted Devices Laurent Sacharoff University of Arkansas School of Law, Fayetteville Follow this and additional works at: https://ir.lawnet.fordham.edu/flr Part of the Constitutional Law Commons, and the Criminal Procedure Commons Recommended Citation Laurent Sacharoff, Unlocking the Fifth Amendment: Passwords and Encrypted Devices, 87 Fordham L. Rev. 203 (2018). Available at: https://ir.lawnet.fordham.edu/flr/vol87/iss1/9 This Article is brought to you for free and open access by FLASH: The Fordham Law Archive of Scholarship and History. It has been accepted for inclusion in Fordham Law Review by an authorized editor of FLASH: The Fordham Law Archive of Scholarship and History. For more information, please contact [email protected]. UNLOCKING THE FIFTH AMENDMENT: PASSWORDS AND ENCRYPTED DEVICES Laurent Sacharoff* Each year, law enforcement seizes thousands of electronic devices— smartphones, laptops, and notebooks—that it cannot open without the suspect’s password. Without this password, the information on the device sits completely scrambled behind a wall of encryption. Sometimes agents will be able to obtain the information by hacking, discovering copies of data on the cloud, or obtaining the password voluntarily from the suspects themselves. But when they cannot, may the government compel suspects to disclose or enter their password? This Article considers the Fifth Amendment protection against compelled disclosures of passwords—a question that has split and confused courts. It measures this right against the legal right of law enforcement, armed with a warrant, to search the device that it has validly seized. -

Zeronet Presentation
ZeroNet Decentralized web platform using Bitcoin cryptography and BitTorrent network. ABOUT ZERONET Why? Current features We believe in open, free, and ◦ Real-time updated sites uncensored network and communication. ◦ Namecoin .bit domain support ◦ No hosting costs ◦ Multi-user sites Sites are served by visitors. ◦ Password less, Bitcoin's BIP32- ◦ Impossible to shut down based authorization It's nowhere because it's ◦ Built-in SQL server with P2P data everywhere. synchronization ◦ No single point of failure ◦ Tor network support Site remains online so long as at least 1 peer serving it. ◦ Works in any browser/OS ◦ Fast and works offline You can access the site even if your internet is unavailable. HOW DOES IT WORK? THE BASICS OF ASYMMETRIC CRYPTOGRAPHY When you create a new site you get two keys: Private key Public key 5JNiiGspzqt8sC8FM54FMr53U9XvLVh8Waz6YYDK69gG6hso9xu 16YsjZK9nweXyy3vNQQPKT8tfjCNjEX9JM ◦ Only you have it ◦ This is your site address ◦ Allows you to sign new content for ◦ Using this anyone can verify if the your site. file is created by the site owner. ◦ No central registry ◦ Every downloaded file is verified, It never leaves your computer. makes it safe from malicious code inserts or any modifications. ◦ Impossible to modify your site without it. MORE INFO ABOUT CRYPTOGRAPHY OF ZERONET ◦ ZeroNet uses the same elliptic curve based encryption as in your Bitcoin wallet. ◦ You can accept payments directly to your site address. ◦ Using the current fastest supercomputer, it would take around 1 billion years to "hack" a private key. WHAT HAPPENS WHEN YOU VISIT A ZERONET SITE? WHAT HAPPENS WHEN YOU VISIT A ZERONET SITE? (1/2) 1 Gathering visitors IP addresses: Please send some IP addresses for site 1EU1tbG9oC1A8jz2ouVwGZyQ5asrNsE4Vr OK, Here are some: 12.34.56.78:13433, 42.42.42.42:13411, .. -

Recognition and Investigation of Listening in Anonymous Communication Systems 1 K
AEGAEUM JOURNAL ISSN NO: 0776-3808 Recognition and investigation of listening in anonymous communication systems 1 K. Balasubramanian, 2 Dr. S. Kannan, 3 S. Sharmila 1Associate Professor, Department of CSE, E.G.S Pillay Engineering College, Nagapattinam, Tamil Nadu, India. Email: [email protected] 2, Professor, Department of CSE, E.G.S Pillay Engineering College, Nagapattinam, Tamil Nadu, India. 3, P.G Student, Department of CSE, E.G.S Pillay Engineering College, Nagapattinam, Tamil Nadu, India. Abstract components through which client activity is steered can Mysterious correspondence systems similar to listen in and get delicate information, for example, user Tor, mostly secure the secrecy of client activity by verification qualifications. This circumstance can scrambling all interchanges inside the overlay system. conceivably decline when clients utilize intermediary based frameworks to get to similar administrations However, when the transferred activity achieves the without utilizing end-to-end encryption, as the quantity limits of the system, toward its end, the first client of hosts or hubs that can listen stealthily on their activity is definitely presented to the last node on the movement increments. Different open and private path. Accordingly, users sending sensitive information, systems may square access to interpersonal interaction similar to verification accreditations, over such and other prominent online administrations for systems, risk having their information between different reasons. Under these conditions, users accepted and uncovered, unless end-to-end encryption regularly depend on utilizing disseminated proxying frameworks to prevent their activity from being is utilized. Listening can be performed by malicious or filtered. They fall back on such mechanisms so as to compromised relay nodes, and additionally any rebel evade system activity filtering in light of source, goal, arrange substance on the way toward the actual end. -

Conditional Pseudonymity in Vehicular Ad Hoc Networks
Diplom Thesis Faculty of Engineering and Computer Science Ulm University Conditional Pseudonymity in Vehicular Ad Hoc Networks Florian Marcus Schaub presented on November 13, 2008 Supervisors Prof. Dr.-Ing. Michael Weber Dr. Frank Kargl Advisor Zhendong Ma Faculty of Engineering and Computer Science, Ulm University James-Franck-Ring, 89081 Ulm, Germany This thesis has been prepared in the summer semester 2008 as a requirement for the completion of the Diplom course Medieninformatik at Ulm University. Cover photo: Night blur by Mando Gomez http://www.mandolux.com Printed on November 9, 2008. Some rights reserved. This work is licensed under the Creative Commons Attribution-Noncommercial-No Derivative Works 3.0 Germany License. To view a copy of this license, visit http://creativecommons.org/ licenses/by-nc-nd/3.0/de/ or send a letter to Creative Commons, 171 Second Street, Suite 300, San Francisco, California, 94105, USA. Computer Science is no more about computers than astronomy is about telescopes. Edsger W. Dijkstra Contents 1 Introduction 1 2 Problem Analysis 5 2.1 Characteristics of Vehicular Ad Hoc Networks . 5 2.2 Security and Privacy in Vehicular Ad Hoc Networks . 9 2.3 Conditional Pseudonymity . 14 2.4 Summary . 18 3 Requirements for Privacy in VANETs 19 3.1 Assumptions . 20 3.2 General VANET Requirements . 21 3.3 Pseudonym Requirements . 23 3.4 Authentication Requirements . 28 3.5 Summary . 30 4 Privacy in other Domains 33 4.1 Health Care . 34 4.2 E-Government . 39 4.3 E-Commerce . 43 4.4 Internet . 51 4.5 Ad Hoc Networks . 59 4.6 Summary . -

BRKSEC-2011.Pdf
#CLUS About Garlic and Onions A little journey… Tobias Mayer, Technical Solutions Architect BRKSEC-2011 #CLUS Me… CCIE Security #14390, CISSP & Motorboat driving license… Working in Content Security & TLS Security tmayer{at}cisco.com Writing stuff at “blogs.cisco.com” #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 3 Agenda • Why anonymization? • Using Tor (Onion Routing) • How Tor works • Introduction to Onion Routing • Obfuscation within Tor • Domain Fronting • Detect Tor • I2P – Invisible Internet Project • Introduction to Garlic Routing • Conclusion #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 4 Cisco Webex Teams Questions? Use Cisco Webex Teams (formerly Cisco Spark) to chat with the speaker after the session How 1 Find this session in the Cisco Events App 2 Click “Join the Discussion” 3 Install Webex Teams or go directly to the team space 4 Enter messages/questions in the team space Webex Teams will be moderated cs.co/ciscolivebot#BRKSEC-2011 by the speaker until June 18, 2018. #CLUS © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 5 Different Intentions Hide me from Government! Hide me from ISP! Hide me from tracking! Bypass Corporate Bypass Country Access Hidden policies restrictions (Videos…) Services #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 6 Browser Identity Tracking does not require a “Name” Tracking is done by examining parameters your browser reveals https://panopticlick.eff.org #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 7 Proxies EPIC Browser #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates.