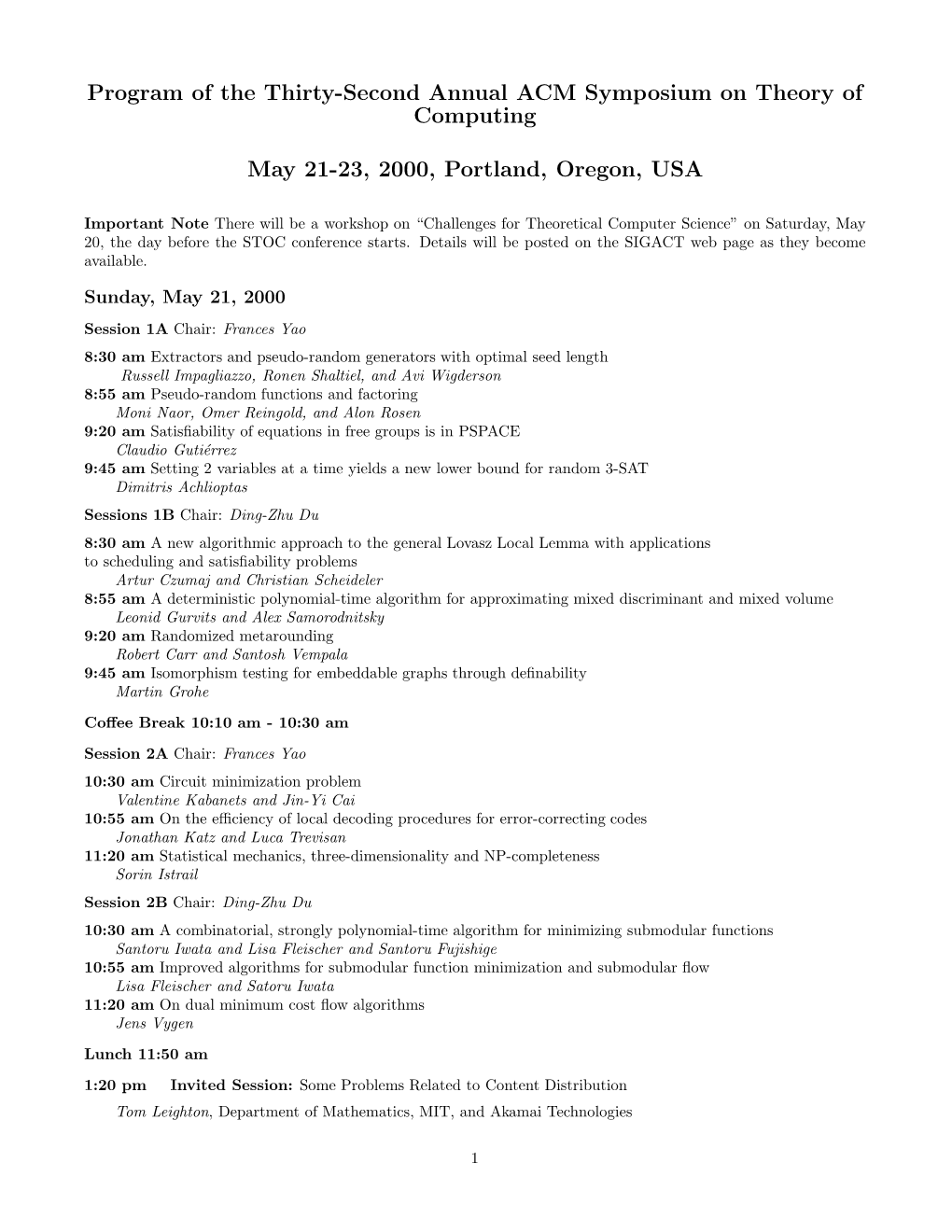
Program of the Thirty-Second Annual ACM Symposium on Theory of Computing
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Challenges in Web Search Engines
Challenges in Web Search Engines Monika R. Henzinger Rajeev Motwani* Craig Silverstein Google Inc. Department of Computer Science Google Inc. 2400 Bayshore Parkway Stanford University 2400 Bayshore Parkway Mountain View, CA 94043 Stanford, CA 94305 Mountain View, CA 94043 [email protected] [email protected] [email protected] Abstract or a combination thereof. There are web ranking optimiza• tion services which, for a fee, claim to place a given web site This article presents a high-level discussion of highly on a given search engine. some problems that are unique to web search en• Unfortunately, spamming has become so prevalent that ev• gines. The goal is to raise awareness and stimulate ery commercial search engine has had to take measures to research in these areas. identify and remove spam. Without such measures, the qual• ity of the rankings suffers severely. Traditional research in information retrieval has not had to 1 Introduction deal with this problem of "malicious" content in the corpora. Quite certainly, this problem is not present in the benchmark Web search engines are faced with a number of difficult prob• document collections used by researchers in the past; indeed, lems in maintaining or enhancing the quality of their perfor• those collections consist exclusively of high-quality content mance. These problems are either unique to this domain, or such as newspaper or scientific articles. Similarly, the spam novel variants of problems that have been studied in the liter• problem is not present in the context of intranets, the web that ature. Our goal in writing this article is to raise awareness of exists within a corporation. -

Adaptive Garbled RAM from Laconic Oblivious Transfer
Adaptive Garbled RAM from Laconic Oblivious Transfer Sanjam Garg?1, Rafail Ostrovsky??2, and Akshayaram Srinivasan1 1 University of California, Berkeley fsanjamg,[email protected] 2 UCLA [email protected] Abstract. We give a construction of an adaptive garbled RAM scheme. In the adaptive setting, a client first garbles a \large" persistent database which is stored on a server. Next, the client can provide garbling of mul- tiple adaptively and adversarially chosen RAM programs that execute and modify the stored database arbitrarily. The garbled database and the garbled program should reveal nothing more than the running time and the output of the computation. Furthermore, the sizes of the garbled database and the garbled program grow only linearly in the size of the database and the running time of the executed program respectively (up to poly logarithmic factors). The security of our construction is based on the assumption that laconic oblivious transfer (Cho et al., CRYPTO 2017) exists. Previously, such adaptive garbled RAM constructions were only known using indistinguishability obfuscation or in random oracle model. As an additional application, we note that this work yields the first constant round secure computation protocol for persistent RAM pro- grams in the malicious setting from standard assumptions. Prior works did not support persistence in the malicious setting. 1 Introduction Over the years, garbling methods [Yao86,LP09,AIK04,BHR12b,App17] have been extremely influential and have engendered an enormous number of applications ? Research supported in part from DARPA/ARL SAFEWARE Award W911NF15C0210, AFOSR Award FA9550-15-1-0274, AFOSR YIP Award, DARPA and SPAWAR under contract N66001-15-C-4065, a Hellman Award and research grants by the Okawa Foundation, Visa Inc., and Center for Long-Term Cybersecurity (CLTC, UC Berkeley). -

Chicago Journal of Theoretical Computer Science the MIT Press
Chicago Journal of Theoretical Computer Science The MIT Press Volume 1997, Article 1 12 March 1997 ISSN 1073–0486. MIT Press Journals, 55 Hayward St., Cambridge, MA 02142 USA; (617)253-2889; [email protected], [email protected]. Published one article at a time in LATEX source form on the Internet. Pag- ination varies from copy to copy. For more information and other articles see: http://www-mitpress.mit.edu/jrnls-catalog/chicago.html • http://www.cs.uchicago.edu/publications/cjtcs/ • ftp://mitpress.mit.edu/pub/CJTCS • ftp://cs.uchicago.edu/pub/publications/cjtcs • Feige and Kilian Limited vs. Polynomial Nondeterminism (Info) The Chicago Journal of Theoretical Computer Science is abstracted or in- R R R dexed in Research Alert, SciSearch, Current Contents /Engineering Com- R puting & Technology, and CompuMath Citation Index. c 1997 The Massachusetts Institute of Technology. Subscribers are licensed to use journal articles in a variety of ways, limited only as required to insure fair attribution to authors and the journal, and to prohibit use in a competing commercial product. See the journal’s World Wide Web site for further details. Address inquiries to the Subsidiary Rights Manager, MIT Press Journals; (617)253-2864; [email protected]. The Chicago Journal of Theoretical Computer Science is a peer-reviewed scholarly journal in theoretical computer science. The journal is committed to providing a forum for significant results on theoretical aspects of all topics in computer science. Editor in chief: Janos Simon Consulting -

(L ,J SEP 3 0 2009 LIBRARIES
Nearest Neighbor Search: the Old, the New, and the Impossible by Alexandr Andoni Submitted to the Department of Electrical Engineering and Computer Science in partial fulfillment of the requirements for the degree of Doctor of Philosophy at the MASSACHUSETTS INSTITUTE OF TECHNOLOGY September 2009 © Massachusetts Institute of Technology 2009. All rights reserved. Author .............. .. .. ......... .... ..... ... ......... ....... Department of Electrical Engineering and Computer Science September 4, 2009 (l ,J Certified by................ Piotr I/ yk Associate Professor Thesis Supervisor Accepted by ................................ /''~~ Terry P. Orlando Chairman, Department Committee on Graduate Students MASSACHUSETTS PaY OF TECHNOLOGY SEP 3 0 2009 ARCHIVES LIBRARIES Nearest Neighbor Search: the Old, the New, and the Impossible by Alexandr Andoni Submitted to the Department of Electrical Engineering and Computer Science on September 4, 2009, in partial fulfillment of the requirements for the degree of Doctor of Philosophy Abstract Over the last decade, an immense amount of data has become available. From collections of photos, to genetic data, and to network traffic statistics, modern technologies and cheap storage have made it possible to accumulate huge datasets. But how can we effectively use all this data? The ever growing sizes of the datasets make it imperative to design new algorithms capable of sifting through this data with extreme efficiency. A fundamental computational primitive for dealing with massive dataset is the Nearest Neighbor (NN) problem. In the NN problem, the goal is to preprocess a set of objects, so that later, given a query object, one can find efficiently the data object most similar to the query. This problem has a broad set of applications in data processing and analysis. -

Stanford University's Economic Impact Via Innovation and Entrepreneurship
Full text available at: http://dx.doi.org/10.1561/0300000074 Impact: Stanford University’s Economic Impact via Innovation and Entrepreneurship Charles E. Eesley Associate Professor in Management Science & Engineering W.M. Keck Foundation Faculty Scholar, School of Engineering Stanford University William F. Miller† Herbert Hoover Professor of Public and Private Management Emeritus Professor of Computer Science Emeritus and former Provost Stanford University and Faculty Co-director, SPRIE Boston — Delft Full text available at: http://dx.doi.org/10.1561/0300000074 Contents 1 Executive Summary2 1.1 Regional and Local Impact................. 3 1.2 Stanford’s Approach ..................... 4 1.3 Nonprofits and Social Innovation .............. 8 1.4 Alumni Founders and Leaders ................ 9 2 Creating an Entrepreneurial Ecosystem 12 2.1 History of Stanford and Silicon Valley ........... 12 3 Analyzing Stanford’s Entrepreneurial Footprint 17 3.1 Case Study: Google Inc., the Global Reach of One Stanford Startup ............................ 20 3.2 The Types of Companies Stanford Graduates Create .... 22 3.3 The BASES Study ...................... 30 4 Funding Startup Businesses 33 4.1 Study of Investors ...................... 38 4.2 Alumni Initiatives: Stanford Angels & Entrepreneurs Alumni Group ............................ 44 4.3 Case Example: Clint Korver ................. 44 5 How Stanford’s Academic Experience Creates Entrepreneurs 46 Full text available at: http://dx.doi.org/10.1561/0300000074 6 Changing Patterns in Entrepreneurial Career Paths 52 7 Social Innovation, Non-Profits, and Social Entrepreneurs 57 7.1 Case Example: Eric Krock .................. 58 7.2 Stanford Centers and Programs for Social Entrepreneurs . 59 7.3 Case Example: Miriam Rivera ................ 61 7.4 Creating Non-Profit Organizations ............. 63 8 The Lean Startup 68 9 How Stanford Supports Entrepreneurship—Programs, Cen- ters, Projects 77 9.1 Stanford Technology Ventures Program ......... -

SIGMOD Flyer
DATES: Research paper SIGMOD 2006 abstracts Nov. 15, 2005 Research papers, 25th ACM SIGMOD International Conference on demonstrations, Management of Data industrial talks, tutorials, panels Nov. 29, 2005 June 26- June 29, 2006 Author Notification Feb. 24, 2006 Chicago, USA The annual ACM SIGMOD conference is a leading international forum for database researchers, developers, and users to explore cutting-edge ideas and results, and to exchange techniques, tools, and experiences. We invite the submission of original research contributions as well as proposals for demonstrations, tutorials, industrial presentations, and panels. We encourage submissions relating to all aspects of data management defined broadly and particularly ORGANIZERS: encourage work that represent deep technical insights or present new abstractions and novel approaches to problems of significance. We especially welcome submissions that help identify and solve data management systems issues by General Chair leveraging knowledge of applications and related areas, such as information retrieval and search, operating systems & Clement Yu, U. of Illinois storage technologies, and web services. Areas of interest include but are not limited to: at Chicago • Benchmarking and performance evaluation Vice Gen. Chair • Data cleaning and integration Peter Scheuermann, Northwestern Univ. • Database monitoring and tuning PC Chair • Data privacy and security Surajit Chaudhuri, • Data warehousing and decision-support systems Microsoft Research • Embedded, sensor, mobile databases and applications Demo. Chair Anastassia Ailamaki, CMU • Managing uncertain and imprecise information Industrial PC Chair • Peer-to-peer data management Alon Halevy, U. of • Personalized information systems Washington, Seattle • Query processing and optimization Panels Chair Christian S. Jensen, • Replication, caching, and publish-subscribe systems Aalborg University • Text search and database querying Tutorials Chair • Semi-structured data David DeWitt, U. -

The Best Nurturers in Computer Science Research
The Best Nurturers in Computer Science Research Bharath Kumar M. Y. N. Srikant IISc-CSA-TR-2004-10 http://archive.csa.iisc.ernet.in/TR/2004/10/ Computer Science and Automation Indian Institute of Science, India October 2004 The Best Nurturers in Computer Science Research Bharath Kumar M.∗ Y. N. Srikant† Abstract The paper presents a heuristic for mining nurturers in temporally organized collaboration networks: people who facilitate the growth and success of the young ones. Specifically, this heuristic is applied to the computer science bibliographic data to find the best nurturers in computer science research. The measure of success is parameterized, and the paper demonstrates experiments and results with publication count and citations as success metrics. Rather than just the nurturer’s success, the heuristic captures the influence he has had in the indepen- dent success of the relatively young in the network. These results can hence be a useful resource to graduate students and post-doctoral can- didates. The heuristic is extended to accurately yield ranked nurturers inside a particular time period. Interestingly, there is a recognizable deviation between the rankings of the most successful researchers and the best nurturers, which although is obvious from a social perspective has not been statistically demonstrated. Keywords: Social Network Analysis, Bibliometrics, Temporal Data Mining. 1 Introduction Consider a student Arjun, who has finished his under-graduate degree in Computer Science, and is seeking a PhD degree followed by a successful career in Computer Science research. How does he choose his research advisor? He has the following options with him: 1. Look up the rankings of various universities [1], and apply to any “rea- sonably good” professor in any of the top universities. -

Approximation, Randomization, and Combinatorial Optimization
Approximation, Randomization, and Combinatorial Optimization. Algorithms and Techniques 17th International Workshop, APPROX 2014, and 18th International Workshop, RANDOM 2014 September 4–6, 2014, Barcelona, Spain Edited by Klaus Jansen José D. P. Rolim Nikhil R. Devanur Cristopher Moore LIPIcs – Vol. 28 – APPROX/RANDOM’14 www.dagstuhl.de/lipics Editors Klaus Jansen José D. P. Rolim University of Kiel University of Geneva Kiel Geneva [email protected] [email protected] Nikhil R. Devanur Cristopher Moore Microsoft Research Santa Fe Institute Redmond New Mexico [email protected] [email protected] ACM Classification 1998 C.2.1 Network Architecture and Design, C.2.2 Computer-communication, E.4 Coding and Information Theory, F. Theory of Computation, F.1.0 Computation by Abstract Devices, F.1.1 Models of Computation – relations between models, F.1.2 Modes of Computation, F.1.3 Complexity Measures and Classes, F.2.0 Analysis of Algorithms and Problem Complexity, F.2.1 Numerical Algorithms and Problems, F.2.2 Nonnumerical Algorithms and Problems G.1.2 Approximation, G.1.6 Optimization, G.2 Discrete Mathematics, G.2.1 Combinatorics, G.2.2 Graph Theory, G.3 Probability and Statistics, I.1.2 Algorithms, J.4 Computer Applications – Social and Behavioral Sciences ISBN 978-3-939897-74-3 Published online and open access by Schloss Dagstuhl – Leibniz-Zentrum für Informatik GmbH, Dagstuhl Publishing, Saarbrücken/Wadern, Germany. Online available at http://www.dagstuhl.de/dagpub/978-3-939897-74-3. Publication date September, 2014 Bibliographic information published by the Deutsche Nationalbibliothek The Deutsche Nationalbibliothek lists this publication in the Deutsche Nationalbibliografie; detailed bibliographic data are available in the Internet at http://dnb.d-nb.de. -

Securely Obfuscating Re-Encryption
Securely Obfuscating Re-Encryption Susan Hohenberger¤ Guy N. Rothblumy abhi shelatz Vinod Vaikuntanathanx December 1, 2008 Abstract We present a positive obfuscation result for a traditional cryptographic functionality. This posi- tive result stands in contrast to well-known impossibility results [3] for general obfuscation and recent impossibility and improbability [13] results for obfuscation of many cryptographic functionalities. Whereas other positive obfuscation results in the standard model apply to very simple point func- tions, our obfuscation result applies to the signi¯cantly more complex and widely-used re-encryption functionality. This functionality takes a ciphertext for message m encrypted under Alice's public key and transforms it into a ciphertext for the same message m under Bob's public key. To overcome impossibility results and to make our results meaningful for cryptographic functionalities, our scheme satis¯es a de¯nition of obfuscation which incorporates more security-aware provisions. ¤Johns Hopkins University, [email protected]. Research partially performed at IBM Zurich Research Laboratory, Switzer- land. yMIT CSAIL, [email protected]. Research supported by NSF grant CNS-0430450 and NSF grant CFF-0635297. zUniversity of Virginia, [email protected]. Research performed at IBM Zurich Research Laboratory, Switzerland. xMIT CSAIL, [email protected] 1 1 Introduction A recent line of research in theoretical cryptography aims to understand whether it is possible to obfuscate programs so that a program's code becomes unintelligible while its functionality remains unchanged. A general method for obfuscating programs would lead to the solution of many open problems in cryptography. Unfortunately, Barak, Goldreich, Impagliazzo, Rudich, Sahai, Vadhan and Yang [3] show that for many notions of obfuscation, a general program obfuscator does not exist|i.e., they exhibit a class of circuits which cannot be obfuscated. -

Prediction from Partial Information and Hindsight, with Application to Circuit Lower Bounds
comput. complex. c Springer Nature Switzerland AG 2019 DOI 10.1007/s00037-019-00177-4 computational complexity PREDICTION FROM PARTIAL INFORMATION AND HINDSIGHT, WITH APPLICATION TO CIRCUIT LOWER BOUNDS Or Meir and Avi Wigderson Abstract. Consider a random sequence of n bits that has entropy at least n − k, where k n. A commonly used observation is that an average coordinate of this random sequence is close to being uniformly distributed, that is, the coordinate “looks random.” In this work, we prove a stronger result that says, roughly, that the average coordinate n looks random to an adversary that is allowed to query ≈ k other co- ordinates of the sequence, even if the adversary is non-deterministic. This implies corresponding results for decision trees and certificates for Boolean functions. As an application of this result, we prove a new result on depth-3 cir- cuits, which recovers as a direct corollary the known lower bounds for the parity and majority functions, as well as a lower bound on sensi- tive functions due to Boppana (Circuits Inf Process Lett 63(5):257–261, 1997). An interesting feature of this proof is that it works in the frame- work of Karchmer and Wigderson (SIAM J Discrete Math 3(2):255–265, 1990), and, in particular, it is a “top-down” proof (H˚astad et al. in Computat Complex 5(2):99–112, 1995). Finally, it yields a new kind of a random restriction lemma for non-product distributions, which may be of independent interest. Keywords. Certificate complexity, Circuit complexity, Circuit com- plexity lower bounds, Decision tree complexity, Information theoretic, Query complexity, Sensitivity Subject classification. -

Uriel Feige, Publications, July 2017. Papers Are Sorted by Categories. for Papers That Have More Than One Version (Typically, Jo
Uriel Feige, Publications, July 2017. Papers are sorted by categories. For papers that have more than one version (typically, journal version and conference proceedings), the different versions are combined into one entry in the list. STOC is shorthand for \Annual ACM Symposium on the Theory of Computing". FOCS is shorthand for \Symposium on Foundations of Computer Science". Journal publications 1. Uriel Feige, Amos Fiat, and Adi Shamir. \Zero Knowledge Proofs of Identity". Jour- nal of Cryptology, 1988, Vol. 1, pp. 77-94. Preliminary version appeared in Proc. of the 19th STOC, 1987, pp. 210-217. 2. Uriel Feige, David Peleg, Prabhakar Raghavan and Eli Upfal. \Randomized Broadcast in Networks". Random Structures and algorithms, 1(4), 1990, pp. 447-460. Preliminary version appeared in proceedings of SIGAL International Symposium on Algorithms, Tokyo, Japan, August 1990. 3. Uriel Feige and Adi Shamir. \Multi-Oracle Interactive Protocols with Constant Space Verifiers”. Journal of Computer and System Sciences, Vol. 44, pp. 259-271, April 1992. Preliminary version appeared in Proceedings of Fourth Annual Conference on Struc- ture in Complexity Theory, June 1989. 4. Uriel Feige. "On the Complexity of Finite Random Functions". Information Process- ing Letters 44 (1992) 295-296. 5. Uriel Feige, David Peleg, Prabhakar Raghavan and Eli Upfal. \Computing With Noisy Information". SIAM Journal on Computing, 23(5), 1001{1018, 1994. Preliminary version appeared in Proceedings of 22nd STOC, 1990, pp. 128-137. 6. Noga Alon, Uriel Feige, Avi Wigderson, and David Zuckerman. "Derandomized Graph Products". Computational Complexity 5 (1995) 60{75. 7. Uriel Feige. \A Tight Upper Bound on the Cover Time for Random Walks on Graphs". -

Statistical Queries and Statistical Algorithms: Foundations and Applications∗
Statistical Queries and Statistical Algorithms: Foundations and Applications∗ Lev Reyzin Department of Mathematics, Statistics, and Computer Science University of Illinois at Chicago [email protected] Abstract We give a survey of the foundations of statistical queries and their many applications to other areas. We introduce the model, give the main definitions, and we explore the fundamental theory statistical queries and how how it connects to various notions of learnability. We also give a detailed summary of some of the applications of statistical queries to other areas, including to optimization, to evolvability, and to differential privacy. 1 Introduction Over 20 years ago, Kearns [1998] introduced statistical queries as a framework for designing machine learning algorithms that are tolerant to noise. The statistical query model restricts a learning algorithm to ask certain types of queries to an oracle that responds with approximately correct answers. This framework has has proven useful, not only for designing noise-tolerant algorithms, but also for its connections to other noise models, for its ability to capture many of our current techniques, and for its explanatory power about the hardness of many important problems. Researchers have also found many connections between statistical queries and a variety of modern topics, including to evolvability, differential privacy, and adaptive data analysis. Statistical queries are now both an important tool and remain a foundational topic with many important questions. The aim of this survey is to illustrate these connections and bring researchers to the forefront of our understanding of this important area. We begin by formally introducing the model and giving the main definitions (Section 2), we then move to exploring the fundamental theory of learning statistical queries and how how it connects to other notions of arXiv:2004.00557v2 [cs.LG] 14 May 2020 learnability (Section 3).