Development and Implementation of Secure Web Applications
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
How to Secure Your Web Site Picked up SQL Injection and Cross-Site Scripting As Sample Cases of Failure Because These Two Are the Two Most Reported Vulnerabilities
How to Secure your Website rd 3 Edition Approaches to Improve Web Application and Web Site Security June 2008 IT SECURITY CENTER (ISEC) INFORMATION-TECHNOLOGY PROMOTION AGENCY, JAPAN This document is a translation of the original Japanese edition. Please be advises that most of the references referred in this book are offered in Japanese only. Both English and Japanese edition are available for download at: http://www.ipa.go.jp/security/english/third.html (English web page) http://www.ipa.go.jp/security/vuln/websecurity.html (Japanese web page) Translated by Hiroko Okashita (IPA), June 11 2008 Contents Contents ......................................................................................................................................... 1 Preface ........................................................................................................................................... 2 Organization of This Book ........................................................................................................... 3 Intended Reader ......................................................................................................................... 3 Fixing Vulnerabilities – Fundamental Solution and Mitigation Measure - .................................... 3 1. Web Application Security Implementation ............................................................................... 5 1.1 SQL Injection .................................................................................................................... 6 1.2 -
Web Hacking 101 How to Make Money Hacking Ethically
Web Hacking 101 How to Make Money Hacking Ethically Peter Yaworski © 2015 - 2016 Peter Yaworski Tweet This Book! Please help Peter Yaworski by spreading the word about this book on Twitter! The suggested tweet for this book is: Can’t wait to read Web Hacking 101: How to Make Money Hacking Ethically by @yaworsk #bugbounty The suggested hashtag for this book is #bugbounty. Find out what other people are saying about the book by clicking on this link to search for this hashtag on Twitter: https://twitter.com/search?q=#bugbounty For Andrea and Ellie. Thanks for supporting my constant roller coaster of motivation and confidence. This book wouldn’t be what it is if it were not for the HackerOne Team, thank you for all the support, feedback and work that you contributed to make this book more than just an analysis of 30 disclosures. Contents 1. Foreword ....................................... 1 2. Attention Hackers! .................................. 3 3. Introduction ..................................... 4 How It All Started ................................. 4 Just 30 Examples and My First Sale ........................ 5 Who This Book Is Written For ........................... 7 Chapter Overview ................................. 8 Word of Warning and a Favour .......................... 10 4. Background ...................................... 11 5. HTML Injection .................................... 14 Description ....................................... 14 Examples ........................................ 14 1. Coinbase Comments ............................. -
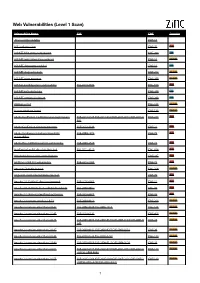
Web Vulnerabilities (Level 1 Scan)
Web Vulnerabilities (Level 1 Scan) Vulnerability Name CVE CWE Severity .htaccess file readable CWE-16 ASP code injection CWE-95 High ASP.NET MVC version disclosure CWE-200 Low ASP.NET application trace enabled CWE-16 Medium ASP.NET debugging enabled CWE-16 Low ASP.NET diagnostic page CWE-200 Medium ASP.NET error message CWE-200 Medium ASP.NET padding oracle vulnerability CVE-2010-3332 CWE-310 High ASP.NET path disclosure CWE-200 Low ASP.NET version disclosure CWE-200 Low AWStats script CWE-538 Medium Access database found CWE-538 Medium Adobe ColdFusion 9 administrative login bypass CVE-2013-0625 CVE-2013-0629CVE-2013-0631 CVE-2013-0 CWE-287 High 632 Adobe ColdFusion directory traversal CVE-2013-3336 CWE-22 High Adobe Coldfusion 8 multiple linked XSS CVE-2009-1872 CWE-79 High vulnerabilies Adobe Flex 3 DOM-based XSS vulnerability CVE-2008-2640 CWE-79 High AjaxControlToolkit directory traversal CVE-2015-4670 CWE-434 High Akeeba backup access control bypass CWE-287 High AmCharts SWF XSS vulnerability CVE-2012-1303 CWE-79 High Amazon S3 public bucket CWE-264 Medium AngularJS client-side template injection CWE-79 High Apache 2.0.39 Win32 directory traversal CVE-2002-0661 CWE-22 High Apache 2.0.43 Win32 file reading vulnerability CVE-2003-0017 CWE-20 High Apache 2.2.14 mod_isapi Dangling Pointer CVE-2010-0425 CWE-20 High Apache 2.x version equal to 2.0.51 CVE-2004-0811 CWE-264 Medium Apache 2.x version older than 2.0.43 CVE-2002-0840 CVE-2002-1156 CWE-538 Medium Apache 2.x version older than 2.0.45 CVE-2003-0132 CWE-400 Medium Apache 2.x version -

HTTP Parameter Pollution Vulnerabilities in Web Applications @ Blackhat Europe 2011 @
HTTP Parameter Pollution Vulnerabilities in Web Applications @ BlackHat Europe 2011 @ Marco ‘embyte’ Balduzzi embyte(at)madlab(dot)it http://www.madlab.it Contents 1 Introduction 2 2 HTTP Parameter Pollution Attacks 3 2.1 Parameter Precedence in Web Applications . .3 2.2 Parameter Pollution . .4 2.2.1 Cross-Channel Pollution . .5 2.2.2 HPP to bypass CSRF tokens . .5 2.2.3 Bypass WAFs input validation checks . .6 3 Automated HPP Vulnerability Detection 6 3.1 Browser and Crawler Components . .7 3.2 P-Scan: Analysis of the Parameter Precedence . .7 3.3 V-Scan: Testing for HPP vulnerabilities . .9 3.3.1 Handling special cases . 10 3.4 Implementation . 10 3.4.1 Online Service . 11 3.5 Limitations . 11 4 Evaluation 11 4.1 HPP Prevalence in Popular Websites . 11 4.1.1 Parameter Precedence . 13 4.1.2 HPP Vulnerabilities . 14 4.1.3 False Positives . 15 4.2 Examples of Discovered Vulnerabilities . 15 4.2.1 Facebook Share . 16 4.2.2 CSRF via HPP Injection . 16 4.2.3 Shopping Carts . 16 4.2.4 Financial Institutions . 16 4.2.5 Tampering with Query Results . 17 5 Related work 17 6 Conclusion 18 7 Acknowledgments 18 1 1 Introduction In the last twenty years, web applications have grown from simple, static pages to complex, full-fledged dynamic applications. Typically, these applications are built using heterogeneous technologies and consist of code that runs on the client (e.g., Javascript) and code that runs on the server (e.g., Java servlets). Even simple web applications today may accept and process hundreds of different HTTP parameters to be able to provide users with rich, inter- active services. -

Developer Report Testphp Vulnweb Com.Pdf
Acunetix Website Audit 31 October, 2014 Developer Report Generated by Acunetix WVS Reporter (v9.0 Build 20140422) Scan of http://testphp.vulnweb.com:80/ Scan details Scan information Start time 31/10/2014 12:40:34 Finish time 31/10/2014 12:49:30 Scan time 8 minutes, 56 seconds Profile Default Server information Responsive True Server banner nginx/1.4.1 Server OS Unknown Server technologies PHP Threat level Acunetix Threat Level 3 One or more high-severity type vulnerabilities have been discovered by the scanner. A malicious user can exploit these vulnerabilities and compromise the backend database and/or deface your website. Alerts distribution Total alerts found 190 High 93 Medium 48 Low 8 Informational 41 Knowledge base WordPress web application WordPress web application was detected in directory /bxss/adminPan3l. List of file extensions File extensions can provide information on what technologies are being used on this website. List of file extensions detected: - php => 50 file(s) - css => 4 file(s) - swf => 1 file(s) - fla => 1 file(s) - conf => 1 file(s) - htaccess => 1 file(s) - htm => 1 file(s) - xml => 8 file(s) - name => 1 file(s) - iml => 1 file(s) - Log => 1 file(s) - tn => 8 file(s) - LOG => 1 file(s) - bak => 2 file(s) - txt => 2 file(s) - html => 2 file(s) - sql => 1 file(s) Acunetix Website Audit 2 - js => 1 file(s) List of client scripts These files contain Javascript code referenced from the website. - /medias/js/common_functions.js List of files with inputs These files have at least one input (GET or POST). -
![WEB APPLICATION PENETRATION TESTING] March 1, 2018](https://docslib.b-cdn.net/cover/5918/web-application-penetration-testing-march-1-2018-925918.webp)
WEB APPLICATION PENETRATION TESTING] March 1, 2018
[WEB APPLICATION PENETRATION TESTING] March 1, 2018 Contents Information Gathering .................................................................................................................................. 4 1. Conduct Search Engine Discovery and Reconnaissance for Information Leakage .......................... 4 2. Fingerprint Web Server ..................................................................................................................... 5 3. Review Webserver Metafiles for Information Leakage .................................................................... 7 4. Enumerate Applications on Webserver ............................................................................................. 8 5. Review Webpage Comments and Metadata for Information Leakage ........................................... 11 6. Identify Application Entry Points ................................................................................................... 11 7. Map execution paths through application ....................................................................................... 13 8. Fingerprint Web Application & Web Application Framework ...................................................... 14 Configuration and Deployment Management Testing ................................................................................ 18 1. Test Network/Infrastructure Configuration..................................................................................... 18 2. Test Application Platform Configuration....................................................................................... -
OWASP Annotated Application Security Verification Standard
OWASP Annotated Application Security Verification Standard Documentation Release 3.0.0 Boy Baukema Oct 03, 2017 Browse by chapter: 1 v1 Architecture, design and threat modelling1 2 v2 Authentication verification requirements3 3 v3 Session management verification requirements 13 4 v4 Access control verification requirements 19 5 v5 Malicious input handling verification requirements 23 6 v6 Output encoding / escaping 27 7 v7 Cryptography at rest verification requirements 29 8 v8 Error handling and logging verification requirements 31 9 v9 Data protection verification requirements 35 10 v10 Communications security verification requirements 39 11 v11 HTTP security configuration verification requirements 43 12 v12 Security configuration verification requirements 47 13 v13 Malicious controls verification requirements 49 14 v14 Internal security verification requirements 51 15 v15 Business logic verification requirements 53 16 v16 Files and resources verification requirements 55 17 v17 Mobile verification requirements 59 18 v18 Web services verification requirements 63 19 v19 Configuration 65 20 Level 1: Opportunistic 67 i 21 Level 2: Standard 69 22 Level 3: Advanced 71 ii CHAPTER 1 v1 Architecture, design and threat modelling 1.1 All components are identified Verify that all application components are identified and are known to be needed. Levels: 1, 2, 3 General The purpose of this requirement is twofold: 1. Discover third party components that may contain (public) vulnerabilities. 2. Discover ‘dead code / dependencies’ that increase attack surface without any benefit in functionality. Developers may be tempted to keep dead code / dependencies around ‘in case I ever need it’, however this is not an argument for a shippable product, such dead code / dependencies is better left on a source control system. -

5G; 5G System; Access and Mobility Management Services; Stage 3 (3GPP TS 29.518 Version 15.0.0 Release 15)
ETSI TS 129 518 V15.0.0 (2018-09) TECHNICAL SPECIFICATION 5G; 5G System; Access and Mobility Management Services; Stage 3 (3GPP TS 29.518 version 15.0.0 Release 15) 3GPP TS 29.518 version 15.0.0 Release 15 1 ETSI TS 129 518 V15.0.0 (2018-09) Reference RTS/TSGC-0429518vf00 Keywords 5G ETSI 650 Route des Lucioles F-06921 Sophia Antipolis Cedex - FRANCE Tel.: +33 4 92 94 42 00 Fax: +33 4 93 65 47 16 Siret N° 348 623 562 00017 - NAF 742 C Association à but non lucratif enregistrée à la Sous-Préfecture de Grasse (06) N° 7803/88 Important notice The present document can be downloaded from: http://www.etsi.org/standards-search The present document may be made available in electronic versions and/or in print. The content of any electronic and/or print versions of the present document shall not be modified without the prior written authorization of ETSI. In case of any existing or perceived difference in contents between such versions and/or in print, the only prevailing document is the print of the Portable Document Format (PDF) version kept on a specific network drive within ETSI Secretariat. Users of the present document should be aware that the document may be subject to revision or change of status. Information on the current status of this and other ETSI documents is available at https://portal.etsi.org/TB/ETSIDeliverableStatus.aspx If you find errors in the present document, please send your comment to one of the following services: https://portal.etsi.org/People/CommiteeSupportStaff.aspx Copyright Notification No part may be reproduced or utilized in any form or by any means, electronic or mechanical, including photocopying and microfilm except as authorized by written permission of ETSI. -

Towards an Ontology of HTTP Interactions Mathieu Lirzin, Béatrice Markhoff
Towards an ontology of HTTP interactions Mathieu Lirzin, Béatrice Markhoff To cite this version: Mathieu Lirzin, Béatrice Markhoff. Towards an ontology of HTTP interactions. [Research Report] Université de Tours - LIFAT. 2020. hal-02901879 HAL Id: hal-02901879 https://hal.archives-ouvertes.fr/hal-02901879 Submitted on 17 Jul 2020 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. Towards an ontology of HTTP interactions Mathieu Lirzin1;2[0000−0002−8366−1861] and B´eatriceMarkhoff2[0000−0002−5171−8499] 1 N´er´eide,8 rue des d´eport´es,37000 Tours, France [email protected] 2 LIFAT EA 6300, Universit´ede Tours, Tours, France [email protected] Abstract. Enterprise information systems have adopted Web-based foun- dations for exchanges between heterogeneous programmes. These programs provide and consume via Web APIs some resources identified by URIs, whose representations are transmitted via HTTP. Furthermore HTTP re- mains at the heart of all Web developments (Semantic Web, linked data, IoT...). Thus, situations where a program must be able to reason about HTTP interactions (request-response) are multiplying. This requires an explicit formal specification of a shared conceptualization of those inter- actions. -

X41 D-SEC Gmbh Dennewartstr
Browser Security White PAPER Final PAPER 2017-09-19 Markus VERVIER, Michele Orrù, Berend-Jan WEVER, Eric Sesterhenn X41 D-SEC GmbH Dennewartstr. 25-27 D-52068 Aachen Amtsgericht Aachen: HRB19989 Browser Security White PAPER Revision History Revision Date Change Editor 1 2017-04-18 Initial Document E. Sesterhenn 2 2017-04-28 Phase 1 M. VERVIER, M. Orrù, E. Sesterhenn, B.-J. WEVER 3 2017-05-19 Phase 2 M. VERVIER, M. Orrù, E. Sesterhenn, B.-J. WEVER 4 2017-05-25 Phase 3 M. VERVIER, M. Orrù, E. Sesterhenn, B.-J. WEVER 5 2017-06-05 First DrAFT M. VERVIER, M. Orrù, E. Sesterhenn, B.-J. WEVER 6 2017-06-26 Second DrAFT M. VERVIER, M. Orrù, E. Sesterhenn, B.-J. WEVER 7 2017-07-24 Final DrAFT M. VERVIER, M. Orrù, E. Sesterhenn, B.-J. WEVER 8 2017-08-25 Final PAPER M. VERVIER, M. Orrù, E. Sesterhenn, B.-J. WEVER 9 2017-09-19 Public Release M. VERVIER, M. Orrù, E. Sesterhenn, B.-J. WEVER X41 D-SEC GmbH PAGE 1 OF 196 Contents 1 ExECUTIVE Summary 7 2 Methodology 10 3 Introduction 12 3.1 Google Chrome . 13 3.2 Microsoft Edge . 14 3.3 Microsoft Internet Explorer (IE) . 16 4 Attack Surface 18 4.1 Supported Standards . 18 4.1.1 WEB TECHNOLOGIES . 18 5 Organizational Security Aspects 21 5.1 Bug Bounties . 21 5.1.1 Google Chrome . 21 5.1.2 Microsoft Edge . 22 5.1.3 Internet Explorer . 22 5.2 Exploit Pricing . 22 5.2.1 ZERODIUM . 23 5.2.2 Pwn2Own . -

Ch 13: Attacking Users: Other Techniques (Part 2) Other Client-Side Injection Attacks HTTP Header Injection
CNIT 129S: Securing Web Applications Ch 13: Attacking Users: Other Techniques (Part 2) Other Client-Side Injection Attacks HTTP Header Injection • User-controlled data in an HTTP header • Most commonly the Location and Set-Cookie headers Injecting Another Header Exploiting Header Injection • See if %0d and %0a return decoded as carriage- return and line-feed • If only one works, you may still be able to exploit it • If they are blocked or sanitized, try these bypasses Injecting Cookies • Cookies may persist across browser sessions Delivering Other Attacks • HTTP header injection allows an attacker to control the entire body of a response • Can deliver almost any attack • Virtual website defacement • Script injection • Redirection HTTP Response Splitting • Inject a second complete page into the headers • Must inject carriage returns and line feeds • Fixed in modern servers (link Ch 13d) Poisoning the Cache on a Proxy Server Preventing Header Injection • Don't insert user-controllable input into headers • If you must, use • Input validation (context-dependent) • Output validation: block all ASCII characters below 0x20 Cookie Injection • Attacker sets or modifies a cookie in the victim user's browser • This may be possible if: • App has functionality that takes a name and value from parameters and sets those within a cookie, such as "Save user preferences" • HTTP header injection vulnerability Cookie Injection • Setting a malicious cookie via XSS • XSS in related domains can be leveraged to set a cookie on the targeted domain, from any of -

Alibaba Cloud Alibaba Cloud CDN
Alibaba Cloud Alibaba Cloud CDN Domain Management Issue: 20190815 Alibaba Cloud CDN Domain Management / Legal disclaimer Legal disclaimer Alibaba Cloud reminds you to carefully read and fully understand the terms and conditions of this legal disclaimer before you read or use this document. If you have read or used this document, it shall be deemed as your total acceptance of this legal disclaimer. 1. You shall download and obtain this document from the Alibaba Cloud website or other Alibaba Cloud-authorized channels, and use this document for your own legal business activities only. The content of this document is considered confidential information of Alibaba Cloud. You shall strictly abide by the confidentiality obligations. No part of this document shall be disclosed or provided to any third party for use without the prior written consent of Alibaba Cloud. 2. No part of this document shall be excerpted, translated, reproduced, transmitted, or disseminated by any organization, company, or individual in any form or by any means without the prior written consent of Alibaba Cloud. 3. The content of this document may be changed due to product version upgrades , adjustments, or other reasons. Alibaba Cloud reserves the right to modify the content of this document without notice and the updated versions of this document will be occasionally released through Alibaba Cloud-authorized channels. You shall pay attention to the version changes of this document as they occur and download and obtain the most up-to-date version of this document from Alibaba Cloud-authorized channels. 4. This document serves only as a reference guide for your use of Alibaba Cloud products and services.