Web Hacking 101 How to Make Money Hacking Ethically
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
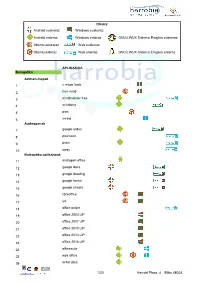
Android Euskaraz Windows Euskaraz Android Erderaz Windows Erderaz GNU/LINUX Sistema Eragilea Euskeraz Ubuntu Euskaraz We
Oharra: Android euskaraz Windows euskaraz Android erderaz Windows erderaz GNU/LINUX Sistema Eragilea euskeraz Ubuntu euskaraz Web euskaraz Ubuntu erderaz Web erderaz GNU/LINUX Sistema Eragilea erderaz APLIKAZIOA Bulegotika Adimen-mapak 1 c maps tools 2 free mind 3 mindmeister free 4 mindomo 5 plan 6 xmind Aurkezpenak 7 google slides 8 pow toon 9 prezi 10 sway Bulegotika-aplikazioak 11 andropen office 12 google docs 13 google drawing 14 google forms 15 google sheets 16 libreoffice 17 lyx 18 office online 19 office 2003 LIP 20 office 2007 LIP 21 office 2010 LIP 22 office 2013 LIP 23 office 2016 LIP 24 officesuite 25 wps office 26 writer plus 1/20 Harrobi Plaza, 4 Bilbo 48003 CAD 27 draftsight 28 librecad 29 qcad 30 sweet home 31 timkercad Datu-baseak 32 appserv 33 dbdesigner 34 emma 35 firebird 36 grubba 37 kexi 38 mysql server 39 mysql workbench 40 postgresql 41 tora Diagramak 42 dia 43 smartdraw Galdetegiak 44 kahoot Maketazioa 45 scribus PDF editoreak 46 master pdf editor 47 pdfedit pdf escape 48 xournal PDF irakurgailuak 49 adobe reader 50 evince 51 foxit reader 52 sumatraPDF 2/20 Harrobi Plaza, 4 Bilbo 48003 Hezkuntza Aditzak lantzeko 53 aditzariketak.wordpress 54 aditz laguntzailea 55 aditzak 56 aditzak.com 57 aditzapp 58 adizkitegia 59 deklinabidea 60 euskaljakintza 61 euskera! 62 hitano 63 ikusi eta ikasi 64 ikusi eta ikasi bi! Apunteak partekatu 65 flashcard machine 66 goconqr 67 quizlet 68 rincon del vago Diktaketak 69 dictation Entziklopediak 70 auñamendi eusko entziklopedia 71 elhuyar zth hiztegi entziklopedikoa 72 harluxet 73 lur entziklopedia tematikoa 74 lur hiztegi entziklopedikoa 75 wikipedia Esamoldeak 76 AEK euskara praktikoa 77 esamoldeapp 78 Ikapp-zaharrak berri Estatistikak 79 pspp 80 r 3/20 Harrobi Plaza, 4 Bilbo 48003 Euskara azterketak 81 ega app 82 egabai 83 euskal jakintza 84 euskara ikasiz 1. -

Volunteered Geographic Information System Design: Project and Participation Guidelines
International Journal of Geo-Information Article Volunteered Geographic Information System Design: Project and Participation Guidelines José-Pablo Gómez-Barrón *, Miguel-Ángel Manso-Callejo, Ramón Alcarria and Teresa Iturrioz MERCATOR Research Group: Geo-Information Technologies, Technical High School of Topography, Geodesy and Cartography Engineering, Technical University of Madrid (UPM), Campus Sur, 28031 Madrid, Spain; [email protected] (M.-A.M.-C.); [email protected] (R.A.); [email protected] (T.I.) * Correspondence: [email protected]; Tel.: +34-913-366-487 Academic Editors: Linda See, Vyron Antoniou, David Jonietz and Wolfgang Kainz Received: 14 March 2016; Accepted: 20 June 2016; Published: 5 July 2016 Abstract: This article sets forth the early phases of a methodological proposal for designing and developing Volunteered Geographic Information (VGI) initiatives based on a system perspective analysis in which the components depend and interact dynamically among each other. First, it focuses on those characteristics of VGI projects that present different goals and modes of organization, while using a crowdsourcing strategy to manage participants and contributions. Next, a tool is developed in order to design the central crowdsourced processing unit that is best suited for a specific project definition, associating it with a trend towards crowd-based or community-driven approaches. The design is structured around the characterization of different ways of participating, and the task cognitive demand of working on geo-information management, spatial problem solving and ideation, or knowledge acquisition. Then, the crowdsourcing process design helps to identify what kind of participants are needed and outline subsequent engagement strategies. This is based on an analysis of differences among volunteers’ participatory behaviors and the associated set of factors motivating them to contribute, whether on a crowd or community-sourced basis. -
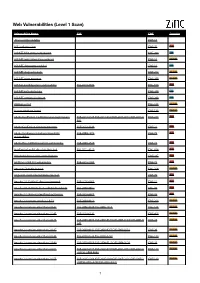
Web Vulnerabilities (Level 1 Scan)
Web Vulnerabilities (Level 1 Scan) Vulnerability Name CVE CWE Severity .htaccess file readable CWE-16 ASP code injection CWE-95 High ASP.NET MVC version disclosure CWE-200 Low ASP.NET application trace enabled CWE-16 Medium ASP.NET debugging enabled CWE-16 Low ASP.NET diagnostic page CWE-200 Medium ASP.NET error message CWE-200 Medium ASP.NET padding oracle vulnerability CVE-2010-3332 CWE-310 High ASP.NET path disclosure CWE-200 Low ASP.NET version disclosure CWE-200 Low AWStats script CWE-538 Medium Access database found CWE-538 Medium Adobe ColdFusion 9 administrative login bypass CVE-2013-0625 CVE-2013-0629CVE-2013-0631 CVE-2013-0 CWE-287 High 632 Adobe ColdFusion directory traversal CVE-2013-3336 CWE-22 High Adobe Coldfusion 8 multiple linked XSS CVE-2009-1872 CWE-79 High vulnerabilies Adobe Flex 3 DOM-based XSS vulnerability CVE-2008-2640 CWE-79 High AjaxControlToolkit directory traversal CVE-2015-4670 CWE-434 High Akeeba backup access control bypass CWE-287 High AmCharts SWF XSS vulnerability CVE-2012-1303 CWE-79 High Amazon S3 public bucket CWE-264 Medium AngularJS client-side template injection CWE-79 High Apache 2.0.39 Win32 directory traversal CVE-2002-0661 CWE-22 High Apache 2.0.43 Win32 file reading vulnerability CVE-2003-0017 CWE-20 High Apache 2.2.14 mod_isapi Dangling Pointer CVE-2010-0425 CWE-20 High Apache 2.x version equal to 2.0.51 CVE-2004-0811 CWE-264 Medium Apache 2.x version older than 2.0.43 CVE-2002-0840 CVE-2002-1156 CWE-538 Medium Apache 2.x version older than 2.0.45 CVE-2003-0132 CWE-400 Medium Apache 2.x version -

HTTP Parameter Pollution Vulnerabilities in Web Applications @ Blackhat Europe 2011 @
HTTP Parameter Pollution Vulnerabilities in Web Applications @ BlackHat Europe 2011 @ Marco ‘embyte’ Balduzzi embyte(at)madlab(dot)it http://www.madlab.it Contents 1 Introduction 2 2 HTTP Parameter Pollution Attacks 3 2.1 Parameter Precedence in Web Applications . .3 2.2 Parameter Pollution . .4 2.2.1 Cross-Channel Pollution . .5 2.2.2 HPP to bypass CSRF tokens . .5 2.2.3 Bypass WAFs input validation checks . .6 3 Automated HPP Vulnerability Detection 6 3.1 Browser and Crawler Components . .7 3.2 P-Scan: Analysis of the Parameter Precedence . .7 3.3 V-Scan: Testing for HPP vulnerabilities . .9 3.3.1 Handling special cases . 10 3.4 Implementation . 10 3.4.1 Online Service . 11 3.5 Limitations . 11 4 Evaluation 11 4.1 HPP Prevalence in Popular Websites . 11 4.1.1 Parameter Precedence . 13 4.1.2 HPP Vulnerabilities . 14 4.1.3 False Positives . 15 4.2 Examples of Discovered Vulnerabilities . 15 4.2.1 Facebook Share . 16 4.2.2 CSRF via HPP Injection . 16 4.2.3 Shopping Carts . 16 4.2.4 Financial Institutions . 16 4.2.5 Tampering with Query Results . 17 5 Related work 17 6 Conclusion 18 7 Acknowledgments 18 1 1 Introduction In the last twenty years, web applications have grown from simple, static pages to complex, full-fledged dynamic applications. Typically, these applications are built using heterogeneous technologies and consist of code that runs on the client (e.g., Javascript) and code that runs on the server (e.g., Java servlets). Even simple web applications today may accept and process hundreds of different HTTP parameters to be able to provide users with rich, inter- active services. -

Developer Report Testphp Vulnweb Com.Pdf
Acunetix Website Audit 31 October, 2014 Developer Report Generated by Acunetix WVS Reporter (v9.0 Build 20140422) Scan of http://testphp.vulnweb.com:80/ Scan details Scan information Start time 31/10/2014 12:40:34 Finish time 31/10/2014 12:49:30 Scan time 8 minutes, 56 seconds Profile Default Server information Responsive True Server banner nginx/1.4.1 Server OS Unknown Server technologies PHP Threat level Acunetix Threat Level 3 One or more high-severity type vulnerabilities have been discovered by the scanner. A malicious user can exploit these vulnerabilities and compromise the backend database and/or deface your website. Alerts distribution Total alerts found 190 High 93 Medium 48 Low 8 Informational 41 Knowledge base WordPress web application WordPress web application was detected in directory /bxss/adminPan3l. List of file extensions File extensions can provide information on what technologies are being used on this website. List of file extensions detected: - php => 50 file(s) - css => 4 file(s) - swf => 1 file(s) - fla => 1 file(s) - conf => 1 file(s) - htaccess => 1 file(s) - htm => 1 file(s) - xml => 8 file(s) - name => 1 file(s) - iml => 1 file(s) - Log => 1 file(s) - tn => 8 file(s) - LOG => 1 file(s) - bak => 2 file(s) - txt => 2 file(s) - html => 2 file(s) - sql => 1 file(s) Acunetix Website Audit 2 - js => 1 file(s) List of client scripts These files contain Javascript code referenced from the website. - /medias/js/common_functions.js List of files with inputs These files have at least one input (GET or POST). -
Manual Oruxmaps V.7.0.0
Manual OruxMaps v.7.0.0 ¡COLABRORATE WITH ORUXMAPS! You can help the project: Donate using Paypal Download OruxMaps Donate WORKING WITH THE MANUALS It is an easy task if we do it between all. Español English ***NEEDS A LOT OF HELP*** 1 INDEX NEWS 7.0. VERSION ............................................................................................ 3 NEWS 6.5.0 VERSION .......................................................................................... 6 QUICK START ................................................................................................... 13 Widget ..............................................................................................................................14 MAPS ............................................................................................................... 15 Online Maps ....................................................................................................................16 WMS (Web Map Service) ......................................................................................18 Composite maps .......................................................................................................22 Maps Off-Line ................................................................................................................24 Index map .......................................................................................................................29 Nigth mode .....................................................................................................................29 -
![WEB APPLICATION PENETRATION TESTING] March 1, 2018](https://docslib.b-cdn.net/cover/5918/web-application-penetration-testing-march-1-2018-925918.webp)
WEB APPLICATION PENETRATION TESTING] March 1, 2018
[WEB APPLICATION PENETRATION TESTING] March 1, 2018 Contents Information Gathering .................................................................................................................................. 4 1. Conduct Search Engine Discovery and Reconnaissance for Information Leakage .......................... 4 2. Fingerprint Web Server ..................................................................................................................... 5 3. Review Webserver Metafiles for Information Leakage .................................................................... 7 4. Enumerate Applications on Webserver ............................................................................................. 8 5. Review Webpage Comments and Metadata for Information Leakage ........................................... 11 6. Identify Application Entry Points ................................................................................................... 11 7. Map execution paths through application ....................................................................................... 13 8. Fingerprint Web Application & Web Application Framework ...................................................... 14 Configuration and Deployment Management Testing ................................................................................ 18 1. Test Network/Infrastructure Configuration..................................................................................... 18 2. Test Application Platform Configuration....................................................................................... -

Global and Complementary Geospatial Data for Sdgs
Global and Complementary (Non-authoritative) Geospatial Data for SDGs: Role and Utilisation Stephan Arnold, Jun Chen & Olav Eggers A report produced jointly by the Task Team on Global Data and Task Team on Alternative Data Sources established in December 2016 by the Working Group on Geospatial Information of the Inter-agency and Expert Group on Sustainable Development Goal Indicators (IAEG-SDGs) with contributions from Mr. Stephan Arnold, Prof. Jun Chen, Mr. Olav Eggers, Prof. Zhilin Li, Ms. Sandra Liliana Moreno Mayorga, Prof. John Mills, and Prof. John Shi. This report was reviewed by members of the working group before being made available to IAEG-SDGs at its ninth meeting in March 2019. Content 1 PREAMBLE ................................................................................................................................. 3 1.1 Importance of geospatial data to SDGs ............................................................................................... 3 1.2 Scope of this report ............................................................................................................................. 3 2 GLOBAL AND COMPLEMENTARY GEOSPATIAL DATASETS ....................................... 4 2.1 National versus international (global) mapping initiatives .................................................................. 4 2.1.1 Topographic maps and Digital Elevation Models .................................................................................. 4 2.1.2 Satellite Image Data ............................................................................................................................. -

Deriving Incline for Street Networks from Voluntarily Collected GPS Traces
Methods of Geoinformation Science Institute of Geodesy and Geoinformation Science Faculty VI Planning Building Environment MASTER’S THESIS Deriving incline for street networks from voluntarily collected GPS traces Submitted by: Steffen John Matriculation number: 343372 Email: [email protected] Supervisors: Prof. Dr.-Ing. Marc-O. Löwner (TU Berlin) Dr.-Ing. Stefan Hahmann (Universität Heidelberg) Submission date: 24.07.2015 in cooperation with: GIScience Group Institute of Geography Faculty of Chemistry and Earth Sciences Declaration of Authorship I, Steffen John, declare that this thesis titled, 'Deriving incline for street networks from voluntarily collected GPS traces’ and the work presented in it are my own. I confirm that: This work was done wholly or mainly while in candidature for a research degree at this Uni- versity. Where any part of this thesis has previously been submitted for a degree or any other qualifi- cation at this University or any other institution, this has been clearly stated. Where I have consulted the published work of others, this is always clearly attributed. Where I have quoted from the work of others, the source is always given. With the exception of such quotations, this thesis is entirely my own work. I have acknowledged all main sources of help. Where the thesis is based on work done by myself jointly with others, I have made clear exact- ly what was done by others and what I have contributed myself. Signed: Date: ii Abstract The knowledge of incline is useful for many use-cases in navigation for electricity-powered vehicles, cyclists or mobility-restricted people (e.g. -

By the Great Horn Spoon! Chapters 1&2
By the © Scisetti Alfio © Scisetti Great Horn Spoon! by Sid Fleischman AR level 5.1 Lexile Level 730 Guiding Reading Level V Anything written in blue in this Prepare your notebook document is a The first page of your notebook gets lots of link to a wear & tear, so go to the 2nd page and start website—just numbering the pages, including the backs. click on it. Number them up to page 6. The 1st numbered page will be your title page. Table of contents Go to page number 3 and label it “Table of Glossary Contents.” As you answer questions and do There will be words throughout the book you’ll be activities in this document, continue to adding to a glossary. You’ll also look up the number the pages in your notebook and add definitions of those words. Go to the back of your them to your table of contents. notebook and count inward 5 pages. Label this page, “Glossary.” Use a post-it note to make a tab for this page so it’s easy to find. You’ll be Map it out numbering these pages and adding them to your Print the map of North and South America table of contents last. from page 13 of this document. You’ll be labeling places mentioned throughout the book on this map. Tape or glue the map to page 6. Whenever you can, buy a copy of any book you’re reading for an assignment. That way, you can highlight important parts and write notes in the margins. -

Social Media Identity Deception Detection: a Survey
Social Media Identity Deception Detection: A Survey AHMED ALHARBI, HAI DONG, XUN YI, ZAHIR TARI, and IBRAHIM KHALIL, School of Computing Technologies, RMIT University, Australia Social media have been growing rapidly and become essential elements of many people’s lives. Meanwhile, social media have also come to be a popular source for identity deception. Many social media identity deception cases have arisen over the past few years. Recent studies have been conducted to prevent and detect identity deception. This survey analyses various identity deception attacks, which can be categorized into fake profile, identity theft and identity cloning. This survey provides a detailed review of social media identity deception detection techniques. It also identifies primary research challenges and issues in the existing detection techniques. This article is expected to benefit both researchers and social media providers. CCS Concepts: • Security and privacy ! Social engineering attacks; Social network security and privacy. Additional Key Words and Phrases: identity deception, fake profile, Sybil, sockpuppet, social botnet, identity theft, identity cloning, detection techniques ACM Reference Format: Ahmed Alharbi, Hai Dong, Xun Yi, Zahir Tari, and Ibrahim Khalil. 2021. Social Media Identity Deception Detection: A Survey . ACM Comput. Surv. 37, 4, Article 111 (January 2021), 35 pages. https://doi.org/10.1145/ 1122445.1122456 1 INTRODUCTION Social media are web-based communication tools that facilitate people with creating customized user profiles to interact and share information with each other. Social media have been growing rapidly in the last two decades and have become an integral part of many people’s lives. Users in various social media platforms totalled almost 3.8 billion at the start of 2020, with a total growth of 321 million worldwide in the past 12 months1. -
Headwaters Tmt Must Read List Best Articles from the Week of August 3Rd, 2015
HEADWATERS TMT MUST READ LIST BEST ARTICLES FROM THE WEEK OF AUGUST 3RD, 2015 HEADWATERS TMT MUST READ LIST – BEST ARTICLES FROM THE WEEK OF AUGUST 3RD, 2015 Deal News Microsoft & Salesforce / Informatica – The leveraged buyout of Informatica Corp. reflects the ways in which the entire business software market is being reshaped by the importance of data. Microsoft Corp. and Salesforce.com Inc. joined private-equity investors Permira Advisers LLC and the Canada Pension Plan Investment Board in the roughly $5.3 billion deal to take private, as the Wall Street Journal reported on Thursday. Informatica has delisted from the Nasdaq and also retired it’s INFA ticker. The company, founded in 1993, had revenue of about $1 billion last year, and grew 11 percent, according to the WSJ. That growth reflects strong demand among businesses for its services, which help companies organize and analyze broad swaths of information, the WSJ says. (WSJ) Daimler, BMW & Audi / Nokia HERE – BMW AG, Audi AG and Daimler AG will buy Nokia Oyj’s digital-map unit for 2.8 billion euros ($3.1 billion) to gain technology for connected cars that will eventually be the basis for self-driving vehicles. The world’s three largest makers of luxury cars will each acquire an equal share of Nokia’s HERE division, and the transaction is expected to be completed in the first quarter of next year, they said Monday. Nokia said its net proceeds on the sale will total slightly more than 2.5 billion euros. While there has previously been limited cooperation on auto parts, a joint acquisition on this scale involving BMW, Volkswagen AG’s Audi division and Mercedes-Benz owner Daimler is unprecedented.