Detecting and Analyzing Insecure Component Usage∗
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Comodo System Cleaner Version 3.0
Comodo System Cleaner Version 3.0 User Guide Version 3.0.122010 Versi Comodo Security Solutions 525 Washington Blvd. Jersey City, NJ 07310 Comodo System Cleaner - User Guide Table of Contents 1.Comodo System-Cleaner - Introduction ............................................................................................................ 3 1.1.System Requirements...........................................................................................................................................5 1.2.Installing Comodo System-Cleaner........................................................................................................................5 1.3.Starting Comodo System-Cleaner..........................................................................................................................9 1.4.The Main Interface...............................................................................................................................................9 1.5.The Summary Area.............................................................................................................................................11 1.6.Understanding Profiles.......................................................................................................................................12 2.Registry Cleaner............................................................................................................................................. 15 2.1.Clean.................................................................................................................................................................16 -

HTTP Cookie - Wikipedia, the Free Encyclopedia 14/05/2014
HTTP cookie - Wikipedia, the free encyclopedia 14/05/2014 Create account Log in Article Talk Read Edit View history Search HTTP cookie From Wikipedia, the free encyclopedia Navigation A cookie, also known as an HTTP cookie, web cookie, or browser HTTP Main page cookie, is a small piece of data sent from a website and stored in a Persistence · Compression · HTTPS · Contents user's web browser while the user is browsing that website. Every time Request methods Featured content the user loads the website, the browser sends the cookie back to the OPTIONS · GET · HEAD · POST · PUT · Current events server to notify the website of the user's previous activity.[1] Cookies DELETE · TRACE · CONNECT · PATCH · Random article Donate to Wikipedia were designed to be a reliable mechanism for websites to remember Header fields Wikimedia Shop stateful information (such as items in a shopping cart) or to record the Cookie · ETag · Location · HTTP referer · DNT user's browsing activity (including clicking particular buttons, logging in, · X-Forwarded-For · Interaction or recording which pages were visited by the user as far back as months Status codes or years ago). 301 Moved Permanently · 302 Found · Help 303 See Other · 403 Forbidden · About Wikipedia Although cookies cannot carry viruses, and cannot install malware on 404 Not Found · [2] Community portal the host computer, tracking cookies and especially third-party v · t · e · Recent changes tracking cookies are commonly used as ways to compile long-term Contact page records of individuals' browsing histories—a potential privacy concern that prompted European[3] and U.S. -

Detecting and Analyzing Insecure Component Integration
Taeho Kwon December 2011 Computer Science Detecting and Analyzing Insecure Component Integration Abstract Component technologies have been widely adopted for designing and engineering software ap- plications and systems, which dynamically integrate software components to achieve desired func- tionalities. Engineering software in a component-based style has significant benefits, such as im- proved programmer productivity and software reliability. To support component integration, oper- ating systems allow an application to dynamically load and use a component. Although developers have frequently utilized such a system-level mechanism, programming errors can lead to insecure component integration and serious security vulnerabilities. The security and reliability impact of component integration has not yet been much explored. This dissertation systematically investigates security issues in dynamic component integration and their impact on software security. On the conceptual level, we formulate two types of insecure component integration—unsafe component loading and insecure component usage—and present practical, scalable techniques to detect and analyze them. Our techniques operate directly on soft- ware binaries and do not require source code. On the practical level, we have used them to discover new vulnerabilities in popular, real-world software, and show that insecure component integration is prevalent and can be exploited by attackers to subvert important software and systems. Our research has had substantial practical impact and helped -

Lisans Gerektirmeyen Programlar Lisans Gerektirmeyen Programlar
Lisans Gerektirmeyen Programlar Lisans Gerektirmeyen Programlar GNU Özgür Belgeleme Lisansı.Bu lisansın amacı, bir kullanıcı kılavuzuna, bir ders kitabı veya başka işlevsel ve faydalı bir belgeye, herkesin, etkili bir kullanım hakkıyla, ticari veya gayri-ticari, değiştirerek ya da olduğu gibi, almak ve tekrar dağıtmak özgürlüğü anlamında, serbest kullanım hakkı vermektir.İkincil olarak, bu Lisans, yazar ve yayıncının, başkaları tarafından yapılan değişiklikler sebebiyle sorumlu olduklarını düşünmeden, bir bakıma yaptıkları işten saygınlık kazanmalarını da sağlar 3D Graphics -------------------------- 3Delight Free - http://www.3delight.com/index.htm Anim8or - http://www.anim8or.com/ Blender - http://www.blender3d.org/ Now3D - http://digilander.libero.it/giulios/Eng/homepage.htm OpenFX - http://www.openfx.org POV-Ray - http://www.povray.org/ Terragen - http://www.planetside.co.uk/terragen/ Toxic - http://www.toxicengine.org/ Wings 3D - http://www.wings3d.com/ Anti-spam programs ----------------------------- K9 - http://www.keir.net/k9.html MailWasher- http://www.mailwasher.net/ POPFile - http://popfile.sourceforge.net/ SpamBayes - http://spambayes.sourceforge.net/ SpamPal - http://www.spampal.org/ Anti-Spyware ---------------------------------------- Ad-aware - http://www.lavasoft.de/software/adaware/ Bazooka - http://www.kephyr.com/spywarescanner/index.html Hijackthis - http://http://ctech.link/remove-spyware Microsoft Defender (Beta 2) - http://www.microsoft.com/athome/security/s...re/default.mspx SpyBot Search & Destroy - http://spybot.safer-networking.de/ -

Web Browser Free Download for Mobile
Web browser free download for mobile click here to download Experience a fast, smart and personal Web. Firefox is the independent, people-first browser made by Mozilla, voted the Most Trusted Internet Company for. This is no doubt the fastest browser ever Over 1,, Download Web Explorer rewrite the stock rom of Android Browser and eliminate unnecessary. Opera Mini. Opera Mini is one of the world's most popular web browsers that works on almost any phone or tablet. Discover new content and speed up slow connections with our fast mobile browsers for Android and iOS. Opera is a fast and secure browser. Developed in Europe, used by millions around the world. Now with a built-in ad blocker and free VPN. Outfoxin' the Trackers: Android Private Browsing with Firefox Focus In our everyday quests through the wild untamed country of the web, we need ways to. Mobile phones and tablets will come with a browser, but depending Need a Mobile Web Browser? Price: Free (UC web Download Page). Download your free mobile browser now: Use Dolphin's tabbed browsing, share any web content instantly to your favorite social networks and send between. Firefox for Android, free and safe download. Firefox latest version: Feels like Firefox, just mobile. What's the Best Browser for Web Developers? Read more. If you're looking for am alternative mini web browser for your mobile phone It's available for free on the Opera Mini Download Page or directly. Full PC-style browsing on all types of mobile phones; Web content is never reformatted, repurposed or removed; Loads pages faster than. -

Freeware-List.Pdf
FreeWare List A list free software from www.neowin.net a great forum with high amount of members! Full of information and questions posted are normally answered very quickly 3D Graphics: 3DVia http://www.3dvia.com...re/3dvia-shape/ Anim8or - http://www.anim8or.com/ Art Of Illusion - http://www.artofillusion.org/ Blender - http://www.blender3d.org/ CreaToon http://www.creatoon.com/index.php DAZ Studio - http://www.daz3d.com/program/studio/ Freestyle - http://freestyle.sourceforge.net/ Gelato - http://www.nvidia.co...ge/gz_home.html K-3D http://www.k-3d.org/wiki/Main_Page Kerkythea http://www.kerkythea...oomla/index.php Now3D - http://digilander.li...ng/homepage.htm OpenFX - http://www.openfx.org OpenStages http://www.openstages.co.uk/ Pointshop 3D - http://graphics.ethz...loadPS3D20.html POV-Ray - http://www.povray.org/ SketchUp - http://sketchup.google.com/ Sweet Home 3D http://sweethome3d.sourceforge.net/ Toxic - http://www.toxicengine.org/ Wings 3D - http://www.wings3d.com/ Anti-Virus: a-squared - http://www.emsisoft..../software/free/ Avast - http://www.avast.com...ast_4_home.html AVG - http://free.grisoft.com/ Avira AntiVir - http://www.free-av.com/ BitDefender - http://www.softpedia...e-Edition.shtml ClamWin - http://www.clamwin.com/ Microsoft Security Essentials http://www.microsoft...ity_essentials/ Anti-Spyware: Ad-aware SE Personal - http://www.lavasoft....se_personal.php GeSWall http://www.gentlesec...m/download.html Hijackthis - http://www.softpedia...ijackThis.shtml IObit Security 360 http://www.iobit.com/beta.html Malwarebytes' -

Возможности КИБ Searchinform
SEARCHINFORM DLP CAPABILITIES 2 Contents SearchInform DLP Capabilities ............................................................................... 3 1 Capabilities of EndpointController Interception Modules for Windows ............. 3 2 Capabilities of NetworkController Interception Modules .................................. 8 3 Capabilities of NetworkController Integration with Mail Servers, Lync (Skype for Business) and ISA/TMG .................................................................................. 10 4 Capabilities of EndpointController Interception Modules for Linux (Ubuntu, CentOS, Rosa, Gos, Astra) .................................................................................... 11 5 Blocking Capabilities in SearchInform DLP .................................................... 12 5.1 Blocking at the Level of Agent ....................................................................... 12 5.2 Blocking at the Level of Network ................................................................... 13 5.3 Blocking Email at the Level of Workstation or Mail Server (Agent) ..................... 14 6 Protection of Data at Rest .............................................................................. 15 3 SEARCHINFORM DLP CAPABILITIES SearchInform Data Loss Prevention (SearchInform DLP) is used to collect and analyse information flows within the local computer network. Data can be captured in two ways, depending on the server component: SearchInform EndpointController or SearchInform NetworkController. Server components -
Linkman PDF Manual
Outertech Linkman Linkman is a bookmark management solution which supports 10 different browsers and integrates with Firefox, Internet Explorer and Maxthon. Linkman calls upon many powerful features that replace the browser's native URL management and allow to browse faster and more efficiently. To give you a better impression a Linkman tutorial video can be watched at http://linkmanvideo.outertech.com You can choose between two editions. Linkman Lite (Freeware) http://linkmanlite.outertech.com Linkman Lite is free for private non-commercial use as well as for use in charity organizations and educational use. Private use is only when used by individuals at home on their private PC. Educational use is by students for education in school or university. Linkman Pro ($25 | EUR19 for single computer license) http://linkmanpro.outertech.com This edition is intended for the professional user. Linkman Pro contains all features of Linkman Lite. In addition these abilities are included: * Synchronize links between two (or more) computers * Ability to check URLs for dead links, intelligent (only major) content changes, and page movements * Add all links on a single webpage * Improved keyword features (e.g. Keyword List) * Replace feature * Improved Database backup * Retrieve URL meta tags * Editable Export Templates (XML, TSV...) with UTF8 support * Optional installation on USB sticks for mobile usage Linkman 3 Table of Content Foreword 0 Part I Introduction 7 1 .O...v..e...r.v..i.e...w.............................................................................................................................. 7 2 .W...h...a..t.'.s.. .n..e..w............................................................................................................................ 9 3 ...O...t.h..e...r. .s..o..f..t.w...a..r.e................................................................................................................... 21 Part II Frequently Asked Questions 23 Part III Tutorial 27 1 ...F..i.r..s..t. -

Apex Filters 18.2.0.0 User Guide 26 Jan 2021 Table of Contents
Apex Filters 18.2.0.0 User Guide 26 Jan 2021 Table of Contents Chapter 1: Apex filters..............................................................................................................4 Boolean operators used in filter expressions......................................................................... 5 app...........................................................................................................................................6 browser....................................................................................................................................7 browserPlatform.......................................................................................................................8 browserVersion........................................................................................................................9 dataSource............................................................................................................................ 10 ethertype................................................................................................................................11 fixRequest..............................................................................................................................13 fixResponse...........................................................................................................................14 flowIdx....................................................................................................................................15 -
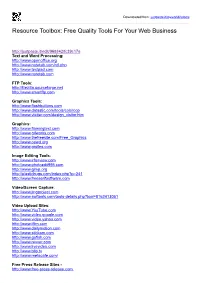
Resource Toolbox: Free Quality Tools for Your Web Business
Downloaded from: justpaste.it/myworld2utools Resource Toolbox: Free Quality Tools For Your Web Business http://justpaste.it/edit/968842/fc39c17a Text and Word Processing: http://www.openoffice.org http://www.notetab.com/n tl.php http://www.textpad.com http://www.notetab.com FTP Tools: http://filezilla .sourceforge.net http://www.smartftp.com Graphics Tools: http://www.flashbu ttons.com http://www.datastic.com/tools /colorcop http://www.vletter.com/design_visitor.ht m Graphics: http://www. flamingtext.com http://www.gifworks.com http://www.thefreesite.com /Free_Graphics http://www.oswd.org http://www.grsites.co m Image Editing Tools: http://www.irfanview.co m http://www.photoedit995. com http://www.gimp.org http://plasticbugs.co m/index.php?p=241 http://www.freeserifsoftware.com Video/Screen Capture: http://www.jingproject.co m http://www.swftools.com/to ols-details.php?tool=8162413051 Video Upload Sites: http://www.YouTube.c om http://www.video.google.c om http://www.video.yahoo.com http://www.ifilm.com http://www.dailymoti on.com http://www.stickam.com http://www.gofish.com http://www.revver.com http://www.livevideo.co m http://www.blip.tv http://www.metac afe.com/ Free Press Release Sites - http://www.free-press-release .com http://www.24-7pressrelease.com http://www.i-newswire.com http://www.pr.com http://www.pressmethod.com http://www.1888pressrelease.com http://www.prbuzz.com http://www.prleap.com http://www.clickpress.com http://www.prfree.com http://www.addpr.com http://www.eworldwire.com http://www.prurgent.com http:///www.theopenpress.com -

Build Muscle in Four Easy Steps!
World’s Safest Car! How To "Clean Up" Messy Hard Drive? Build Muscle In Four Easy Steps! The World's Most Expensive Car! Software Categories AntiVirus Audio & Video Business/Organize Desktop Enhancements Developer Tools Drivers Games Hot! Graphics/Design Home & Education Internet Network Programming Screensavers Security/Privacy Hot! Utilities Featured Freeware Rainmeter 2.0 A customizable performance meter, displays the CPU load, memory utilization, much more. Download Now CheatBook Issue 02/2011 Grab the latest cheats and hints for PC and console games. Download Now Site Links New Releases Top 100 File Bar RSS Feeds Free Tech Magazines Submit Software Link to Us Partners Resources Check Your PC for Errors Top 100 Game Sites Top 10 Banned iPhone Applications Weekly Poll How many contacts do you have in your cell phone? 1-10 11-20 21-50 51-75 76-100 100+ vote 94 Vote View Results View All Polls FreewareFiles Express delivers the Hottest Downloads right to your Inbox! Sign up Now! Next Issue: 02-11-2011 1 subscribe Privacy Policy | Archives | Top Graphics Top Business Weekly Polls Download Manager FileBar Driver Scan Top Top Top Top Top Top Internet Top Game Games Security Audio/Video Desktop Utilities Tools Sites Home : Internet Tools : Top 100 Internet Tools Downloads Top 100 Downloads: Internet Program Name Downloads Youtube Video Downloader 2.5.4 1. 866101 Software to download and convert YouTube videos. Download Accelerator Plus 9.5.0.3 2. 516986 Push your downloads into High- speed with DAP. Internet Explorer for Windows XP 7.0 3. The latest release of Microsoft´s 237899 popular Internet Explorer Web browser. -

Top Ten Browser Download Download Browser for Windows 10 - Best Software & Apps
top ten browser download Download Browser For Windows 10 - Best Software & Apps. Google Chrome is a free cross-platform web browser that launched for Microsoft Windows platforms in 2008, preceding later releases on Mac, Linux, and mobile. Adobe Flash Player. Important note: as of 2021, this software has been discontinued. The download button will redirect to Adobe Flash Player EOL General Information Page.Adobe Flash Player is a comprehensive tool to create, edit, and view. Mozilla Firefox. Free open-source browser. Mozilla Firefox is a free web browser for Windows and Mac operating systems. Launched by the Mozilla Foundation in 2003, the open-source program has. Google Chrome (64-bit) Google Chrome is one of the best browsers. Google Chrome is one of the leading internet browsers, and for good reason. You’ve just bought a new computer and you are wondering which browser to use. Avast Free Antivirus. A free and safe antivirus tool. Avast Free Antivirus is a free security software that you can download on your Windows device. The latest version of the program includes multiple scanning. UC Browser. A light browser that’s free. UC Browser is a web browser built for low-end computers and slow connections. It comes with a dedicated download manager, cloud sync, theme customization. Opera Browser. A fast next-generation web browser! Opera is one of the oldest browsers in the market and runs on the versatile Google Chromium system. With a simple interface and plenty of features, Opera. Google Play Chrome Extension. Play Store integrated right in the browser! Google Play is one of the most popular add-ons/extensions for the Google Chrome browser.