Electronic Mail Solutions
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Cathedral and the Bazaar Eric Steven Raymond Thyrsus Enterprises [
The Cathedral and the Bazaar Eric Steven Raymond Thyrsus Enterprises [http://www.tuxedo.org/~esr/] <[email protected]> This is version 3.0 Copyright © 2000 Eric S. Raymond Copyright Permission is granted to copy, distribute and/or modify this document under the terms of the Open Publication License, version 2.0. $Date: 2002/08/02 09:02:14 $ Revision History Revision1.57 11September2000 esr New major section “How Many Eyeballs Tame Complexity”. Revision1.52 28August2000 esr MATLAB is a reinforcing parallel to Emacs. Corbatoó & Vyssotsky got it in 1965. Revision1.51 24August2000 esr First DocBook version. Minor updates to Fall 2000 on the time-sensitive material. Revision1.49 5May2000 esr Added the HBS note on deadlines and scheduling. Revision1.51 31August1999 esr This the version that O’Reilly printed in the first edition of the book. Revision1.45 8August1999 esr Added the endnotes on the Snafu Principle, (pre)historical examples of bazaar development, and originality in the bazaar. Revision 1.44 29 July 1999 esr Added the “On Management and the Maginot Line” section, some insights about the usefulness of bazaars for exploring design space, and substantially improved the Epilog. Revision1.40 20Nov1998 esr Added a correction of Brooks based on the Halloween Documents. Revision 1.39 28 July 1998 esr I removed Paul Eggert’s ’graph on GPL vs. bazaar in response to cogent aguments from RMS on Revision1.31 February101998 esr Added “Epilog: Netscape Embraces the Bazaar!” Revision1.29 February91998 esr Changed “free software” to “open source”. Revision1.27 18November1997 esr Added the Perl Conference anecdote. Revision 1.20 7 July 1997 esr Added the bibliography. -

Email Issues
EMAIL ISSUES - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - TABLE OF CONTENTS NEW POLICY WITH RESPECT TO EMAIL ADDRESSES A NECESSARY EMAIL SETTING WHY OUR EMAILS POSSIBLY ARRIVED LATE OR NOT AT ALL STOP USING YAHOO, NETZERO, AND JUNO EMAIL PROVIDERS - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - NEW POLICY WITH RESPECT TO EMAIL ADDRESSES: There are two important issues here. FIRST, members must not supply CFIC with their company email addresses. That is, companies that they work for. (If you own the company, that's different.) All email on a company's server can be read by any supervisor. All it takes is one pro vaccine activist to get hold of our mobilization alerts to throw a monkey wrench in all of our efforts. Thus, do not supply me with a company email address. We can help you get an alternative to that if necesary. SECONDLY, CFIC needs members' email addresses to supply important information to mobilize parents to do things that advances our goal to enact our legislative reforms of the exemptions from vaccination. That has always been CFIC's sole agenda. CFIC has been able to keep the membership fee to zero because we don't communicate via snail mail. But people change their addresses frequently and forget to update CFIC. When this happens over the years, that member is essentually blind and deaf to us, and is no longer of any value to the coalition---your fellow parents. Therefore, it warrants me to require that members supply CFIC with their most permanent email account. That means the email address of the company in which you are paying a monthly fee for internet access, be it broadband or dialup service. -

Here Is a Step by Step Example on How to Set up Outlook 2010 for Your Email Address
Here is a step by step example on how to set up Outlook 2010 for your email address. If you are using some other mail client, (ie. Outlook Express, Microsoft Mail) you can still use the information about the name of the POP3 server and the SMTP server. In any case, make sure that you have created an account that does not leave the messages on the server. Step One: With Outlook open, click on the file tab in the upper left screen area. This is what you will see. Now, click on the +Add Account button. (look at the picture and then page down for step two) Step 2: After you clicked the +Add Account button, this window will pop up. When you first open this window the E-Mail Account option is checked. This is not what we want. Go down to the bottom of the window and check Manually configure server settings or additional server types. Then, click the Next> button at the bottom of the window. (look at the picture and then page down for step three) Step 3: After you clicked the Next > button, this window will pop up. This time, the correct selection is already chosen. If, for some reason it is not checked, please check the Internet E-Mail and then click the Next> button at the bottom of the window. look at the picture and then page down for step four) Step 4: After you clicked the Next> button, this window will pop up. User Informatio n: This window is set up for the Red Knights Regalia Treasurer. -

Florida Library Directory with Statistics, 2000. INSTITUTION Florida Dept
DOCUMENT RESUME ED 446 777 IR 057 922 AUTHOR Taylor-Furbee, Sondra, Comp.; Kellenberger, Betsy, Comp. TITLE Florida Library Directory with Statistics, 2000. INSTITUTION Florida Dept. of State, Tallahassee. Div. of Library and Information Services. PUB DATE 2000-00-00 NOTE 268p.; For the 1999 directory, see ED 437 953. AVAILABLE FROM For full text: http://librarydata.dos.state.fl.us. PUB TYPE Numerical/Quantitative Data (110) Reference Materials Directories /Catalogs (132) EDRS PRICE MF01/PC11 Plus Postage. DESCRIPTORS Academic Libraries; Elementary Secondary Education; Higher Education; Institutional Libraries; Library Associations; *Library Statistics; *Public Libraries; School Libraries; Special Libraries IDENTIFIERS Florida ABSTRACT This document contains directory and statistical information about libraries in Florida organized in the following sections: (1) "Florida Division of Library and Information Services (DLIS) Library Organizations, Councils, and Associations," including the State Library Council, Library Services & Technology Act Advisory Council, Florida Library Literacy Advisory Council, Florida Library Network Council, DLIS staff directory, DLIS statistics, Florida Library Information Network, library associations, graduate library schools, networks and multitype library cooperatives, and Florida State documents depositories; (2) "Directory of Libraries," including public libraries, academic libraries, special libraries, institutional libraries, and school library media supervisors; (3) "Public Library Data," including a narrative statistical summary and selected historical data; (4) "Public Library Data Table," including access to library service (outlets, square feet, Sunday hours), library staff, librarian salaries, income, expenses, expenses by category, collection, circulation and borrowers, visits/reference/interlibrary loan, programs, and electronic access; (5) "Personnel Index"; and (6) "County Index." (MES) Reproductions supplied by EDRS are the best that can be made from the original document. -
Argosoft Mail Server Pro User Guide
http://www.argosoft.com Argosoft Mail Server Pro User Guide June 2002 1 Introduction Thank you for choosing Argosoft Mail Server Pro. This lightweight and extremely affordable mail server is robust, stable, easy to configure, easy to manage and is fully capable of competing head to head with any mail server on the market. It can perform all basic e-mail tasks, and much more. It is fully functional mail system, which supports most popular protocols, SMTP, POP3, Finger, and has a built-in Web server, to give users quick and easy access to their email via any Web browser, which supports HTTP 1.0 or later. The web interface can also be used to administer the mail server. While this easy to use mail server is pretty much obvious in terms of use there are few little things that even a seasoned e-mail expert may not stumble across immediately. This document is basic guide to getting started! Features • Has true support of multiple domains - you can create accounts with the same name, which belong to different domains • Supports multiple IP homes (virtual domains) • Has built in mailing list server • Has WAP interface • Allows setup of domain administrators - users who can change domain related information via the Web interface; • Filtering of mail according to IP addresses of server which attempts to relay mail to local users • ORDB and MAPS support • Supports distribution lists; • Supports auto responders; • Supports basic filters; • Unlimited message size (there is a limit of 5 Megs for freeware version); • Can listen on single IP address, rather than all addresses available on your computer; • Has built-in web server. -

In the United States District Court for the District of Puerto Rico
Case 3:11-cv-02271-GAG-BJM Document 467 Filed 04/03/13 Page 1 of 10 IN THE UNITED STATES DISTRICT COURT FOR THE DISTRICT OF PUERTO RICO W HOLDING COMPANY, INC., et al., Plaintiffs, v. CHARTIS INSURANCE COMPANY OF PUERTO RICO, Defendant; FEDERAL DEPOSIT INSURANCE CORPORATION, as receiver of Westernbank Puerto Rico, Plaintiff-Intervenor, Civil No. 11-2271 (GAG/BJM) v. FRANK STIPES GARCIA, et al., Cross-Claim Defendants, CHARTIS INSURANCE COMPANY OF PUERTO RICO, Previously-Joined Defendant, and MARLENE CRUZ CABALLERO, et al., Additional Defendants. ORDER GOVERNING DISCOVERY OF ELECTRONICALLY STORED INFORMATION FROM FDIC-R I. Preamble and Definitions For the reasons stated in the accompanying opinion, the parties to this action are hereby ordered to comply with the following as a default protocol for obtaining certain electronically stored information (“ESI”) from the Federal Deposit Insurance Corporation in its capacity as receiver of Westernbank Puerto Rico (“FDIC-R”). FDIC-R and any other party may privately Case 3:11-cv-02271-GAG-BJM Document 467 Filed 04/03/13 Page 2 of 10 W Holding Co. v. Chartis Ins. Co. of P.R. (FDIC v. Stipes Garcia) Page 2 Civil No. 11-2271 (GAG/BJM) — Order Governing Discovery of ESI from FDIC-R agree to alter these terms as permitted by Fed. R. Civ. P. 29(b). In the absence of agreement, however, this order will control until it is amended or vacated by the court. The following terms are given special meanings: Native File means ESI in the electronic format of the application in which such ESI is normally created, viewed, and/or modified. -

Downloadable Email Program for My Pc 32 Best Free Email Clients
downloadable email program for my pc 32 Best Free Email Clients. Here are 32 best free email client software . These let you manage and access all of your email accounts in one single place easily. All these email client software are completely free and can be downloaded to Windows PC. These free software offer various features, like: can be used with IMAP, SMTP, POP3 and Gmail, keeps your emails safe and secure, lets you open various emails simultaneously, provide protection from spam, lets you view your emails offline, manage and access all of your email accounts in one single place, supports PH, LDAP, IMAP4, POP3 and SMPT mail protocols etc. So, go through this list of free email client software and see which ones you like the most. Thunderbird. Thunderbird is a free and handy email client software for your computer. It can be used with IMAP, SMTP, POP3 and Gmail. It will also work with email accounts provided by MS Exchange Server. The user interface of Thunderbird is tabbed. It lets you open various emails simultaneously. Thunderbird keeps your emails safe and secure. It also has special filters for filtering the mail. Windows Live Mail. Windows Live Mail is a free email client for your computer. It works with various email accounts. It lets you access Yahoo, Gmail, Hotmail and emails from different servers which supports POP3 and SMTP. Its security features are excellent it will also provide protection from spam. You can also view your emails offline in this freeware. Zimbra Desktop. Zimbra Desktop is a free email client. -

The Cathedral and the Bazaar
The Cathedral and the Bazaar Linux is subversive. Who would have thought even five years ago (1991) that a world- class operating system could coalesce as if by magic out of part-time hacking by several thousand developers scattered all over the planet, connected only by the tenuous strands of the Internet? Certainly not I. By the time Linux swam onto my radar screen in early 1993, I had already been involved in Unix and open-source development for ten years. I was one of the first GNU contributors in the mid-1980s. I had released a good deal of open-source software onto the net, developing or co-developing several programs (nethack, Emacs's VC and GUD modes, xlife, and others) that are still in wide use today. I thought I knew how it was done. Linux overturned much of what I thought I knew. I had been preaching the Unix gospel of small tools, rapid prototyping and evolutionary programming for years. But I also believed there was a certain critical complexity above which a more centralized, a priori approach was required. I believed that the most important software (operating systems and really large tools like the Emacs programming editor) needed to be built like cathedrals, carefully crafted by individual wizards or small bands of mages working in splendid isolation, with no beta to be released before its time. Linus Torvalds's style of development—release early and often, delegate everything you can, be open to the point of promiscuity—came as a surprise. No quiet, reverent cathedral-building here—rather, the Linux community seemed to resemble a great babbling bazaar of differing agendas and approaches (aptly symbolized by the Linux archive sites, who'd take submissions from anyone) out of which a coherent and stable system could seemingly emerge only by a succession of miracles. -

EDUCATION; Board 04 PROJECT TEAMS (TEACHER EDUCATION at AKRON for MATH- MEDICAL; SOCIAL SCIENCES EMATICS and SCIENCE)
Program Abstracts A-7. relatively low SAT-Math scores. Such accommodations, while upholding academic POSTER SESSION standards and admissions policies, would include frank and early advising of at-risk students and early and continuous remedial assistance. BIOLOGICAL; EDUCATION; Board 04 PROJECT TEAMS (TEACHER EDUCATION AT AKRON FOR MATH- MEDICAL; SOCIAL SCIENCES EMATICS AND SCIENCE). Annabelle Foos1, [email protected]. Katharine Owens2, [email protected]. David McConnell1, [email protected]. Sandy 9:00 -10:00 AM Coyner2, [email protected]. Francis Broadway2, [email protected]. The University of Akron, department of Geology, College of Education, Akron TOLERTON & HOOD HALL OF SCIENCE OH 44325-4101. Project TEAMS addressed the need at The University of Akron forfocused dialogue Board 01 DEVELOPMENT OF A WEB-SITE FOR EDUCATIONAL PURPOSES. on national standardsfor science and mathematics teaching, science and mathemat- Frederick J. Kluth, [email protected]. 1060 DeLeone Dr., Kent OH 44240-2026. ics content course development, and incorporation of inquiry-based methods in The value of the Internet has been widely touted with demands made for computer undergraduate science and mathematics courses. Faculty from institutions of higher equipment for the classroom. Much emphasis has been placed on the development education in the local area, science and mathematics teachers from grades 6-12 of physical infrastructure for the classroom with less on the content to be presented. schools, and UA faculty members came together for focused discussions on these The purpose of this paper is to focus on the development of content. The hypothesis topics. Initially, a series of "brown bag" luncheon seminars were held. -
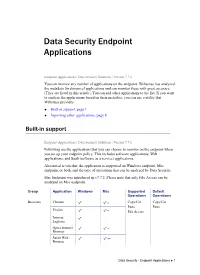
Data Security Endpoint Applications
Data Security Endpoint Applications Endpoint Applications | Data Security Solutions | Version 7.7.x You can monitor any number of applications on the endpoint. Websense has analyzed the metadata for dozens of applications and can monitor these with great accuracy. (They are listed in this article.) You can add other applications to the list. If you want to analyze the applications based on their metadata, you can use a utility that Websense provides. Built-in support, page 1 Importing other applications, page 8 Built-in support Endpoint Applications | Data Security Solutions | Version 7.7.x Following are the applications that you can choose to monitor on the endpoint when you set up your endpoint policy. This includes software applications, Web applications, and SaaS (software as a service) applications. Also noted is whether the application is supported on Windows endpoint, Mac endpoint, or both, and the type of operations that can be analyzed by Data Security. Mac Endpoint was introduced in v7.7.2. Please note that only File Access can be analyzed on Mac endpoint. Group Application Windows Mac Supported Default Operations Operations Browsers Chrome * Copy/Cut Copy/Cut Paste Paste Firefox * File Access Internet Explorer Opera Internet * Browser Safari Web ** Browser Data Security - Endpoint Applications 1 Data Security Endpoint Applications Group Application Windows Mac Supported Default Operations Operations CD Burners Acoustica Copy/Cut File Access MP3 CD Paste Burner File Access Alcohol 120% Alcohol Launcher CD Mate Disk Utility -
Malware: Computer Viruses, Spyware, and Key-Loggers
Certificates for cs.washington.edu 1 Certificates for GMail Important fields: Testing SSL Configuration (1) 3 Client completed verification of received certificate chain Testing SSL Configuration (2) 4 Received certificate chain (two certificates) Size of received certificate chain Testing SSL Configuration (3) 5 Issued session identifier (Session-ID) for stateful TLS resume. Example from “High Performance Browser Networking” Where to Use SSL? 6 Login page? Where else? What about JavaScript includes? Image includes? Why not encrypt everything? Where to Use SSL? 7 Some browsers may not support SSL SSL may decrease performance somewhat. If users are downloading large, public files, there may be a system burden to encrypt these each time. You will probably want the home page accessible via HTTP, so that users don't have to remember to type https to get to it. Firesheep (2010) 8 Assume you are using the facebook.com site over an unsecured Wi-Fi network such as in shopping malls and coffee shops. When you visit the Facebook site, you are required to enter the username and password. When you send that request and on successful login, Facebook sends you an authentication token in the clear which is then sent every time you browse Facebook pages Firesheep 9 Facebook Switches to HTTPS in 2012 10 Lab-2 11 Part 1 Part 2 Black-box fuzzing is far C programming is tricky from easy Bounds are far from obvious even when Very little insight into reasoning about a short program behavior function Makes you appreciate Makes you appreciate programming in Java or having access to C# where array accesses source code! are checked at runtime! Lab-2: Survey 12 Part 1 Part 2 A. -
Title Pub Date Note Abstract
DOCUMENT RESUME ED 366 244 HE 027 085 TITLE 20 Years: Putting It All Together. Proceedings of the Annual Conference of the North East Association for Institutional Research (20th, Bolton Landing, New York, November 6-9, 1993). INSTITUTION North East Association for InsC'utional Research. PUB DATE Nov 93 NOTE 337p. PUB TYPE Collected Works Conference Proceedings (021) EDRS PRICE MF01/PC14 Plus Postage. DESCRIPTORS Alumni; *College Administration; College Freshmen; Crime; Data; *Data Analysis; Demography; Educational Finance; Electronic Mail; Enrollment Trends; Federal Aid; Financial Exigency; *Higher Education; Institutional Mission; *Institutional Research; Outreach Programs; Program Evaluation; *Research Methodology; School Holding Power; Sex Differences; Teacher Salaries; Telecommunications IDENTIFIERS Internet; Suffolk County Community College NY ABSTRACT This report of the proceedings of a conference on institutional research techniques contains information on the conference and 23 selected papers. Conference information includes the program, a list of steering committee members, and a list of attenders. The following papers are included:(1) "Examples of How Institutional Research Can Help Campus Administrators with Their Survey Research Needs" (Karen W. Bauer) ;(2) "No Pain, No Gain: How One College Emerged Stronger from the Fiscal Crisis" (Craig A. Clagett);(3) "Outreach Programs and Their Varying Impact on Key Market Segments" (David J. Costello) ;(4) "Analytical Techniques for Studying Student Retention" (Anne Marie Delaney);(5) "Designing Alumni Research for Assessment and Planning" (Anne Marie Delaney); (6) "Beyond E-mail: Getting Data from the Internet" (Jim Fergerson); (7)"To Have and To Hold: On the Meaning of 'Retention" (Thomas B. Flaherty and Jennifer A. Brown) ;(8) "Making the Most of the Mission Review: A Topical Case Study" (Eleanor Fujita and Mark Oromaner); (9) "A Review of Reliability, Validity and Useability Considerations in the Use of the Writing Sample as an Index of Program Effect" (Stanley S.