Multiproxy: a Collaborative Approach to Censorship Circumvention
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Uila Supported Apps
Uila Supported Applications and Protocols updated Oct 2020 Application/Protocol Name Full Description 01net.com 01net website, a French high-tech news site. 050 plus is a Japanese embedded smartphone application dedicated to 050 plus audio-conferencing. 0zz0.com 0zz0 is an online solution to store, send and share files 10050.net China Railcom group web portal. This protocol plug-in classifies the http traffic to the host 10086.cn. It also 10086.cn classifies the ssl traffic to the Common Name 10086.cn. 104.com Web site dedicated to job research. 1111.com.tw Website dedicated to job research in Taiwan. 114la.com Chinese web portal operated by YLMF Computer Technology Co. Chinese cloud storing system of the 115 website. It is operated by YLMF 115.com Computer Technology Co. 118114.cn Chinese booking and reservation portal. 11st.co.kr Korean shopping website 11st. It is operated by SK Planet Co. 1337x.org Bittorrent tracker search engine 139mail 139mail is a chinese webmail powered by China Mobile. 15min.lt Lithuanian news portal Chinese web portal 163. It is operated by NetEase, a company which 163.com pioneered the development of Internet in China. 17173.com Website distributing Chinese games. 17u.com Chinese online travel booking website. 20 minutes is a free, daily newspaper available in France, Spain and 20minutes Switzerland. This plugin classifies websites. 24h.com.vn Vietnamese news portal 24ora.com Aruban news portal 24sata.hr Croatian news portal 24SevenOffice 24SevenOffice is a web-based Enterprise resource planning (ERP) systems. 24ur.com Slovenian news portal 2ch.net Japanese adult videos web site 2Shared 2shared is an online space for sharing and storage. -

Poster: Introducing Massbrowser: a Censorship Circumvention System Run by the Masses
Poster: Introducing MassBrowser: A Censorship Circumvention System Run by the Masses Milad Nasr∗, Anonymous∗, and Amir Houmansadr University of Massachusetts Amherst fmilad,[email protected] ∗Equal contribution Abstract—We will present a new censorship circumvention sys- side the censorship regions, which relay the Internet traffic tem, currently being developed in our group. The new system of the censored users. This includes systems like Tor, VPNs, is called MassBrowser, and combines several techniques from Psiphon, etc. Unfortunately, such circumvention systems are state-of-the-art censorship studies to design a hard-to-block, easily blocked by the censors by enumerating their limited practical censorship circumvention system. MassBrowser is a set of proxy server IP addresses [14]. (2) Costly to operate: one-hop proxy system where the proxies are volunteer Internet To resist proxy blocking by the censors, recent circumven- users in the free world. The power of MassBrowser comes from tion systems have started to deploy the proxies on shared-IP the large number of volunteer proxies who frequently change platforms such as CDNs, App Engines, and Cloud Storage, their IP addresses as the volunteer users move to different a technique broadly referred to as domain fronting [3]. networks. To get a large number of volunteer proxies, we This mechanism, however, is prohibitively expensive [11] provide the volunteers the control over how their computers to operate for large scales of users. (3) Poor QoS: Proxy- are used by the censored users. Particularly, the volunteer based circumvention systems like Tor and it’s variants suffer users can decide what websites they will proxy for censored from low quality of service (e.g., high latencies and low users, and how much bandwidth they will allocate. -

DNS Spoofing 2
Professor Vahab COMP 424 13 November 2016 DNS Spoofing DNS spoofing, also known as DNS Cache Poisoning, is one of the most widely used man-in-the-middle attacks that capitalizes on vulnerabilities in the domain name system that returns a false IP address and routes the user to a malicious domain. Whenever a machine contacts a domain name such as www.bankofamerica.com, it must first contact its DNS server which responds with multiple IP addresses where your machine can reach the website. Your computer is then able to connect directly to one of the IP addresses and the DNS is able to convert the IP addresses into a human-readable domain name. If an attacker is able to gain control of a DNS server and change some of its properties such as routing Bank of America’s website to an attacker’s IP address. At that location, the attacker is then able to unsuspectingly steal the user’s credentials and account information. Attackers use spam and other forms of attack to deliver malware that changes DNS settings and installs a rogue Certificate Authority. The DNS changes point to the hacker's secret DNS name server so that when the users access the web they are directed to proxy servers instead of authorized sites. They can also start to blacklist domains and frustrate the user with their day to day activities. All blacklisted domains would have their traffic dropped instead of forwarded to their intended destination. Based on the rogue Certificate Authority the system has no sign that an attack is taking place or ever took place. -

Secure Shell- Its Significance in Networking (Ssh)
International Journal of Application or Innovation in Engineering & Management (IJAIEM) Web Site: www.ijaiem.org Email: [email protected] Volume 4, Issue 3, March 2015 ISSN 2319 - 4847 SECURE SHELL- ITS SIGNIFICANCE IN NETWORKING (SSH) ANOOSHA GARIMELLA , D.RAKESH KUMAR 1. B. TECH, COMPUTER SCIENCE AND ENGINEERING Student, 3rd year-2nd Semester GITAM UNIVERSITY Visakhapatnam, Andhra Pradesh India 2.Assistant Professor Computer Science and Engineering GITAM UNIVERSITY Visakhapatnam, Andhra Pradesh India ABSTRACT This paper is focused on the evolution of SSH, the need for SSH, working of SSH, its major components and features of SSH. As the number of users over the Internet is increasing, there is a greater threat of your data being vulnerable. Secure Shell (SSH) Protocol provides a secure method for remote login and other secure network services over an insecure network. The SSH protocol has been designed to support many features along with proper security. This architecture with the help of its inbuilt layers which are independent of each other provides user authentication, integrity, and confidentiality, connection- oriented end to end delivery, multiplexes encrypted tunnel into several logical channels, provides datagram delivery across multiple networks and may optionally provide compression. Here, we have also described in detail what every layer of the architecture does along with the connection establishment. Some of the threats which Ssh can encounter, applications, advantages and disadvantages have also been mentioned in this document. Keywords: SSH, Cryptography, Port Forwarding, Secure SSH Tunnel, Key Exchange, IP spoofing, Connection- Hijacking. 1. INTRODUCTION SSH Secure Shell was first created in 1995 by Tatu Ylonen with the release of version 1.0 of SSH Secure Shell and the Internet Draft “The SSH Secure Shell Remote Login Protocol”. -

Threat Modeling and Circumvention of Internet Censorship by David Fifield
Threat modeling and circumvention of Internet censorship By David Fifield A dissertation submitted in partial satisfaction of the requirements for the degree of Doctor of Philosophy in Computer Science in the Graduate Division of the University of California, Berkeley Committee in charge: Professor J.D. Tygar, Chair Professor Deirdre Mulligan Professor Vern Paxson Fall 2017 1 Abstract Threat modeling and circumvention of Internet censorship by David Fifield Doctor of Philosophy in Computer Science University of California, Berkeley Professor J.D. Tygar, Chair Research on Internet censorship is hampered by poor models of censor behavior. Censor models guide the development of circumvention systems, so it is important to get them right. A censor model should be understood not just as a set of capabilities|such as the ability to monitor network traffic—but as a set of priorities constrained by resource limitations. My research addresses the twin themes of modeling and circumvention. With a grounding in empirical research, I build up an abstract model of the circumvention problem and examine how to adapt it to concrete censorship challenges. I describe the results of experiments on censors that probe their strengths and weaknesses; specifically, on the subject of active probing to discover proxy servers, and on delays in their reaction to changes in circumvention. I present two circumvention designs: domain fronting, which derives its resistance to blocking from the censor's reluctance to block other useful services; and Snowflake, based on quickly changing peer-to-peer proxy servers. I hope to change the perception that the circumvention problem is a cat-and-mouse game that affords only incremental and temporary advancements. -

Style Counsel: Seeing the (Random) Forest for the Trees in Adversarial Code Stylometry∗
Style Counsel: Seeing the (Random) Forest for the Trees in Adversarial Code Stylometry∗ Christopher McKnight Ian Goldberg Magnet Forensics University of Waterloo [email protected] [email protected] ABSTRACT worm based on an examination of the reverse-engineered code [17], The results of recent experiments have suggested that code stylom- casting style analysis as a forensic technique. etry can successfully identify the author of short programs from This technique, however, may be used to chill speech for soft- among hundreds of candidates with up to 98% precision. This poten- ware developers. There are several cases of developers being treated tial ability to discern the programmer of a code sample from a large as individuals of suspicion, intimidated by authorities and/or co- group of possible authors could have concerning consequences for erced into removing their software from the Internet. In the US, the open-source community at large, particularly those contrib- Nadim Kobeissi, the Canadian creator of Cryptocat (an online se- utors that may wish to remain anonymous. Recent international cure messaging application) was stopped, searched, and questioned events have suggested the developers of certain anti-censorship by Department of Homeland Security officials on four separate oc- and anti-surveillance tools are being targeted by their governments casions in 2012 about Cryptocat and the algorithms it employs [16]. and forced to delete their repositories or face prosecution. In November 2014, Chinese developer Xu Dong was arrested, pri- In light of this threat to the freedom and privacy of individual marily for political tweets, but also because he allegedly “committed programmers around the world, we devised a tool, Style Counsel, to crimes of developing software to help Chinese Internet users scale aid programmers in obfuscating their inherent style and imitating the Great Fire Wall of China” [4] in relation to proxy software he another, overt, author’s style in order to protect their anonymity wrote. -

Thesis That TW-OR Forwards All DNS Queries to a Resolver in China
The Impact of DNSSEC on the Internet Landscape Von der Fakult¨atf¨urIngenieurwissenschaften, Abteilung Informatik und Angewandte Kognitionswissenschaft der Universit¨atDuisburg-Essen zur Erlangung des akademischen Grades Doktor der Ingenieurwissenschaften genehmigte Dissertation von Matth¨ausWander aus Lubin (L¨uben) Gutachter: Prof. Dr.-Ing. Torben Weis Prof. Dr.-Ing. Felix Freiling Tag der m¨undlichen Pr¨ufung:19. Juni 2015 Abstract In this dissertation we investigate the security deficiencies of the Domain Name System (DNS) and assess the impact of the DNSSEC security extensions. DNS spoofing attacks divert an application to the wrong server, but are also used routinely for blocking access to websites. We provide evidence for systematic DNS spoofing in China and Iran with measurement-based analyses, which allow us to examine the DNS spoofing filters from van- tage points outside of the affected networks. Third-parties in other countries can be affected inadvertently by spoofing-based domain filtering, which could be averted with DNSSEC. The security goals of DNSSEC are data integrity and authenticity. A point solution called NSEC3 adds a privacy assertion to DNSSEC, which is supposed to prevent disclosure of the domain namespace as a whole. We present GPU-based attacks on the NSEC3 privacy assertion, which allow efficient recovery of the namespace contents. We demonstrate with active measurements that DNSSEC has found wide adoption after initial hesitation. At server-side, there are more than five million domains signed with DNSSEC. A portion of them is insecure due to insufficient cryptographic key lengths or broken due to maintenance failures. At client-side, we have observed a worldwide increase of DNSSEC validation over the last three years, though not necessarily on the last mile. -

A Privacy Threat for Internet Users in Internet-Censoring Countries
A Privacy Threat for Internet Users in Internet-censoring Countries Feno Heriniaina R. College of Computer Science, Chongqing University, Chongqing, China Keywords: Censorship, Human Computer Interaction, Privacy, Virtual Private Networks. Abstract: Online surveillance has been increasingly used by different governments to control the spread of information on the Internet. The magnitude of this activity differs widely and is based primarily on the areas that are deemed, by the state, to be critical. Aside from the use of keywords and the complete domain name filtering technologies, Internet censorship can sometimes even use the total blocking of IP addresses to censor content. Despite the advances, in terms of technology used for Internet censorship, there are also different types of circumvention tools that are available to the general public. In this paper, we report the results of our investigation on how migrants who previously had access to the open Internet behave toward Internet censorship when subjected to it. Four hundred and thirty-two (432) international students took part in the study that lasted two years. We identified the most common circumvention tools that are utilized by the foreign students in China. We investigated the usability of these tools and monitored the way in which they are used. We identified a behaviour-based privacy threat that puts the users of circumvention tools at risk while they live in an Internet-censoring country. We also recommend the use of a user-oriented filtering method, which should be considered as part of the censoring system, as it enhances the performance of the screening process and recognizes the real needs of its users. -

BRKSEC-2011.Pdf
#CLUS About Garlic and Onions A little journey… Tobias Mayer, Technical Solutions Architect BRKSEC-2011 #CLUS Me… CCIE Security #14390, CISSP & Motorboat driving license… Working in Content Security & TLS Security tmayer{at}cisco.com Writing stuff at “blogs.cisco.com” #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 3 Agenda • Why anonymization? • Using Tor (Onion Routing) • How Tor works • Introduction to Onion Routing • Obfuscation within Tor • Domain Fronting • Detect Tor • I2P – Invisible Internet Project • Introduction to Garlic Routing • Conclusion #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 4 Cisco Webex Teams Questions? Use Cisco Webex Teams (formerly Cisco Spark) to chat with the speaker after the session How 1 Find this session in the Cisco Events App 2 Click “Join the Discussion” 3 Install Webex Teams or go directly to the team space 4 Enter messages/questions in the team space Webex Teams will be moderated cs.co/ciscolivebot#BRKSEC-2011 by the speaker until June 18, 2018. #CLUS © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 5 Different Intentions Hide me from Government! Hide me from ISP! Hide me from tracking! Bypass Corporate Bypass Country Access Hidden policies restrictions (Videos…) Services #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 6 Browser Identity Tracking does not require a “Name” Tracking is done by examining parameters your browser reveals https://panopticlick.eff.org #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 7 Proxies EPIC Browser #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. -
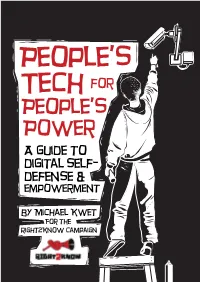
People's Tech Movement to Kick Big Tech out of Africa Could Form a Critical Part of the Global Protests Against the Enduring Legacy of Racism and Colonialism
CONTENTS Acronyms ................................................................................................................................................ 1 1 Introduction: The Rise of Digital Colonialism and Surveillance Capitalism ..................... 2 2 Threat Modeling .......................................................................................................................... 8 3 The Basics of Information Security and Software ............................................................... 10 4 Mobile Phones: Talking and Texting ...................................................................................... 14 5 Web Browsing ............................................................................................................................ 18 6 Searching the Web .................................................................................................................... 23 7 Sharing Data Safely ................................................................................................................... 25 8 Email Encryption ....................................................................................................................... 28 9 Video Chat ................................................................................................................................... 31 10 Online Document Collaboration ............................................................................................ 34 11 Protecting Your Data ................................................................................................................ -

Vyprvpn Auf Einem ASUS Router Einrichten “Schritt Für Schritt”
8.11.2019 Anleitung: ASUS Router mit VPN in Betrieb nehmen "Schritt für Schritt" mit VyprVPN - dem besten VPN-Service für sicheres Sufen Menue Anleitung: VyprVPN auf einem ASUS Router einrichten “Schritt für Schritt” von Markus Hanf Letzte Aktualisierung: 12. September 2019 Approbierter Mathematiker und Netzwerkspezialist. Dozent an einigen Universitäten. Es ist ganz einfach einen ASUS Router direkt in Betrieb zu nehmen, ganz unabhängig davon welchen Internetrouter Du derzeit verwendest. Wir haben einen ganzen Vorgang der Inbetriebnahme in einer Anleitung beschrieben. VPN Router Schematische Darstellung Einen VPN-Service direkt über den ASUS Router zu verwenden bietet die folgenden Vorteile: Alle Geräte (auch SmartTV, FireTV, AndroidTV, xBox usw) werden zuverlässig über VPN verbunden ohne Softwareinstallation. Die Firewall und die zusätzlichen Schutzfunktionen die im Router vorhanden sind lassen es zu, auch Kinder und Jugendliche vor Bedrohungen aus dem Internet zu schützen. (Malwareschutz, Sperren von Webseiten, Zugriff für bestimmte Apps auf Smartphones usw) Die gesamte Familie wird zuverlässig vor Abmahnungen und sonstigen Fallen im Internet geschützt, ohne dass dabei Software oder Apps auf den Geräten zusätzlich installiert werden müssen. Die Benutzer des Routers werden “Anonymisiert” und nutzen damit eine nicht direkt zuordenbare Internetadresse für alle täglichen Aktivitäten. Zuverlässiger Schutz aller Nutzer vor Überwachung und Vorratsdatenspeicherung und damit auch eine aktive Maßnahme für eine bessere Privatsphäre. Hilfe & Beratung -

Blocking-Resistant Communication Through Domain Fronting
Proceedings on Privacy Enhancing Technologies 2015; 2015 (2):46–64 David Fifield*, Chang Lan, Rod Hynes, Percy Wegmann, and Vern Paxson Blocking-resistant communication through domain fronting Abstract: We describe “domain fronting,” a versatile 1 Introduction censorship circumvention technique that hides the re- mote endpoint of a communication. Domain fronting Censorship is a daily reality for many Internet users. works at the application layer, using HTTPS, to com- Workplaces, schools, and governments use technical and municate with a forbidden host while appearing to com- social means to prevent access to information by the net- municate with some other host, permitted by the cen- work users under their control. In response, those users sor. The key idea is the use of different domain names at employ technical and social means to gain access to the different layers of communication. One domain appears forbidden information. We have seen an ongoing conflict on the “outside” of an HTTPS request—in the DNS re- between censor and censored, with advances on both quest and TLS Server Name Indication—while another sides, more subtle evasion countered by more powerful domain appears on the “inside”—in the HTTP Host detection. header, invisible to the censor under HTTPS encryp- Circumventors, at a natural disadvantage because tion. A censor, unable to distinguish fronted and non- the censor controls the network, have a point working fronted traffic to a domain, must choose between allow- in their favor: the censor’s distaste for “collateral dam- ing circumvention traffic and blocking the domain en- age,” incidental overblocking committed in the course of tirely, which results in expensive collateral damage.