Reference Architecture for Mobile Device and App Management
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Sharefile Enterprise
Product Overview ShareFile Enterprise Built for business. Trusted by IT. Flexible enough to meet enterprise needs. Secure enough to satisfy corporate policies. Easy enough for everyone to use. Collaborate, share, store, sync, and secure data on any device, anywhere. citrix.com Product Overview ShareFile Enterprise Key Benefits: Trends such as employee mobility, workshifting and BYO devices are • Provide secure, instant access to corporate data – online or offline putting pressure on IT, along with the business need to leverage • Data mobility - mobilize existing existing investments, protect corporate data and intellectual property enterprise data wherever it is stored • Choose where data is stored – and meet regulatory compliance requirements. In addition, growing on prem, in the cloud or both global and dispersed workforces, the need to collaborate and • Sync, share and collaborate from anywhere securely share data with other employees, 3rd parties, customers, • Protect data and retain IT control partners, further adds to these complexities. Employees have – solve the “Dropbox problem” • Deliver next-gen mobility increasingly turned to unsecure and unauthorized personal online – integrated mobile desktops, file sharing accounts for access to corporate data and files across all apps and data of their devices, and to share data with others. Personal online file sharing usage in the workplace creates serious risks for the enterprise with potential data loss, violation of regulatory rules, and places data outside of IT control. To combat this, Citrix ShareFile, a secure data sync and sharing service with flexible storage options allows IT to protect and mobilize all enterprise data. ShareFile enables mobile productivity with read-write access to data, workflows and collaboration, allows users to securely share files with anyone, and sync files across all of their devices. -
Citrix Netscaler - NITRO REST - Getting Started Guide
Citrix NetScaler - NITRO REST - Getting Started Guide Citrix® NetScaler® 10.5 Copyright and Trademark Notice Copyright © 2014 Citrix Systems, Inc. All rights reserved. NO PART OF THIS DOCUMENT MAY BE REPRODUCED OR TRANSMITTED IN ANY FORM OR BY ANY MEANS OR USED TO MAKE DERIVATIVE WORK (SUCH AS TRANSLATION, TRANSFORMATION, OR ADAPTATION) WITHOUT THE EXPRESS WRITTEN PERMISSION OF CITRIX SYSTEMS, INC. ALTHOUGH THE MATERIAL PRESENTED IN THIS DOCUMENT IS BELIEVED TO BE ACCURATE, IT IS PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE ALL RESPONSIBILITY FOR THE USE OR APPLICATION OF THE PRODUCT(S) DESCRIBED IN THIS MANUAL. CITRIX SYSTEMS, INC. OR ITS SUPPLIERS DO NOT ASSUME ANY LIABILITY THAT MAY OCCUR DUE TO THE USE OR APPLICATION OF THE PRODUCT(S) DESCRIBED IN THIS DOCUMENT. In no event shall Citrix, its agents, officers, employees, licensees or affiliates be liable for any damages whatsoever (including, without limitation, damages for loss of profits, business information, loss of information) arising out of the information or statements contained in the publication, even if Citrix has been advised of the possibility of such loss or damages. INFORMATION IN THIS DOCUMENT IS SUBJECT TO CHANGE WITHOUT NOTICE. COMPANIES, NAMES, AND DATA USED IN EXAMPLES ARE FICTITIOUS UNLESS OTHERWISE NOTED. This equipment has been tested and found to comply with the limits for a Class A digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference when the equipment is operated in a commercial environment. This equipment generates, uses, and can radiate radio-frequency energy and, if not installed and used in accordance with the instruction manual, may cause harmful interference to radio communications. -

Introducing Xendesktop, Built on the Avalon Platform
Introducing XenDesktop White Paper Introducing XenDesktop, built on the Avalon platform Citrix XenDesktop transforms Windows apps and desktops into a secure, mobile service for any user, any device, anywhere. citrix.com Introducing XenDesktop White Paper 2 Citrix XenDesktop enables mobile workstyles by empowering IT to deliver Windows desktops and apps as mobile services. Users can self-select apps from an easy-to-use “store” that is securely accessible from tablets, smartphones, PCs, Macs and thin clients. Only XenDesktop delivers a native touch-optimized experience with HDX high-definition performance over mobile networks. XenDesktop is built on the new Avalon platform that offers simple management, fast deployment, support visibility, and a cloud-ready architecture. This whitepaper provides an overview of the capabilities and benefits of XenDesktop. Windows apps and desktops anywhere delivered with XenDesktop delivery technology Users across the enterprise have varying performance, personalization and mobility requirements. Some require offline mobility of laptops, others need simplicity and standardization, while still others need a high-performance, fully personalized desktop, or simple access to a Windows app from their iPad or Android tablet. XenDesktop meets all these requirements in a single solution with its unique delivery technology. With XenDesktop, IT can deliver every type of virtual desktop or app, hosted or local, optimized to meet the performance, security and mobility requirements of each individual user while optimizing the cost of deployment and ongoing management. • The right workspace—complete virtual desktops or just the apps Some users enjoy a full desktop workspace with applications, data, shortcuts, wallpaper, and multi-tasking windows available across big screens or even multiple displays. -

Citrix Workspace Suite Datasheet
Data Sheet Citrix Workspace Suite Citrix Workspace Suite Seamlessly enable secure access to apps, desktops, data and services, anywhere Citrix Workspace Suite delivers secure access to apps, desktops, data and services optimized to meet the performance, security and mobility requirements of individuals. This complete and powerful solution can deliver secure access to personalized desktops, mobile, web and Windows apps, and corporate data, as well as provide device configuration management. The result is a high performance user experience delivered from any device, including tablets, smartphones, PCs, Macs or thin clients, over any network or cloud to empower mobile workers with the freedom and flexibility to choose how they work. Features Personalized content and self-service access for individuals on any device Follow-me apps, desktops and data across more than 3 billion devices Enterprise app store for self-service selection of IT provisioned applications Deliver Windows apps to users on any device with application virtualization Deliver mobile and web/SaaS apps to users on their mobile devices with mobile application management Worx Mobile Apps, such as WorxMail, WorxWeb, WorxNotes and more improve productivity and provide a seamless user experience and maximum security Support for any Worx-enabled app, including GoToMeeting, Podio or other 3rd party apps for improved productivity and maximum security Secure, sync and share enterprise files across any device, with full view and edit capabilities, including file systems, network drives -
Automatic Trust Based Segregation for Mobile Devices
The Interdisciplinary Center, Herzlia Efi Arazi School of Computer Science Automatic trust based segregation for mobile devices M.Sc. Dissertation Submitted in Partial Fulfillment of the Requirements for the Degree of Master of Science (M.Sc.) Research Track in Computer Science Submitted by Oren Poleg Under the supervision of Dr. David Movshovitz (IDC) June, 2015 Acknowledgments I would like to express my deepest appreciation to Dr. David Movshovitz. Without his guidance and persistent help this dissertation would not have been possible. His thorough knowledge of information security was a valuable asset for this work. Dr. Movshovitz invested a substantial amount of time, beyond the regular office hours, so I could fulfill my commitments and for this I want to extend my sincere gratitude. I would also like to thank Prof. Anat Bremler-Bar for her encouragement and assistance. I feel privileged to have worked together with Dr. Movshovitz and Prof. Bremler-Bar. Working with such professionals was an inspirational experience for me. Last but not least, my dear wife Einat who provided me with the time and space to write this paper. ii Abstract Mobile devices have become an essential part of our lives. These devices hold much of our personal information such as contact lists, calendar appointments and private messages. Writers of applications for mobile devices are trying to get hold of personal information. Application such as WhatsApp and Viber needs this information for justified causes, as their business is built on sending messages to people in the contact list. Other applications may use personal information for targeted advertisement, and sometimes for malicious purposes. -
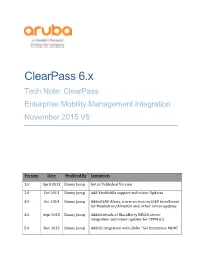
Clearpass 6.X Tech Note: Clearpass Enterprise Mobility Management Integration November 2015 V5
ClearPass 6.x Tech Note: ClearPass Enterprise Mobility Management Integration November 2015 V5 Version Date Modified By Comments 1.0 April 2013 Danny Jump Initial Published Version 2.0 Oct 2013 Danny Jump Add XenMobile support and minor Updates 3.0 Oct 2014 Danny Jump Added SAP Afaria, a new section on SCEP Enrollment for MobileIron/Airwatch and ‘other’ minor updates 4.0 Sept 2015 Danny Jump Added details of BlackBerry BES10 server integration and minor updates for CPPM 6.5 5.0 Nov 2015 Danny Jump Added integration with Globo “Go! Enterprise MDM” ClearPass 6.x Tech Note: ClearPass and EMM Integration Guide November 2015 - V5 Table of Contents Table of Contents ............................................................................................................................................ 2 Table of Figures ............................................................................................................................................... 3 Introduction ........................................................................................................................................... 6 EMM Integration ................................................................................................................................... 7 Configuration of EMM Vendors ................................................................................................................ 10 Normalized Dataset ..................................................................................................................................... -

Secure Mobile Collaboration with Citrix Xenmobile and Sharefile
White Paper Secure Mobile Collaboration with Citrix XenMobile and ShareFile citrix.com White Paper Enterprise Mobility Management Mobile devices and BYOD have brought unprecedented agility to the enterprise, allowing users to collaborate, access information and get serious work done any time, from almost anywhere on the planet. Along with this mobile user freedom and agility, however, have come unprecedented security challenges. Mobile devices and BYOD have brought unprecedented agility to the enterprise, allowing users to collaborate, access information and get serious work done any time, from almost anywhere on the planet. Along with this mobile user freedom and agility, however, have come unprecedented security challenges. Any time users store sensitive enterprise information on their laptops, smart phones or tablets, they subject it to theft or exposure if those devices are ever lost, stolen, or connected over insecure WiFi networks or the Internet. When users mix personal and work lives on the same device, they risk insecure personal applications and mixed personal and work data leading to sensitive data loss and theft. This could happen either advertently or inadvertently, when, for example, users send corporate information in personal emails or browse infected Web sites that introduce malware into the corporate network. When mobile users take advantage of consumer file sharing services such as DropBox and Box, they take a risk as well, as these services were not built with enterprise management and security in mind. Even those that have enterprise features are not as manageable and tightly integrated with enterprise mobile security solutions as they should be. Conversely, if IT imposes draconian security policies and monitors personal mobile devices and data it risks impeding employee productivity and agility. -
Citrix Solutions for Banking and Financial Services
Solutions Brief Citrix solutions for banking and Solutions Brief 100 percent of the top 20 global Citrix® • Protect customer and business information, reduce risk and ensure compliance • Deliver an innovative, differentiated customer experience across all channels 2 Solutions Brief • Improve workforce productivity, satisfaction and engagement • Increase business agility • Ensure business continuity and zero downtime ®® ® ® ® 3 Solutions Brief ®®, Citrix ® and Citrix Podio® ® ® Improve employee productivity and engagement without the risk: Four best practices for secure mobility 4 Solutions Brief Banking and Financial Services Corporate Headquarters India Development Center Latin America Headquarters Fort Lauderdale, FL, USA Bangalore, India Coral Gables, FL, USA Silicon Valley Headquarters Online Division Headquarters UK Development Center Santa Clara, CA, USA Santa Barbara, CA, USA Chalfont, United Kingdom EMEA Headquarters Schaffhausen, Switzerland Hong Kong, China About Citrix Citrix (NASDAQ:CTXS) is a leader in mobile workspaces, providing virtualization, mobility management, networking and cloud services to enable new ways to work better. Citrix solutions power business mobility through secure, personal workspaces that provide people with instant access to apps, desktops, data and communications on any device, over any network and cloud. This year Citrix is celebrating 25 years of -

Insight MFR By
Manufacturers, Publishers and Suppliers by Product Category 11/6/2017 10/100 Hubs & Switches ASCEND COMMUNICATIONS CIS SECURE COMPUTING INC DIGIUM GEAR HEAD 1 TRIPPLITE ASUS Cisco Press D‐LINK SYSTEMS GEFEN 1VISION SOFTWARE ATEN TECHNOLOGY CISCO SYSTEMS DUALCOMM TECHNOLOGY, INC. GEIST 3COM ATLAS SOUND CLEAR CUBE DYCONN GEOVISION INC. 4XEM CORP. ATLONA CLEARSOUNDS DYNEX PRODUCTS GIGAFAST 8E6 TECHNOLOGIES ATTO TECHNOLOGY CNET TECHNOLOGY EATON GIGAMON SYSTEMS LLC AAXEON TECHNOLOGIES LLC. AUDIOCODES, INC. CODE GREEN NETWORKS E‐CORPORATEGIFTS.COM, INC. GLOBAL MARKETING ACCELL AUDIOVOX CODI INC EDGECORE GOLDENRAM ACCELLION AVAYA COMMAND COMMUNICATIONS EDITSHARE LLC GREAT BAY SOFTWARE INC. ACER AMERICA AVENVIEW CORP COMMUNICATION DEVICES INC. EMC GRIFFIN TECHNOLOGY ACTI CORPORATION AVOCENT COMNET ENDACE USA H3C Technology ADAPTEC AVOCENT‐EMERSON COMPELLENT ENGENIUS HALL RESEARCH ADC KENTROX AVTECH CORPORATION COMPREHENSIVE CABLE ENTERASYS NETWORKS HAVIS SHIELD ADC TELECOMMUNICATIONS AXIOM MEMORY COMPU‐CALL, INC EPIPHAN SYSTEMS HAWKING TECHNOLOGY ADDERTECHNOLOGY AXIS COMMUNICATIONS COMPUTER LAB EQUINOX SYSTEMS HERITAGE TRAVELWARE ADD‐ON COMPUTER PERIPHERALS AZIO CORPORATION COMPUTERLINKS ETHERNET DIRECT HEWLETT PACKARD ENTERPRISE ADDON STORE B & B ELECTRONICS COMTROL ETHERWAN HIKVISION DIGITAL TECHNOLOGY CO. LT ADESSO BELDEN CONNECTGEAR EVANS CONSOLES HITACHI ADTRAN BELKIN COMPONENTS CONNECTPRO EVGA.COM HITACHI DATA SYSTEMS ADVANTECH AUTOMATION CORP. BIDUL & CO CONSTANT TECHNOLOGIES INC Exablaze HOO TOO INC AEROHIVE NETWORKS BLACK BOX COOL GEAR EXACQ TECHNOLOGIES INC HP AJA VIDEO SYSTEMS BLACKMAGIC DESIGN USA CP TECHNOLOGIES EXFO INC HP INC ALCATEL BLADE NETWORK TECHNOLOGIES CPS EXTREME NETWORKS HUAWEI ALCATEL LUCENT BLONDER TONGUE LABORATORIES CREATIVE LABS EXTRON HUAWEI SYMANTEC TECHNOLOGIES ALLIED TELESIS BLUE COAT SYSTEMS CRESTRON ELECTRONICS F5 NETWORKS IBM ALLOY COMPUTER PRODUCTS LLC BOSCH SECURITY CTC UNION TECHNOLOGIES CO FELLOWES ICOMTECH INC ALTINEX, INC. -

Citrix Xenmobile Service Security
White Paper Citrix XenMobile Service Security Citrix.com Table of contents Introduction . 4 Cloud Benefits . 5 Cloud Security . 5 Security Concerns . 6 Overview . 7 XenMobile Service . 8 Architecture . 8 Environment Security . 9 Logical Security . 9 Access controls . 10 Data access controls . 10 Network access controls . 10 Operating system access controls . 11 Change control and business continuity . 11 Personnel security . 12 Compliance . 13 Data Encryption . 13 Physical Security . 13 UEM . 14 Enrollment . 14 Authentication . 15 Client Management . 16 Citrix Cloud . 17 Services . 18 Benefits . 19 Cloud Connector . 20 Citrix.com | White Paper | Citrix XenMobile Service Security 2 Table of contents Cloud Platform Provider . 22 Microsoft Azure . 22 Azure Transparent Data Encryption . 23 Azure Security Center . 24 Azure Active Directory (AAD) . 24 Network Security Groups . 24 Availability Sets . 25 Physical Security . 25 Azure Portal . 25 Azure Activity Logs . 25 Amazon Web Services . 26 Resource Locations . 26 Domain Controllers . 27 NetScaler Gateway . 27 Data . 28 Exchange . 28 Intranet Web Sites . 28 ShareFile StorageZones . 28 XenMobile Client . 29 Device Security . 29 App Security . 30 MDX Container . 30 Partners Container Solutions . 32 Productivity Apps . 32 Network Security . 34 Summary . 35 About the Authors and Contributors . 35 Citrix.com | White Paper | Citrix XenMobile Service Security 3 Introduction Enterprises are moving to Citrix Workspace to support their digital transformation efforts to utilize its breadth of services in a consolidated and secure environment. The Citrix Workspace simplifies the management of information systems by centralizing management while unifying applications, data and desktops into a digital workspace. Enterprise are under attack and protecting their digital workspace is an essential requirement. -

RFI Template for Enterprise Mobile Device Management
RFI Template for Enterprise Mobile Device Management MDM SOLUTION – RFI TEMPLATE About This RFI Template A secure mobile device management solution is an integral part of any effective enterprise mobility program. Mobile devices are similar to other endpoints in the enterprise and require similar security as corporate issued desktops and laptops. Many businesses are also subject to regulatory requirements and compliance standards that drive the need for specific mobile security capabilities. Enterprise mobility is fast-changing with a crowded field of products and solutions from several vendors. Businesses have to choose carefully to pick the correct solution that will not only address their needs today but also those of the future. Not all MDM solutions are created equal. There are several products that only offer basic asset management capabilities for mobile devices. Some others support only a limited range of features on some platforms. Very few solutions offer a full complement of capabilities that address enterprise mobile security, availability, and manageability requirements that go beyond device management to address content security and “business-ready” apps. This document provides guidelines on key requirements that should be addressed by an MDM solution. The requirements for MDM solutions are grouped into the following categories: 1. Core MDM capabilities 2. Simplicity of MDM solution for administrators and end-users 3. End-to-end security and compliance 4. Enterprise-grade architecture 5. Best-in-class support, services and training © 2012 Zenprise, Inc. 2 MDM SOLUTION – RFI TEMPLATE 1 Core MDM Capabilities 1.1 Delivery Model: 1.1.1 Solution should provide deployment options that fit the business model and budget, with cloud and on-premises options, as well as a hybrid option with a mix of cloud solution and back-end integrations with LDAP, PKI, and application servers, as well as subscription options. -

Exinda Applications List
Application List Exinda ExOS Version 6.4 © 2014 Exinda Networks, Inc. 2 Copyright © 2014 Exinda Networks, Inc. All rights reserved. No parts of this work may be reproduced in any form or by any means - graphic, electronic, or mechanical, including photocopying, recording, taping, or information storage and retrieval systems - without the written permission of the publisher. Products that are referred to in this document may be either trademarks and/or registered trademarks of the respective owners. The publisher and the author make no claim to these trademarks. While every precaution has been taken in the preparation of this document, the publisher and the author assume no responsibility for errors or omissions, or for damages resulting from the use of information contained in this document or from the use of programs and source code that may accompany it. In no event shall the publisher and the author be liable for any loss of profit or any other commercial damage caused or alleged to have been caused directly or indirectly by this document. Document Built on Tuesday, October 14, 2014 at 5:10 PM Documentation conventions n bold - Interface element such as buttons or menus. For example: Select the Enable checkbox. n italics - Reference to other documents. For example: Refer to the Exinda Application List. n > - Separates navigation elements. For example: Select File > Save. n monospace text - Command line text. n <variable> - Command line arguments. n [x] - An optional CLI keyword or argument. n {x} - A required CLI element. n | - Separates choices within an optional or required element. © 2014 Exinda Networks, Inc.