PMDF User's Guide UNIX Edition
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

COMMUNICATION STUDIES REGISTRATION INFORMATION DO NOT E-Mail the Professor to Request Permission for Communication Studies Class
COMMUNICATION STUDIES REGISTRATION INFORMATION DO NOT e-mail the professor to request permission for Communication Studies classes! We follow our departmental waitlist priorities found on the Department web page at: http://www.lsa.umich.edu/comm/undergraduate/generalinformation/majorpolicies. Students on the waitlist are expected to attend the first two lectures and the first discussion section for the class, just as any enrolled student. Students who do not do attend will lose their spot in the class or on the waitlist! ---------------------------------------------------------------------------------------------------------------------- Comm 101 & 102 are restricted to students with freshman and sophomore standing. If you have over 54 credits, including the current semester, you will not be able to register for these. Juniors and seniors wishing to take Comm 101 and 102 may attend the first two lectures and first discussion section of the course and ask the instructor to add them to the waitlist. Instructors will issue permissions from the waitlist after classes begin, according to department waitlist priorities. There may be some exceptions to this policy, but you will need to e-mail [email protected] 2 (TWO) days prior to your registration date to find out if you qualify for an exception. Provide the following: Name: UMID#: Registration Date: Registration Term: Course: Top 3 section choices: Exception eligibility - AP credit has pushed you over the 54 credits for junior standing, OR you have junior standing but have already completed Comm 101 or 102 to start the Comm prerequisites, OR you are a transfer student with junior standing OR you are an MDDP student with more than sophomore standing. -

Excerpts of Chapters From
Excerpts of Chapters from A Practical Guide to Ubuntu Linux® FOURTH EDITION Mark G. Sobell ISBN-13: 978-0-13-392731-3 CopyrightExcerpt © 2015 Mark G. Sobell Upper Saddle River, NJ • Boston • Indianapolis • San Francisco New York • Toronto • Montreal • London • Munich • Paris • Madrid Capetown • Sydney • Tokyo • Singapore • Mexico City Blank Excerpt 3 Step-by-Step Installation 3Chapter3 In This Chapter Objectives Booting Ubuntu and Running a After reading this chapter you should be able to: Live Session. 56 Run a live session and use gnome-disks to view and Automatic Boot Sequence . 56 change disk partitioning Running a Live Session. 59 Install Ubuntu from a live session Installing from a Live Session . 60 Install Ubuntu using the Server Image Installing from the Desktop Modify system behavior using boot parameters Boot Menu . 61Excerpt Modify partitions during installation The ubiquity Graphical Installer. 61 The ubiquity Advanced Partitioning List the requirement and considerations for a dual- Screen. 67 boot configuration Advanced Installation. 71 Modifying Boot Parameters (Options) . 75 debian-installer: The Ubuntu Textual Installer . 78 gnome-disks: The GNOME Disk Utility . 88 Setting Up a Dual-Boot System . 91 5555 56 Chapter 3 Step-by-Step Installation Chapter 2 covered planning the installation of Ubuntu: determining the requirements; planning the layout of the hard disk; obtaining the files you need for the installation, including how to download and burn or write Desktop and Server Images to installa- tion media; and collecting information about the system. This chapter focuses on installing Ubuntu. Frequently the installation is quite simple, especially if you have done a good job of planning. -
Netop Remote Control User's Guide
USER'S GUIDE 27 September 2017 Netop Remote Control User's Guide Copyright© 1981-2017 Netop Business Solutions A/S. All Rights Reserved. Portions used under license from third parties. Please send any comments to: Netop Business Solutions A/S Bregnerodvej 127 DK-3460 Birkerod Denmark E-mail: [email protected] Internet: www.netop.com Netop™ is a trademark of Netop Business Solutions A/S. All other products mentioned in this document are trademarks of their respective manufacturers. Netop Business Solutions A/S denies any and all responsibility for damages caused directly or indirectly as a result of using this document. The content of this document is subject to change without notice. Netop Business Solutions A/S retains the copyright to this document. The document is optimized for double-sided printing. 27 September 2017 Netop Remote Control User's Guide Contents 1 Overview ....................................................................................................................................................4 1.1 Remote Control modules ...............................................................................................................................................4 1.2 Security ...........................................................................................................................................4 1.3 Communication profiles ...............................................................................................................................................5 2 Managing Hosts ........................................................................................................................................6 -

Powerview Command Reference
PowerView Command Reference TRACE32 Online Help TRACE32 Directory TRACE32 Index TRACE32 Documents ...................................................................................................................... PowerView User Interface ............................................................................................................ PowerView Command Reference .............................................................................................1 History ...................................................................................................................................... 12 ABORT ...................................................................................................................................... 13 ABORT Abort driver program 13 AREA ........................................................................................................................................ 14 AREA Message windows 14 AREA.CLEAR Clear area 15 AREA.CLOSE Close output file 15 AREA.Create Create or modify message area 16 AREA.Delete Delete message area 17 AREA.List Display a detailed list off all message areas 18 AREA.OPEN Open output file 20 AREA.PIPE Redirect area to stdout 21 AREA.RESet Reset areas 21 AREA.SAVE Save AREA window contents to file 21 AREA.Select Select area 22 AREA.STDERR Redirect area to stderr 23 AREA.STDOUT Redirect area to stdout 23 AREA.view Display message area in AREA window 24 AutoSTOre .............................................................................................................................. -

Text Editing in UNIX: an Introduction to Vi and Editing
Text Editing in UNIX A short introduction to vi, pico, and gedit Copyright 20062009 Stewart Weiss About UNIX editors There are two types of text editors in UNIX: those that run in terminal windows, called text mode editors, and those that are graphical, with menus and mouse pointers. The latter require a windowing system, usually X Windows, to run. If you are remotely logged into UNIX, say through SSH, then you should use a text mode editor. It is possible to use a graphical editor, but it will be much slower to use. I will explain more about that later. 2 CSci 132 Practical UNIX with Perl Text mode editors The three text mode editors of choice in UNIX are vi, emacs, and pico (really nano, to be explained later.) vi is the original editor; it is very fast, easy to use, and available on virtually every UNIX system. The vi commands are the same as those of the sed filter as well as several other common UNIX tools. emacs is a very powerful editor, but it takes more effort to learn how to use it. pico is the easiest editor to learn, and the least powerful. pico was part of the Pine email client; nano is a clone of pico. 3 CSci 132 Practical UNIX with Perl What these slides contain These slides concentrate on vi because it is very fast and always available. Although the set of commands is very cryptic, by learning a small subset of the commands, you can edit text very quickly. What follows is an outline of the basic concepts that define vi. -

PATACS Posts Newsletterofthe Potomacareatechnology and Computersociety
PATACS Posts Newsletterofthe PotomacAreaTechnology and ComputerSociety May 2014 www.patacs.org Page 1 Useful Bits & Pieces Entertaining Web Sites On occasion it can be fun to explore off-beat Web CboyluLmonrrisitn, PRo.toGmaarcsAornea Technology and Computer Society sites. Here are a few sites for your entertainment pleasure: Free Antivirus Software for Apple Computers • See http://www.dumblaws.com/. Did you know that in Virginia “No animal may be Whether to use antivirus software on Apple hunted on Sunday with the exception of computers has been a controversial issue for raccoons, which may be hunted until 2:00 years. Major providers such as Symantec, AM?” Well, now you know. Kaspersky, Panda and Trend-Micro offer products for a fee. In the table below is a list of • See http://www.funnytypos.com/. An amusing some free offerings for Macs. See collection of typos like “world famuos”, “no http://goo.gl/VA1iHz for a comprehensive list of smorking” and “free chicken stips with antivirus software for PCs, Macs, Linux, Unix, purchas”. smartphones, etc. Also search the term • See http://whitewhine.com/. Want to learn “antivirus” in Apple’s App Store for numerous what people are complaining about? For antimalware apps (free and for fee). example, “I hate it when I have money to spend and can’t find anything I want.” Poor baby! • See http://www.craigslist.org/about/best/all for offers voted best by Craiglist readers. For example: “I have 2 dozen goats I need to get rid of. I had no idea raising goats would be this hard. These little ***** keep eating all my wife's flowers and climbing on our **** cars. -

Binpac: a Yacc for Writing Application Protocol Parsers
binpac: A yacc for Writing Application Protocol Parsers Ruoming Pang∗ Vern Paxson Google, Inc. International Computer Science Institute and New York, NY, USA Lawrence Berkeley National Laboratory [email protected] Berkeley, CA, USA [email protected] Robin Sommer Larry Peterson International Computer Science Institute Princeton University Berkeley, CA, USA Princeton, NJ, USA [email protected] [email protected] ABSTRACT Similarly, studies of Email traffic [21, 46], peer-to-peer applica- A key step in the semantic analysis of network traffic is to parse the tions [37], online gaming, and Internet attacks [29] require under- traffic stream according to the high-level protocols it contains. This standing application-level traffic semantics. However, it is tedious, process transforms raw bytes into structured, typed, and semanti- error-prone, and sometimes prohibitively time-consuming to build cally meaningful data fields that provide a high-level representation application-level analysis tools from scratch, due to the complexity of the traffic. However, constructing protocol parsers by hand is a of dealing with low-level traffic data. tedious and error-prone affair due to the complexity and sheer num- We can significantly simplify the process if we can leverage a ber of application protocols. common platform for various kinds of application-level traffic anal- This paper presents binpac, a declarative language and com- ysis. A key element of such a platform is application-protocol piler designed to simplify the task of constructing robust and effi- parsers that translate packet streams into high-level representations cient semantic analyzers for complex network protocols. We dis- of the traffic, on top of which we can then use measurement scripts cuss the design of the binpac language and a range of issues that manipulate semantically meaningful data elements such as in generating efficient parsers from high-level specifications. -
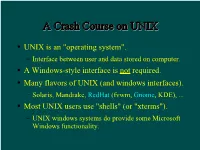
A Crash Course on UNIX
AA CCrraasshh CCoouurrssee oonn UUNNIIXX UNIX is an "operating system". Interface between user and data stored on computer. A Windows-style interface is not required. Many flavors of UNIX (and windows interfaces). Solaris, Mandrake, RedHat (fvwm, Gnome, KDE), ... Most UNIX users use "shells" (or "xterms"). UNIX windows systems do provide some Microsoft Windows functionality. TThhee SShheellll A shell is a command-line interface to UNIX. Also many flavors, e.g. sh, bash, csh, tcsh. The shell provides commands and functionality beyond the basic UNIX tools. E.g., wildcards, shell variables, loop control, etc. For this tutorial, examples use tcsh in RedHat Linux running Gnome. Differences are minor for the most part... BBaassiicc CCoommmmaannddss You need these to survive: ls, cd, cp, mkdir, mv. Typically these are UNIX (not shell) commands. They are actually programs that someone has written. Most commands such as these accept (or require) "arguments". E.g. ls -a [show all files, incl. "dot files"] mkdir ASTR688 [create a directory] cp myfile backup [copy a file] See the handout for a list of more commands. AA WWoorrdd AAbboouutt DDiirreeccttoorriieess Use cd to change directories. By default you start in your home directory. E.g. /home/dcr Handy abbreviations: Home directory: ~ Someone else's home directory: ~user Current directory: . Parent directory: .. SShhoorrttccuuttss To return to your home directory: cd To return to the previous directory: cd - In tcsh, with filename completion (on by default): Press TAB to complete filenames as you type. Press Ctrl-D to print a list of filenames matching what you have typed so far. Completion works with commands and variables too! Use ↑, ↓, Ctrl-A, & Ctrl-E to edit previous lines. -

Kubuntu Desktop Guide
Kubuntu Desktop Guide Ubuntu Documentation Project <[email protected]> Kubuntu Desktop Guide by Ubuntu Documentation Project <[email protected]> Copyright © 2004, 2005, 2006 Canonical Ltd. and members of the Ubuntu Documentation Project Abstract The Kubuntu Desktop Guide aims to explain to the reader how to configure and use the Kubuntu desktop. Credits and License The following Ubuntu Documentation Team authors maintain this document: • Venkat Raghavan The following people have also have contributed to this document: • Brian Burger • Naaman Campbell • Milo Casagrande • Matthew East • Korky Kathman • Francois LeBlanc • Ken Minardo • Robert Stoffers The Kubuntu Desktop Guide is based on the original work of: • Chua Wen Kiat • Tomas Zijdemans • Abdullah Ramazanoglu • Christoph Haas • Alexander Poslavsky • Enrico Zini • Johnathon Hornbeck • Nick Loeve • Kevin Muligan • Niel Tallim • Matt Galvin • Sean Wheller This document is made available under a dual license strategy that includes the GNU Free Documentation License (GFDL) and the Creative Commons ShareAlike 2.0 License (CC-BY-SA). You are free to modify, extend, and improve the Ubuntu documentation source code under the terms of these licenses. All derivative works must be released under either or both of these licenses. This documentation is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE AS DESCRIBED IN THE DISCLAIMER. Copies of these licenses are available in the appendices section of this book. Online versions can be found at the following URLs: • GNU Free Documentation License [http://www.gnu.org/copyleft/fdl.html] • Attribution-ShareAlike 2.0 [http://creativecommons.org/licenses/by-sa/2.0/] Disclaimer Every effort has been made to ensure that the information compiled in this publication is accurate and correct. -
Fedora 14 User Guide
Fedora 14 User Guide Using Fedora 14 for common desktop computing tasks Fedora Documentation Project User Guide Fedora 14 User Guide Using Fedora 14 for common desktop computing tasks Edition 1.0 Author Fedora Documentation Project [email protected] Copyright © 2010 Red Hat, Inc. and others. The text of and illustrations in this document are licensed by Red Hat under a Creative Commons Attribution–Share Alike 3.0 Unported license ("CC-BY-SA"). An explanation of CC-BY-SA is available at http://creativecommons.org/licenses/by-sa/3.0/. The original authors of this document, and Red Hat, designate the Fedora Project as the "Attribution Party" for purposes of CC-BY-SA. In accordance with CC-BY-SA, if you distribute this document or an adaptation of it, you must provide the URL for the original version. Red Hat, as the licensor of this document, waives the right to enforce, and agrees not to assert, Section 4d of CC-BY-SA to the fullest extent permitted by applicable law. Red Hat, Red Hat Enterprise Linux, the Shadowman logo, JBoss, MetaMatrix, Fedora, the Infinity Logo, and RHCE are trademarks of Red Hat, Inc., registered in the United States and other countries. For guidelines on the permitted uses of the Fedora trademarks, refer to https://fedoraproject.org/wiki/ Legal:Trademark_guidelines. Linux® is the registered trademark of Linus Torvalds in the United States and other countries. Java® is a registered trademark of Oracle and/or its affiliates. XFS® is a trademark of Silicon Graphics International Corp. or its subsidiaries in the United States and/or other countries. -

Puremessage for Unix Help Contents Getting Started
PureMessage for Unix help Contents Getting Started......................................................................................................................................... 1 Welcome to PureMessage for Unix.............................................................................................. 1 Deployment Strategies.................................................................................................................. 6 Installing PureMessage............................................................................................................... 18 Upgrading PureMessage.............................................................................................................51 Quick Reference Guide...............................................................................................................65 Contacting Sophos...................................................................................................................... 75 Managing PureMessage........................................................................................................................ 77 Dashboard Tab............................................................................................................................77 Policy Tab....................................................................................................................................79 Quarantine Tab..........................................................................................................................130 -

MX-19.2 Users Manual
MX-19.2 Users Manual v. 20200801 manual AT mxlinux DOT org Ctrl-F = Search this Manual Ctrl+Home = Return to top Table of Contents 1 Introduction...................................................................................................................................4 1.1 About MX Linux................................................................................................................4 1.2 About this Manual..............................................................................................................4 1.3 System requirements..........................................................................................................5 1.4 Support and EOL................................................................................................................6 1.5 Bugs, issues and requests...................................................................................................6 1.6 Migration............................................................................................................................7 1.7 Our positions......................................................................................................................8 1.8 Notes for Translators.............................................................................................................8 2 Installation...................................................................................................................................10 2.1 Introduction......................................................................................................................10