Virus Bulletin, August 2000
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Strategies of Computer Worms
304543_ch09.qxd 1/7/05 9:05 AM Page 313 CHAPTER 9 Strategies of Computer Worms “Worm: n., A self-replicating program able to propagate itself across network, typically having a detrimental effect.” —Concise Oxford English Dictionary, Revised Tenth Edition 313 304543_ch09.qxd 1/7/05 9:05 AM Page 314 Chapter 9—Strategies of Computer Worms 9.1 Introduction This chapter discusses the generic (or at least “typical”) structure of advanced computer worms and the common strategies that computer worms use to invade new target systems. Computer worms primarily replicate on networks, but they represent a subclass of computer viruses. Interestingly enough, even in security research communities, many people imply that computer worms are dramatically different from computer viruses. In fact, even within CARO (Computer Antivirus Researchers Organization), researchers do not share a common view about what exactly can be classified as a “worm.” We wish to share a common view, but well, at least a few of us agree that all computer worms are ultimately viruses1. Let me explain. The network-oriented infection strategy is indeed a primary difference between viruses and computer worms. Moreover, worms usually do not need to infect files but propagate as standalone programs. Additionally, several worms can take con- trol of remote systems without any help from the users, usually exploiting a vul- nerability or set of vulnerabilities. These usual characteristics of computer worms, however, do not always hold. Table 9.1 shows several well-known threats. Table -
Tangled Web : Tales of Digital Crime from the Shadows of Cyberspace
TANGLED WEB Tales of Digital Crime from the Shadows of Cyberspace RICHARD POWER A Division of Macmillan USA 201 West 103rd Street, Indianapolis, Indiana 46290 Tangled Web: Tales of Digital Crime Associate Publisher from the Shadows of Cyberspace Tracy Dunkelberger Copyright 2000 by Que Corporation Acquisitions Editor All rights reserved. No part of this book shall be reproduced, stored in a Kathryn Purdum retrieval system, or transmitted by any means, electronic, mechanical, pho- Development Editor tocopying, recording, or otherwise, without written permission from the Hugh Vandivier publisher. No patent liability is assumed with respect to the use of the infor- mation contained herein. Although every precaution has been taken in the Managing Editor preparation of this book, the publisher and author assume no responsibility Thomas Hayes for errors or omissions. Nor is any liability assumed for damages resulting from the use of the information contained herein. Project Editor International Standard Book Number: 0-7897-2443-x Tonya Simpson Library of Congress Catalog Card Number: 00-106209 Copy Editor Printed in the United States of America Michael Dietsch First Printing: September 2000 Indexer 02 01 00 4 3 2 Erika Millen Trademarks Proofreader Benjamin Berg All terms mentioned in this book that are known to be trademarks or ser- vice marks have been appropriately capitalized. Que Corporation cannot Team Coordinator attest to the accuracy of this information. Use of a term in this book should Vicki Harding not be regarded as affecting the validity of any trademark or service mark. Design Manager Warning and Disclaimer Sandra Schroeder Every effort has been made to make this book as complete and as accurate Cover Designer as possible, but no warranty or fitness is implied. -
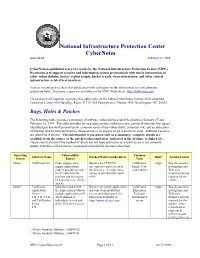
Cybernotes Issue #4-99 February 17, 1999
National Infrastructure Protection Center CyberNotes Issue #4-99 February 17, 1999 CyberNotes is published every two weeks by the National Infrastructure Protection Center (NIPC). Its mission is to support security and information system professionals with timely information on cyber vulnerabilities, hacker exploit scripts, hacker trends, virus information, and other critical infrastructure-related best practices. You are encouraged to share this publication with colleagues in the information and infrastructure protection field. Electronic copies are available on the NIPC Web site at http://www.nipc.gov. Please direct any inquiries regarding this publication to the Editor-CyberNotes, National Infrastructure Protection Center, FBI Building, Room 11719, 935 Pennsylvania Avenue, NW, Washington, DC, 20535. Bugs, Holes & Patches The following table provides a summary of software vulnerabilities identified between January 27 and February 12, 1999. The table provides the operating system, software name, potential vulnerability/impact, identified patches/workarounds/alerts, common name of the vulnerability, potential risk, and an indication of whether attacks have utilized this vulnerability or an exploit script is known to exist. Software versions are identified if known. This information is presented only as a summary; complete details are available from the source of the patch/workaround/alert, indicated in the footnote or linked site. Please note that even if the method of attack has not been utilized or an exploit script is not currently widely available on the Internet, a potential vulnerability has been identified. Operating Vulnerability/ Common Software Name Patches/Workarounds/Alerts Risk* Attacks/Scripts System Impact Name Allaire1 ColdFusion 4.0 Code snippets from Remove the CFDOCS ColdFusion High Bug discussed in sample applications directory or restrict access to Sample Code newsgroups and make it possible to make the directory. -
IBM X-Force Threat Insight Quarterly 2 X-Force Threat Insight Quarterly IBM Security Solutions
IBM Security Solutions May 2011 IBM X-Force Threat Insight Quarterly 2 X-Force Threat Insight Quarterly IBM Security Solutions Contents About the report 2 About the Report The IBM X-Force® Threat Insight Quarterly is designed to highlight some of the most significant threats and challenges 3 Evolution: From Nuisance to Weapon facing security professionals today. This report is a product of IBM Managed Security Services and the IBM X-Force 8 Prolific and Impacting Issues of Q1 2011 research and development team. Each issue focuses on specific challenges and provides a recap of the most significant recent 16 References online threats. IBM Managed Security Services are designed to help an organization improve its information security, by outsourcing security operations or supplementing your existing security teams. The IBM protection on-demand platform helps deliver Managed Security Services and the expertise, knowledge and infrastructure an organization needs to secure its information assets from Internet attacks. The X-Force team provides the foundation for a preemptive approach to Internet security. The X-Force team is one of the best-known commercial security research groups in the world. This group of security experts researches and evaluates vulnerabilities and security issues, develops assessment and countermeasure technology for IBM security products, and educates the public about emerging Internet threats. We welcome your feedback. Questions or comments regarding the content of this report should be addressed to [email protected]. 3 X-Force Threat Insight Quarterly IBM Security Solutions Evolution: From Nuisance to Weapon One of the more notable examples here is Brain3, a boot sector infector which originated in Pakistan and released in 1986, was Creeper, Wabbit, Animal, Elk Cloner, Brain, Vienna, Lehigh, one of the first examples of malware that infected PC’s running Stoned, Jerusalem. -

Programming with Windows Forms
A P P E N D I X A ■ ■ ■ Programming with Windows Forms Since the release of the .NET platform (circa 2001), the base class libraries have included a particular API named Windows Forms, represented primarily by the System.Windows.Forms.dll assembly. The Windows Forms toolkit provides the types necessary to build desktop graphical user interfaces (GUIs), create custom controls, manage resources (e.g., string tables and icons), and perform other desktop- centric programming tasks. In addition, a separate API named GDI+ (represented by the System.Drawing.dll assembly) provides additional types that allow programmers to generate 2D graphics, interact with networked printers, and manipulate image data. The Windows Forms (and GDI+) APIs remain alive and well within the .NET 4.0 platform, and they will exist within the base class library for quite some time (arguably forever). However, Microsoft has shipped a brand new GUI toolkit called Windows Presentation Foundation (WPF) since the release of .NET 3.0. As you saw in Chapters 27-31, WPF provides a massive amount of horsepower that you can use to build bleeding-edge user interfaces, and it has become the preferred desktop API for today’s .NET graphical user interfaces. The point of this appendix, however, is to provide a tour of the traditional Windows Forms API. One reason it is helpful to understand the original programming model: you can find many existing Windows Forms applications out there that will need to be maintained for some time to come. Also, many desktop GUIs simply might not require the horsepower offered by WPF. -

GOTOHELL.DLL: Software Dependencies and The
GOTOHELL.DLL Software Dependencies and the Maintenance of Microsoft Windows Stephanie Dick Daniel Volmar Harvard University Presented at “The Maintainers: A Conference” Stephens Institute of Technology, Hoboken, NJ April 9, 2016 Abstract Software never stands alone, but exists always in relation to the other soft- ware that enables it, the hardware that runs it, and the communities who make, own, and maintain it. Here we consider a phenomenon called “DLL hell,” a case in which those relationships broke down, endemic the to Mi- crosoft Windows platform in the mid-to-late 1990s. Software applications often failed because they required specific dynamic-link libraries (DLLs), which other applications may have overwritten with their own preferred ver- sions. We will excavate “DLL hell” for insight into the experience of modern computing, which emerged from the complex ecosystem of manufacturers, developers, and users who collectively held the Windows platform together. Furthermore, we propose that in producing Windows, Microsoft had to balance a unique and formidable tension between customer expectations and investor demands. Every day, millions of people rely on software that assumes Windows will behave a certain way, even if that behavior happens to be outdated, inconvenient, or just plain broken, leaving Microsoft “on the hook” for the uses or abuses that others make of its platform. Bound so tightly to its legacy, Windows had to maintain the old in order to pro- mote the new, and DLL hell highlights just how difficult this could be. We proceed in two phases: first, exploring the history of software componenti- zation in order to explain its implementation on the Windows architecture; and second, defining the problem and surveying the official and informal means with which IT professionals managed their unruly Windows systems, with special attention paid to the contested distinction between a flaw on the designer’s part and a lack of discipline within the using community. -

What Are Kernel-Mode Rootkits?
www.it-ebooks.info Hacking Exposed™ Malware & Rootkits Reviews “Accessible but not dumbed-down, this latest addition to the Hacking Exposed series is a stellar example of why this series remains one of the best-selling security franchises out there. System administrators and Average Joe computer users alike need to come to grips with the sophistication and stealth of modern malware, and this book calmly and clearly explains the threat.” —Brian Krebs, Reporter for The Washington Post and author of the Security Fix Blog “A harrowing guide to where the bad guys hide, and how you can find them.” —Dan Kaminsky, Director of Penetration Testing, IOActive, Inc. “The authors tackle malware, a deep and diverse issue in computer security, with common terms and relevant examples. Malware is a cold deadly tool in hacking; the authors address it openly, showing its capabilities with direct technical insight. The result is a good read that moves quickly, filling in the gaps even for the knowledgeable reader.” —Christopher Jordan, VP, Threat Intelligence, McAfee; Principal Investigator to DHS Botnet Research “Remember the end-of-semester review sessions where the instructor would go over everything from the whole term in just enough detail so you would understand all the key points, but also leave you with enough references to dig deeper where you wanted? Hacking Exposed Malware & Rootkits resembles this! A top-notch reference for novices and security professionals alike, this book provides just enough detail to explain the topics being presented, but not too much to dissuade those new to security.” —LTC Ron Dodge, U.S. -
CSCI E-170 Lecture 09: Attacker Motivations, Computer Crime and Secure Coding
CSCI E-170 Lecture 09: Attacker Motivations, Computer Crime and Secure Coding Simson L. Garfinkel Center for Research on Computation and Society Harvard University November 21, 2005 1 Today’s Agenda 1. Administrivia 2. Missing Readings for L09, L10 3. Threat Models: Who is the attacker? What can the attacker do? 4. Secure Coding 5. Translucent Databases 6. RFID 2 Administrivia 1. Quizes - If you are a remote student and you want it back, please email csci [email protected] with a fax number and we will fax it out. 2. Midterm Projects should be in. 3 Final Projects This is a research project, not a book review. You are expected to: 1. Create something and write about it. 2. Analyze something in detail. You have until next Monday to form groups of 4 students. Email group names and your proposed topic to csci [email protected]. Students who have not chosen groups will be assigned. 4 Why is building a secure system different than building a system that is: 1. Reliable 2. Safe 3. Easy-to-use ? 5 With security, there is an adversary. No reason to defend against an unbounded adversary. Why? 6 The nature of the adversary determines your defenses. Possible adversaries include: 1. Employees (good and bad) 2. High school students 3. Foreign Governments (“Titan Rain?”) Evaluate according to who they are and by what they can accomplish. 7 Remember RFC 602? Public acknowledgment of hackers on the Internet: 1. Sites used physical security have not taken measures to secure machines accessible over the network. -

A Programmer's Introduction to Visual Basic.NET
00 2203-x FM 5/25/01 9:57 AM Page i Dear Reader, I wanted to take this opportunity to explain the rationale behind this book showing up on your shelf for free. Quite some time ago, Sams Publishing determined that the next big thing to hit the programmer/developer community would be Microsoft’s Visual Studio.NET and the .NET Framework. After discussions with many of you, our authors and key Microsoft team members, Sams dedicated itself to a strategy that would support your efforts to learn the .NET Framework as efficiently and as quickly as possible. A Programmer’s Introduction to Visual Basic.NET is the perfect example of how our strong relationship with Microsoft and our dedication to bring- ing you authors who are already respected sources in the community suc- cessfully blend and show that Sams Publishing is the source for .NET learning. Bringing you a Beta2 compliant book by May 2001 was not an easy task. Sams called upon a respected author, Craig Utley, to take on this project. Craig holds a unique place in the VB community where he has been devel- oping in VB since version 1.0. He brings years of experience as a trainer, writer, and speaker to this project and gives you the solid reference you need to make the transition from VB to VB.NET. I hope this book gives you the tools you need to begin to learn VB.NET. I invite your comments and ideas as I work to make Sams the publisher you look to as your .NET learning resource. -

Computer Parasitology
Computer Parasitology Carey Nachenberg Symantec AntiVirus Research Center [email protected] Posted with the permission of Virus Bulletin http://www.virusbtn.com/ Table of Contents Table of Contents............................................................................................................................................................. 2 Introduction....................................................................................................................................................................... 4 Worm Classifications...................................................................................................................................................... 4 Worm Transport Classifications............................................................................................................................... 4 E-mail Worms ......................................................................................................................................................... 4 Arbitrary Protocol Worms: IRC Worms, TCP/IP Worms, etc. ...................................................................... 4 Worm Launch Classifications................................................................................................................................... 5 Self-launching Worms ........................................................................................................................................... 5 User-launched Worms ........................................................................................................................................... -

Managing the Evolution of .NET Programs
Managing the Evolution of .NET Programs Susan Eisenbach, Vladimir Jurisic and Chris Sadler Department of Computing Imperial College London, UK SW7 2BZ [sue, vj98]@doc.ic.ac.uk School of Computing Science Middlesex University London, UK N14 4YZ [email protected] Abstract Programs in the .NET environment consist of collaborating software components, and the Common Language Runtime has been designed in such a way that linking occurs ‘just-in-time’. This offers a good platform for transpar- ent evolution, provided that compatibility can be maintained between service- providing components and their clients. One goal of program evolution is to use the most recent version of each com- ponent that will actually link. We propose a model of a cache of interdepen- dent evolving components with operations defined to update this cache safely. A demonstration tool Dejavue.NET implements these ideas. 1 Introduction The dynamic link library (DLL) was invented to allow applications running on a sin- gle system to share code. Sharing code in this way confers several distinct benefits. In the first place, applications both when running in memory and when stored on disk are likely to be smaller because duplicated code has been eliminated. In the second place, applications accessing common code share a common functionality so they all do cer- tain things in the same way. This is good for the users, who get a reliable and predictable user interface. It is also makes the operating system design more straightforward, with provision of access to certain facilities through narrow and well-defined interfaces. The main benefit however, arises when the DLL needs to be corrected or enhanced – in other words, to evolve. -
NET Framework Overview
.NET Framework Overview .NET Framework, CLR, MSIL, Assemblies, CTS, etc. Svetlin Nakov Telerik Corporation www.telerik.com Table of Contents 1. What is .NET? Microsoft .NET platform architecture 2. What is .NET Framework? .NET Framework Architecture 3. Common Language Runtime (CLR) 4. Managed Code 5. Intermediate Language MSIL 6. Assemblies and Metadata 7. .NET Applications Table of Contents (2) 8. Common Language Infrastructure (CLI) and integration of different languages Common Language Specification (CLS) Common Type System (CTS) 9. Framework Class Library 10. Integrated Development Environment Visual Studio .NET Framework Microsoft's Platform for Application Development What is the .NET Platform? The .NET platform Microsoft's platform for software development Unified technology for development of almost any kind of applications GUI / Web / RIA / mobile / server / cloud / etc. .NET platform versions .NET Framework Silverlight / Windows Phone 7 .NET Compact Framework What is .NET Framework? .NET Framework An environment for developing and executing .NET applications Unified programming model, set of languages, class libraries, infrastructure, components and tools for application development Environment for controlled execution of managed code It is commonly assumed that .NET platform == .NET Framework .NET Framework Components Common Language Runtime (CLR) Environment for controlled execution of programmed code – like a virtual machine Executes .NET applications Framework Class Library (FCL) Standard class library