Computer Parasitology
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Strategies of Computer Worms
304543_ch09.qxd 1/7/05 9:05 AM Page 313 CHAPTER 9 Strategies of Computer Worms “Worm: n., A self-replicating program able to propagate itself across network, typically having a detrimental effect.” —Concise Oxford English Dictionary, Revised Tenth Edition 313 304543_ch09.qxd 1/7/05 9:05 AM Page 314 Chapter 9—Strategies of Computer Worms 9.1 Introduction This chapter discusses the generic (or at least “typical”) structure of advanced computer worms and the common strategies that computer worms use to invade new target systems. Computer worms primarily replicate on networks, but they represent a subclass of computer viruses. Interestingly enough, even in security research communities, many people imply that computer worms are dramatically different from computer viruses. In fact, even within CARO (Computer Antivirus Researchers Organization), researchers do not share a common view about what exactly can be classified as a “worm.” We wish to share a common view, but well, at least a few of us agree that all computer worms are ultimately viruses1. Let me explain. The network-oriented infection strategy is indeed a primary difference between viruses and computer worms. Moreover, worms usually do not need to infect files but propagate as standalone programs. Additionally, several worms can take con- trol of remote systems without any help from the users, usually exploiting a vul- nerability or set of vulnerabilities. These usual characteristics of computer worms, however, do not always hold. Table 9.1 shows several well-known threats. Table -
Tangled Web : Tales of Digital Crime from the Shadows of Cyberspace
TANGLED WEB Tales of Digital Crime from the Shadows of Cyberspace RICHARD POWER A Division of Macmillan USA 201 West 103rd Street, Indianapolis, Indiana 46290 Tangled Web: Tales of Digital Crime Associate Publisher from the Shadows of Cyberspace Tracy Dunkelberger Copyright 2000 by Que Corporation Acquisitions Editor All rights reserved. No part of this book shall be reproduced, stored in a Kathryn Purdum retrieval system, or transmitted by any means, electronic, mechanical, pho- Development Editor tocopying, recording, or otherwise, without written permission from the Hugh Vandivier publisher. No patent liability is assumed with respect to the use of the infor- mation contained herein. Although every precaution has been taken in the Managing Editor preparation of this book, the publisher and author assume no responsibility Thomas Hayes for errors or omissions. Nor is any liability assumed for damages resulting from the use of the information contained herein. Project Editor International Standard Book Number: 0-7897-2443-x Tonya Simpson Library of Congress Catalog Card Number: 00-106209 Copy Editor Printed in the United States of America Michael Dietsch First Printing: September 2000 Indexer 02 01 00 4 3 2 Erika Millen Trademarks Proofreader Benjamin Berg All terms mentioned in this book that are known to be trademarks or ser- vice marks have been appropriately capitalized. Que Corporation cannot Team Coordinator attest to the accuracy of this information. Use of a term in this book should Vicki Harding not be regarded as affecting the validity of any trademark or service mark. Design Manager Warning and Disclaimer Sandra Schroeder Every effort has been made to make this book as complete and as accurate Cover Designer as possible, but no warranty or fitness is implied. -

The Norman Book on Computer Viruses Ii Z the Norman Book on Computer Viruses
The Norman Book on Computer Viruses ii z The Norman Book on Computer Viruses Norman ASA is not liable for any other form of loss or damage arising from use of the documentation or from errors or deficiencies therein, including but not limited to loss of earnings. In particular, and without the limitations imposed by the licensing agreement with regard to any special use or purpose, Norman ASA will in no event be liable for loss of profits or other commercial damage including but not limited to incidental or consequential damages. The information in this document as well as the functionality of the software is subject to change without notice. No part of this documentation may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording or information storage and retrieval systems, for any purpose other than the purchaser's personal use, without the explicit written permission of Norman ASA. Contributors to The Norman Book on Viruses: Snorre Fagerland, Sylvia Moon, Kenneth Walls, Carl Bretteville Edited by Camilla Jaquet and Yngve Ness The Norman logo is a registered trademark of Norman ASA. Names of products mentioned in this documentation are either trademarks or registered trademarks of their respective owners. They are mentioned for identification purposes only. Norman documentation is Copyright © 1990-2002 Norman ASA. All rights reserved. October 2001 Copyright © 1990-2002 Norman z iii Norman Offices Norman Data Defense Systems Pty Ltd 6 Sarton Road, Clayton, Victoria, 3168 Australia. Tel: +61 3 9562 7655 Fax: +61 3 9562 9663 E-mail: [email protected] Web: http://www.norman.com.au Norman Data Defense Systems A/S Dronningensgade 23, DK-5000 Odense C, Denmark Tel. -

UTTARAKHAND OPEN UNIVERSITY Teen Pani Bypass Road, Near Transport Nagar, Haldwani -263139 Phone No- 05946 - 261122, 261123 Toll Free No
CYBER CRIMES AND CONSUMER PROTECTION IN CYBERSPACE CYL-104 [1] CYL- 104 Cyber Crimes And Consumer Protection in Cyber Space School of Law UTTARAKHAND OPEN UNIVERSITY Teen Pani Bypass Road, Near Transport Nagar, Haldwani -263139 Phone No- 05946 - 261122, 261123 Toll Free No. 18001804025 Fax No.- 05946-264232, Email- [email protected], http://uou.ac.in Uttarakhand Open University CYBER CRIMES AND CONSUMER PROTECTION IN CYBERSPACE CYL-104 [2] BOARD OF STUDIES Professor Girija Prasad Pande, Director, School of Law, Uttarakhand Open University, Haldwani, Nainital. Professor J.S.Bisht, Faculty of Law,S.S. Jeena Campus, Almora,Kumaun University, Nainital, Uttarakhand. Professor B.P. Maithani, Former RTI Advisor, Government of Uttarakhand Mr. Deepankur Joshi, Coordinator School of Law, Uttarakhand Open University, Haldwani, (Nainital). UNIT WRITING UNIT WRITERS UNIT [1] Dr. Razit Sharma, Assistant Professor, Unit- 1,2,3,4 Law College, Uttaranchal University, Dehradun Uttarakhand [2] Ms. Sapna Agarwal, Advocate High Court of Uttarakhand, Unit- 5,6,7 Nainital [3 Mr. Rajeev Bhatt, Advocate High Court of Uttarakhand, Ex. RTI Advisor Kumaun University Nainital, Ex. Assistant Professor Unity Unit- 8 ,9,10 Law College Rudrapur [4] Dr. Sushim Shukla, Assistant Professor, Unit- 11, 12, 13 Law College, Uttaranchal University, Dehradun Uttarakhand EDITOR Mr. Deepankur Joshi, Coordinator, School of Law, Uttarakhand Open University, Haldwani, (Nainital) Copyright © Uttarakhand Open University, Haldwani, Nainital Edition- 2018, Pre Publication copy for Limited Circulation ISBN- Publication- Directorate of Studies and Publication, Uttarakhand Open University, Haldwani, Nainital. E- Mail: [email protected] . Uttarakhand Open University CYBER CRIMES AND CONSUMER PROTECTION IN CYBERSPACE CYL-104 [3] POST GRADUATE DIPLOMA IN CYBER LAW CYL- 104 CYBERCRIMES AND CONSUMER PROTECTION IN CYBER SPACE INDEX S. -

"Year 2000 Y2K" December 28, 1999
NIPC ADVISORY 99-031 "Year 2000 Y2K" December 28, 1999 Introduction Large-scale U.S. infrastructure disruptions are not expected from "Y2K failures" during the Y2K transition period. However we are prepared for a possible increase in real or reported criminal cyber activity (such as hacking and spreading computer viruses), considering the heightened awareness of and media focus on malicious activity during the Y2K period. Any increased criminal activity during the Y2K period could raise the level of problems in infrastructure systems, adding to genuine Y2K-generated issues and the normal level of infrastructure concerns. We anticipate encountering both known and new viruses and hacking exploits. We could see the dissemination of several new and possibly destructive viruses, and the successful exploitation of both corporate and government information systems. But even these possibilities reflect only a larger assembly of the same kinds of malicious activity seen and addressed every day. Finally, known and possible extremist or apocalyptic terrorist activity in the United States by individuals or groups suggests the possibility of threats to domestic infrastructures. For example, the media have reported arrests of certain individuals allegedly planning violent actions against electric power and oil and gas facilities. These indications of possible threats to our infrastructures warrant an increased vigilance to protect against both cyber and physical threats to our nation's critical infrastructures. Summary The Y2K Transition might be seen by potential malefactors as an unprecedented opportunity for malicious code release and associated publicity, where a new and significant exploit can achieve a widespread notoriety in the information security and hacker world. -
Chapter 3: Viruses, Worms, and Blended Threats
Chapter 3 Chapter 3: Viruses, Worms, and Blended Threats.........................................................................46 Evolution of Viruses and Countermeasures...................................................................................46 The Early Days of Viruses.................................................................................................47 Beyond Annoyance: The Proliferation of Destructive Viruses .........................................48 Wiping Out Hard Drives—CIH Virus ...................................................................48 Virus Programming for the Masses 1: Macro Viruses...........................................48 Virus Programming for the Masses 2: Virus Generators.......................................50 Evolving Threats, Evolving Countermeasures ..................................................................51 Detecting Viruses...................................................................................................51 Radical Evolution—Polymorphic and Metamorphic Viruses ...............................53 Detecting Complex Viruses ...................................................................................55 State of Virus Detection.........................................................................................55 Trends in Virus Evolution..................................................................................................56 Worms and Vulnerabilities ............................................................................................................57 -

Virus Bulletin, June 1999
ISSN 0956-9979 JUNE 1999 THE INTERNATIONAL PUBLICATION ON COMPUTER VIRUS PREVENTION, RECOGNITION AND REMOVAL Editor: Francesca Thorneloe CONTENTS Technical Consultant: Fraser Howard Technical Editor: Jakub Kaminski COMMENT Flashback – When the Chips were Down 2 Consulting Editors: VIRUS PREVALENCE TABLE 3 Nick FitzGerald, Independent Consultant, NZ Ian Whalley, Sophos Plc, UK NEWS Richard Ford, Independent Consultant, USA 1. Two Be or not Two Be 3 Edward Wilding, Maxima Group Plc, UK 2. ThanY2Ks for the Memory! 3 LETTERS 4 IN THIS ISSUE: VIRUS ANALYSES 1. Beast Regards 6 • Oh dear, oh dear, oh dear Virus Bulletin: At long last 2. Papa Don’t Preach 8 the Letters page makes a comeback in this issue. Love it or hate it, it’s your way to have your say, starting on p.4. A DAY IN THE LIFE • Define your terms: Find out all you need to know about Educating Who? 10 polymorphism. Two researchers from Kaspersky Lab set FEATURES the record straight on p.14. 1. Virus Writers – Part 2 12 • Don’t panic! Our tutorial this month paves the way for 2. pOLEmorphism 14 future corporate case studies. In clear and easy-to-follow steps, the actions to take in the event of a virus or malware TUTORIAL outbreak on your system are documented on p.16. When Barriers Break Down 16 PRODUCT REVIEWS 1. DialogueScience AntiVirus Kit v3.0 18 2. eSafe Protect Enterprise 21 END NOTES AND NEWS 24 VIRUS BULLETIN ©1999 Virus Bulletin Ltd, The Pentagon, Abingdon, Oxfordshire, OX14 3YP, England. Tel +44 1235 555139. /99/$0.00+2.50 No part of this publication may be reproduced, stored in a retrieval system, or transmitted in any form without the prior written permission of the publishers. -
Cybernotes Issue #4-99 February 17, 1999
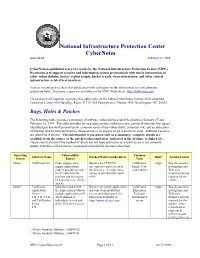
National Infrastructure Protection Center CyberNotes Issue #4-99 February 17, 1999 CyberNotes is published every two weeks by the National Infrastructure Protection Center (NIPC). Its mission is to support security and information system professionals with timely information on cyber vulnerabilities, hacker exploit scripts, hacker trends, virus information, and other critical infrastructure-related best practices. You are encouraged to share this publication with colleagues in the information and infrastructure protection field. Electronic copies are available on the NIPC Web site at http://www.nipc.gov. Please direct any inquiries regarding this publication to the Editor-CyberNotes, National Infrastructure Protection Center, FBI Building, Room 11719, 935 Pennsylvania Avenue, NW, Washington, DC, 20535. Bugs, Holes & Patches The following table provides a summary of software vulnerabilities identified between January 27 and February 12, 1999. The table provides the operating system, software name, potential vulnerability/impact, identified patches/workarounds/alerts, common name of the vulnerability, potential risk, and an indication of whether attacks have utilized this vulnerability or an exploit script is known to exist. Software versions are identified if known. This information is presented only as a summary; complete details are available from the source of the patch/workaround/alert, indicated in the footnote or linked site. Please note that even if the method of attack has not been utilized or an exploit script is not currently widely available on the Internet, a potential vulnerability has been identified. Operating Vulnerability/ Common Software Name Patches/Workarounds/Alerts Risk* Attacks/Scripts System Impact Name Allaire1 ColdFusion 4.0 Code snippets from Remove the CFDOCS ColdFusion High Bug discussed in sample applications directory or restrict access to Sample Code newsgroups and make it possible to make the directory. -
IBM X-Force Threat Insight Quarterly 2 X-Force Threat Insight Quarterly IBM Security Solutions
IBM Security Solutions May 2011 IBM X-Force Threat Insight Quarterly 2 X-Force Threat Insight Quarterly IBM Security Solutions Contents About the report 2 About the Report The IBM X-Force® Threat Insight Quarterly is designed to highlight some of the most significant threats and challenges 3 Evolution: From Nuisance to Weapon facing security professionals today. This report is a product of IBM Managed Security Services and the IBM X-Force 8 Prolific and Impacting Issues of Q1 2011 research and development team. Each issue focuses on specific challenges and provides a recap of the most significant recent 16 References online threats. IBM Managed Security Services are designed to help an organization improve its information security, by outsourcing security operations or supplementing your existing security teams. The IBM protection on-demand platform helps deliver Managed Security Services and the expertise, knowledge and infrastructure an organization needs to secure its information assets from Internet attacks. The X-Force team provides the foundation for a preemptive approach to Internet security. The X-Force team is one of the best-known commercial security research groups in the world. This group of security experts researches and evaluates vulnerabilities and security issues, develops assessment and countermeasure technology for IBM security products, and educates the public about emerging Internet threats. We welcome your feedback. Questions or comments regarding the content of this report should be addressed to [email protected]. 3 X-Force Threat Insight Quarterly IBM Security Solutions Evolution: From Nuisance to Weapon One of the more notable examples here is Brain3, a boot sector infector which originated in Pakistan and released in 1986, was Creeper, Wabbit, Animal, Elk Cloner, Brain, Vienna, Lehigh, one of the first examples of malware that infected PC’s running Stoned, Jerusalem. -
Basics of Ethical Hacking – Manthan M. Desai
Hacking For Beginners – Manthan Desai 2010 Legal Disclaimer Any proceedings and or activities related to the material contained within this book are exclusively your liability. The misuse and mistreat of the information in this book can consequence in unlawful charges brought against the persons in question. The authors and review analyzers will not be held responsible in the event any unlawful charges brought against any individuals by misusing the information in this book to break the law. This book contains material and resources that can be potentially destructive or dangerous. If you do not fully comprehend something on this book, don‘t study this book. Please refer to the laws and acts of your state/region/ province/zone/territory or country before accessing, using, or in any other way utilizing these resources. These materials and resources are for educational and research purposes only. Do not attempt to violate the law with anything enclosed here within. If this is your intention, then leave now. While using this book and reading various hacking tutorials, you agree to follow the below mentioned terms and conditions: 1. All the information provided in this book is for educational purposes only. The book author is no way responsible for any misuse of the information. 2. "Hacking for Beginners” is just a term that represents the name of the book and is not a book that provides any illegal information. “Hacking for Beginners” is a book related to Computer Security and not a book that promotes hacking/cracking/software piracy. 3. This book is totally meant for providing information on "Computer Security”, "Computer Programming” and other related topics and is no way related towards the terms "CRACKING” or "HACKING” (Unethical). -

What Are Kernel-Mode Rootkits?
www.it-ebooks.info Hacking Exposed™ Malware & Rootkits Reviews “Accessible but not dumbed-down, this latest addition to the Hacking Exposed series is a stellar example of why this series remains one of the best-selling security franchises out there. System administrators and Average Joe computer users alike need to come to grips with the sophistication and stealth of modern malware, and this book calmly and clearly explains the threat.” —Brian Krebs, Reporter for The Washington Post and author of the Security Fix Blog “A harrowing guide to where the bad guys hide, and how you can find them.” —Dan Kaminsky, Director of Penetration Testing, IOActive, Inc. “The authors tackle malware, a deep and diverse issue in computer security, with common terms and relevant examples. Malware is a cold deadly tool in hacking; the authors address it openly, showing its capabilities with direct technical insight. The result is a good read that moves quickly, filling in the gaps even for the knowledgeable reader.” —Christopher Jordan, VP, Threat Intelligence, McAfee; Principal Investigator to DHS Botnet Research “Remember the end-of-semester review sessions where the instructor would go over everything from the whole term in just enough detail so you would understand all the key points, but also leave you with enough references to dig deeper where you wanted? Hacking Exposed Malware & Rootkits resembles this! A top-notch reference for novices and security professionals alike, this book provides just enough detail to explain the topics being presented, but not too much to dissuade those new to security.” —LTC Ron Dodge, U.S. -
![Reversing Malware [Based on Material from the Textbook]](https://docslib.b-cdn.net/cover/8924/reversing-malware-based-on-material-from-the-textbook-1438924.webp)
Reversing Malware [Based on Material from the Textbook]
SoftWindows 11/23/05 Reversing Malware [based on material from the textbook] Reverse Engineering (Reversing Malware) © SERG What is Malware? • Malware (malicious software) is any program that works against the interest of the system’s user or owner. • Question: Is a program that spies on the web browsing habits of the employees of a company considered malware? • What if the CEO authorized the installation of the spying program? Reverse Engineering (Reversing Malware) © SERG Reversing Malware • Revering is the strongest weapon we have against the creators of malware. • Antivirus researchers engage in reversing in order to: – analyze the latest malware, – determine how dangerous the malware is, – learn the weaknesses of malware so that effective antivirus programs can be developed. Reverse Engineering (Reversing Malware) © SERG Distributed Objects 1 SoftWindows 11/23/05 Uses of Malware • Why do people develop and deploy malware? – Financial gain – Psychological urges and childish desires to “beat the system”. – Access private data – … Reverse Engineering (Reversing Malware) © SERG Typical Purposes of Malware • Backdoor access: – Attacker gains unlimited access to the machine. • Denial-of-service (DoS) attacks: – Infect a huge number of machines to try simultaneously to connect to a target server in hope of overwhelming it and making it crash. • Vandalism: – E.g., defacing a web site. • Resource Theft: – E.g., stealing other user’s computing and network resources, such as using your neighbors’ Wireless Network. • Information Theft: – E.g., stealing other user’s credit card numbers. Reverse Engineering (Reversing Malware) © SERG Types of Malware • Viruses • Worms • Trojan Horses • Backdoors • Mobile code • Adware • Sticky software Reverse Engineering (Reversing Malware) © SERG Distributed Objects 2 SoftWindows 11/23/05 Viruses • Viruses are self-replicating programs that usually have a malicious intent.