The Prosecution of Nationai Security Leaks Under the Espionage a Ct
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Running Head: Wikileaks and the Censorship of News Media in the U.S
RUNNING HEAD: WIKILEAKS AND THE CENSORSHIP OF NEWS MEDIA IN THE U.S. WikiLeaks and the Censorship of News Media in the U.S. Author: Asa Hilmersson Faculty Mentor: Professor Keeton Ramapo College of New Jersey WIKILEAKS AND THE CENSORSHIP OF NEWS MEDIA IN THE U.S. 1 “Censorship in free societies is infinitely more sophisticated and thorough than in dictatorships, because ‘unpopular ideas can be silenced, and inconvenient facts kept dark, without any need for an official ban’.” – George Orwell Introduction Throughout history, media has been censored or obscured in different ways which seem to fit the dominant ideology or ruling regime. As William Powers (1995) from The Washington Post said; the Nazis were censored, Big Brother was a censor, and nightmare regimes such as China have censors. Though we are all aware of censorship around the world and in history, little do we look to ourselves because as Powers writes, “None of that [censorship] for us. This is America” (para. 3). People in America have long been led to believe that they live in a free world where every voice is heard. It is not until someone uses the opportunities of this right that we see that this freedom of speech might only be an illusion. The emergence of WikiLeaks in 2010 and the censorship exercised against this organization by the United States’ government exemplifies the major obstacles individuals can face when seeking to expose potential wrongdoing by public officials. Through questioning of media’s power as whistleblowers it is hinted that there are institutions which may carry more weight than the truth in making decisions that affect that public interest. -

Government Hacking What Is It and When Should It Be Used?
Government Hacking What is it and when should it be used? Encryption is a critical component of our day-to-day lives. For much of the world, basic aspects of life rely on encryption to function. Power systems, transport, financial markets, and baby monitors1 are more trustworthy because of encryption. Encryption protects our most vulnerable data from criminals and terrorists, but it can also hide criminal content from governments. Government hacking is one of the approaches national security and law enforcement agencies use to obtain access to otherwise encrypted information (e.g. the FBI hired a hacking company to unlock the iPhone at the center of the San Bernardino case2). It complements their other efforts to obtain exceptional access3 by asking or requiring tech companies to have the technical ability to decrypt users’ content when it is needed for law enforcement purposes. The Internet Society believes strong encryption is vital to the health of the Internet and is deeply concerned about any policy or action that might put that in jeopardy — regardless of its motivation. Government hacking poses a risk of collateral damage to both the Internet and its users, and as such should only ever be considered as a tool of last resort. Government hacking defined We define ‘government hacking’ as government entities (e.g. national security or law enforcement agencies or private actors on their behalf) exploiting vulnerabilities in systems, software, or hardware to gain access to information that is otherwise encrypted, or inaccessible. Dangers of government hacking Exploiting vulnerabilities of any kind, whether for law enforcement purposes, security testing, or any other purpose, should not be taken lightly. -

The Views of the U.S. Left and Right on Whistleblowers Whistleblowers on Right and U.S
The Views of the U.S. Left and Right on Whistleblowers Concerning Government Secrets By Casey McKenzie Submitted to Central European University Department of International Relations and European Studies In partial fulfillment of the requirements for the degree of Master of Arts Supervisor: Professor Erin Kristin Jenne Word Count: 12,868 CEU eTD Collection Budapest Hungary 2014 Abstract The debates on whistleblowers in the United States produce no simple answers and to make thing more confusing there is no simple political left and right wings. The political wings can be further divided into far-left, moderate-left, moderate-right, far-right. To understand the reactions of these political factions, the correct political spectrum must be applied. By using qualitative content analysis of far-left, moderate-left, moderate-right, far-right news sites I demonstrate the debate over whistleblowers belongs along a establishment vs. anti- establishment spectrum. CEU eTD Collection i Acknowledgments I would like to express my fullest gratitude to my supervisor, Erin Kristin Jenne, for the all the help see gave me and without whose guidance I would have been completely lost. And to Danielle who always hit me in the back of the head when I wanted to give up. CEU eTD Collection ii Table of Contents Abstract ....................................................................................................................................... i Acknowledgments..................................................................................................................... -

Wikileaks and the Institutional Framework for National Security Disclosures
THE YALE LAW JOURNAL PATRICIA L. BELLIA WikiLeaks and the Institutional Framework for National Security Disclosures ABSTRACT. WikiLeaks' successive disclosures of classified U.S. documents throughout 2010 and 2011 invite comparison to publishers' decisions forty years ago to release portions of the Pentagon Papers, the classified analytic history of U.S. policy in Vietnam. The analogy is a powerful weapon for WikiLeaks' defenders. The Supreme Court's decision in the Pentagon Papers case signaled that the task of weighing whether to publicly disclose leaked national security information would fall to publishers, not the executive or the courts, at least in the absence of an exceedingly grave threat of harm. The lessons of the PentagonPapers case for WikiLeaks, however, are more complicated than they may first appear. The Court's per curiam opinion masks areas of substantial disagreement as well as a number of shared assumptions among the Court's members. Specifically, the Pentagon Papers case reflects an institutional framework for downstream disclosure of leaked national security information, under which publishers within the reach of U.S. law would weigh the potential harms and benefits of disclosure against the backdrop of potential criminal penalties and recognized journalistic norms. The WikiLeaks disclosures show the instability of this framework by revealing new challenges for controlling the downstream disclosure of leaked information and the corresponding likelihood of "unintermediated" disclosure by an insider; the risks of non-media intermediaries attempting to curtail such disclosures, in response to government pressure or otherwise; and the pressing need to prevent and respond to leaks at the source. AUTHOR. -

The Use of Prior Restraints on Publication in the Age of Wikileaks
35 6 June 2018 Patent Volume 35 ▲ Number 6 ▲ JUNE 2018 Ronald L. Johnston, Arnold & Porter, LLP, Editor-in-Chief The Use of Prior Restraints on Publication in the Age of Wikileaks By CJ Griffin and Frank Corrado s James Madison put it, “A popular Government, The rationale for that principle is simple: If the gov- Awithout popular information, or the means of ernment can ban publication of speech, it can control acquiring it, is but a Prologue to a Farce or a Tragedy; or, what the public knows about governmental operations perhaps both. Knowledge will forever govern ignorance: and thereby deprive citizens of their ability to make And a people who mean to be their own Governors, intelligent decisions about governmental action. Too must arm themselves with the power which knowl- often, government favors secrecy over disclosure. The edge gives.”1 Free speech is essential to effective self- presumption against prior restraints ensures that officials government. A democracy cannot function if its citi- cannot indulge that propensity. It prevents the govern- zens do not know what their government is doing. ment from enjoining purportedly “secret” or “sensitive” For that reason, the First Amendment significantly information that may really be embarrassing, unsavory, limits the government’s ability to control the flow or indicative of government illegality or abuse. of information to the public. In particular, the First Of course, legitimate reasons exist for government Amendment renders prior restraints on speech pre- secrecy. As the Supreme Court said in Near v. Minne- sumptively unconstitutional.2 Even if the government sota,3 the seminal case on prior restraints, “no one would could punish the speech after the fact, it cannot—absent question but that a government might prevent actual a heavy burden of justification—prohibit the publica- obstruction to its recruiting service or the publica- tion of that speech. -

As Assange Awaits Ruling, Wikileaks Faces Its Fate 1 November 2011, by RAPHAEL G
As Assange awaits ruling, WikiLeaks faces its fate 1 November 2011, By RAPHAEL G. SATTTER , Associated Press Harvard University's Belfer Center for Science and International Affairs. Legal analysts were predicting a ruling in favor of extradition. "Very, very few people defeat a European Arrest Warrant," said Julian Knowles, an extradition lawyer at London's Matrix Chambers who has been following the case. "The courts in England generally lean in favor of extradition." Assange may have the right to challenge an This is a Monday, Feb. 7, 2011 file photo of WikiLeaks unfavorable verdict in Britain's Supreme Court. But founder Julian Assange as he leaves Belmarsh Magistrates' Court in London. Assange on Tuesday Nov. Knowles said that if he were denied leave to 1, 2011 awaits a judge's extradition verdict, it could be appeal, it could be only days before he were sent to WikiLeaks' very future that's at stake. Its finances under Scandinavia to face allegations of sex crimes. pressure and some of its biggest revelations already public, WikiLeaks may not have the strength to survive if That result could be devastating for WikiLeaks. Britain's High Court judge decides Wednesday in favor of a Swedish request to extradite Assange to face trial For much of the past year Assange has been over rape allegations, some experts argue. (AP running the website from a supporter's country Photo/Kirsty Wigglesworth, File) manor in eastern England, where the terms of his bail have confined him to virtual house arrest. The 40-year-old Australian says he has 20 staff (AP) -- As Julian Assange awaits a judge's members, but it's unclear who might take over were extradition verdict, it could be WikiLeaks' very he jailed. -

USA -V- Julian Assange Judgment
JUDICIARY OF ENGLAND AND WALES District Judge (Magistrates’ Court) Vanessa Baraitser In the Westminster Magistrates’ Court Between: THE GOVERNMENT OF THE UNITED STATES OF AMERICA Requesting State -v- JULIAN PAUL ASSANGE Requested Person INDEX Page A. Introduction 2 a. The Request 2 b. Procedural History (US) 3 c. Procedural History (UK) 4 B. The Conduct 5 a. Second Superseding Indictment 5 b. Alleged Conduct 9 c. The Evidence 15 C. Issues Raised 15 D. The US-UK Treaty 16 E. Initial Stages of the Extradition Hearing 25 a. Section 78(2) 25 b. Section 78(4) 26 I. Section 78(4)(a) 26 II. Section 78(4)(b) 26 i. Section 137(3)(a): The Conduct 27 ii. Section 137(3)(b): Dual Criminality 27 1 The first strand (count 2) 33 The second strand (counts 3-14,1,18) and Article 10 34 The third strand (counts 15-17, 1) and Article 10 43 The right to truth/ Necessity 50 iii. Section 137(3)(c): maximum sentence requirement 53 F. Bars to Extradition 53 a. Section 81 (Extraneous Considerations) 53 I. Section 81(a) 55 II. Section 81(b) 69 b. Section 82 (Passage of Time) 71 G. Human Rights 76 a. Article 6 84 b. Article 7 82 c. Article 10 88 H. Health – Section 91 92 a. Prison Conditions 93 I. Pre-Trial 93 II. Post-Trial 98 b. Psychiatric Evidence 101 I. The defence medical evidence 101 II. The US medical evidence 105 III. Findings on the medical evidence 108 c. The Turner Criteria 111 I. -

PEER-REVIEW FEEDBACK on the GOODNESS FIELD: a Guidebook for Proactive Nonviolence
PEER-REVIEW FEEDBACK ON THE GOODNESS FIELD: A Guidebook for Proactive Nonviolence Bob Aldridge's powerful book, The Goodness Field: A Guidebook for Proactive Nonviolence points out the need and opportunity for a Global Satyagraha Movement – nonviolent, active, creative, and compassionate – to challenge the US addiction to power and greed which feeds our nation's endless wars and empire. Aldridge gives some very helpful suggestions for how to build that movement. This is not a pipe dream. We, the world's people can make it happen! – David Hartsough Author, Waging Peace: Global Adventures of a Lifelong Activist Co-Founder, Nonviolent Peaceforce and World beyond War - - - - I am in wholehearted agreement with Bob Aldridge's call for a "Global Satyagraha Movement inspired by a Global Constructive Pro- gram.” I'm glad to say, also, that these very ideas are catching on. If humanity is to rescue itself from the materialism, the low human image based on outdated science, and the devastation that they are causing to our personal and social lives -- indeed for our continued existence -- I can see no other way of doing that than the discovery of what he calls the "goodness field" that science is beginning to discover and traditional wisdom has long spoken of, by whatever name. – Michael N. Nagler President, Metta Center for Nonviolence Author, The Third Harmony: Nonviolence and the New Story of Human Nature - - - - Every so often an elder, whose life has embodied the way of faith, peace and justice, writes a “testament” (as Jim Douglass rightly calls this book), one that peers well past what the rest of us see. -
The Theory of Prosecution You Love for Julian Assange May Look Different When Applied to Jason Leopold
THE THEORY OF PROSECUTION YOU LOVE FOR JULIAN ASSANGE MAY LOOK DIFFERENT WHEN APPLIED TO JASON LEOPOLD The WaPo confirmed something Seamus Hughes disclosed last night: Sometime before August 22, EDVA had filed a sealed complaint (not indictment) against Julian Assange. WikiLeaks founder Julian Assange has been charged under seal, prosecutors inadvertently revealed in a recently unsealed court filing — a development that could significantly advance the probe into Russian interference in the 2016 election and have major implications for those who publish government secrets. The disclosure came in a filing in a case unrelated to Assange. Assistant U.S. Attorney Kellen S. Dwyer, urging a judge to keep the matter sealed, wrote that “due to the sophistication of the defendant and the publicity surrounding the case, no other procedure is likely to keep confidential the fact that Assange has been charged.” Later, Dwyer wrote the charges would “need to remain sealed until Assange is arrested.” Dwyer is also assigned to the WikiLeaks case. People familiar with the matter said what Dwyer was disclosing was true, but unintentional. The confirmation closely follows a WSJ story describing increased confidence that the US will succeed in extraditing Assange for trial. The confirmation that Assange has been charged has set off a frenzy, both among Assange supporters who claim this proves their years of claims he was indicted back in 2011 and insisting that charging him now would amount to criminalizing journalism, and among so-called liberals attacking Assange lawyer Barry Pollack’s scolding of DOJ for breaking their own rules. I’ve long been on record saying that I think most older theories of charging Assange would be very dangerous for journalism. -

Disinformation, and Influence Campaigns on Twitter 'Fake News'
Disinformation, ‘Fake News’ and Influence Campaigns on Twitter OCTOBER 2018 Matthew Hindman Vlad Barash George Washington University Graphika Contents Executive Summary . 3 Introduction . 7 A Problem Both Old and New . 9 Defining Fake News Outlets . 13 Bots, Trolls and ‘Cyborgs’ on Twitter . 16 Map Methodology . 19 Election Data and Maps . 22 Election Core Map Election Periphery Map Postelection Map Fake Accounts From Russia’s Most Prominent Troll Farm . 33 Disinformation Campaigns on Twitter: Chronotopes . 34 #NoDAPL #WikiLeaks #SpiritCooking #SyriaHoax #SethRich Conclusion . 43 Bibliography . 45 Notes . 55 2 EXECUTIVE SUMMARY This study is one of the largest analyses to date on how fake news spread on Twitter both during and after the 2016 election campaign. Using tools and mapping methods from Graphika, a social media intelligence firm, we study more than 10 million tweets from 700,000 Twitter accounts that linked to more than 600 fake and conspiracy news outlets. Crucially, we study fake and con- spiracy news both before and after the election, allowing us to measure how the fake news ecosystem has evolved since November 2016. Much fake news and disinformation is still being spread on Twitter. Consistent with other research, we find more than 6.6 million tweets linking to fake and conspiracy news publishers in the month before the 2016 election. Yet disinformation continues to be a substantial problem postelection, with 4.0 million tweets linking to fake and conspiracy news publishers found in a 30-day period from mid-March to mid-April 2017. Contrary to claims that fake news is a game of “whack-a-mole,” more than 80 percent of the disinformation accounts in our election maps are still active as this report goes to press. -
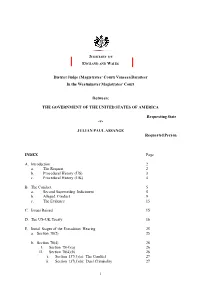
Julian Assange Judgment
JUDICIARY OF ENGLAND AND WALES District Judge (Magistrates’ Court) Vanessa Baraitser In the Westminster Magistrates’ Court Between: THE GOVERNMENT OF THE UNITED STATES OF AMERICA Requesting State -v- JULIAN PAUL ASSANGE Requested Person INDEX Page A. Introduction 2 a. The Request 2 b. Procedural History (US) 3 c. Procedural History (UK) 4 B. The Conduct 5 a. Second Superseding Indictment 5 b. Alleged Conduct 9 c. The Evidence 15 C. Issues Raised 15 D. The US-UK Treaty 16 E. Initial Stages of the Extradition Hearing 25 a. Section 78(2) 25 b. Section 78(4) 26 I. Section 78(4)(a) 26 II. Section 78(4)(b) 26 i. Section 137(3)(a): The Conduct 27 ii. Section 137(3)(b): Dual Criminality 27 1 The first strand (count 2) 33 The second strand (counts 3-14,1,18) and Article 10 34 The third strand (counts 15-17, 1) and Article 10 43 The right to truth/ Necessity 50 iii. Section 137(3)(c): maximum sentence requirement 53 F. Bars to Extradition 53 a. Section 81 (Extraneous Considerations) 53 I. Section 81(a) 55 II. Section 81(b) 69 b. Section 82 (Passage of Time) 71 G. Human Rights 76 a. Article 6 84 b. Article 7 82 c. Article 10 88 H. Health – Section 91 92 a. Prison Conditions 93 I. Pre-Trial 93 II. Post-Trial 98 b. Psychiatric Evidence 101 I. The defence medical evidence 101 II. The US medical evidence 105 III. Findings on the medical evidence 108 c. The Turner Criteria 111 I. -

STATEMENT for the RECORD Assistant United States Attorney Aaron S
STATEMENT FOR THE RECORD Assistant United States Attorney Aaron S. J. Zelinsky House Judiciary Committee June 24, 2020 Good afternoon, Chairman Nadler, ranking Member Jordan, and Members of the Committee. In response to your subpoena, I am prepared to testify before you today about the sentencing in UnitedStates v.Roger Stone. Since 2014, I have been privileged to serve as one of over 5,000 Assistant UnitedStates Attorneys.We arenon-partisancareer prosecutorsworkinginoffices throughoutthecountry.Our job is to see that justiceis done,in every case,without fear or favor.Withoutparty or politics. I remain committed to these principles, as I am likewise committed to complying with your subpoena to the best of my ability. It is unusual for a prosecutor to testify about a criminal case, and given my role as a prosecutor, there are reasons why my testimony will necessarily be limited. The Department of Justice has indicated it may assert certain privileges related to investigative information and decisions, ongoing matters within the Department, and deliberations within the Department. I intend to respect the invocation of these privileges in appropriate circumstances, but also recognize that, for example, the deliberative process privilege does not apply when testimony sheds light on government misconduct, or when the Government has disclosed deliberative information selectively and misleadingly. The Department has cleared my submission of this written statement. The first thing every AUSA learns is that we have an ethical and legal obligationto treat every defendantequally and fairly.No one is entitledto moreor less because of who they are,who they know,or what they believe.In the United States of America,we do not prosecutepeoplebecauseof their politics.