Secure GNSS-Based Positioning and Timing
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Model-Based System Engineering for Powertrain Systems Optimization Sandra Hamze
Model-based System Engineering for Powertrain Systems Optimization Sandra Hamze To cite this version: Sandra Hamze. Model-based System Engineering for Powertrain Systems Optimization. Automatic Control Engineering. Université Grenoble Alpes, 2019. English. NNT : 2019GREAT055. tel- 02524432 HAL Id: tel-02524432 https://tel.archives-ouvertes.fr/tel-02524432 Submitted on 30 Mar 2020 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. THÈSE pour obtenir le grade de DOCTEUR DE L’UNIVERSITÉ DE GRENOBLE ALPES Spécialité : Automatique-Productique Arrêté ministériel : 7 août 2006 Présentée par Sandra HAMZE Thèse dirigée par Emmanuel WITRANT et codirigée par Delphine BRESCH-PIETRI et Vincent TALON préparée au sein du laboratoire Grenoble Images Parole Signal Automatique (GIPSA-lab) dans l’école doctorale Electronique, Electrotechnique, Automatique, Traitement du Signal (EEATS) en collaboration avec Renault s.a.s Optimisation Multi-objectifs Inter-systèmes des Groupes Motopropulseurs Model-based System Engineering for Powertrain Systems Optimization 2 Thèse soutenue -

Construction of an Active Rectifier for a Transverse-Flux Wave Power Generator
EXAMENSARBETE INOM ELEKTROTEKNIK, AVANCERAD NIVÅ, 30 HP STOCKHOLM, SVERIGE 2017 Construction of an Active Rectifier for a Transverse-Flux Wave Power Generator OLOF BRANDT LUNDQVIST KTH SKOLAN FÖR ELEKTRO- OCH SYSTEMTEKNIK 1 Sammanfattning Vågkraft är en energikälla som skulle kunna göra en avgörande skillnad i om- ställningen mot en hållbar energisektor. Tillväxten för vågkraft har dock inte varit lika snabb som tillväxten för andra förnybara energislag, såsom vindkraft och solkraft. Vissa tekniska hinder kvarstår innan ett stort genombrott för våg- kraft kan bli möjligt. Ett hinder fram tills nu har varit de låga spänningarna och de resulterande höga effektförlusterna i många vågkraftverk. En ny typ av våg- kraftsgenerator, som har tagits fram av Anders Hagnestål vid KTH i Stockholm, avser att lösa dessa problem. I det här examensarbetet behandlas det effekte- lektroniska omvandlingssystemet för Anders Hagneståls generator. Det beskriver planerings- och konstruktionsprocessen för en enfasig AC/DC-omvandlare, som så småningom skall bli en del av det större omvandlingssystemet för generatorn. Ett kontrollsystem för omvandlaren, baserat på hystereskontroll för strömmen, planeras och sätts ihop. Den färdiga enfasomvandlaren visar goda resultat under drift som växelriktare. Dock kvarstår visst konstruktionsarbete och viss kalibre- ring av det digitala kontrollsystemet innan omvandlaren kan användas för sin uppgift i effektomvandlingen hos vågkraftverket. 2 2 Abstract Wave power is an energy source which could make a decisive difference in the transition towards a more sustainable energy sector. The growth of wave power production has however not been as rapid as the growth in other renewable energy fields, such as wind power and solar power. Some technical obstacles remain before a major breakthrough for wave power can be expected. -

The Governance of Galileo
The Governance of Galileo Report 62 January 2017 Amiel Sitruk Serge Plattard Short title: ESPI Report 62 ISSN: 2218-0931 (print), 2076-6688 (online) Published in January 2017 Editor and publisher: European Space Policy Institute, ESPI Schwarzenbergplatz 6 • 1030 Vienna • Austria http://www.espi.or.at Tel. +43 1 7181118-0; Fax -99 Rights reserved – No part of this report may be reproduced or transmitted in any form or for any purpose without permission from ESPI. Citations and extracts to be published by other means are subject to mentioning “Source: ESPI Report 62; January 2017. All rights reserved” and sample transmission to ESPI before publishing. ESPI is not responsible for any losses, injury or damage caused to any person or property (including under contract, by negligence, product liability or otherwise) whether they may be direct or indirect, special, incidental or consequential, resulting from the information contained in this publication. Design: Panthera.cc ESPI Report 62 2 January 2017 The Governance of Galileo Table of Contents Executive Summary 5 1. Introduction 7 1.1 Purposes, Principle and Current State of Global Navigation Satellite Systems (GNSS) 7 1.2 Description of Galileo 7 1.3 A Brief History of Galileo and Its Governance 9 1.4 Current State and Next Steps 10 2. The Challenges of Galileo Governance 12 2.1 Political Challenges 12 2.1.1 Giving to the EU and Its Member States an Effective Instrument of Sovereignty 12 2.1.2 Providing Effective Interaction between the European Stakeholders 12 2.1.3 Dealing with Security Issues Related to Galileo 13 2.1.4 Ensuring a Strong Presence on the International Scene 13 2.2 Economic Challenges 14 2.2.1 Setting up a Cost-Effective Organization 14 2.2.2 Fostering the Development of a Downstream Market Associated with Galileo 14 2.2.3 Fostering Indirect Benefits 15 2.3 Technical Challenges 15 2.3.1 Successfully Exploiting the System 15 2.3.2 Ensuring the Evolution of the System 16 2.3.3 Technically Enabling “GNSS Diplomacy” 16 3. -

[email protected] University of Pittsburgh Web : Pittsburgh, PA 15260 Office : 412.624.8924, Fax : 412.624.8854
PANOS K. CHRYSANTHIS Department of Computer Science E-Mail : [email protected] University of Pittsburgh Web : http://panos.cs.pitt.edu Pittsburgh, PA 15260 Office : 412.624.8924, Fax : 412.624.8854 RESEARCH INTERESTS Management of Data (Big Data, Databases, Web Databases, Data Streams & Sensor networks), Cloud, Distributed & Mobile Computing, Workflow Management, Operating & Real-time Systems EDUCATION Ph.D. in Computer and Information Science, University of Massachusetts, Amherst, August 1991 M.S. in Computer and Information Science, University of Massachusetts, Amherst, May 1986 B.S. in Physics (Computer Science concentration), University of Athens, Greece, December 1982 APPOINTMENTS Professor, Dept. of Computer Science (Joint-Secondary appointment in Electrical Engineering and the Telcomm Program), University of Pittsburgh (Jan. 2004 to present). Adjunct Professor, Dept. of Computer Science, Carnegie-Mellon University (Aug. 2000 to present). Faculty member, Computational Biology PhD Program, University of Pittsburgh and Carnegie-Mellon University (Sept. 2004 to present). Adjunct Professor, Dept. of Computer Science, University of Cyprus, Cyprus (Jan. 2008 to Dec. 2016, Jan. 2018 to present). Visiting Professor, Laboratory of Information, Networking and Communication Sciences (LINCS), Paris, France (Feb. 2019 to Mar. 2019) Visiting Professor, Dept. of Computer Science, University of Cyprus, Cyprus (Aug. 2006 to June 2007, May 2016, June 2018 June 2019). Visiting Professor, Dept. of Computer Science, Carnegie Mellon University, Pittsburgh (Aug. 1999 to Aug. 2000; Dec. 2014 to Aug. 2015) Faculty Member, RODS Laboratory, Center for Biomedical Informatics, University of Pittsburgh (May 2002 to Aug. 2006). Associate Professor, Dept. of Computer Science (Joint-Secondary appointment in Electrical Engineering), University of Pittsburgh (Sept. 1997 to Dec. -

An Overview of the Netware Operating System
An Overview of the NetWare Operating System Drew Major Greg Minshall Kyle Powell Novell, Inc. Abstract The NetWare operating system is designed specifically to provide service to clients over a computer network. This design has resulted in a system that differs in several respects from more general-purpose operating systems. In addition to highlighting the design decisions that have led to these differences, this paper provides an overview of the NetWare operating system, with a detailed description of its kernel and its software-based approach to fault tolerance. 1. Introduction The NetWare operating system (NetWare OS) was originally designed in 1982-83 and has had a number of major changes over the intervening ten years, including converting the system from a Motorola 68000-based system to one based on the Intel 80x86 architecture. The most recent re-write of the NetWare OS, which occurred four years ago, resulted in an “open” system, in the sense of one in which independently developed programs could run. Major enhancements have occurred over the past two years, including the addition of an X.500-like directory system for the identification, location, and authentication of users and services. The philosophy has been to start as with as simple a design as possible and try to make it simpler as we gain experience and understand the problems better. The NetWare OS provides a reasonably complete runtime environment for programs ranging from multiprotocol routers to file servers to database servers to utility programs, and so forth. Because of the design tradeoffs made in the NetWare OS and the constraints those tradeoffs impose on the structure of programs developed to run on top of it, the NetWare OS is not suited to all applications. -

D2.3 Design Guidelines for the Rapid-Api Industrial Design of Multimodal Interactive Expressive Technology
REALTIME ADAPTIVE PROTOTYPING FOR D2.3 DESIGN GUIDELINES FOR THE RAPID-API INDUSTRIAL DESIGN OF MULTIMODAL INTERACTIVE EXPRESSIVE TECHNOLOGY D2.3 DESIGN GUIDELINES FOR THE RAPID-API Grant Agreement nr 644862 Project title Realtime Adaptive Prototyping for Industrial Design of Multimodal Interactive eXpressive technology Project acronym RAPID-MIX Start date of project (dur.) Feb 1st, 2015 (3 years) Document reference RAPIDMIX-WD-WP2-UPF-D2.3.docx Report availability PU - Public Document due Date June 30th, 2016 Actual date of delivery July 31st, 2016 Leader UPF Reply to Sebastian Mealla C. ([email protected]) Additional main contributors Panos Papiots (UPF) (author’s name / partner acr.) Carles F. Julia (UPF) Frederic Bevilacqua (IRCAM) Joseph Larralde (IRCAM) Norbert Schnell (IRCAM) Mick Grierson (GS) Rebecca Fiebrink (GS) Francisco Bernardo (GS) Michael Zbyszyński (GS) xavier boissarie (ORBE) Hugo Silva (PLUX) Document status Final version (reviewed by GS) This project has received funding from the European Union’s Horizon 2020 research and innovation programme under grant agreement N° 644862 D2.3 DESIGN GUIDELINES FOR THE RAPID-API Page 1 of 32- MIX_WD_WP1_DeliverableTemplate_20120314_MTG-UPF Page 1 of 32 EXECUTIVE SUMMARY This deliverable updates the user-centred design specifications defined in D2.2 to include guidelines for the RAPID-API development, according to the requirements of research and SME partners, and end-users beyond the consortium. D2.3 DESIGN GUIDELINES FOR THE RAPID-API Page 2 of 32 TABLE OF CONTENTS 1 INTRODUCTION -
Acorn User Welcomes Submissions Irom Readers
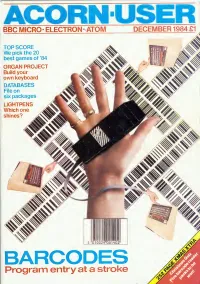
ACORN BBC MICRO- ELECTRON- ATOM DECEMBER 1984 £1 TOP SCORE We pick the 20 best games of '84 ORGAN PROJECT Build your own keyboard DATABASES File on six packages LIGHTPENS Which one shines? Program entry at a stroke ' MUSIC MICRO PLEASE!! Jj V L S ECHO I is a high quality 3 octave keyboard of 37 full sized keys operating electroni- cally through gold plated contacts. The keyboard which is directly connected to the user port of the computer does not require an independent power supply unit. The ECHOSOFT Programme "Organ Master" written for either the BBC Model B' or the Commodore 64 supplied with the keyboard allows these computers to be used as real time synth- esizers with full control of the sound envelopes. The pitch and duration of the sound envelope can be changed whilst playing, and the programme allows the user to create and allocate his own sounds to four pre-defined keys. Additional programmes in the ECHOSOFT Series are in the course of preparation and will be released shortly. Other products in the range available from your LVL Dealer are our: ECHOKIT (£4.95)" External Speaker Adaptor Kit, allows your Commodore or BBC Micro- computer to have an external sound output socket allowing the ECHOSOUND Speaker amplifier to be connected. (£49.95)' - ECHOSOUND A high quality speaker amplifier with a 6 dual cone speaker and a full 6 watt output will fill your room with sound. The sound frequency control allows the tone of the sound output to be changed. Both of the above have been specifically designed to operate with the ECHO Series keyboard. -

Acorn ABC 210/Cambridge Workstation
ACORN COMPUTERS LTD. ACW 443 SERVICE MANUAL 0420,001 Issue 1 January 1987 ACW SERVICE MANUAL Title: ACW SERVICE MANUAL Reference: 0420,001 Issue: 1 Replaces: 0.56 Applicability: Product Support Distribution: Authorised Service Agents Status: for publication Author: C.Watters, J.Wilkins and Others Date: 7 January 1987 Published by: Acorn Computers Ltd, Fulbourn Road, Cherry Hinton, Cambridge, CB1 4JN, England Within this publication the term 'BBC' is used as an abbreviation for 'British Broadcasting Corporation'. Copyright ACORN Computers Limited 1985 Neither the whole or any part of the information contained in, or the product described in, this manual may be adapted or reproduced in any material form except with the prior written approval of ACORN Computers Limited ( ACORN Computers). The product described in this manual and products for use with it, are subject to continuous development and improvement. All information of a technical nature and particulars of the product and its use (including the information and particulars in this manual) are given by ACORN Computers in good faith. However, it is acknowledged that there may be errors or omissions in this manual. A list of details of any amendments or revisions to this manual can be obtained upon request from ACORN Computers Technical Enquiries. ACORN Computers welcome comments and suggestions relating to the product and this manual. All correspondence should be addressed to:- Technical Enquiries ACORN Computers Limited Newmarket Road Cambridge CB5 8PD All maintenance and service on the product must be carried out by ACORN Computers' authorised service agents. ACORN Computers can accept no liability whatsoever for any loss or damage caused by service or maintenance by unauthorised personnel. -

App91a Acorn Scientific Products
storage as standard. Further external hard and PASCAL. the languages, together GLIM package developed by the Royal disc storage is easily added. with extensions and library support have Statistical Society of London. Communications been optimised to ease greatly the porting SCIENTIFIC of programs and modules to and from The electonic engineer is well supported For local communications the ECONET mainframes. A 32000 assembler is by the Acorn Scientific range. Programs PRODUCTS Local Area Network provides included and an extension to C allows the available include SPICE, a general communications to other workstations purpose circuit simulation program and and BBC type micros and an RS423 calling of machine code inserts. The PANOS full screen editor is a QUICKCHIP, a comprehensive CAD The Acorn Scientific range of products interface provides communications to a comprehensive package ideally suited to package for semi-custom gate arrays. has been designed to provide engineers wide variety of devices including modems and scientists with a real alternative to the program development in these languages. Quickchip is supported by a high speed and mainframes. Communication with direct write electron beam fabrication mainframe and supermini computers that mainframes is supported by terminal have been their only means of access to BASIC continues to be a popular facility. General purpose engineering, in emulation and file transfer software language for a variety of tasks. The particular control engineering, is catered high levels of computation. Acorn including host code for various Scientific products can break down the version provided is Acorn's famous BBC for by the Cambridge Linear Analysis anc mainframes. -

The Master Series
N 1981 a good-looking newcomer This means that an enormous range of arrived on the microcomputer scene. add-ons and peripheral devices, plus a Its impressive pedigree and range of vast software library with many thousands BRITISH I BROADCASTING connections aroused interest. Its of titles, are available for use with the CORPORATION performance caused a sensation. Master Series — now. MASTER SERIES That newcomer was the British The Master 512, through its DOS+ MICROCOMPUTER Broadcasting Corporation Microcomputer, operating system, can be compatible with one of the great success stories of the software written for MS-DOS, CP/M-86 computer industry. A key feature of the or GEM, the most popular operating BBC's Computer Literacy Project, it was systems for the business environment. chosen for seven out of every ten micros bought for UK schools and five out of ten The Reliability of Experience used for medical applications. In homes The Master Series incorporates the and factories, offices and laboratories, the experience gained by Acorn Computers BBC Micro's user friendliness and ability on more than 700,000 microcomputers to solve problems has won it countless over five years of operation. Acorn's friends and admirers. design skills and production expertise Now, the concepts that were the key ensure that the Master Series maintains to that success have been incorporated in the BBC Micro's tradition of high a new range of advanced microcomputers them to share data and resources, the Master Scientific. engineering standards and its reputation — the BBC Master Series. highly regarded BBC BASIC The Master Scientific brings the power for reliability. -

Labels and Event Processes in the Asbestos Operating System
Labels and Event Processes in the Asbestos Operating System Petros Efstathopoulos∗ Maxwell Krohn† Steve VanDeBogart∗ Cliff Frey† David Ziegler† Eddie Kohler∗ David Mazieres` ‡ Frans Kaashoek† Robert Morris† ∗UCLA †MIT ‡Stanford/NYU http://asbestos.cs.ucla.edu/ ABSTRACT purposes [20]. Most servers instead revert to the most insecure de- sign, monolithic code running with many privileges. It should come Asbestos, a new prototype operating system, provides novel la- as no surprise that high-impact breaches continue. beling and isolation mechanisms that help contain the effects New operating system primitives are needed [21], and the best of exploitable software flaws. Applications can express a wide place to explore candidates is the unconstrained context of a new range of policies with Asbestos’s kernel-enforced label mechanism, OS. Hence the Asbestos operating system, which can enforce strict including controls on inter-process communication and system- application-defined security policies even on efficient, unprivileged wide information flow. A new event process abstraction provides servers. lightweight, isolated contexts within a single process, allowing the same process to act on behalf of multiple users while preventing Asbestos’s contributions are twofold. First, all access control it from leaking any single user’s data to any other user. A Web checks use Asbestos labels, a primitive that combines advantages server that uses Asbestos labels to isolate user data requires about of discretionary and nondiscretionary access control. Labels deter- 1.5 memory pages per user, demonstrating that additional security mine which services a process can invoke and with which other can come at an acceptable cost. processes it can interact. -

Prototype Eclipse OMR Port Performance Evaluation on Aarch64
Prototype Eclipse OMR Port Performance Evaluation on AArch64 by Jean-Philippe Legault Bachelor with Honors of Computer Science, UNB, 2018 A THESIS SUBMITTED IN PARTIAL FULFILLMENT OF THE REQUIREMENTS FOR THE DEGREE OF Master of Computer Science In the Graduate Academic Unit of Computer Science Supervisor(s): Kenneth B. Kent, Ph.D., Computer Science Examining Board: Gerhard Dueck, Ph.D., Computer Science, Chair Panos Patros, Ph.D., Computer Science Julian Cardenas-Barrera, Ph.D., ECE This thesis is accepted by the Dean of Graduate Studies THE UNIVERSITY OF NEW BRUNSWICK November, 2020 ©Jean-Philippe Legault, 2021 Abstract This thesis discusses the steps taken to build the prototype Eclipse OMR port to the AArch64 architecture. The AArch64 OMR port is evaluated using Eclipse OpenJ9 against an AMD64 counter-part (similar cache size and clock speed); The results are used to build a baseline for future research and provide an evaluation framework upon which further enhancements to the platform can be compared. This thesis also reviews the AArch64 hardware landscape and its suitability for a development platform. AArch64 is reviewed in terms of software availability and ease of use. Developing for embedded devices adds a layer of difficulty to software development that cannot be ignored and this thesis reviews the usability of modern development tools on the AArch64 ISA. This thesis offers an experience review on the AArch64 ISA with modern software as well as the viability of a high-performance runtime on AArch64. ii Acknowledgments I would like to thank Aaron Graham for guidance and help throughout the project. Without his support, both as a best friend and a coworker, this thesis could never have seen daylight.