Cryptanalysis and Design of Symmetric Primitives
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Lecture Note 8 ATTACKS on CRYPTOSYSTEMS I Sourav Mukhopadhyay
Lecture Note 8 ATTACKS ON CRYPTOSYSTEMS I Sourav Mukhopadhyay Cryptography and Network Security - MA61027 Attacks on Cryptosystems • Up to this point, we have mainly seen how ciphers are implemented. • We have seen how symmetric ciphers such as DES and AES use the idea of substitution and permutation to provide security and also how asymmetric systems such as RSA and Diffie Hellman use other methods. • What we haven’t really looked at are attacks on cryptographic systems. Cryptography and Network Security - MA61027 (Sourav Mukhopadhyay, IIT-KGP, 2010) 1 • An understanding of certain attacks will help you to understand the reasons behind the structure of certain algorithms (such as Rijndael) as they are designed to thwart known attacks. • Although we are not going to exhaust all possible avenues of attack, we will get an idea of how cryptanalysts go about attacking ciphers. Cryptography and Network Security - MA61027 (Sourav Mukhopadhyay, IIT-KGP, 2010) 2 • This section is really split up into two classes of attack: Cryptanalytic attacks and Implementation attacks. • The former tries to attack mathematical weaknesses in the algorithms whereas the latter tries to attack the specific implementation of the cipher (such as a smartcard system). • The following attacks can refer to either of the two classes (all forms of attack assume the attacker knows the encryption algorithm): Cryptography and Network Security - MA61027 (Sourav Mukhopadhyay, IIT-KGP, 2010) 3 – Ciphertext-only attack: In this attack the attacker knows only the ciphertext to be decoded. The attacker will try to find the key or decrypt one or more pieces of ciphertext (only relatively weak algorithms fail to withstand a ciphertext-only attack). -

On Quantum Slide Attacks Xavier Bonnetain, María Naya-Plasencia, André Schrottenloher
On Quantum Slide Attacks Xavier Bonnetain, María Naya-Plasencia, André Schrottenloher To cite this version: Xavier Bonnetain, María Naya-Plasencia, André Schrottenloher. On Quantum Slide Attacks. 2018. hal-01946399 HAL Id: hal-01946399 https://hal.inria.fr/hal-01946399 Preprint submitted on 6 Dec 2018 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. On Quantum Slide Attacks Xavier Bonnetain1,2, María Naya-Plasencia2 and André Schrottenloher2 1 Sorbonne Université, Collège Doctoral, F-75005 Paris, France 2 Inria de Paris, France Abstract. At Crypto 2016, Kaplan et al. proposed the first quantum exponential acceleration of a classical symmetric cryptanalysis technique: they showed that, in the superposition query model, Simon’s algorithm could be applied to accelerate the slide attack on the alternate-key cipher. This allows to recover an n-bit key with O(n) quantum time and queries. In this paper we propose many other types of quantum slide attacks, inspired by classical techniques including sliding with a twist, complementation slide and mirror slidex. These slide attacks on Feistel networks reach up to two round self-similarity with modular additions inside branch or key-addition operations. -

Identifying Open Research Problems in Cryptography by Surveying Cryptographic Functions and Operations 1
International Journal of Grid and Distributed Computing Vol. 10, No. 11 (2017), pp.79-98 http://dx.doi.org/10.14257/ijgdc.2017.10.11.08 Identifying Open Research Problems in Cryptography by Surveying Cryptographic Functions and Operations 1 Rahul Saha1, G. Geetha2, Gulshan Kumar3 and Hye-Jim Kim4 1,3School of Computer Science and Engineering, Lovely Professional University, Punjab, India 2Division of Research and Development, Lovely Professional University, Punjab, India 4Business Administration Research Institute, Sungshin W. University, 2 Bomun-ro 34da gil, Seongbuk-gu, Seoul, Republic of Korea Abstract Cryptography has always been a core component of security domain. Different security services such as confidentiality, integrity, availability, authentication, non-repudiation and access control, are provided by a number of cryptographic algorithms including block ciphers, stream ciphers and hash functions. Though the algorithms are public and cryptographic strength depends on the usage of the keys, the ciphertext analysis using different functions and operations used in the algorithms can lead to the path of revealing a key completely or partially. It is hard to find any survey till date which identifies different operations and functions used in cryptography. In this paper, we have categorized our survey of cryptographic functions and operations in the algorithms in three categories: block ciphers, stream ciphers and cryptanalysis attacks which are executable in different parts of the algorithms. This survey will help the budding researchers in the society of crypto for identifying different operations and functions in cryptographic algorithms. Keywords: cryptography; block; stream; cipher; plaintext; ciphertext; functions; research problems 1. Introduction Cryptography [1] in the previous time was analogous to encryption where the main task was to convert the readable message to an unreadable format. -

Authentication Key Recovery on Galois/Counter Mode (GCM)
Authentication Key Recovery on Galois/Counter Mode (GCM) John Mattsson and Magnus Westerlund Ericsson Research, Stockholm, Sweden {firstname.lastname}@ericsson.com Abstract. GCM is used in a vast amount of security protocols and is quickly becoming the de facto mode of operation for block ciphers due to its exceptional performance. In this paper we analyze the NIST stan- dardized version (SP 800-38D) of GCM, and in particular the use of short tag lengths. We show that feedback of successful or unsuccessful forgery attempts is almost always possible, contradicting the NIST assumptions for short tags. We also provide a complexity estimation of Ferguson’s authentication key recovery method on short tags, and suggest several novel improvements to Fergusons’s attacks that significantly reduce the security level for short tags. We show that for many truncated tag sizes; the security levels are far below, not only the current NIST requirement of 112-bit security, but also the old NIST requirement of 80-bit security. We therefore strongly recommend NIST to revise SP 800-38D. Keywords. Secret-key Cryptography, Message Authentication Codes, Block Ciphers, Cryptanalysis, Galois/Counter Mode, GCM, Authentica- tion Key Recovery, AES-GCM, Suite B, IPsec, ESP, SRTP, Re-forgery. 1 Introduction Galois/Counter Mode (GCM) [1] is quickly becoming the de facto mode of op- eration for block ciphers. GCM is included in the NSA Suite B set of cryp- tographic algorithms [2], and AES-GCM is the benchmark algorithm for the AEAD competition CAESAR [3]. Together with Galois Message Authentication Code (GMAC), GCM is used in a vast amount of security protocols: – Many protocols such as IPsec [4], TLS [5], SSH [6], JOSE [7], 802.1AE (MAC- sec) [8], 802.11ad (WiGig) [9], 802.11ac (Wi-Fi) [10], P1619.1 (data storage) [11], Fibre Channel [12], and SRTP [13, 14]1 only allow 128-bit tags. -

Impossible Differential Cryptanalysis of Reduced Round Hight
1 IMPOSSIBLE DIFFERENTIAL CRYPTANALYSIS OF REDUCED ROUND HIGHT A THESIS SUBMITTED TO THE GRADUATE SCHOOL OF APPLIED MATHEMATICS OF MIDDLE EAST TECHNICAL UNIVERSITY BY CIHANG˙ IR˙ TEZCAN IN PARTIAL FULFILLMENT OF THE REQUIREMENTS FOR THE DEGREE OF MASTER OF SCIENCE IN CRYPTOGRAPHY JUNE 2009 Approval of the thesis: IMPOSSIBLE DIFFERENTIAL CRYPTANALYSIS OF REDUCED ROUND HIGHT submitted by CIHANG˙ IR˙ TEZCAN in partial fulfillment of the requirements for the degree of Master of Science in Department of Cryptography, Middle East Technical University by, Prof. Dr. Ersan Akyıldız Director, Graduate School of Applied Mathematics Prof. Dr. Ferruh Ozbudak¨ Head of Department, Cryptography Assoc. Prof. Dr. Ali Doganaksoy˘ Supervisor, Mathematics Examining Committee Members: Prof. Dr. Ersan Akyıldız METU, Institute of Applied Mathematics Assoc. Prof. Ali Doganaksoy˘ METU, Department of Mathematics Dr. Muhiddin Uguz˘ METU, Department of Mathematics Dr. Meltem Sonmez¨ Turan Dr. Nurdan Saran C¸ankaya University, Department of Computer Engineering Date: I hereby declare that all information in this document has been obtained and presented in accordance with academic rules and ethical conduct. I also declare that, as required by these rules and conduct, I have fully cited and referenced all material and results that are not original to this work. Name, Last Name: CIHANG˙ IR˙ TEZCAN Signature : iii ABSTRACT IMPOSSIBLE DIFFERENTIAL CRYPTANALYSIS OF REDUCED ROUND HIGHT Tezcan, Cihangir M.Sc., Department of Cryptography Supervisor : Assoc. Prof. Dr. Ali Doganaksoy˘ June 2009, 49 pages Design and analysis of lightweight block ciphers have become more popular due to the fact that the future use of block ciphers in ubiquitous devices is generally assumed to be extensive. -

Security Enhancement in Cloud Storage Using ARIA and Elgamal Algorithms
International Journal of Computer Applications (0975 – 8887) Volume 171 – No. 9, August 2017 Security Enhancement in Cloud Storage using ARIA and Elgamal Algorithms Navdeep Kaur Heena Wadhwa Research Scholar Assistant Professor Department of IT Department of CSE CEC Landran, Mohali, Punjab CEC Landran, Mohali, Punjab ABSTRACT Cloud Computing examination [3]. The cloud does appear Cloud Computing is not an improvement, excluding an resolve some ancient issues with the still growing costs of income towards constructs information technology services apply, preserve, & supporting an IT communications that is that utilize superior computational authority & better storage rarely utilized everywhere near its ability in the single-owner space utilization. The major centre of Cloud Computing starts atmosphere. There is a chance to amplify competence & when the supplier vision as irrelevant hardware associated to reduce expenses in the IT section of the commerce & sustain down-time on some appliance in the system. It is not a decision-makers are commencement to pay concentration. modification in the user viewpoint. As well, the user software Vendors who can supply a protected, high-availability, picture should be simply convertible as of one confuse to a scalable communications to the loads may be poised to be new. Though cloud computing is embattled to offer better successful in receiving association to accept their cloud operation of possessions using virtualization method and to services[20]. receive up a great deal of the job load from the customer and Due to the current development in computer network provides safety also. Cloud Computing is a rising technology technology, giving out of digital multimedia pleased through with joint property and lower cost that relies on pay per use the internet is massive. -

ARIA-CTR Encryption for Low-End Embedded Processors
sensors Article ACE: ARIA-CTR Encryption for Low-End Embedded Processors Hwajeong Seo * , Hyeokdong Kwon, Hyunji Kim and Jaehoon Park Division of IT Convergence Engineering, Hansung University, Seoul, 02876, Korea; [email protected] (H.K.); [email protected] (H.K.); [email protected] (J.P.) * Correspondence: [email protected]; Tel.:+82-2-760-8033 Received: 21 June 2020; Accepted: 4 July 2020; Published: 6 July 2020 Abstract: In this paper, we present the first optimized implementation of ARIA block cipher on low-end 8-bit Alf and Vegard’s RISC processor (AVR) microcontrollers. To achieve high-speed implementation, primitive operations, including rotation operation, a substitute layer, and a diffusion layer, are carefully optimized for the target low-end embedded processor. The proposed ARIA implementation supports the electronic codebook (ECB) and the counter (CTR) modes of operation. In particular, the CTR mode of operation is further optimized with the pre-computed table of two add-round-key, one substitute layer, and one diffusion layer operations. Finally, the proposed ARIA-CTR implementations on 8-bit AVR microcontrollers achieved 187.1, 216.8, and 246.6 clock cycles per byte for 128-bit, 192-bit, and 256-bit security levels, respectively. Compared with previous reference implementations, the execution timing is improved by 69.8%, 69.6%, and 69.5% for 128-bit, 192-bit, and 256-bit security levels, respectively. Keywords: ARIA; electronic codebook mode of operation; counter mode of operation; software implementation; embedded processors 1. Introduction Data encryption is a fundamental technology for secure network communication in the Internet of Things (IoT). -

Cryptanalysis of Selected Block Ciphers
Downloaded from orbit.dtu.dk on: Sep 24, 2021 Cryptanalysis of Selected Block Ciphers Alkhzaimi, Hoda A. Publication date: 2016 Document Version Publisher's PDF, also known as Version of record Link back to DTU Orbit Citation (APA): Alkhzaimi, H. A. (2016). Cryptanalysis of Selected Block Ciphers. Technical University of Denmark. DTU Compute PHD-2015 No. 360 General rights Copyright and moral rights for the publications made accessible in the public portal are retained by the authors and/or other copyright owners and it is a condition of accessing publications that users recognise and abide by the legal requirements associated with these rights. Users may download and print one copy of any publication from the public portal for the purpose of private study or research. You may not further distribute the material or use it for any profit-making activity or commercial gain You may freely distribute the URL identifying the publication in the public portal If you believe that this document breaches copyright please contact us providing details, and we will remove access to the work immediately and investigate your claim. Cryptanalysis of Selected Block Ciphers Dissertation Submitted in Partial Fulfillment of the Requirements for the Degree of Doctor of Philosophy at the Department of Mathematics and Computer Science-COMPUTE in The Technical University of Denmark by Hoda A.Alkhzaimi December 2014 To my Sanctuary in life Bladi, Baba Zayed and My family with love Title of Thesis Cryptanalysis of Selected Block Ciphers PhD Project Supervisor Professor Lars R. Knudsen(DTU Compute, Denmark) PhD Student Hoda A.Alkhzaimi Assessment Committee Associate Professor Christian Rechberger (DTU Compute, Denmark) Professor Thomas Johansson (Lund University, Sweden) Professor Bart Preneel (Katholieke Universiteit Leuven, Belgium) Abstract The focus of this dissertation is to present cryptanalytic results on selected block ci- phers. -
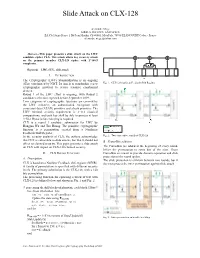
Slide Attack on CLX-128
Slide Attack on CLX-128 Alexandre Mège AIRBUS DEFENCE AND SPACE ZA Clef Saint-Pierre, 1 Bd Jean Moulin, CS 40001, MetaPole, 78996 ELANCOURT Cedex - France [email protected] Abstract—This paper presents a slide attack on the LWC candidate cipher CLX. This attack allows key recovery attack on the primary member CLX-128 cipher with 2^108.5 complexity. Keywords—LWC, CLX , slide,attack I. INTRODUCTION The Cryptography (LWC) Standardization is an ongoing effort coordinated by NIST. Its aim is to standardize a new Fig. 1. CLX-128 nonlinear Feedback Shift Register cryptographic protocol to secure resource constrained devices. Round 1 of the LWC effort is ongoing, with Round 2 candidates selection expected before September 2019. Two categories of cryptographic functions are covered by the LWC initiative, an authenticated encryption with associated data (AEAD) primitive and a hash primitive. The LWC minimal security requirement is 2^112 classical computations, and each key shall be able to process at least 2^50-1 Bytes before rekeying is required. CLX is a round 1 candidate submission for LWC by Hongjun Wu and Tao Huang. The primitive cryptographic function is a permutation created from a Nonlinear Feedback Shift Register. In the security analysis of CLX, the authors acknowledge Fig. 2. Two consecutive rounds of CLX-128 that CLX is vulnerable to slide attacks, but that it should not B. FrameBits addition affect its claimed security. This paper presents a slide attack on CLX with impact on CLX-128 claimed security. The FrameBits are added at the beginning of every round, before the permutation to some bits of the state. -

ICEBERG : an Involutional Cipher Efficient for Block Encryption in Reconfigurable Hardware
1 ICEBERG : an Involutional Cipher Efficient for Block Encryption in Reconfigurable Hardware. Francois-Xavier Standaert, Gilles Piret, Gael Rouvroy, Jean-Jacques Quisquater, Jean-Didier Legat UCL Crypto Group Laboratoire de Microelectronique Universite Catholique de Louvain Place du Levant, 3, B-1348 Louvain-La-Neuve, Belgium standaert,piret,rouvroy,quisquater,[email protected] Abstract. We present a fast involutional block cipher optimized for re- configurable hardware implementations. ICEBERG uses 64-bit text blocks and 128-bit keys. All components are involutional and allow very effi- cient combinations of encryption/decryption. Hardware implementations of ICEBERG allow to change the key at every clock cycle without any per- formance loss and its round keys are derived “on-the-fly” in encryption and decryption modes (no storage of round keys is needed). The result- ing design offers better hardware efficiency than other recent 128-key-bit block ciphers. Resistance against side-channel cryptanalysis was also con- sidered as a design criteria for ICEBERG. Keywords: block cipher design, efficient implementations, reconfigurable hardware, side-channel resistance. 1 Introduction In October 2000, NIST (National Institute of Standards and Technology) se- lected Rijndael as the new Advanced Encryption Standard. The selection pro- cess included performance evaluation on both software and hardware platforms. However, as implementation versatility was a criteria for the selection of the AES, it appeared that Rijndael is not optimal for reconfigurable hardware im- plementations. Its highly expensive substitution boxes are a typical bottleneck but the combination of encryption and decryption in hardware is probably as critical. In general, observing the AES candidates [1, 2], one may assess that the cri- teria selected for their evaluation led to highly conservative designs although the context of certain cryptanalysis may be considered as very unlikely (e.g. -
Encryption Block Cipher
10/29/2007 Encryption Encryption Block Cipher Dr.Talal Alkharobi 2 Block Cipher A symmetric key cipher which operates on fixed-length groups of bits, termed blocks, with an unvarying transformation. When encrypting, a block cipher take n-bit block of plaintext as input, and output a corresponding n-bit block of ciphertext. The exact transformation is controlled using a secret key. Decryption is similar: the decryption algorithm takes n-bit block of ciphertext together with the secret key, and yields the original n-bit block of plaintext. Mode of operation is used to encrypt messages longer than the block size. 1 Dr.Talal Alkharobi 10/29/2007 Encryption 3 Encryption 4 Decryption 2 Dr.Talal Alkharobi 10/29/2007 Encryption 5 Block Cipher Consists of two algorithms, encryption, E, and decryption, D. Both require two inputs: n-bits block of data and key of size k bits, The output is an n-bit block. Decryption is the inverse function of encryption: D(E(B,K),K) = B For each key K, E is a permutation over the set of input blocks. n Each key K selects one permutation from the possible set of 2 !. 6 Block Cipher The block size, n, is typically 64 or 128 bits, although some ciphers have a variable block size. 64 bits was the most common length until the mid-1990s, when new designs began to switch to 128-bit. Padding scheme is used to allow plaintexts of arbitrary lengths to be encrypted. Typical key sizes (k) include 40, 56, 64, 80, 128, 192 and 256 bits. -
Cryptanalysis of Block Ciphers
Cryptanalysis of Block Ciphers Jiqiang Lu Technical Report RHUL–MA–2008–19 30 July 2008 Royal Holloway University of London Department of Mathematics Royal Holloway, University of London Egham, Surrey TW20 0EX, England http://www.rhul.ac.uk/mathematics/techreports CRYPTANALYSIS OF BLOCK CIPHERS JIQIANG LU Thesis submitted to the University of London for the degree of Doctor of Philosophy Information Security Group Department of Mathematics Royal Holloway, University of London 2008 Declaration These doctoral studies were conducted under the supervision of Prof. Chris Mitchell. The work presented in this thesis is the result of original research carried out by myself, in collaboration with others, whilst enrolled in the Information Security Group of Royal Holloway, University of London as a candidate for the degree of Doctor of Philosophy. This work has not been submitted for any other degree or award in any other university or educational establishment. Jiqiang Lu July 2008 2 Acknowledgements First of all, I thank my supervisor Prof. Chris Mitchell for suggesting block cipher cryptanalysis as my research topic when I began my Ph.D. studies in September 2005. I had never done research in this challenging ¯eld before, but I soon found it to be really interesting. Every time I ¯nished a manuscript, Chris would give me detailed comments on it, both editorial and technical, which not only bene¯tted my research, but also improved my written English. Chris' comments are fantastic, and it is straightforward to follow them to make revisions. I thank my advisor Dr. Alex Dent for his constructive suggestions, although we work in very di®erent ¯elds.