Lecture Note 8 ATTACKS on CRYPTOSYSTEMS I Sourav Mukhopadhyay
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Improved Rectangle Attacks on SKINNY and CRAFT
Improved Rectangle Attacks on SKINNY and CRAFT Hosein Hadipour1, Nasour Bagheri2 and Ling Song3( ) 1 Department of Mathematics and Computer Science, University of Tehran, Tehran, Iran, [email protected] 2 Electrical Engineering Department, Shahid Rajaee Teacher Training University, Tehran, Iran, [email protected] 3 Jinan University, Guangzhou, China [email protected] Abstract. The boomerang and rectangle attacks are adaptions of differential crypt- analysis that regard the target cipher E as a composition of two sub-ciphers, i.e., 2 2 E = E1 ◦ E0, to construct a distinguisher for E with probability p q by concatenat- ing two short differential trails for E0 and E1 with probability p and q respectively. According to the previous research, the dependency between these two differential characteristics has a great impact on the probability of boomerang and rectangle distinguishers. Dunkelman et al. proposed the sandwich attack to formalise such dependency that regards E as three parts, i.e., E = E1 ◦ Em ◦ E0, where Em contains the dependency between two differential trails, satisfying some differential propagation with probability r. Accordingly, the entire probability is p2q2r. Recently, Song et al. have proposed a general framework to identify the actual boundaries of Em and systematically evaluate the probability of Em with any number of rounds, and applied their method to accurately evaluate the probabilities of the best SKINNY’s boomerang distinguishers. In this paper, using a more advanced method to search for boomerang distinguishers, we show that the best previous boomerang distinguishers for SKINNY can be significantly improved in terms of probability and number of rounds. -

Hash Functions and the (Amplified) Boomerang Attack
Hash Functions and the (Amplified) Boomerang Attack Antoine Joux1,3 and Thomas Peyrin2,3 1 DGA 2 France T´el´ecomR&D [email protected] 3 Universit´ede Versailles Saint-Quentin-en-Yvelines [email protected] Abstract. Since Crypto 2004, hash functions have been the target of many at- tacks which showed that several well-known functions such as SHA-0 or MD5 can no longer be considered secure collision free hash functions. These attacks use classical cryptographic techniques from block cipher analysis such as differential cryptanal- ysis together with some specific methods. Among those, we can cite the neutral bits of Biham and Chen or the message modification techniques of Wang et al. In this paper, we show that another tool of block cipher analysis, the boomerang attack, can also be used in this context. In particular, we show that using this boomerang attack as a neutral bits tool, it becomes possible to lower the complexity of the attacks on SHA-1. Key words: hash functions, boomerang attack, SHA-1. 1 Introduction The most famous design principle for dedicated hash functions is indisputably the MD-SHA family, firstly introduced by R. Rivest with MD4 [16] in 1990 and its improved version MD5 [15] in 1991. Two years after, the NIST publishes [12] a very similar hash function, SHA-0, that will be patched [13] in 1995 to give birth to SHA-1. This family is still very active, as NIST recently proposed [14] a 256-bit new version SHA-256 in order to anticipate the potential cryptanalysis results and also to increase its security with regard to the fast growth of the computation power. -

Boomerang Analysis Method Based on Block Cipher
International Journal of Security and Its Application Vol.11, No.1 (2017), pp.165-178 http://dx.doi.org/10.14257/ijsia.2017.11.1.14 Boomerang Analysis Method Based on Block Cipher Fan Aiwan and Yang Zhaofeng Computer School, Pingdingshan University, Pingdingshan, 467002 Henan province, China { Fan Aiwan} [email protected] Abstract This paper fused together the related key analysis and differential analysis and did multiple rounds of attack analysis for the DES block cipher. On the basis of deep analysis of Boomerang algorithm principle, combined with the characteristics of the key arrangement of the DES block cipher, the 8 round DES attack experiment and the 9 round DES attack experiment were designed based on the Boomerang algorithm. The experimental results show that, after the design of this paper, the value of calculation complexity of DES block cipher is only 240 and the analysis performance is greatly improved by the method of Boomerang attack. Keywords: block cipher, DES, Boomerang, Computational complexity 1. Introduction With the advent of the information society, especially the extensive application of the Internet to break the traditional limitations of time and space, which brings great convenience to people. However, at the same time, a large amount of sensitive information is transmitted through the channel or computer network, especially the rapid development of e-commerce and e-government, more and more personal information such as bank accounts require strict confidentiality, how to guarantee the security of information is particularly important [1-2]. The essence of information security is to protect the information system or the information resources in the information network from various types of threats, interference and destruction, that is, to ensure the security of information [3]. -

Report on the AES Candidates
Rep ort on the AES Candidates 1 2 1 3 Olivier Baudron , Henri Gilb ert , Louis Granb oulan , Helena Handschuh , 4 1 5 1 Antoine Joux , Phong Nguyen ,Fabrice Noilhan ,David Pointcheval , 1 1 1 1 Thomas Pornin , Guillaume Poupard , Jacques Stern , and Serge Vaudenay 1 Ecole Normale Sup erieure { CNRS 2 France Telecom 3 Gemplus { ENST 4 SCSSI 5 Universit e d'Orsay { LRI Contact e-mail: [email protected] Abstract This do cument rep orts the activities of the AES working group organized at the Ecole Normale Sup erieure. Several candidates are evaluated. In particular we outline some weaknesses in the designs of some candidates. We mainly discuss selection criteria b etween the can- didates, and make case-by-case comments. We nally recommend the selection of Mars, RC6, Serp ent, ... and DFC. As the rep ort is b eing nalized, we also added some new preliminary cryptanalysis on RC6 and Crypton in the App endix which are not considered in the main b o dy of the rep ort. Designing the encryption standard of the rst twentyyears of the twenty rst century is a challenging task: we need to predict p ossible future technologies, and wehavetotake unknown future attacks in account. Following the AES pro cess initiated by NIST, we organized an op en working group at the Ecole Normale Sup erieure. This group met two hours a week to review the AES candidates. The present do cument rep orts its results. Another task of this group was to up date the DFC candidate submitted by CNRS [16, 17] and to answer questions which had b een omitted in previous 1 rep orts on DFC. -

On Quantum Slide Attacks Xavier Bonnetain, María Naya-Plasencia, André Schrottenloher
On Quantum Slide Attacks Xavier Bonnetain, María Naya-Plasencia, André Schrottenloher To cite this version: Xavier Bonnetain, María Naya-Plasencia, André Schrottenloher. On Quantum Slide Attacks. 2018. hal-01946399 HAL Id: hal-01946399 https://hal.inria.fr/hal-01946399 Preprint submitted on 6 Dec 2018 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. On Quantum Slide Attacks Xavier Bonnetain1,2, María Naya-Plasencia2 and André Schrottenloher2 1 Sorbonne Université, Collège Doctoral, F-75005 Paris, France 2 Inria de Paris, France Abstract. At Crypto 2016, Kaplan et al. proposed the first quantum exponential acceleration of a classical symmetric cryptanalysis technique: they showed that, in the superposition query model, Simon’s algorithm could be applied to accelerate the slide attack on the alternate-key cipher. This allows to recover an n-bit key with O(n) quantum time and queries. In this paper we propose many other types of quantum slide attacks, inspired by classical techniques including sliding with a twist, complementation slide and mirror slidex. These slide attacks on Feistel networks reach up to two round self-similarity with modular additions inside branch or key-addition operations. -

Identifying Open Research Problems in Cryptography by Surveying Cryptographic Functions and Operations 1
International Journal of Grid and Distributed Computing Vol. 10, No. 11 (2017), pp.79-98 http://dx.doi.org/10.14257/ijgdc.2017.10.11.08 Identifying Open Research Problems in Cryptography by Surveying Cryptographic Functions and Operations 1 Rahul Saha1, G. Geetha2, Gulshan Kumar3 and Hye-Jim Kim4 1,3School of Computer Science and Engineering, Lovely Professional University, Punjab, India 2Division of Research and Development, Lovely Professional University, Punjab, India 4Business Administration Research Institute, Sungshin W. University, 2 Bomun-ro 34da gil, Seongbuk-gu, Seoul, Republic of Korea Abstract Cryptography has always been a core component of security domain. Different security services such as confidentiality, integrity, availability, authentication, non-repudiation and access control, are provided by a number of cryptographic algorithms including block ciphers, stream ciphers and hash functions. Though the algorithms are public and cryptographic strength depends on the usage of the keys, the ciphertext analysis using different functions and operations used in the algorithms can lead to the path of revealing a key completely or partially. It is hard to find any survey till date which identifies different operations and functions used in cryptography. In this paper, we have categorized our survey of cryptographic functions and operations in the algorithms in three categories: block ciphers, stream ciphers and cryptanalysis attacks which are executable in different parts of the algorithms. This survey will help the budding researchers in the society of crypto for identifying different operations and functions in cryptographic algorithms. Keywords: cryptography; block; stream; cipher; plaintext; ciphertext; functions; research problems 1. Introduction Cryptography [1] in the previous time was analogous to encryption where the main task was to convert the readable message to an unreadable format. -

Applications of Search Techniques to Cryptanalysis and the Construction of Cipher Components. James David Mclaughlin Submitted F
Applications of search techniques to cryptanalysis and the construction of cipher components. James David McLaughlin Submitted for the degree of Doctor of Philosophy (PhD) University of York Department of Computer Science September 2012 2 Abstract In this dissertation, we investigate the ways in which search techniques, and in particular metaheuristic search techniques, can be used in cryptology. We address the design of simple cryptographic components (Boolean functions), before moving on to more complex entities (S-boxes). The emphasis then shifts from the construction of cryptographic arte- facts to the related area of cryptanalysis, in which we first derive non-linear approximations to S-boxes more powerful than the existing linear approximations, and then exploit these in cryptanalytic attacks against the ciphers DES and Serpent. Contents 1 Introduction. 11 1.1 The Structure of this Thesis . 12 2 A brief history of cryptography and cryptanalysis. 14 3 Literature review 20 3.1 Information on various types of block cipher, and a brief description of the Data Encryption Standard. 20 3.1.1 Feistel ciphers . 21 3.1.2 Other types of block cipher . 23 3.1.3 Confusion and diffusion . 24 3.2 Linear cryptanalysis. 26 3.2.1 The attack. 27 3.3 Differential cryptanalysis. 35 3.3.1 The attack. 39 3.3.2 Variants of the differential cryptanalytic attack . 44 3.4 Stream ciphers based on linear feedback shift registers . 48 3.5 A brief introduction to metaheuristics . 52 3.5.1 Hill-climbing . 55 3.5.2 Simulated annealing . 57 3.5.3 Memetic algorithms . 58 3.5.4 Ant algorithms . -
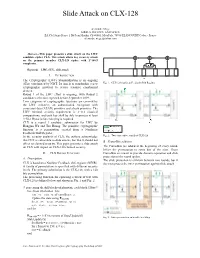
Slide Attack on CLX-128
Slide Attack on CLX-128 Alexandre Mège AIRBUS DEFENCE AND SPACE ZA Clef Saint-Pierre, 1 Bd Jean Moulin, CS 40001, MetaPole, 78996 ELANCOURT Cedex - France [email protected] Abstract—This paper presents a slide attack on the LWC candidate cipher CLX. This attack allows key recovery attack on the primary member CLX-128 cipher with 2^108.5 complexity. Keywords—LWC, CLX , slide,attack I. INTRODUCTION The Cryptography (LWC) Standardization is an ongoing effort coordinated by NIST. Its aim is to standardize a new Fig. 1. CLX-128 nonlinear Feedback Shift Register cryptographic protocol to secure resource constrained devices. Round 1 of the LWC effort is ongoing, with Round 2 candidates selection expected before September 2019. Two categories of cryptographic functions are covered by the LWC initiative, an authenticated encryption with associated data (AEAD) primitive and a hash primitive. The LWC minimal security requirement is 2^112 classical computations, and each key shall be able to process at least 2^50-1 Bytes before rekeying is required. CLX is a round 1 candidate submission for LWC by Hongjun Wu and Tao Huang. The primitive cryptographic function is a permutation created from a Nonlinear Feedback Shift Register. In the security analysis of CLX, the authors acknowledge Fig. 2. Two consecutive rounds of CLX-128 that CLX is vulnerable to slide attacks, but that it should not B. FrameBits addition affect its claimed security. This paper presents a slide attack on CLX with impact on CLX-128 claimed security. The FrameBits are added at the beginning of every round, before the permutation to some bits of the state. -

ICEBERG : an Involutional Cipher Efficient for Block Encryption in Reconfigurable Hardware
1 ICEBERG : an Involutional Cipher Efficient for Block Encryption in Reconfigurable Hardware. Francois-Xavier Standaert, Gilles Piret, Gael Rouvroy, Jean-Jacques Quisquater, Jean-Didier Legat UCL Crypto Group Laboratoire de Microelectronique Universite Catholique de Louvain Place du Levant, 3, B-1348 Louvain-La-Neuve, Belgium standaert,piret,rouvroy,quisquater,[email protected] Abstract. We present a fast involutional block cipher optimized for re- configurable hardware implementations. ICEBERG uses 64-bit text blocks and 128-bit keys. All components are involutional and allow very effi- cient combinations of encryption/decryption. Hardware implementations of ICEBERG allow to change the key at every clock cycle without any per- formance loss and its round keys are derived “on-the-fly” in encryption and decryption modes (no storage of round keys is needed). The result- ing design offers better hardware efficiency than other recent 128-key-bit block ciphers. Resistance against side-channel cryptanalysis was also con- sidered as a design criteria for ICEBERG. Keywords: block cipher design, efficient implementations, reconfigurable hardware, side-channel resistance. 1 Introduction In October 2000, NIST (National Institute of Standards and Technology) se- lected Rijndael as the new Advanced Encryption Standard. The selection pro- cess included performance evaluation on both software and hardware platforms. However, as implementation versatility was a criteria for the selection of the AES, it appeared that Rijndael is not optimal for reconfigurable hardware im- plementations. Its highly expensive substitution boxes are a typical bottleneck but the combination of encryption and decryption in hardware is probably as critical. In general, observing the AES candidates [1, 2], one may assess that the cri- teria selected for their evaluation led to highly conservative designs although the context of certain cryptanalysis may be considered as very unlikely (e.g. -
Cryptanalysis of Block Ciphers
Cryptanalysis of Block Ciphers Jiqiang Lu Technical Report RHUL–MA–2008–19 30 July 2008 Royal Holloway University of London Department of Mathematics Royal Holloway, University of London Egham, Surrey TW20 0EX, England http://www.rhul.ac.uk/mathematics/techreports CRYPTANALYSIS OF BLOCK CIPHERS JIQIANG LU Thesis submitted to the University of London for the degree of Doctor of Philosophy Information Security Group Department of Mathematics Royal Holloway, University of London 2008 Declaration These doctoral studies were conducted under the supervision of Prof. Chris Mitchell. The work presented in this thesis is the result of original research carried out by myself, in collaboration with others, whilst enrolled in the Information Security Group of Royal Holloway, University of London as a candidate for the degree of Doctor of Philosophy. This work has not been submitted for any other degree or award in any other university or educational establishment. Jiqiang Lu July 2008 2 Acknowledgements First of all, I thank my supervisor Prof. Chris Mitchell for suggesting block cipher cryptanalysis as my research topic when I began my Ph.D. studies in September 2005. I had never done research in this challenging ¯eld before, but I soon found it to be really interesting. Every time I ¯nished a manuscript, Chris would give me detailed comments on it, both editorial and technical, which not only bene¯tted my research, but also improved my written English. Chris' comments are fantastic, and it is straightforward to follow them to make revisions. I thank my advisor Dr. Alex Dent for his constructive suggestions, although we work in very di®erent ¯elds. -

Differential-Linear Cryptanalysis Revisited
Differential-Linear Cryptanalysis Revisited C´elineBlondeau1 and Gregor Leander2 and Kaisa Nyberg1 1 Department of Information and Computer Science, Aalto University School of Science, Finland fceline.blondeau, [email protected] 2 Faculty of Electrical Engineering and Information Technology, Ruhr Universit¨atBochum, Germany [email protected] Abstract. Block ciphers are arguably the most widely used type of cryptographic primitives. We are not able to assess the security of a block cipher as such, but only its security against known attacks. The two main classes of attacks are linear and differential attacks and their variants. While a fundamental link between differential and linear crypt- analysis was already given in 1994 by Chabaud and Vaudenay, these at- tacks have been studied independently. Only recently, in 2013 Blondeau and Nyberg used the link to compute the probability of a differential given the correlations of many linear approximations. On the cryptana- lytical side, differential and linear attacks have been applied on different parts of the cipher and then combined to one distinguisher over the ci- pher. This method is known since 1994 when Langford and Hellman presented the first differential-linear cryptanalysis of the DES. In this paper we take the natural step and apply the theoretical link between linear and differential cryptanalysis to differential-linear cryptanalysis to develop a concise theory of this method. We give an exact expression of the bias of a differential-linear approximation in a closed form under the sole assumption that the two parts of the cipher are independent. We also show how, under a clear assumption, to approximate the bias effi- ciently, and perform experiments on it. -

Boomerang Connectivity Table: a New Cryptanalysis Tool
Boomerang Connectivity Table: A New Cryptanalysis Tool Carlos Cid1, Tao Huang2, Thomas Peyrin2;3;4, Yu Sasaki5, and Ling Song2;3;6 1 Information Security Group Royal Holloway, University of London, UK [email protected] 2 School of Physical and Mathematical Sciences Nanyang Technological University, Singapore [email protected] [email protected] [email protected] 3 Temasek Laboratories, Nanyang Technological University, Singapore 4 School of Computer Science and Engineering Nanyang Technological University, Singapore 5 NTT Secure Platform Laboratories, Japan [email protected] 6 State Key Laboratory of Information Security, Institute of Information Engineering, Chinese Academy of Sciences, China Abstract. A boomerang attack is a cryptanalysis framework that re- gards a block cipher E as the composition of two sub-ciphers E1 ◦E0 and builds a particular characteristic for E with probability p2q2 by combin- ing differential characteristics for E0 and E1 with probability p and q, respectively. Crucially the validity of this figure is under the assumption that the characteristics for E0 and E1 can be chosen independently. In- deed, Murphy has shown that independently chosen characteristics may turn out to be incompatible. On the other hand, several researchers ob- served that the probability can be improved to p or q around the bound- ary between E0 and E1 by considering a positive dependency of the two characteristics, e.g. the ladder switch and S-box switch by Biryukov and Khovratovich. This phenomenon was later formalised by Dunkelman et al. as a sandwich attack that regards E as E1 ◦ Em ◦ E0, where Em sat- isfies some differential propagation among four texts with probability r, and the entire probability is p2q2r.