SEA a Scalable Encryption Algorithm for Small Embedded Applications
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Improved Rectangle Attacks on SKINNY and CRAFT
Improved Rectangle Attacks on SKINNY and CRAFT Hosein Hadipour1, Nasour Bagheri2 and Ling Song3( ) 1 Department of Mathematics and Computer Science, University of Tehran, Tehran, Iran, [email protected] 2 Electrical Engineering Department, Shahid Rajaee Teacher Training University, Tehran, Iran, [email protected] 3 Jinan University, Guangzhou, China [email protected] Abstract. The boomerang and rectangle attacks are adaptions of differential crypt- analysis that regard the target cipher E as a composition of two sub-ciphers, i.e., 2 2 E = E1 ◦ E0, to construct a distinguisher for E with probability p q by concatenat- ing two short differential trails for E0 and E1 with probability p and q respectively. According to the previous research, the dependency between these two differential characteristics has a great impact on the probability of boomerang and rectangle distinguishers. Dunkelman et al. proposed the sandwich attack to formalise such dependency that regards E as three parts, i.e., E = E1 ◦ Em ◦ E0, where Em contains the dependency between two differential trails, satisfying some differential propagation with probability r. Accordingly, the entire probability is p2q2r. Recently, Song et al. have proposed a general framework to identify the actual boundaries of Em and systematically evaluate the probability of Em with any number of rounds, and applied their method to accurately evaluate the probabilities of the best SKINNY’s boomerang distinguishers. In this paper, using a more advanced method to search for boomerang distinguishers, we show that the best previous boomerang distinguishers for SKINNY can be significantly improved in terms of probability and number of rounds. -

Improved Related-Key Attacks on DESX and DESX+
Improved Related-key Attacks on DESX and DESX+ Raphael C.-W. Phan1 and Adi Shamir3 1 Laboratoire de s´ecurit´eet de cryptographie (LASEC), Ecole Polytechnique F´ed´erale de Lausanne (EPFL), CH-1015 Lausanne, Switzerland [email protected] 2 Faculty of Mathematics & Computer Science, The Weizmann Institute of Science, Rehovot 76100, Israel [email protected] Abstract. In this paper, we present improved related-key attacks on the original DESX, and DESX+, a variant of the DESX with its pre- and post-whitening XOR operations replaced with addition modulo 264. Compared to previous results, our attack on DESX has reduced text complexity, while our best attack on DESX+ eliminates the memory requirements at the same processing complexity. Keywords: DESX, DESX+, related-key attack, fault attack. 1 Introduction Due to the DES’ small key length of 56 bits, variants of the DES under multiple encryption have been considered, including double-DES under one or two 56-bit key(s), and triple-DES under two or three 56-bit keys. Another popular variant based on the DES is the DESX [15], where the basic keylength of single DES is extended to 120 bits by wrapping this DES with two outer pre- and post-whitening keys of 64 bits each. Also, the endorsement of single DES had been officially withdrawn by NIST in the summer of 2004 [19], due to its insecurity against exhaustive search. Future use of single DES is recommended only as a component of the triple-DES. This makes it more important to study the security of variants of single DES which increase the key length to avoid this attack. -

Integral Cryptanalysis on Full MISTY1⋆
Integral Cryptanalysis on Full MISTY1? Yosuke Todo NTT Secure Platform Laboratories, Tokyo, Japan [email protected] Abstract. MISTY1 is a block cipher designed by Matsui in 1997. It was well evaluated and standardized by projects, such as CRYPTREC, ISO/IEC, and NESSIE. In this paper, we propose a key recovery attack on the full MISTY1, i.e., we show that 8-round MISTY1 with 5 FL layers does not have 128-bit security. Many attacks against MISTY1 have been proposed, but there is no attack against the full MISTY1. Therefore, our attack is the first cryptanalysis against the full MISTY1. We construct a new integral characteristic by using the propagation characteristic of the division property, which was proposed in 2015. We first improve the division property by optimizing a public S-box and then construct a 6-round integral characteristic on MISTY1. Finally, we recover the secret key of the full MISTY1 with 263:58 chosen plaintexts and 2121 time complexity. Moreover, if we can use 263:994 chosen plaintexts, the time complexity for our attack is reduced to 2107:9. Note that our cryptanalysis is a theoretical attack. Therefore, the practical use of MISTY1 will not be affected by our attack. Keywords: MISTY1, Integral attack, Division property 1 Introduction MISTY [Mat97] is a block cipher designed by Matsui in 1997 and is based on the theory of provable security [Nyb94,NK95] against differential attack [BS90] and linear attack [Mat93]. MISTY has a recursive structure, and the component function has a unique structure, the so-called MISTY structure [Mat96]. -

The First Biclique Cryptanalysis of Serpent-256
The First Biclique Cryptanalysis of Serpent-256 Gabriel C. de Carvalho1, Luis A. B. Kowada1 1Instituto de Computac¸ao˜ – Universidade Federal Fluminense (UFF) – Niteroi´ – RJ – Brazil Abstract. The Serpent cipher was one of the finalists of the AES process and as of today there is no method for finding the key with fewer attempts than that of an exhaustive search of all possible keys, even when using known or chosen plaintexts for an attack. This work presents the first two biclique attacks for the full-round Serpent-256. The first uses a dimension 4 biclique while the second uses a dimension 8 biclique. The one with lower dimension covers nearly 4 complete rounds of the cipher, which is the reason for the lower time complex- ity when compared with the other attack (which covers nearly 3 rounds of the cipher). On the other hand, the second attack needs a lot less pairs of plain- texts for it to be done. The attacks require 2255:21 and 2255:45 full computations of Serpent-256 using 288 and 260 chosen ciphertexts respectively with negligible memory. 1. Introduction The Serpent cipher is, along with MARS, RC6, Twofish and Rijindael, one of the AES process finalists [Nechvatal et al. 2001] and has not had, since its proposal, its full round versions attacked. It is a Substitution Permutation Network (SPN) with 32 rounds, 128 bit block size and accepts keys of sizes 128, 192 and 256 bits. Serpent has been targeted by several cryptanalysis [Kelsey et al. 2000, Biham et al. 2001b, Biham et al. -

Atlantic Highly Migratory Species Stock Assessment and Fisheries Evaluation Report 2019
Atlantic Highly Migratory Species Stock Assessment and Fisheries Evaluation Report 2019 U.S. Department of Commerce | National Oceanic and Atmospheric Administration | National Marine Fisheries Service 2019 Stock Assessment and Fishery Evaluation Report for Atlantic Highly Migratory Species Atlantic Highly Migratory Species Management Division May 2020 Highly Migratory Species Management Division NOAA Fisheries 1315 East-West Highway Silver Spring, MD 20910 Phone (301) 427-8503 Fax (301) 713-1917 For HMS Permitting Information and Regulations • HMS recreational fishermen, commercial fishermen, and dealer compliance guides: www.fisheries.noaa.gov/atlantic-highly-migratory-species/atlantic-hms-fishery- compliance-guides • Regulatory updates for tunas: hmspermits.noaa.gov For HMS Permit Purchase or Renewals Open Access Vessel Permits Issuer Permits Contact Information HMS Permit HMS Charter/Headboat, (888) 872-8862 Shop Atlantic Tunas (General, hmspermits.noaa.gov Harpoon, Trap), Swordfish General Commercial, HMS Angling (recreational) Southeast Commercial Caribbean Small (727) 824-5326 Regional Boat, Smoothhound Shark www.fisheries.noaa.gov/southeast/resources- Office fishing/southeast-fisheries-permits Greater Incidental HMS Squid Trawl (978) 281-9370 Atlantic www.fisheries.noaa.gov/new-england-mid- Regional atlantic/resources-fishing/vessel-and-dealer- Fisheries permitting-greater-atlantic-region Office Limited Access Vessel Permits Issuer Permits Contact Information HMS Permit Atlantic Tunas Purse Seine (888) 872-8862 Shop category hmspermits.noaa.gov -
The Data Encryption Standard (DES) – History
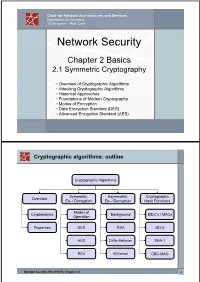
Chair for Network Architectures and Services Department of Informatics TU München – Prof. Carle Network Security Chapter 2 Basics 2.1 Symmetric Cryptography • Overview of Cryptographic Algorithms • Attacking Cryptographic Algorithms • Historical Approaches • Foundations of Modern Cryptography • Modes of Encryption • Data Encryption Standard (DES) • Advanced Encryption Standard (AES) Cryptographic algorithms: outline Cryptographic Algorithms Symmetric Asymmetric Cryptographic Overview En- / Decryption En- / Decryption Hash Functions Modes of Cryptanalysis Background MDC’s / MACs Operation Properties DES RSA MD-5 AES Diffie-Hellman SHA-1 RC4 ElGamal CBC-MAC Network Security, WS 2010/11, Chapter 2.1 2 Basic Terms: Plaintext and Ciphertext Plaintext P The original readable content of a message (or data). P_netsec = „This is network security“ Ciphertext C The encrypted version of the plaintext. C_netsec = „Ff iThtIiDjlyHLPRFxvowf“ encrypt key k1 C P key k2 decrypt In case of symmetric cryptography, k1 = k2. Network Security, WS 2010/11, Chapter 2.1 3 Basic Terms: Block cipher and Stream cipher Block cipher A cipher that encrypts / decrypts inputs of length n to outputs of length n given the corresponding key k. • n is block length Most modern symmetric ciphers are block ciphers, e.g. AES, DES, Twofish, … Stream cipher A symmetric cipher that generats a random bitstream, called key stream, from the symmetric key k. Ciphertext = key stream XOR plaintext Network Security, WS 2010/11, Chapter 2.1 4 Cryptographic algorithms: overview -
Lecture Note 8 ATTACKS on CRYPTOSYSTEMS I Sourav Mukhopadhyay
Lecture Note 8 ATTACKS ON CRYPTOSYSTEMS I Sourav Mukhopadhyay Cryptography and Network Security - MA61027 Attacks on Cryptosystems • Up to this point, we have mainly seen how ciphers are implemented. • We have seen how symmetric ciphers such as DES and AES use the idea of substitution and permutation to provide security and also how asymmetric systems such as RSA and Diffie Hellman use other methods. • What we haven’t really looked at are attacks on cryptographic systems. Cryptography and Network Security - MA61027 (Sourav Mukhopadhyay, IIT-KGP, 2010) 1 • An understanding of certain attacks will help you to understand the reasons behind the structure of certain algorithms (such as Rijndael) as they are designed to thwart known attacks. • Although we are not going to exhaust all possible avenues of attack, we will get an idea of how cryptanalysts go about attacking ciphers. Cryptography and Network Security - MA61027 (Sourav Mukhopadhyay, IIT-KGP, 2010) 2 • This section is really split up into two classes of attack: Cryptanalytic attacks and Implementation attacks. • The former tries to attack mathematical weaknesses in the algorithms whereas the latter tries to attack the specific implementation of the cipher (such as a smartcard system). • The following attacks can refer to either of the two classes (all forms of attack assume the attacker knows the encryption algorithm): Cryptography and Network Security - MA61027 (Sourav Mukhopadhyay, IIT-KGP, 2010) 3 – Ciphertext-only attack: In this attack the attacker knows only the ciphertext to be decoded. The attacker will try to find the key or decrypt one or more pieces of ciphertext (only relatively weak algorithms fail to withstand a ciphertext-only attack). -

Optimizing the Block Cipher Resource Overhead at the Link Layer Security Framework in the Wireless Sensor Networks
Proceedings of the World Congress on Engineering 2008 Vol I WCE 2008, July 2 - 4, 2008, London, U.K. Optimizing the Block Cipher Resource Overhead at the Link Layer Security Framework in the Wireless Sensor Networks Devesh C. Jinwala, Dhiren R. Patel and Kankar S. Dasgupta, data collected from different sensor nodes. Since the Abstract—The security requirements in Wireless Sensor processing of the data is done on-the-fly, while being Networks (WSNs) and the mechanisms to support the transmitted to the base station; the overall communication requirements, demand a critical examination. Therefore, the costs are reduced [2]. Due to the multi-hop communication security protocols employed in WSNs should be so designed, as and the in-network processing demanding applications, the to yield the optimum performance. The efficiency of the block cipher is, one of the important factors in leveraging the conventional end-to-end security mechanisms are not performance of any security protocol. feasible for the WSN [3]. Hence, the use of the standard In this paper, therefore, we focus on the issue of optimizing end-to-end security protocols like SSH, SSL [4] or IPSec [5] the security vs. performance tradeoff in the security protocols in WSN environment is rejected. Instead, appropriate link in WSNs. As part of the exercise, we evaluate the storage layer security architecture, with low associated overhead is requirements of the block ciphers viz. the Advanced Encryption required. Standard (AES) cipher Rijndael, the Corrected Block Tiny Encryption Algorithm (XXTEA) using the Output Codebook There are a number of research attempts that aim to do so. -

Hash Functions and the (Amplified) Boomerang Attack
Hash Functions and the (Amplified) Boomerang Attack Antoine Joux1,3 and Thomas Peyrin2,3 1 DGA 2 France T´el´ecomR&D [email protected] 3 Universit´ede Versailles Saint-Quentin-en-Yvelines [email protected] Abstract. Since Crypto 2004, hash functions have been the target of many at- tacks which showed that several well-known functions such as SHA-0 or MD5 can no longer be considered secure collision free hash functions. These attacks use classical cryptographic techniques from block cipher analysis such as differential cryptanal- ysis together with some specific methods. Among those, we can cite the neutral bits of Biham and Chen or the message modification techniques of Wang et al. In this paper, we show that another tool of block cipher analysis, the boomerang attack, can also be used in this context. In particular, we show that using this boomerang attack as a neutral bits tool, it becomes possible to lower the complexity of the attacks on SHA-1. Key words: hash functions, boomerang attack, SHA-1. 1 Introduction The most famous design principle for dedicated hash functions is indisputably the MD-SHA family, firstly introduced by R. Rivest with MD4 [16] in 1990 and its improved version MD5 [15] in 1991. Two years after, the NIST publishes [12] a very similar hash function, SHA-0, that will be patched [13] in 1995 to give birth to SHA-1. This family is still very active, as NIST recently proposed [14] a 256-bit new version SHA-256 in order to anticipate the potential cryptanalysis results and also to increase its security with regard to the fast growth of the computation power. -

Block Ciphers and the Data Encryption Standard
Lecture 3: Block Ciphers and the Data Encryption Standard Lecture Notes on “Computer and Network Security” by Avi Kak ([email protected]) January 26, 2021 3:43pm ©2021 Avinash Kak, Purdue University Goals: To introduce the notion of a block cipher in the modern context. To talk about the infeasibility of ideal block ciphers To introduce the notion of the Feistel Cipher Structure To go over DES, the Data Encryption Standard To illustrate important DES steps with Python and Perl code CONTENTS Section Title Page 3.1 Ideal Block Cipher 3 3.1.1 Size of the Encryption Key for the Ideal Block Cipher 6 3.2 The Feistel Structure for Block Ciphers 7 3.2.1 Mathematical Description of Each Round in the 10 Feistel Structure 3.2.2 Decryption in Ciphers Based on the Feistel Structure 12 3.3 DES: The Data Encryption Standard 16 3.3.1 One Round of Processing in DES 18 3.3.2 The S-Box for the Substitution Step in Each Round 22 3.3.3 The Substitution Tables 26 3.3.4 The P-Box Permutation in the Feistel Function 33 3.3.5 The DES Key Schedule: Generating the Round Keys 35 3.3.6 Initial Permutation of the Encryption Key 38 3.3.7 Contraction-Permutation that Generates the 48-Bit 42 Round Key from the 56-Bit Key 3.4 What Makes DES a Strong Cipher (to the 46 Extent It is a Strong Cipher) 3.5 Homework Problems 48 2 Computer and Network Security by Avi Kak Lecture 3 Back to TOC 3.1 IDEAL BLOCK CIPHER In a modern block cipher (but still using a classical encryption method), we replace a block of N bits from the plaintext with a block of N bits from the ciphertext. -

Multiple New Formulas for Cipher Performance Computing
International Journal of Network Security, Vol.20, No.4, PP.788-800, July 2018 (DOI: 10.6633/IJNS.201807 20(4).21) 788 Multiple New Formulas for Cipher Performance Computing Youssef Harmouch1, Rachid Elkouch1, Hussain Ben-azza2 (Corresponding author: Youssef Harmouch) Department of Mathematics, Computing and Networks, National Institute of Posts and Telecommunications1 10100, Allal El Fassi Avenue, Rabat, Morocco (Email:[email protected] ) Department of Industrial and Production Engineering, Moulay Ismail University2 National High School of Arts and Trades, Mekns, Morocco (Received Apr. 03, 2017; revised and accepted July 17, 2017) Abstract are not necessarily commensurate properties. For exam- ple, an online newspaper will be primarily interested in Cryptography is a science that focuses on changing the the integrity of their information while a financial stock readable information to unrecognizable and useless data exchange network may define their security as real-time to any unauthorized person. This solution presents the availability and information privacy [14, 23]. This means main core of network security, therefore the risk analysis that, the many facets of the attribute must all be iden- for using a cipher turn out to be an obligation. Until now, tified and adequately addressed. Furthermore, the secu- the only platform for providing each cipher resistance is rity attributes are terms of qualities, thus measuring such the cryptanalysis study. This cryptanalysis can make it quality terms need a unique identification for their inter- hard to compare ciphers because each one is vulnerable to pretations meaning [20, 24]. Besides, the attributes can a different kind of attack that is often very different from be interdependent. -

Related-Key Statistical Cryptanalysis
Related-Key Statistical Cryptanalysis Darakhshan J. Mir∗ Poorvi L. Vora Department of Computer Science, Department of Computer Science, Rutgers, The State University of New Jersey George Washington University July 6, 2007 Abstract This paper presents the Cryptanalytic Channel Model (CCM). The model treats statistical key recovery as communication over a low capacity channel, where the channel and the encoding are determined by the cipher and the specific attack. A new attack, related-key recovery – the use of n related keys generated from k independent ones – is defined for all ciphers vulnera- ble to single-key recovery. Unlike classical related-key attacks such as differential related-key cryptanalysis, this attack does not exploit a special structural weakness in the cipher or key schedule, but amplifies the weakness exploited in the basic single key recovery. The related- key-recovery attack is shown to correspond to the use of a concatenated code over the channel, where the relationship among the keys determines the outer code, and the cipher and the attack the inner code. It is shown that there exists a relationship among keys for which the communi- cation complexity per bit of independent key is finite, for any probability of key recovery error. This may be compared to the unbounded communication complexity per bit of the single-key- recovery attack. The practical implications of this result are demonstrated through experiments on reduced-round DES. Keywords: related keys, concatenated codes, communication channel, statistical cryptanalysis, linear cryptanalysis, DES Communicating Author: Poorvi L. Vora, [email protected] ∗This work was done while the author was in the M.S.