Modern Data Communications: Analog and Digital Signals, Compression, Data Integrity
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Digital Television Systems
This page intentionally left blank Digital Television Systems Digital television is a multibillion-dollar industry with commercial systems now being deployed worldwide. In this concise yet detailed guide, you will learn about the standards that apply to fixed-line and mobile digital television, as well as the underlying principles involved, such as signal analysis, modulation techniques, and source and channel coding. The digital television standards, including the MPEG family, ATSC, DVB, ISDTV, DTMB, and ISDB, are presented toaid understanding ofnew systems in the market and reveal the variations between different systems used throughout the world. Discussions of source and channel coding then provide the essential knowledge needed for designing reliable new systems.Throughout the book the theory is supported by over 200 figures and tables, whilst an extensive glossary defines practical terminology.Additional background features, including Fourier analysis, probability and stochastic processes, tables of Fourier and Hilbert transforms, and radiofrequency tables, are presented in the book’s useful appendices. This is an ideal reference for practitioners in the field of digital television. It will alsoappeal tograduate students and researchers in electrical engineering and computer science, and can be used as a textbook for graduate courses on digital television systems. Marcelo S. Alencar is Chair Professor in the Department of Electrical Engineering, Federal University of Campina Grande, Brazil. With over 29 years of teaching and research experience, he has published eight technical books and more than 200 scientific papers. He is Founder and President of the Institute for Advanced Studies in Communications (Iecom) and has consulted for several companies and R&D agencies. -

Analog Output Signal the Signal Saturation Can Be Controlled by Setting the Respective ▪ Introduction AO-LL and the AO-UL
FieldGuide Enhance Operations Analog Output Signal The Signal Saturation can be controlled by setting the respective ▪ Introduction AO-LL and the AO-UL. The AO-LL and the AO-UL are programmable Yokogawa’s pressure transmitters with BRAIN or HART within the parameter limits of the transmitter via the FieldMate. communication have a 4 to 20 mA analog signal corresponding to the Primary Variable (PV). This output signal is generated from the digital signal supplied by the DPHarp sensor using a 15BitD/A signal converter with 0.004% resolution. The transmitters are designed to drive output slightly greater than the 4 to 20 mA “Base” signal. The intention is to set analog alarm thresholds recognizably beyond the normal operating 4 to 20 mA range, to indicate measurement our of range, and to set further alarm thresholds to indicate a fault condition. ▪ Applicable Models > EJA-E Series: All models with either BRAIN or HART communication > EJX-A Series: All models with either BRAIN or HART communication ▪ Process Measurement Out-of-Range Standard Analog Output Signal Yokogawa’s standard analog output transmitters are factory set to an Analog Output– Lower Limit (AO-LL) and Analog Output-Upper Limit The AO-LL and the AO-UL can be set to any value between 3.6 mA to (AO-UL) of 3.6 mA and 21.6 mA respectively. This allows for a small 21.6 mA. amount of linear over-range process readings. This over-range signal is referred to as Signal Saturation. During operation, if the AO-LL or Although FieldMate is highlighted here, any Hart Communicator has AO-UL limits are reached, the analog signal locks to the respective access to these functions. -

The Big Picture: HDTV and High-Resolution Systems (Part 6 Of
Chapter 4 TV and HRS Technologies INTRODUCTION picture on the TV screen by scanning electron beams (one for each primary color) across the picture tube As an entertainment medium, HDTV is not and varying their intensity in exact synchronism revolutionary. It is simply another step in the with the original picture signal. ongoing evolution of television that began with black and white (B&W) TV in the 1940s and will The 1950s technologies used today to bring color continue into the future with as yet undreamed of TV pictures to the home have a variety of shortcom- technologies. Each successive generation of TV ings and imperfections that modern systems can technology attempts to provide a more realistic correct. TV production formats, established in the picture and sound within the constraints of low-cost, 1930s and 40s, were originally based on 35-mm easy-to-use consumer technology. motion picture film. This gave today’s TV picture its Here we describe conventional NTSC1 television, nearly square shape (or aspect ratio) of 4 units wide Advanced Television (ATV) systems, and some of by 3 high (4:3). Research has found, however, a their underlying technologies (box 4-l). The conver- strong viewer preference for screens 5 to 6 units gence of ATVS, computer and telecommunications wide by 3 units high—as seen in today’s theatres— equipment toward High Resolution Systems (HRS) that correspond to the human field of vision.4 is discussed later. The original motion picture standard was 16 CONVENTIONAL TELEVISION: pictures per second—manually cranked cameras could go no faster.5 At that rate the viewer saw a PRODUCTION, TRANSMISSION, significant ‘flicker’ in the picture displayed (hence AND RECEPTION the term, the ‘flicks’ ‘).6 In developing TV transmis- Television systems involve three distinct activi- sion standards, engineers sought a system that sent ties: l)production, 2) transmission, and 3) display of pictures often enough that viewers did not see them the TV program. -

Acquiring an Analog Signal: Bandwidth, Nyquist Sampling Theorem, and Aliasing
Acquiring an Analog Signal: Bandwidth, Nyquist Sampling Theorem, and Aliasing Overview Learn about acquiring an analog signal, including topics such as bandwidth, amplitude error, rise time, sample rate, the Nyquist Sampling Theorem, aliasing, and resolution. This tutorial is part of the Instrument Fundamentals series. Contents wwWhat is a Digitizer? wwBandwidth a. Calculating Amplitude Error b. Calculating Rise Time wwSample Rate a. Nyquist Sampling Theorem b. Aliasing wwResolution wwSummary ni.com/instrument-fundamentals Next Acquiring an Analog Signal: Bandwidth, Nyquist Sampling Theorem, and Aliasing What Is a Digitizer? Scientists and engineers often use a digitizer to capture analog data in the real world and convert it into digital signals for analysis. A digitizer is any device used to convert analog signals into digital signals. One of the most common digitizers is a cell phone, which converts a voice, an analog signal, into a digital signal to send to another phone. However, in test and measurement applications, a digitizer most often refers to an oscilloscope or a digital multimeter (DMM). This article focuses on oscilloscopes, but most topics are also applicable to other digitizers. Regardless of the type, the digitizer is vital for the system to accurately reconstruct a waveform. To ensure you select the correct oscilloscope for your application, consider the bandwidth, sampling rate, and resolution of the oscilloscope. Bandwidth The front end of an oscilloscope consists of two components: an analog input path and an analog-to-digital converter (ADC). The analog input path attenuates, amplifies, filters, and/or couples the signal to optimize it in preparation for digitization by the ADC. -
Fcc Written Response to the Gao Report on Dtv Table of Contents
FCC WRITTEN RESPONSE TO THE GAO REPORT ON DTV TABLE OF CONTENTS I. TECHNICAL GOALS 1. Develop Technical Standard for Digital Broadcast Operations……………………… 1 2. Pre-Transition Channel Assignments/Allotments……………………………………. 5 3. Construction of Pre-Transition DTV Facilities……………………………………… 10 4. Transition Broadcast Stations to Final Digital Operations………………………….. 16 5. Facilitate the production of set top boxes and other devices that can receive digital broadcast signals in connection with subscription services………………….. 24 6. Facilitate the production of television sets and other devices that can receive digital broadcast signals……………………………………………………………… 29 II. POLICY GOALS 1. Protect MVPD Subscribers in their Ability to Continue Watching their Local Broadcast Stations After the Digital Transition……………………………….. 37 2. Maximize Consumer Benefits of the Digital Transition……………………………... 42 3. Educate consumers about the DTV transition……………………………………….. 48 4. Identify public interest opportunities afforded by digital transition…………………. 53 III. CONSUMER OUTREACH GOALS 1. Prepare and Distribute Publications to Consumers and News Media………………. 59 2. Participate in Events and Conferences……………………………………………… 60 3. Coordinate with Federal, State and local Entities and Community Stakeholders…… 62 4. Utilize the Commission’s Advisory Committees to Help Identify Effective Strategies for Promoting Consumer Awareness…………………………………….. 63 5. Maintain and Expand Information and Resources Available via the Internet………. 63 IV. OTHER CRITICAL ELEMENTS 1. Transition TV stations in the cross-border areas from analog to digital broadcasting by February 17, 2009………………………………………………………………… 70 2. Promote Consumer Awareness of NTIA’s Digital-to-Analog Converter Box Coupon Program………………………………………………………………………72 I. TECHNICAL GOALS General Overview of Technical Goals: One of the most important responsibilities of the Commission, with respect to the nation’s transition to digital television, has been to shepherd the transformation of television stations from analog broadcasting to digital broadcasting. -

Minimum Signal Tests
Federal Communications Commission FCC 05-199 0 Kepeat steps for other TVs Measure injected noise level 0 Set signal attenuator to 81 dB 0 Measure the “long average power” twice for use as described following I” measurements of inJected noise level. Because both the injected noise power measurement and the injected signal measurement were performed using the same vector signal analyzer on the same amplitude range, the CNR is expected to be quite accurate, since it doesn’t depend on thc absolute calibration accuracy of the measuring instrument. Additional information on the testing is included in the “Measurement Method section of Chapter 3 Minimum Signal Tests Note that all measurements are performed using the vector signal analyzer (VSA), and all attenuator settings and measurements are entered into a spreadsheet that performs the required computations. The tests are performed for TV channels 3, IO, and 30. Connect equipment as shown in Figure A-2. VSA setup 0 Run DTV measurement software* 0 Set number of averages to 1200 0 Set selected broadcast channel 0 Execute “single cal” 0 Set amplitude range to -50 dBm (most sensitive range) RF player setup 0 Load “HawaiiLReferenceA file 0 Set output channel to selected channel 0 Set output level to -30 dBm Measure VSA self noise three times by connecting a 50-ohm termination to the VSA input and performing a “long average power” measurements. (The average of these measurements will be subtracted-in linear power units-from all subsequent measurements.) TV tests. Repeat for each of TV to be tested (typically eight). Include receiver D3 in each test sequence as a consistency check. -

Digital Television: Has the Revolution Stalled?
iBRIEF / Media & Communications Cite as 2001 Duke L. & Tech. Rev. 0014 3/26/2001 April 26, 2001 DIGITAL TELEVISION: HAS THE REVOLUTION STALLED? When digital television technology first hit the scene it garnered great excitement, with its promise of movie theater picture and sound on a fraction of the bandwidth of analog. A plan was implemented to transition from the current analog broadcasting system to a digital system effective December 23, 2006. As we reach the half point of this plan, the furor begins to die as the realities of the difficult change sink in. The History of Digital Television ¶1 The technological possibilities of digital television are immense.1 It could provide the broadcast of theater quality sound and picture via cable, antenna or satellite; multicasting which enables the transmission of multiple programs within one digital signal; and signals for data communications that could potentially bring to the TV the capabilities of web pages and interactive compact discs.2 ¶2 The motivation behind the development of digital television technologies can be traced back to the history of analog broadcasting. As television became a viable medium in the United States at the start of the Second World War, the establishment of technical standards in transmission and reception equipment was of vital importance. In 1940, the National Television Systems Committee (NTSC) met to determine guidelines for the transmission and reception of television signals. With the US leading the charge into early broadcasting in the late 1940s, the technology available at the time became entrenched and remains a part of our lives today, with the familiar 525-line low-resolution screens that bring us the evening news. -

Analog Access to the Telephone Network
Telecommunications Telephony Analog Access to the Telephone Network Courseware Sample 32964-F0 Order no.: 32964-00 First Edition Revision level: 01/2015 By the staff of Festo Didactic © Festo Didactic Ltée/Ltd, Quebec, Canada 2001 Internet: www.festo-didactic.com e-mail: [email protected] Printed in Canada All rights reserved ISBN 978-2-89289-541-4 (Printed version) Legal Deposit – Bibliothèque et Archives nationales du Québec, 2001 Legal Deposit – Library and Archives Canada, 2001 The purchaser shall receive a single right of use which is non-exclusive, non-time-limited and limited geographically to use at the purchaser's site/location as follows. The purchaser shall be entitled to use the work to train his/her staff at the purchaser's site/location and shall also be entitled to use parts of the copyright material as the basis for the production of his/her own training documentation for the training of his/her staff at the purchaser's site/location with acknowledgement of source and to make copies for this purpose. In the case of schools/technical colleges, training centers, and universities, the right of use shall also include use by school and college students and trainees at the purchaser's site/location for teaching purposes. The right of use shall in all cases exclude the right to publish the copyright material or to make this available for use on intranet, Internet and LMS platforms and databases such as Moodle, which allow access by a wide variety of users, including those outside of the purchaser's site/location. -
Design of a UAV-Based Radio Receiver for Avalanche Beacon Detection Using Software Defined Radio and Signal Processing
UPTEC F19 003 Examensarbete 30 hp Februari 2019 Design of a UAV-based radio receiver for avalanche beacon detection using software defined radio and signal processing Richard Hedlund Abstract Design of a UAV-based radio receiver for avalanche beacon detection using software defined radio and signal processing Richard Hedlund Teknisk- naturvetenskaplig fakultet UTH-enheten A fully functional proof of concept radio receiver for detecting avalanche beacons at the frequency 457 kHz was constructed in the work of this master thesis. The radio Besöksadress: receiver is intended to be mounted on an unmanned aerial vehicle (UAV or drone) Ångströmlaboratoriet Lägerhyddsvägen 1 and used to aid the mountain rescue teams by reducing the rescue time in finding Hus 4, Plan 0 avalanche victims carrying a transmitting beacon. The main parts of this master thesis involved hardware requirement analysis, software development, digital signal Postadress: processing and wireless communications. Box 536 751 21 Uppsala The radio receiver was customized to receive low power signal levels because Telefon: magnetic antennas are used and the avalanche beacon will operate in the reactive near 018 – 471 30 03 field of the radio receiver. Noise from external sources has a significant impact on the Telefax: performance of the radio receiver. 018 – 471 30 00 This master thesis allows for straightforward further development and refining of the Hemsida: radio receiver due to the flexibility of the used open-source software development kit http://www.teknat.uu.se/student GNU Radio where the digital signal processing was performed. Handledare: Johan Tenstam Ämnesgranskare: Mikael Sternad Examinator: Tomas Nyberg ISSN: 1401-5757, UPTEC F19 003 Populärvetenskaplig sammanfattning I detta examensarbete har en fullt funktionell "proof of concept" radiomottagare för de- tektering av lavintransceivers på frekvensen 457 kHz konstruerats. -

Carriers and Modulation DIGITAL TRANSMISSION of DIGITAL DATA
DIGITAL TRANSMISSION OF Carriers and Modulation DIGITAL DATA CS442 Review… Baseband Transmission Digital transmission is the transmission of electrical Baseband Transmission pulses. Digital information is binary in nature in that it has only two possible states 1 or 0. With unipolar signaling techniques, the voltage is Sequences of bits encode data (e.g., text always positive or negative (like a dc current). characters). In bipolar signaling, the 1’s and 0’s vary from a plus Digital signals are commonly referred to as baseband signals. voltage to a minus voltage (like an ac current). In order to successfully send and receive a message, both the sender and receiver have to agree how In general, bipolar signaling experiences fewer errors often the sender can transmit data (data rate). than unipolar signaling because the signals are Data rate often called bandwidth – but there is a more distinct. different definition of bandwidth referring to the frequency range of a signal! 1 Baseband Transmission Baseband Transmission Manchester encoding is a special type of unipolar signaling in which the signal is changed from a high to low (0) or low to high (1) in the middle of the signal. • More reliable detection of transition rather than level – consider perhaps some constant amount of dc noise, transitions still detectable but dc component could throw off NRZ-L scheme – Transitions still detectable even if polarity reversed Manchester encoding is commonly used in local area networks (ethernet, token ring). ANALOG TRANSMISSION OF Manchester Encoding DIGITAL DATA Analog Transmission occurs when the signal sent over the transmission media continuously varies from one state to another in a wave-like pattern. -

Analog and Digital Signals Digital Electronics TM 1.2 Introduction to Analog
Analog and Digital Signals Digital Electronics TM 1.2 Introduction to Analog Analog & Digital Signals This presentation will • Review the definitions of analog and digital signals. • Detail the components of an analog signal. • Define logic levels. Analog & Digital Signals • Detail the components of a digital signal. • Review the function of the virtual oscilloscope. Digital Electronics 2 Analog and Digital Signals Example of Analog Signals • An analog signal can be any time-varying signal. Analog Signals Digital Signals • Minimum and maximum values can be either positive or negative. • Continuous • Discrete • They can be periodic (repeating) or non-periodic. • Infinite range of values • Finite range of values (2) • Sine waves and square waves are two common analog signals. • Note that this square wave is not a digital signal because its • More exact values, but • Not as exact as analog, minimum value is negative. more difficult to work with but easier to work with Example: A digital thermostat in a room displays a temperature of 72. An analog thermometer measures the room 0 volts temperature at 72.482. The analog value is continuous and more accurate, but the digital value is more than adequate for the application and Sine Wave Square Wave Random-Periodic significantly easier to process electronically. 3 (not digital) 4 Project Lead The Way, Inc. Copyright 2009 1 Analog and Digital Signals Digital Electronics TM 1.2 Introduction to Analog Parts of an Analog Signal Logic Levels Before examining digital signals, we must define logic levels. A logic level is a voltage level that represents a defined Period digital state. -
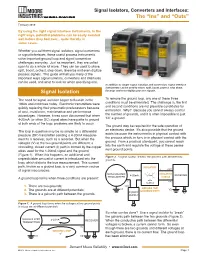
Signal Isolation
Signal Isolators, Converters and Interfaces: The “Ins” and “Outs” February 2019 By using the right signal interface instruments, in the right ways, potential problems can be easily avoided well before they boil over... quite literally in some cases. Whether you call them signal isolators, signal converters or signal interfaces, these useful process instruments solve important ground loop and signal conversion challenges everyday. Just as important, they are called upon to do a whole lot more. They can be used to share, split, boost, protect, step down, linearize and even digitize process signals. This guide will tell you many of the important ways signal isolators, converters and interfaces can be used, and what to look for when specifying one. In addition to simple signal isolation and conversion, signal interface instruments can be used to share, split, boost, protect, step down, Signal Isolation linearize and even digitize process signals. The need for signal isolation began to flourish in the To remove the ground loop, any one of these three 1960s and continues today. Electronic transmitters were conditions must be eliminated. The challenge is, the first quickly replacing their pneumatic predecessors because and second conditions are not plausible candidates for of cost, installation, maintenance and performance elimination. Why? Because you cannot always control advantages. However, it was soon discovered that when the number of grounds, and it is often impossible to just 4-20mA (or other DC) signal wires have paths to ground “lift” a ground. at both ends of the loop, problems are likely to occur. The ground may be required for the safe operation of The loop in question may be as simple as a differential an electronic device.