Mirai – Inside of an Iot Botnet
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Internet Infrastructure Review Vol.34
Internet Infrastructure Review Mar.2017 Vol. 34 Infrastructure Security Ursnif (Gozi) Anti-Analysis Techniques and Methods for Bypassing Them Technology Trends The Current State of Library OSes Internet Infrastructure Review March 2017 Vol.34 Executive Summary ............................................................................................................................ 3 1. Infrastructure Security .................................................................................................................. 4 1.1 Introduction ..................................................................................................................................... 4 1.2 Incident Summary ........................................................................................................................... 4 1.3 Incident Survey ...............................................................................................................................11 1.3.1 DDoS Attacks ...................................................................................................................................11 1.3.2 Malware Activities ......................................................................................................................... 13 1.3.3 SQL Injection Attacks ..................................................................................................................... 17 1.3.4 Website Alterations ....................................................................................................................... -
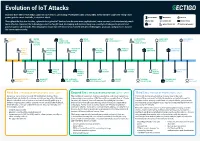
Evolution of Iot Attacks
Evolution of IoT Attacks By 2025, there will be 41.6 billion connected IoT devices, generating 79 zettabytes (ZB) of data (IDC). Every Internet-connected “thing,” from power grids to smart doorbells, is at risk of attack. BLUETOOTH INDUSTRIAL MEDICAL Throughout the last few decades, cyberattacks against IoT devices have become more sophisticated, more common, and unfortunately, much BOTNET GENERIC IOT SMART HOME more effective. However, the technology sector has fought back, developing and implementing new security technologies to prevent and CAR INFRASTRUCTURE WATCH/WEARABLE protect against cyberattacks. This infographic shows how the industry has evolved with new technologies, protocols, and processes to raise the bar on cybersecurity. STUXNET WATER BMW MIRAI FITBIT SAUDI PETROL SILEX LINUX DARK NEXUS VIRUS UTILITY CONNECTED BOTNET VULNERABILITY CHEMICAL MALWARE BOTNET SYSTEM DRIVE SYSTEM PLANT ATTACK (SCADA) PUERTO UNIVERSITY UKRAINIAN HAJIME AMNESIA AMAZON PHILIPS HUE RICO OF MICHIGAN POWER VIGILANTE BOTNET RING HACK LIGHTBULB SMART TRAFFIC GRID BOTNET METERS LIGHTS MEDTRONIC GERMAN TESLA CCTV PERSIRAI FANCY SWEYNTOOTH INSULIN STEEL MODEL S BOTNET BOTNET BEAR VS. FAMILY PUMPS MILL HACK REMOTE SPORTS HACK HACKABLE HEART BASHLITE FIAT CHRYSLER NYADROP SELF- REAPER THINKPHP TWO MILLION KAIJI MONITORS BOTNET REMOTE CONTROL UPDATING MALWARE BOTNET EXPLOITATION TAKEOVER MALWARE First Era | THE AGE OF EXPLORATION | 2005 - 2009 Second Era | THE AGE OF EXPLOITATION | 2011 - 2019 Third Era | THE AGE OF PROTECTION | 2020 Security is not a priority for early IoT/embedded devices. Most The number of connected devices is exploding, and cloud connectivity Connected devices are ubiquitous in every area of life, from cyberattacks are limited to malware and viruses impacting Windows- is becoming commonplace. -

Malware Trends
NCCIC National Cybersecurity and Communications Integration Center Malware Trends Industrial Control Systems Emergency Response Team (ICS-CERT) Advanced Analytical Laboratory (AAL) October 2016 This product is provided subject only to the Notification Section as indicated here:http://www.us-cert.gov/privacy/ SUMMARY This white paper will explore the changes in malware throughout the past several years, with a focus on what the security industry is most likely to see today, how asset owners can harden existing networks against these attacks, and the expected direction of developments and targets in the com- ing years. ii CONTENTS SUMMARY .................................................................................................................................................ii ACRONYMS .............................................................................................................................................. iv 1.INTRODUCTION .................................................................................................................................... 1 1.1 State of the Battlefield ..................................................................................................................... 1 2.ATTACKER TACTIC CHANGES ........................................................................................................... 2 2.1 Malware as a Service ...................................................................................................................... 2 2.2 Destructive Malware ...................................................................................................................... -

A Malicious Concept That Conquered the Elf Format
DDOS TROJAN: A MALICIOUS fl ooding tools) that provides an attacker with the possibility of forming a malicious botnet. The framework consists of C&C CONCEPT THAT CONQUERED panels, bot builders, installation scripts, port scanners, SSH THE ELF FORMAT brute-forcers, etc. In our paper we provide a survey of current Linux DDoS bots and we sketch a wider context of usage of Peter Kálnai & Jaromír Hořejší the above-mentioned components. This topic has been covered Avast Software, Czech Republic by many independent security researchers, e.g. the MalwareMustDie! group summarised their series of blogposts Email {kalnai, horejsi}@avast.com in [2]. The authors presented its early development in [21]. 2. COMMON CHARACTERISTICS ABSTRACT DDoS threats have been around ever since the Internet took 2.1 About the ELF format over half of global communications, posing the real problem of ELF is short for ‘Executable and Linkable Format’, which is a denial of access to online service providers. Recently, a new common standard format for executables under Unix systems. trend has emerged in non-Windows DDoS attacks that has been The instruction set architecture (ISA) of the binary is stored at induced by code availability, lack of security and an abundance the offset e_machine, and we refer to this parameter using the of resources. The attack infrastructure has undergone prefi x ‘EM_’. Unix systems power not only desktop and server signifi cant changes in structure, function and complexity. machines, but are also the main operating systems for Malware has evolved into complex and relatively sophisticated embedded devices. Although Intel 80386 (EM_386) and pieces of code, employing compression, advanced encryption AMD64 (EM_x86_64) ISAs are the most common for desktops and even rootkit capabilities. -

Identifying and Characterizing Bashlite and Mirai C&C Servers
Identifying and Characterizing Bashlite and Mirai C&C Servers Gabriel Bastos∗, Artur Marzano∗, Osvaldo Fonseca∗, Elverton Fazzion∗y, Cristine Hoepersz, Klaus Steding-Jessenz, Marcelo H. P. C. Chavesz, Italo´ Cunha∗, Dorgival Guedes∗, Wagner Meira Jr.∗ ∗Department of Computer Science – Universidade Federal de Minas Gerais (UFMG) yDepartment of Computing – Universidade Federal de Sao˜ Joao˜ del-Rei (UFSJ) zCERT.br - Brazilian National Computer Emergency Response Team NIC.br - Brazilian Network Information Center Abstract—IoT devices are often a vector for assembling massive which contributes to the rise of a large number of variants. botnets, as a consequence of being broadly available, having Variants exploit other vulnerabilities, include new forms of limited security protections, and significant challenges in deploy- attack, and use different mechanisms to circumvent existing ing software upgrades. Such botnets are usually controlled by centralized Command-and-Control (C&C) servers, which need forms of defense. The increasing number of variants of these to be identified and taken down to mitigate threats. In this paper malwares makes the analysis and reverse engineering process we propose a framework to infer C&C server IP addresses using expensive, hindering the development of countermeasures and four heuristics. Our heuristics employ static and dynamic analysis mitigations. To address the growing number of threats, security to automatically extract information from malware binaries. We analysts and researchers need tools to automate the collection, use active measurements to validate inferences, and demonstrate the efficacy of our framework by identifying and characterizing analysis, and reverse engineering of malware. C&C servers for 62% of 1050 malware binaries collected using The C&C server is a core component of botnets, responsible 47 honeypots. -

Designing an Effective Network Forensic Framework for The
Designing an effective network forensic framework for the investigation of botnets in the Internet of Things Nickolaos Koroniotis A thesis submitted in fulfilment of the requirements for the degree of Doctor of Philosophy School of Engineering and Information Technology The University of New South Wales Australia March 2020 COPYRIGHT STATEMENT ‘I hereby grant the University of New South Wales or its agents a non-exclusive licence to archive and to make available (including to members of the public) my thesis or dissertation in whole or part in the University libraries in all forms of media, now or here after known. I acknowledge that I retain all intellectual property rights which subsist in my thesis or dissertation, such as copyright and patent rights, subject to applicable law. I also retain the right to use all or part of my thesis or dissertation in future works (such as articles or books).’ ‘For any substantial portions of copyright material used in this thesis, written permission for use has been obtained, or the copyright material is removed from the final public version of the thesis.’ Signed ……………………………………………........................... Date …………………………………………….............................. AUTHENTICITY STATEMENT ‘I certify that the Library deposit digital copy is a direct equivalent of the final officially approved version of my thesis.’ Signed ……………………………………………........................... Date …………………………………………….............................. 1 Thesis Dissertation Sheet Surname/Family Name : Koroniotis Given Name/s : Nickolaos Abbreviation for degree : PhD as give in the University calendar Faculty : UNSW Canberra at ADFA School : UC Engineering & Info Tech Thesis Title : Designing an effective network forensic framework for the investigation of botnets in the Internet of Things 2 Abstract 350 words maximum: The emergence of the Internet of Things (IoT), has heralded a new attack surface, where attackers exploit the security weaknesses inherent in smart things. -

Techniques for Detecting Compromised Iot Devices
MSc System and network Engineering Research Project 1 Techniques for detecting compromised IoT devices Project Report Ivo van der Elzen Jeroen van Heugten February 12, 2017 Abstract The amount of connected Internet of Things (IoT) devices is growing, expected to hit 50 billion devices in 2020. Many of those devices lack proper security. This has led to malware families designed to infect IoT devices and use them in Distributed Denial of Service (DDoS) attacks. In this paper we do an in-depth analysis of two families of IoT malware to determine common properties which can be used for detection. Focusing on the ISP-level, we evaluate commonly available detection techniques and apply the results from our analysis to detect IoT malware activity in an ISP network. Applying our detection method to a real-world data set we find indications for a Mirai malware infection. Using generic honeypots we gain new insight in IoT malware behavior. 1 Introduction ple of days after the attacks, the source code for the malware (dubbed \Mirai") was pub- September 20th 2016: A record setting Dis- lished [9] [10]. tributed Denial of Service (DDoS) attack of over 660 Gbps is launched on the website krebsonse- With the rise of these IoT based DDoS at- curity.com of infosec journalist Brian Krebs [1]. tacks [11] it has become clear that this problem A few days later, web hosting company OVH will only become bigger in the future, unless reports they have been hit with a DDoS of over IoT device vendors accept responsibility and 1 Tbps [2]. -
Securing Your Home Routers: Understanding Attacks and Defense Strategies of the Modem’S Serial Number As a Password
Securing Your Home Routers Understanding Attacks and Defense Strategies Joey Costoya, Ryan Flores, Lion Gu, and Fernando Mercês Trend Micro Forward-Looking Threat Research (FTR) Team A TrendLabsSM Research Paper TREND MICRO LEGAL DISCLAIMER The information provided herein is for general information Contents and educational purposes only. It is not intended and should not be construed to constitute legal advice. The information contained herein may not be applicable to all situations and may not reflect the most current situation. 4 Nothing contained herein should be relied on or acted upon without the benefit of legal advice based on the particular facts and circumstances presented and nothing Entry Points: How Threats herein should be construed otherwise. Trend Micro reserves the right to modify the contents of this document Can Infiltrate Your Home at any time without prior notice. Router Translations of any material into other languages are intended solely as a convenience. Translation accuracy is not guaranteed nor implied. If any questions arise related to the accuracy of a translation, please refer to 10 the original language official version of the document. Any discrepancies or differences created in the translation are not binding and have no legal effect for compliance or Postcompromise: Threats enforcement purposes. to Home Routers Although Trend Micro uses reasonable efforts to include accurate and up-to-date information herein, Trend Micro makes no warranties or representations of any kind as to its accuracy, currency, or completeness. You agree that access to and use of and reliance on this document 17 and the content thereof is at your own risk. -

An Automated and Comprehensive Framework for Iot Botnet Detection and Analysis (Iot-BDA)
This article has been accepted for publication in a future issue of this journal, but has not been fully edited. Content may change prior to final publication. Citation information: DOI 10.1109/ACCESS.2021.3110188, IEEE Access Digital Object Identifier 10.1109/ACCESS.2017.DOI An Automated and Comprehensive Framework for IoT Botnet Detection and Analysis (IoT-BDA) TOLIJAN TRAJANOVSKI1, NING ZHANG1 1Department of Computer Science, University of Manchester, M13 9PL UK Corresponding author: Tolijan Trajanovski (e-mail: [email protected]). ABSTRACT The proliferation of insecure Internet-connected devices gave rise to the IoT botnets which can grow very large rapidly and may perform high-impact cyber-attacks. The related studies for tackling IoT botnets are concerned with either capturing or analyzing IoT botnet samples, using honeypots and sandboxes, respectively. The lack of integration between the two implies that the samples captured by the honeypots must be manually submitted for analysis in sandboxes, introducing a delay during which a botnet may change its operation. Furthermore, the effectiveness of the proposed sandboxes is limited by the potential use of anti-analysis techniques and the inability to identify features for effective detection and identification of IoT botnets. In this paper, we propose and evaluate a novel framework, the IoT-BDA framework, for automated capturing, analysis, identification, and reporting of IoT botnets. The framework consists of honeypots integrated with a novel sandbox that supports a wider range of hardware and software configurations, and can identify indicators of compromise and attack, along with anti-analysis, persistence, and anti-forensics techniques. These features can make botnet detection and analysis, and infection remedy more effective. -

Early Detection of Mirai-Like Iot Bots in Large-Scale Networks Through Sub-Sampled Packet Traffic Analysis
Early Detection Of Mirai-Like IoT Bots In Large-Scale Networks Through Sub-Sampled Packet Traffic Analysis Ayush Kumar and Teng Joon Lim Department of Electrical and Computer Engineering, National University of Singapore, Singapore 119077 [email protected], [email protected] Abstract. The widespread adoption of Internet of Things has led to many secu- rity issues. Recently, there have been malware attacks on IoT devices, the most prominent one being that of Mirai. IoT devices such as IP cameras, DVRs and routers were compromised by the Mirai malware and later large-scale DDoS at- tacks were propagated using those infected devices (bots) in October 2016. In this research, we develop a network-based algorithm which can be used to detect IoT bots infected by Mirai or similar malware in large-scale networks (e.g. ISP network). The algorithm particularly targets bots scanning the network for vul- nerable devices since the typical scanning phase for botnets lasts for months and the bots can be detected much before they are involved in an actual attack. We analyze the unique signatures of the Mirai malware to identify its presence in an IoT device. The prospective deployment of our bot detection solution is discussed next along with the countermeasures which can be taken post detection. Further, to optimize the usage of computational resources, we use a two-dimensional (2D) packet sampling approach, wherein we sample the packets transmitted by IoT devices both across time and across the devices. Leveraging the Mirai signatures identified and the 2D packet sampling approach, a bot detection algorithm is pro- posed. -

Honor Among Thieves: Towards Understanding the Dynamics and Interdependencies in Iot Botnets
Honor Among Thieves: Towards Understanding the Dynamics and Interdependencies in IoT Botnets Jinchun Choi1;2, Ahmed Abusnaina1, Afsah Anwar1, An Wang3, Songqing Chen4, DaeHun Nyang2, Aziz Mohaisen1 1University of Central Florida 2Inha University 3Case Western Reserve University 4George Mason University Abstract—In this paper, we analyze the Internet of Things (IoT) affected. The same botnet was able to take down the Internet Linux malware binaries to understand the dependencies among of the African nation of Liberia [14]. malware. Towards this end, we use static analysis to extract Competition and coordination among botnets are not well endpoints that malware communicates with, and classify such endpoints into targets and dropzones (equivalent to Command explored, although recent reports have highlighted the potential and Control). In total, we extracted 1,457 unique dropzone of such competition as demonstrated in adversarial behaviors IP addresses that target 294 unique IP addresses and 1,018 of Gafgyt towards competing botnets [9]. Understanding a masked target IP addresses. We highlight various characteristics phenomenon in behavior is important for multiple reasons. of those dropzones and targets, including spatial, network, and First, such an analysis would highlight the competition and organizational affinities. Towards the analysis of dropzones’ interdependencies and dynamics, we identify dropzones chains. alliances among IoT botnets (or malactors; i.e., those who Overall, we identify 56 unique chains, which unveil coordination are behind the botnet), which could shed light on cybercrime (and possible attacks) among different malware families. Further economics. Second, understanding such a competition would analysis of chains with higher node counts reveals centralization. necessarily require appropriate analysis modalities, and such We suggest a centrality-based defense and monitoring mechanism a competition signifies those modalities, even when they are to limit the propagation and impact of malware. -
Iot Vulnerabilities Easily 5
• Babak D. Beheshti, Associate Dean of the School of Engineering and Computing Sciences at NYIT. • Clyde Bennett, Chief Healthcare Technology Strategist at Aldridge Health. • Ross Brewer, VP and MD of EMEA at LogRhythm. • Ben Desjardins, Director of Security Solutions at Radware. • Eric O'Neill, National Security Strategist at Carbon Black. • Jeff Schilling, Chief of Operations and Security at Armor. • Karl Sigler, Threat Intelligence Manager at Trustwave. • Sigurdur Stefnisson, VP of Threat Research at CYREN. • Amos Stern, CEO at Siemplify. • Ronen Yehoshua, CEO at Morphisec. ! Visit the magazine website at www.insecuremag.com Feedback and contributions: Mirko Zorz, Editor in Chief - [email protected] News: Zeljka Zorz, Managing Editor - [email protected] Marketing: Berislav Kucan, Director of Operations - [email protected] (IN)SECURE Magazine can be freely distributed in the form of the original, non-modified PDF document. Distribution of modified versions of (IN)SECURE Magazine content is prohibited without permission. ! Copyright (IN)SECURE Magazine 2016. www.insecuremag.com Are all IoT vulnerabilities easily 5. Insecure or no network pairing control op- avoidable? tions (device to device or device to net- works). Every vulnerability or privacy issue reported 6. Not testing for common code injection ex- for consumer connected home and wearable ploits. technology products since November 2015 7. The lack of transport security and encrypt- could have been easily avoided, according to ed storage including unencrypted data the Online Trust Alliance (OTA). transmission of personal and sensitive in- formation including but not limited to user OTA researchers analyzed publicly reported ID and passwords. device vulnerabilities from November 2015 8. Lacking a sustainable and supportable through July 2016, and found the most glaring plan to address vulnerabilities through the failures were attributed to: product lifecycle including the lack of soft- ware/firmware update capabilities and/or insecure and untested security patches/ 1.