Malware Analysis Bahcesehir University Cyber Security Msc Program
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Malware and Social Engineering Attacks
chapter 2 Malware and Social Engineering Attacks After completing this chapter, you will be able to do the following: ● Describe the differences between a virus and a worm ● List the types of malware that conceals its appearance ● Identify different kinds of malware that is designed for profit ● Describe the types of social engineering psychological attacks ● Explain physical social engineering attacks 41 42 Chapter 2 Malware and Social Engineering Attacks Today’s Attacks and Defenses Successful software companies use a variety of strategies to outsell their competition and gain market share. These strategies may include selling their software at or below a com- petitor’s price, offering better technical support to customers, or providing customized software for clients. And if all else fails, a final strategy can be to buy out the competition through a merger or acquisition. These strategies are also being widely used by attackers who sell their attack software to others. Approximately two out of three malicious Web attacks have been developed using one of three popular attack toolkits. The toolkits are MPack (the most popular attack toolkit, which has almost half of the attacker toolkit mar- ket), NeoSploit, and ZeuS. These toolkits, which are bought and sold online through the underground attacker community, are used to create customized malware that can steal personal information, execute fraudulent financial transactions, and infect computers without the user’s knowledge. The toolkits range in price from only $40 to as much as $8,000. The developers behind these attack toolkits compete fiercely with each other. Some of their tactics include updating the toolkits to keep ahead of the latest security defenses, advertising their attack toolkits as cheaper than the competition, and provid- ing technical support to purchasers. -

Internet Security Threat Report Volume 24 | February 2019
ISTRInternet Security Threat Report Volume 24 | February 2019 THE DOCUMENT IS PROVIDED “AS IS” AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. SYMANTEC CORPORATION SHALL NOT BE LIABLE FOR INCIDENTAL OR CONSEQUENTIAL DAMAGES IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS DOCUMENT. THE INFORMATION CONTAINED IN THIS DOCUMENT IS SUBJECT TO CHANGE WITHOUT NOTICE. INFORMATION OBTAINED FROM THIRD PARTY SOURCES IS BELIEVED TO BE RELIABLE, BUT IS IN NO WAY GUARANTEED. SECURITY PRODUCTS, TECHNICAL SERVICES, AND ANY OTHER TECHNICAL DATA REFERENCED IN THIS DOCUMENT (“CONTROLLED ITEMS”) ARE SUBJECT TO U.S. EXPORT CONTROL AND SANCTIONS LAWS, REGULATIONS AND REQUIREMENTS, AND MAY BE SUBJECT TO EXPORT OR IMPORT REGULATIONS IN OTHER COUNTRIES. YOU AGREE TO COMPLY STRICTLY WITH THESE LAWS, REGULATIONS AND REQUIREMENTS, AND ACKNOWLEDGE THAT YOU HAVE THE RESPONSIBILITY TO OBTAIN ANY LICENSES, PERMITS OR OTHER APPROVALS THAT MAY BE REQUIRED IN ORDER FOR YOU TO EXPORT, RE-EXPORT, TRANSFER IN COUNTRY OR IMPORT SUCH CONTROLLED ITEMS. TABLE OF CONTENTS 1 2 3 BIG NUMBERS YEAR-IN-REVIEW FACTS AND FIGURES METHODOLOGY Formjacking Messaging Cryptojacking Malware Ransomware Mobile Living off the land Web attacks and supply chain attacks Targeted attacks Targeted attacks IoT Cloud Underground economy IoT Election interference MALICIOUS -

Security Now! #664 - 05-22-18 Spectreng Revealed
Security Now! #664 - 05-22-18 SpectreNG Revealed This week on Security Now! This week we examine the recent flaws discovered in the secure Signal messaging app for desktops, the rise in DNS router hijacking, another seriously flawed consumer router family, Microsoft Spectre patches for Win10's April 2018 feature update, the threat of voice assistant spoofing attacks, the evolving security of HTTP, still more new trouble with GPON routers, Facebook's Android app mistake, BMW's 14 security flaws and some fun miscellany. Then we examine the news of the next-generation of Spectre processor speculation flaws and what they mean for us. Our Picture of the Week Security News Update your Signal Desktop Apps for Windows & Linux A few weeks ago, Argentinian security researchers discovered a severe vulnerability in the Signal messaging app for Windows and Linux desktops that allows remote attackers to execute malicious code on recipient systems simply by sending a message—without requiring any user interaction. The vulnerability was accidentally discovered while researchers–amond them Juliano Rizzo–were chatting on Signal messenger and one of them shared a link of a vulnerable site with an XSS payload in its URL. However, the XSS payload unexpectedly got executed on the Signal desktop app!! (Juliano Rizzo was on the beach when the BEAST and CRIME attacks occurred to him.) After analyzing the scope of this issue by testing multiple XSS payloads, they found that the vulnerability resides in the function responsible for handling shared links, allowing attackers to inject user-defined HTML/JavaScript code via iFrame, image, video and audio tags. -

Internet of Things Botnet Detection Approaches: Analysis and Recommendations for Future Research
applied sciences Systematic Review Internet of Things Botnet Detection Approaches: Analysis and Recommendations for Future Research Majda Wazzan 1,*, Daniyal Algazzawi 2 , Omaima Bamasaq 1, Aiiad Albeshri 1 and Li Cheng 3 1 Computer Science Department, Faculty of Computing and Information Technology, King Abdulaziz University, Jeddah 21589, Saudi Arabia; [email protected] (O.B.); [email protected] (A.A.) 2 Information Systems Department, Faculty of Computing and Information Technology, King Abdulaziz University, Jeddah 21589, Saudi Arabia; [email protected] 3 Xinjiang Technical Institute of Physics & Chemistry Chinese Academy of Sciences, Urumqi 830011, China; [email protected] * Correspondence: [email protected] Abstract: Internet of Things (IoT) is promising technology that brings tremendous benefits if used optimally. At the same time, it has resulted in an increase in cybersecurity risks due to the lack of security for IoT devices. IoT botnets, for instance, have become a critical threat; however, systematic and comprehensive studies analyzing the importance of botnet detection methods are limited in the IoT environment. Thus, this study aimed to identify, assess and provide a thoroughly review of experimental works on the research relevant to the detection of IoT botnets. To accomplish this goal, a systematic literature review (SLR), an effective method, was applied for gathering and critically reviewing research papers. This work employed three research questions on the detection methods used to detect IoT botnets, the botnet phases and the different malicious activity scenarios. The authors analyzed the nominated research and the key methods related to them. The detection Citation: Wazzan, M.; Algazzawi, D.; methods have been classified based on the techniques used, and the authors investigated the botnet Bamasaq, O.; Albeshri, A.; Cheng, L. -

Security of Personal Identifiable Information
https://doi.org/10.48009/2_iis_2008_634-638 SECURITY OF PERSONAL IDENTIFIABLE INFORMATION Jack D. Shorter,Texas A&M University – Kingsville, [email protected] Karen A. Forcht, North Carolina A & T University, [email protected] Alicia Aldridge,Appalachian State University, [email protected] Daphyne S. Thomas, James Madison University,[email protected] Abstract impacted if Google’s merger with DoubleClick is completed? In today’s fast moving world, the use of technology has become a part of everyday life. Whether it is DoubleClick is one of the fastest growing digital using a computer to access the Internet, sending marketers, and the amount of user data that could be email, or using cell phones to contact friends and provided to them from Google would be phenomenal. family, technology is found in almost everything. At issue is whether Google can be trusted with users’ Technology provides many conveniences such as PII at its disposal. Armed with this information online banking, renewing a driver’s license, making a DoubleClick could target consumers with a method known as “retargeting.” This type of practice was consumer purchase, or conducting research. th However, using technology has its pros and cons. On one of the topics discussed at the 17 annual the positive side, conducting personal business online Conference on Computers, Freedom & Privacy in is convenient, saves time, and is economical. May 2007. This method uses ads and serves them to However, with the pluses, there are usually minuses users based on their Web surfing behaviors. [4] as well. In the case of an online consumer purchase, one may find price deals, but may discover a lack of A user uses a search engine such as Google to find a quality or poor customer care. -
![What Is Exploit Kit and How Does It Work? [1]Ade Kurniawan, [2]Ahmadfitriansyah [1][2]Department of Informatics Engineering, Universal University,Batam, Indonesia](https://docslib.b-cdn.net/cover/8911/what-is-exploit-kit-and-how-does-it-work-1-ade-kurniawan-2-ahmadfitriansyah-1-2-department-of-informatics-engineering-universal-university-batam-indonesia-348911.webp)
What Is Exploit Kit and How Does It Work? [1]Ade Kurniawan, [2]Ahmadfitriansyah [1][2]Department of Informatics Engineering, Universal University,Batam, Indonesia
International Journal of Pure and Applied Mathematics Volume 118 No. 20 2018, 509-516 ISSN: 1314-3395 (on-line version) url: http://www.ijpam.eu Special Issue ijpam.eu What is Exploit Kit and How Does it Work? [1]Ade Kurniawan, [2]AhmadFitriansyah [1][2]Department of Informatics Engineering, Universal University,Batam, Indonesia Abstract— In the Year 2016 to mid-2017, the analysts have claimed those years as the years of Malware especially Ransomware. The number, spread, infection and impact of malware have caused many users, businesses, governments, and organizations to be anxious, one of the tools to spread it by using exploit kits. A popular method of mass distribution used the perpetrators of cyber criminals is using the exploit kit. Exploit kit has become more effective, cheaper and sophisticated tools to spread malware to their victims. Therefore, in this paper, we provide this research using the Network Forensic Method. The results which are done will explain the chain of events about what the exploit kit is and how the exploit kit works, including actors, campaigns, payload, and terminology involved in the spreading of malware Index Terms—Exploit Kit, Payload, Malware, Ransomware, and Chain of events. I. INTRODUCTION In our digital era, everything is connected and Network Forensics Method. Network forensics is a everyone is vulnerable. The development, part of Digital Forensic conducted with scientific dependability, and complexity of computer software methods to identify, analyse and reconstruct events have brought immediate implications for global based on digital evidence/logs from the network safety and security, especially physical objects such [14][15][16]. -

Analyse De Mpack Et De La Bluepill (Septembre 2007)
7 BRE 200 L’ACTU SÉCU 16 SEPTEM LES “UNE MENACE NOMMÉE MPACK” Le hacking devient un jeu d’enfant... SOMMAIRE DOSSIER SPÉCIAL PACK : LES ROOTKITS VIRTUELS “BLUEPILL” ARTNERS.COM MPACK et TORPIG LES VULNÉRABILITÉS DU MOIS ICEPACK LES OUTILS LIBRES .XMCOP FISHING_BAIT SHARK WWW © XMCO Partners - 2007 [1] Ce document est la propriété du cabinet XMCO Partners. Toute reproduction est strictement interdite. 7 BRE 200 L’EDITO SEPTEM Les packs spécial rentrée... Vous avez certainement vu le film tions, nous plongeons pour vous Michel Sardou et de Johnny Hal- « The Matrix » : le monde dans au cœur des menaces du moment lyday contrôlés par une backdoor lequel nous vivons ne serait pas pour les décortiquer et ainsi vous (voir l’interview de LCI de Marc réel, nous serions en fait endormis aider à vous en protéger. Behar sur notre site). pendant qu’une machine nous ferait vivre dans un monde virtuel L’Actu Secu continue d’évoluer et et utiliserait notre énergie vitale ne manquera pas de présenter pour se nourrir. des sujets d’actualité comme : l’ISO27001, la sécurité Bluetooth, Cette fiction est la toile de fond de l’Ajax ou encore les risques liés à ce 16ième ActuSécu. Fort de nos la technologie RFID… 1000 téléchargements pour son numéro consacré aux Botnets, Bonne lecture nous vous présentons pour cette rentrée 2007 les menaces qui font L’équipe XMCO vous souhaite et feront parler d’elles : MPACK, une bonne rentrée IcePack, la BluePill, Torpig, Des menaces d'ailleurs présentes Shark… dans l’actualité du mois d’août : les clients du Crédit Mutuel atta- Avec le même souci de clarté qui qués par le trojan Banker « Tor- nous anime lors de nos presta- pig » ou encore les ordinateurs de AOUT 2007 Nombre de bulletins Microsoft : 9 Nombre d’exploits dangereux : 20 Nombre de bulletins XMCO : 103 Le TOP des Menaces du Mois 1. -

Technical Brief P2P Iot Botnets Clean AC Font
Uncleanable and Unkillable: The Evolution of IoT Botnets Through P2P Networking Technical Brief By Stephen Hilt, Robert McArdle, Fernando Merces, Mayra Rosario, and David Sancho Introduction Peer-to-peer (P2P) networking is a way for computers to connect to one another without the need for a central server. It was originally invented for file sharing, with BitTorrent being the most famous P2P implementation. Decentralized file-sharing systems built on P2P networking have stood the test of time. Even though they have been used to share illegal pirated content for over 20 years, authorities have not been able to put a stop to these systems. Of course, malicious actors have used it for malware for quite a long time as well. Being able to create and manage botnets without the need for a central server is a powerful capability, mostly because law enforcement and security companies typically take down criminal servers. And since a P2P botnet does not need a central command-and-control (C&C) server, it is much more difficult to take down. From the point of view of defenders, this is the scariest problem presented by P2P botnets: If they cannot be taken down centrally, the only option available would be to disinfect each of the bot clients separately. Since computers communicate only with their own peers, the good guys would need to clean all the members one by one for a botnet to disappear. Originally, P2P botnets were implemented in Windows, but developers of internet-of-things (IoT) botnets do have a tendency to start incorporating this feature into their creations. -

Crimeware on the Net
Crimeware on the Net The “Behind the scenes” of the new web economy Iftach Ian Amit Director, Security Research – Finjan BlackHat Europe, Amsterdam 2008 Who Am I ? (iamit) • Iftach Ian Amit – In Hebrew it makes more sense… • Director Security Research @ Finjan • Various security consulting/integration gigs in the past – R&D – IT • A helping hand when needed… (IAF) 2 BlackHat Europe – Amsterdam 2008 Today’s Agenda • Terminology • Past vs. Present – 10,000 feet view • Business Impact • Key Characteristics – what does it look like? – Anti-Forensics techniques – Propagation methods • What is the motive (what are they looking for)? • Tying it all up – what does it look like when successful (video). • Anything in it for us to learn from? – Looking forward on extrusion testing methodologies 3 BlackHat Europe – Amsterdam 2008 Some Terminology • Crimeware – what we refer to most malware these days is actually crimeware – malware with specific goals for making $$$ for the attackers. • Attackers – not to be confused with malicious code writers, security researchers, hackers, crackers, etc… These guys are the Gordon Gecko‟s of the web security field. The buy low, and capitalize on the investment. • Smart (often mislead) guys write the crimeware and get paid to do so. 4 BlackHat Europe – Amsterdam 2008 How Do Cybercriminals Steal Business Data? Criminals’ activity in the cyberspace Federal Prosecutor: “Cybercrime Is Funding Organized Crime” 5 BlackHat Europe – Amsterdam 2008 The Business Impact Of Crimeware Criminals target sensitive business data -

Internet Infrastructure Review Vol.34
Internet Infrastructure Review Mar.2017 Vol. 34 Infrastructure Security Ursnif (Gozi) Anti-Analysis Techniques and Methods for Bypassing Them Technology Trends The Current State of Library OSes Internet Infrastructure Review March 2017 Vol.34 Executive Summary ............................................................................................................................ 3 1. Infrastructure Security .................................................................................................................. 4 1.1 Introduction ..................................................................................................................................... 4 1.2 Incident Summary ........................................................................................................................... 4 1.3 Incident Survey ...............................................................................................................................11 1.3.1 DDoS Attacks ...................................................................................................................................11 1.3.2 Malware Activities ......................................................................................................................... 13 1.3.3 SQL Injection Attacks ..................................................................................................................... 17 1.3.4 Website Alterations ....................................................................................................................... -
Evolution of Iot Attacks
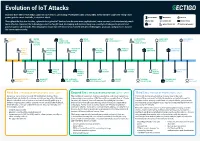
Evolution of IoT Attacks By 2025, there will be 41.6 billion connected IoT devices, generating 79 zettabytes (ZB) of data (IDC). Every Internet-connected “thing,” from power grids to smart doorbells, is at risk of attack. BLUETOOTH INDUSTRIAL MEDICAL Throughout the last few decades, cyberattacks against IoT devices have become more sophisticated, more common, and unfortunately, much BOTNET GENERIC IOT SMART HOME more effective. However, the technology sector has fought back, developing and implementing new security technologies to prevent and CAR INFRASTRUCTURE WATCH/WEARABLE protect against cyberattacks. This infographic shows how the industry has evolved with new technologies, protocols, and processes to raise the bar on cybersecurity. STUXNET WATER BMW MIRAI FITBIT SAUDI PETROL SILEX LINUX DARK NEXUS VIRUS UTILITY CONNECTED BOTNET VULNERABILITY CHEMICAL MALWARE BOTNET SYSTEM DRIVE SYSTEM PLANT ATTACK (SCADA) PUERTO UNIVERSITY UKRAINIAN HAJIME AMNESIA AMAZON PHILIPS HUE RICO OF MICHIGAN POWER VIGILANTE BOTNET RING HACK LIGHTBULB SMART TRAFFIC GRID BOTNET METERS LIGHTS MEDTRONIC GERMAN TESLA CCTV PERSIRAI FANCY SWEYNTOOTH INSULIN STEEL MODEL S BOTNET BOTNET BEAR VS. FAMILY PUMPS MILL HACK REMOTE SPORTS HACK HACKABLE HEART BASHLITE FIAT CHRYSLER NYADROP SELF- REAPER THINKPHP TWO MILLION KAIJI MONITORS BOTNET REMOTE CONTROL UPDATING MALWARE BOTNET EXPLOITATION TAKEOVER MALWARE First Era | THE AGE OF EXPLORATION | 2005 - 2009 Second Era | THE AGE OF EXPLOITATION | 2011 - 2019 Third Era | THE AGE OF PROTECTION | 2020 Security is not a priority for early IoT/embedded devices. Most The number of connected devices is exploding, and cloud connectivity Connected devices are ubiquitous in every area of life, from cyberattacks are limited to malware and viruses impacting Windows- is becoming commonplace. -

Dissecting Web Attacks
Dissecting Web Attacks Val Smith ([email protected]) Colin Ames ([email protected]) Delchi ([email protected]) Bios Valsmith – Affiliations: • Attack Research • Metasploit • cDc – Work: • Attack Techniques Research - History • Pen Tester/ Exploit • Founder Offensive Computing developer • Speaker • Reverse Engineer - Blackhat • Malware Analyst - Defcon - Shmoocon Bios Colin Ames – Security Researcher, Attack Research – Steganography Research – Penetration Testing – Reverse Engineering – Malware Analysis The Problem THESE GUYS (For Real?) AND THESE GUYS (Who says so?) AND THESE GUYS ? WANT YOUR AND WILL USE YOUR TO GET THEM While this happens you are: I n t r o d u c t i o n Introduction • Attackers are using the web in various ways to: – Push users to their malicious sites – Gain access to computers – Steal information • They use many technologies – Java/Javascript HTML – Iframes Encoding/Obfuscation – Spam Injection Introduction • For this talk we analyzed different types of attacks – Blog Spam – Web site injection • We dissect the attacks piece by piece to analyze and show – Source code Commands – Network traffic Attack Goals – Binaries Attackers Blog Spam • Analysis process – View victim blog, locate malicious comments – Trace back all A HREFs in comments – WGET code from attacker site • Follow any links • Decode obfuscated instructions • Debug javascript – Firebug, Venkman • Decompile Java Applets – Lookup owners of domains / IPs – Reverse any exploits / binaries Blog Spam • 1st Stage of the attack – Uses comments to sites – Blogs such as Drupal & Wordpress • Comments: – Usually in response to valid post – Splice together random but legitimate phrases from sources such as wikipedia – Contain several linked words to various sites – Will be added en mass to many disparate posts – Often will have non-English embedded words such as Italian, German, Russian Shows some comments added to a legitimate post.