Early Detection of Mirai-Like Iot Bots in Large-Scale Networks Through Sub-Sampled Packet Traffic Analysis
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Internet Security Threat Report Volume 24 | February 2019
ISTRInternet Security Threat Report Volume 24 | February 2019 THE DOCUMENT IS PROVIDED “AS IS” AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. SYMANTEC CORPORATION SHALL NOT BE LIABLE FOR INCIDENTAL OR CONSEQUENTIAL DAMAGES IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS DOCUMENT. THE INFORMATION CONTAINED IN THIS DOCUMENT IS SUBJECT TO CHANGE WITHOUT NOTICE. INFORMATION OBTAINED FROM THIRD PARTY SOURCES IS BELIEVED TO BE RELIABLE, BUT IS IN NO WAY GUARANTEED. SECURITY PRODUCTS, TECHNICAL SERVICES, AND ANY OTHER TECHNICAL DATA REFERENCED IN THIS DOCUMENT (“CONTROLLED ITEMS”) ARE SUBJECT TO U.S. EXPORT CONTROL AND SANCTIONS LAWS, REGULATIONS AND REQUIREMENTS, AND MAY BE SUBJECT TO EXPORT OR IMPORT REGULATIONS IN OTHER COUNTRIES. YOU AGREE TO COMPLY STRICTLY WITH THESE LAWS, REGULATIONS AND REQUIREMENTS, AND ACKNOWLEDGE THAT YOU HAVE THE RESPONSIBILITY TO OBTAIN ANY LICENSES, PERMITS OR OTHER APPROVALS THAT MAY BE REQUIRED IN ORDER FOR YOU TO EXPORT, RE-EXPORT, TRANSFER IN COUNTRY OR IMPORT SUCH CONTROLLED ITEMS. TABLE OF CONTENTS 1 2 3 BIG NUMBERS YEAR-IN-REVIEW FACTS AND FIGURES METHODOLOGY Formjacking Messaging Cryptojacking Malware Ransomware Mobile Living off the land Web attacks and supply chain attacks Targeted attacks Targeted attacks IoT Cloud Underground economy IoT Election interference MALICIOUS -

Security Now! #664 - 05-22-18 Spectreng Revealed
Security Now! #664 - 05-22-18 SpectreNG Revealed This week on Security Now! This week we examine the recent flaws discovered in the secure Signal messaging app for desktops, the rise in DNS router hijacking, another seriously flawed consumer router family, Microsoft Spectre patches for Win10's April 2018 feature update, the threat of voice assistant spoofing attacks, the evolving security of HTTP, still more new trouble with GPON routers, Facebook's Android app mistake, BMW's 14 security flaws and some fun miscellany. Then we examine the news of the next-generation of Spectre processor speculation flaws and what they mean for us. Our Picture of the Week Security News Update your Signal Desktop Apps for Windows & Linux A few weeks ago, Argentinian security researchers discovered a severe vulnerability in the Signal messaging app for Windows and Linux desktops that allows remote attackers to execute malicious code on recipient systems simply by sending a message—without requiring any user interaction. The vulnerability was accidentally discovered while researchers–amond them Juliano Rizzo–were chatting on Signal messenger and one of them shared a link of a vulnerable site with an XSS payload in its URL. However, the XSS payload unexpectedly got executed on the Signal desktop app!! (Juliano Rizzo was on the beach when the BEAST and CRIME attacks occurred to him.) After analyzing the scope of this issue by testing multiple XSS payloads, they found that the vulnerability resides in the function responsible for handling shared links, allowing attackers to inject user-defined HTML/JavaScript code via iFrame, image, video and audio tags. -

Internet of Things Botnet Detection Approaches: Analysis and Recommendations for Future Research
applied sciences Systematic Review Internet of Things Botnet Detection Approaches: Analysis and Recommendations for Future Research Majda Wazzan 1,*, Daniyal Algazzawi 2 , Omaima Bamasaq 1, Aiiad Albeshri 1 and Li Cheng 3 1 Computer Science Department, Faculty of Computing and Information Technology, King Abdulaziz University, Jeddah 21589, Saudi Arabia; [email protected] (O.B.); [email protected] (A.A.) 2 Information Systems Department, Faculty of Computing and Information Technology, King Abdulaziz University, Jeddah 21589, Saudi Arabia; [email protected] 3 Xinjiang Technical Institute of Physics & Chemistry Chinese Academy of Sciences, Urumqi 830011, China; [email protected] * Correspondence: [email protected] Abstract: Internet of Things (IoT) is promising technology that brings tremendous benefits if used optimally. At the same time, it has resulted in an increase in cybersecurity risks due to the lack of security for IoT devices. IoT botnets, for instance, have become a critical threat; however, systematic and comprehensive studies analyzing the importance of botnet detection methods are limited in the IoT environment. Thus, this study aimed to identify, assess and provide a thoroughly review of experimental works on the research relevant to the detection of IoT botnets. To accomplish this goal, a systematic literature review (SLR), an effective method, was applied for gathering and critically reviewing research papers. This work employed three research questions on the detection methods used to detect IoT botnets, the botnet phases and the different malicious activity scenarios. The authors analyzed the nominated research and the key methods related to them. The detection Citation: Wazzan, M.; Algazzawi, D.; methods have been classified based on the techniques used, and the authors investigated the botnet Bamasaq, O.; Albeshri, A.; Cheng, L. -

Technical Brief P2P Iot Botnets Clean AC Font
Uncleanable and Unkillable: The Evolution of IoT Botnets Through P2P Networking Technical Brief By Stephen Hilt, Robert McArdle, Fernando Merces, Mayra Rosario, and David Sancho Introduction Peer-to-peer (P2P) networking is a way for computers to connect to one another without the need for a central server. It was originally invented for file sharing, with BitTorrent being the most famous P2P implementation. Decentralized file-sharing systems built on P2P networking have stood the test of time. Even though they have been used to share illegal pirated content for over 20 years, authorities have not been able to put a stop to these systems. Of course, malicious actors have used it for malware for quite a long time as well. Being able to create and manage botnets without the need for a central server is a powerful capability, mostly because law enforcement and security companies typically take down criminal servers. And since a P2P botnet does not need a central command-and-control (C&C) server, it is much more difficult to take down. From the point of view of defenders, this is the scariest problem presented by P2P botnets: If they cannot be taken down centrally, the only option available would be to disinfect each of the bot clients separately. Since computers communicate only with their own peers, the good guys would need to clean all the members one by one for a botnet to disappear. Originally, P2P botnets were implemented in Windows, but developers of internet-of-things (IoT) botnets do have a tendency to start incorporating this feature into their creations. -

Internet Infrastructure Review Vol.34
Internet Infrastructure Review Mar.2017 Vol. 34 Infrastructure Security Ursnif (Gozi) Anti-Analysis Techniques and Methods for Bypassing Them Technology Trends The Current State of Library OSes Internet Infrastructure Review March 2017 Vol.34 Executive Summary ............................................................................................................................ 3 1. Infrastructure Security .................................................................................................................. 4 1.1 Introduction ..................................................................................................................................... 4 1.2 Incident Summary ........................................................................................................................... 4 1.3 Incident Survey ...............................................................................................................................11 1.3.1 DDoS Attacks ...................................................................................................................................11 1.3.2 Malware Activities ......................................................................................................................... 13 1.3.3 SQL Injection Attacks ..................................................................................................................... 17 1.3.4 Website Alterations ....................................................................................................................... -
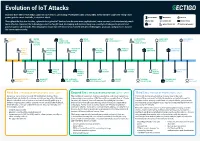
Evolution of Iot Attacks
Evolution of IoT Attacks By 2025, there will be 41.6 billion connected IoT devices, generating 79 zettabytes (ZB) of data (IDC). Every Internet-connected “thing,” from power grids to smart doorbells, is at risk of attack. BLUETOOTH INDUSTRIAL MEDICAL Throughout the last few decades, cyberattacks against IoT devices have become more sophisticated, more common, and unfortunately, much BOTNET GENERIC IOT SMART HOME more effective. However, the technology sector has fought back, developing and implementing new security technologies to prevent and CAR INFRASTRUCTURE WATCH/WEARABLE protect against cyberattacks. This infographic shows how the industry has evolved with new technologies, protocols, and processes to raise the bar on cybersecurity. STUXNET WATER BMW MIRAI FITBIT SAUDI PETROL SILEX LINUX DARK NEXUS VIRUS UTILITY CONNECTED BOTNET VULNERABILITY CHEMICAL MALWARE BOTNET SYSTEM DRIVE SYSTEM PLANT ATTACK (SCADA) PUERTO UNIVERSITY UKRAINIAN HAJIME AMNESIA AMAZON PHILIPS HUE RICO OF MICHIGAN POWER VIGILANTE BOTNET RING HACK LIGHTBULB SMART TRAFFIC GRID BOTNET METERS LIGHTS MEDTRONIC GERMAN TESLA CCTV PERSIRAI FANCY SWEYNTOOTH INSULIN STEEL MODEL S BOTNET BOTNET BEAR VS. FAMILY PUMPS MILL HACK REMOTE SPORTS HACK HACKABLE HEART BASHLITE FIAT CHRYSLER NYADROP SELF- REAPER THINKPHP TWO MILLION KAIJI MONITORS BOTNET REMOTE CONTROL UPDATING MALWARE BOTNET EXPLOITATION TAKEOVER MALWARE First Era | THE AGE OF EXPLORATION | 2005 - 2009 Second Era | THE AGE OF EXPLOITATION | 2011 - 2019 Third Era | THE AGE OF PROTECTION | 2020 Security is not a priority for early IoT/embedded devices. Most The number of connected devices is exploding, and cloud connectivity Connected devices are ubiquitous in every area of life, from cyberattacks are limited to malware and viruses impacting Windows- is becoming commonplace. -

Reporting, and General Mentions Seem to Be in Decline
CYBER THREAT ANALYSIS Return to Normalcy: False Flags and the Decline of International Hacktivism By Insikt Group® CTA-2019-0821 CYBER THREAT ANALYSIS Groups with the trappings of hacktivism have recently dumped Russian and Iranian state security organization records online, although neither have proclaimed themselves to be hacktivists. In addition, hacktivism has taken a back seat in news reporting, and general mentions seem to be in decline. Insikt Group utilized the Recorded FutureⓇ Platform and reports of historical hacktivism events to analyze the shifting targets and players in the hacktivism space. The target audience of this research includes security practitioners whose enterprises may be targets for hacktivism. Executive Summary Hacktivism often brings to mind a loose collective of individuals globally that band together to achieve a common goal. However, Insikt Group research demonstrates that this is a misleading assumption; the hacktivist landscape has consistently included actors reacting to regional events, and has also involved states operating under the guise of hacktivism to achieve geopolitical goals. In the last 10 years, the number of large-scale, international hacking operations most commonly associated with hacktivism has risen astronomically, only to fall off just as dramatically after 2015 and 2016. This constitutes a return to normalcy, in which hacktivist groups are usually small sets of regional actors targeting specific organizations to protest regional events, or nation-state groups operating under the guise of hacktivism. Attack vectors used by hacktivist groups have remained largely consistent from 2010 to 2019, and tooling has assisted actors to conduct larger-scale attacks. However, company defenses have also become significantly better in the last decade, which has likely contributed to the decline in successful hacktivist operations. -

The Tangled Genealogy of Iot Malware
The Tangled Genealogy of IoT Malware Emanuele Cozzi Pierre-Antoine Vervier Matteo Dell’Amico emanuele:cozzi@eurecom:fr France della@linux:it EURECOM France Sophia Antipolis, France Yun Shen Leyla Bilge Davide Balzarotti yun:shen@nortonlifelock:com leylya:yumer@nortonlifelock:com davide:balzarotti@eurecom:fr NortonLifeLock, Inc. NortonLifeLock, Inc. EURECOM Reading, United Kingdom Sophia Antipolis, France Sophia Antipolis, France ABSTRACT 1 INTRODUCTION The recent emergence of consumer off-the-shelf embedded (IoT) Over the last few years we have witnessed an increase in both the devices and the rise of large-scale IoT botnets has dramatically in- volume and sophistication of malware targeting IoT systems. Tra- creased the volume and sophistication of Linux malware observed ditional botnets and DDoS tools now cohabit with crypto-mining, in the wild. The security community has put a lot of effort to docu- spyware, ransomware, and targeted samples designed to conduct ment these threats but analysts mostly rely on manual work, which cyber espionage. To make things worse, the public availability of makes it difficult to scale and hard to regularly maintain. Moreover, the source code associated with some of the main IoT malware the vast amount of code reuse that characterizes IoT malware calls families have paved the way for myriads of variants and tangled for an automated approach to detect similarities and identify the relationships of similarities and code reuse. To make sense of this phylogenetic tree of each family. complex evolution, the security community has devoted a consider- In this paper we present the largest measurement of IoT malware able effort to analyze and document these emerging threats, mostly to date. -

Week 3 Reading Assignment: Understanding the Mirai Botnet
Week 3 Reading Assignment: Understanding the Mirai Botnet Discussion Summary Questions Raised in the Paper: • How could an attacker mine the data available through Spectre attack? • Since the Spectre vulnerability is harder to exploit, it would be interesting to know if this attack has been successfully performed outside of a lab? • Is it possible that Spectre vulnerability is already being taken advantage of, and no one is aware? • What other security problems are embedded in our computers, that we don’t know of? • The released Meltdown and Spectre patches only address issues raised by researches. However, there is a higher probability that one can possibly devise another cache mechanism to trick CPU into reading memory map; as the mechanism is built into the physical memory space. What about those vulnerabilities? Main Take-Aways: About the Attacks: • Meltdown and Spectre vulnerabilities are among the best discoveries in computer science if not the most important • Both vulnerabilities take advantage of a process called speculative execution, where the processor can execute some code in advance and out of order and cache the output, expecting to use that output for the next step in the process. • Using Kernel Page Table Isolation (KPTI) technique, which stops speculation execution by removing mapping kernel into a program when running user space, is one of the current known mitigation techniques to prevent Meltdown. • Noticeable difference between Meltdown and Spectre is the fact that Spectre does not use privilege escalation, thus making the Spectre vulnerability more sophisticated. • “I do not personally consider this a CPU design flaw like Meltdown per se. -

Three Plead Guilty in US to Developing Mirai Botnet
Source: https://internetofbusiness.com/three-plead-guilty-developing-mirai-botnet/ Three plead guilty in US to developing Mirai botnet By Rene Millman - December 18, 2017 Hackers go up before US federal court charged with creating Mirai botnet used in massive DDoS attacks. Three men have pleaded guilty to creating the Mirai IoT botnet, used in distributed denial of service (DDoS) attacks since 2016. A statement released last week by the US Department of Justice, it outlines plea deals and details of the three defendants: Paras Jha, 21, of Fanwood, New Jersey; Josiah White, 20, of Washington, Pennsylvania; and Dalton Norman, 21, of Metairie, Louisiana. The three admitted conspiracy to violate the Computer Fraud & Abuse Act. Jha and Norman also pleaded guilty to building an IoT botnet of 100,000 devices to carry out ‘clickfraud’, an Internet-based scheme that makes it appear that a real user has clicked’ on an advertisement for the purpose of articially generating revenue. In addition, Jha pleaded guilty to a third charge, related to a series of DDoS attacks on the networks of Rutgers University in New Jersey. Read more: Malwar! Hajime IoT botnet ghts back against Mirai Adopted by others The DoJ said the Mirai botnet was created during the summer and autumn of 2016, and went on to compromise 300,000 IoT devices, such as wireless cameras, routers, and digital video recorders. It added that the defendants’ involvement with the original Mirai variant ended in the fall of 2016, when Jha posted its source code on a criminal forum. Since then, other criminal actors have adopted Mirai and used variants in other attacks. -

Identifying and Characterizing Bashlite and Mirai C&C Servers
Identifying and Characterizing Bashlite and Mirai C&C Servers Gabriel Bastos∗, Artur Marzano∗, Osvaldo Fonseca∗, Elverton Fazzion∗y, Cristine Hoepersz, Klaus Steding-Jessenz, Marcelo H. P. C. Chavesz, Italo´ Cunha∗, Dorgival Guedes∗, Wagner Meira Jr.∗ ∗Department of Computer Science – Universidade Federal de Minas Gerais (UFMG) yDepartment of Computing – Universidade Federal de Sao˜ Joao˜ del-Rei (UFSJ) zCERT.br - Brazilian National Computer Emergency Response Team NIC.br - Brazilian Network Information Center Abstract—IoT devices are often a vector for assembling massive which contributes to the rise of a large number of variants. botnets, as a consequence of being broadly available, having Variants exploit other vulnerabilities, include new forms of limited security protections, and significant challenges in deploy- attack, and use different mechanisms to circumvent existing ing software upgrades. Such botnets are usually controlled by centralized Command-and-Control (C&C) servers, which need forms of defense. The increasing number of variants of these to be identified and taken down to mitigate threats. In this paper malwares makes the analysis and reverse engineering process we propose a framework to infer C&C server IP addresses using expensive, hindering the development of countermeasures and four heuristics. Our heuristics employ static and dynamic analysis mitigations. To address the growing number of threats, security to automatically extract information from malware binaries. We analysts and researchers need tools to automate the collection, use active measurements to validate inferences, and demonstrate the efficacy of our framework by identifying and characterizing analysis, and reverse engineering of malware. C&C servers for 62% of 1050 malware binaries collected using The C&C server is a core component of botnets, responsible 47 honeypots. -

Designing an Effective Network Forensic Framework for The
Designing an effective network forensic framework for the investigation of botnets in the Internet of Things Nickolaos Koroniotis A thesis submitted in fulfilment of the requirements for the degree of Doctor of Philosophy School of Engineering and Information Technology The University of New South Wales Australia March 2020 COPYRIGHT STATEMENT ‘I hereby grant the University of New South Wales or its agents a non-exclusive licence to archive and to make available (including to members of the public) my thesis or dissertation in whole or part in the University libraries in all forms of media, now or here after known. I acknowledge that I retain all intellectual property rights which subsist in my thesis or dissertation, such as copyright and patent rights, subject to applicable law. I also retain the right to use all or part of my thesis or dissertation in future works (such as articles or books).’ ‘For any substantial portions of copyright material used in this thesis, written permission for use has been obtained, or the copyright material is removed from the final public version of the thesis.’ Signed ……………………………………………........................... Date …………………………………………….............................. AUTHENTICITY STATEMENT ‘I certify that the Library deposit digital copy is a direct equivalent of the final officially approved version of my thesis.’ Signed ……………………………………………........................... Date …………………………………………….............................. 1 Thesis Dissertation Sheet Surname/Family Name : Koroniotis Given Name/s : Nickolaos Abbreviation for degree : PhD as give in the University calendar Faculty : UNSW Canberra at ADFA School : UC Engineering & Info Tech Thesis Title : Designing an effective network forensic framework for the investigation of botnets in the Internet of Things 2 Abstract 350 words maximum: The emergence of the Internet of Things (IoT), has heralded a new attack surface, where attackers exploit the security weaknesses inherent in smart things.