Ios Security Ios 12.3
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Second Generation of TSMC's Integrated Fan-Out (Info
Apple A11 Application Processor Second generation of TSMC’s inFO packaging PACKAGING report by Stéphane ELISABETH February 2018 – version 1 ©2017 by System Plus Consulting | Apple A11 with TSMC inFO Packaging 1 Table of Contents Overview / Introduction 4 o Application Processor 87 o Executive Summary Die Views, Marking & Dimensions o Reverse Costing Methodology Die Cross-Section Company Profile 8 Die Process Characteristics o Apple Physical Comparison 94 o Apple APE Portfolio o Apple’s APE Series: A9, A10, A11 o Fan-Out Packaging o APE’s PoP Technology: Standard PoP, MCeP, inFO o TSMC inFO Technology Manufacturing Process 98 o Apple iPhone 8 & X Teardown o APE Die Front-End Process & Fabrication Unit o Fan-Out Market o Deep Trench Capacitor Die Front-End Process Flow Physical Analysis 22 & Fabrication Unit o Summary of the Physical Analysis 23 o inFO Packaging Process Flow & Fabrication unit o Packaging 25 Cost Analysis 117 Package Views, Marking & Dimensions o Summary of the cost analysis 118 o Yields Explanation & Hypotheses 119 Package X-Ray o APE die 122 Package RDL Deprocessing Wafer & Die Front-End Cost Package Memory: X-Ray view & Opening Preparation Wafer Cost Package Opening o LSC die 126 Board Cross-Section: Via Frame, PCB, Dimensions Wafer & Die Front-End Cost Package Cross-Section: TiV, Adhesive, RDLs Frond-End cost per Process Steps Package Process o inFO Packaging 131 Summary of Physical Data inFO Wafer Cost o Land-Side Capacitor 65 inFO Front-End Cost per Process Steps Die Views & Dimensions Component Cost Die Deprocessing & Delayering Company services 136 Die Process Die Cross-Section Die Process Characteristics ©2017 by System Plus Consulting | Apple A11 with TSMC inFO Packaging 2 Executive Summary Overview / Introduction o Executive Summary • This full reverse costing study has been conducted to provide insight on technology data, manufacturing cost and selling price of o Reverse Costing Methodology the Apple A11. -

Deploying Ios and Tvos Devices Using Apple Configurator 2 and Jamf Pro
Deploying iOS and tvOS Devices Using Apple Configurator 2 and Jamf Pro Technical Paper Jamf Pro 10.9.0 or Later 7 October 2020 © copyright 2002-2020 Jamf. All rights reserved. Jamf has made all efforts to ensure that this guide is accurate. Jamf 100 Washington Ave S Suite 1100 Minneapolis, MN 55401-2155 (612) 605-6625 Jamf, the Jamf Logo, JAMF SOFTWARE®, and the JAMF SOFTWARE Logo® are registered or common law trademarks of JAMF SOFTWARE, LLC in the U.S. and other countries. Apple, Apple Configurator 2, the Apple logo, Apple TV, iTunes, Mac, macOS, OS X, and tvOS are trademarks of Apple Inc., registered in the United States and other countries. IOS is a trademark or registered trademark of Cisco in the U.S. and other countries. All other product and service names mentioned herein are either registered trademarks or trademarks of their respective companies. Contents Contents 4 Introduction 4 What's in This Guide 4 Additional Resources 5 Choosing a Deployment Method 6 Supervision Identities 6 Use a Supervision Identity from Apple Configurator 2 7 Create and Use a Supervision Identity from Jamf Pro 8 Automated Enrollment 8 Requirements 8 Deploying Devices Using Automated Enrollment 11 Manual Enrollment with an Enrollment URL 11 Requirements 11 Deploy Devices Using Manual Enrollment with an Enrollment URL 13 Further Considerations 14 Manual Enrollment with an Enrollment Profile 14 Requirements 14 Create an Enrollment Profile 14 Create and Upload the Supervision Identity 14 Create the "Prepare" Blueprint 15 Create the "Enroll" Blueprint 15 Deploy Devices Using Manual Enrollment with an Enrollment Profile 3 Introduction What's in This Guide This guide provides step-by-step instructions for deploying iOS and tvOS devices using Apple Configurator 2 and Jamf Pro. -

Initial Setup of Your IOS Device
1. When you first turn on your iOS device, you'll see a screen displaying Hello in different languages. Slide from left to right anywhere on this screen. 2. Select the language you want your iOS device to use, and then the region in which you'll be using your iOS device. This will affect things such as date, time, and contact formatting. 3. Your iOS device requires an Internet connection to set up. Tap the name of your desired Wi-Fi network to begin device activation. § If you're activating an iPhone or iPad (Wi-Fi + Cellular) with active cellular service, you can instead choose cellular activation. 4. Choose whether to enable Location Services. 5. Set up your iPhone as a new device, from an iCloud backup, or from an iTunes backup. § If restoring from backup, you can learn how to restore your content. 6. Sign in with your Apple ID, which you've created previously, or create a free Apple ID. § Alternatively, you can tap Skip This Step to sign in or create an Apple ID later. § If necessary, learn how to create a free Apple ID: 1. Select your birthday, then tap Next: 2. Enter your first and last name, then tap Next: 3. You can then use either your current email address, or choose to get a free iCloud email address. Select the option you'd like, then tap Next. 4. Enter your current email address, or what you'd like for your iCloud email, then tap Next. 5. Enter what you'd like for your password and tap Next. -
Protect Yourself and Your Personal Information*
CYBER SAFETY Protect yourself and your personal information * Cybercrime is a growing and serious threat, making it essential that fraud prevention is part of our daily activities. Put these safeguards in place as soon as possible—if you haven’t already. Email Public Wi-Fi/hotspots Key Use separate email accounts: one each Minimize the use of unsecured, public networks CYBER SAFETY for work, personal use, user IDs, alerts Turn oF auto connect to non-preferred networks 10 notifications, other interests Tips Turn oF file sharing Choose a reputable email provider that oFers spam filtering and multi-factor authentication When public Wi-Fi cannot be avoided, use a 1 Create separate email accounts virtual private network (VPN) to help secure your for work, personal use, alert Use secure messaging tools when replying session to verified requests for financial or personal notifications and other interests information Disable ad hoc networking, which allows direct computer-to-computer transmissions Encrypt important files before emailing them 2 Be cautious of clicking on links or Never use public Wi-Fi to enter personal attachments sent to you in emails Do not open emails from unknown senders credentials on a website; hackers can capture Passwords your keystrokes 3 Use secure messaging tools when Create complex passwords that are at least 10 Home networks transmitting sensitive information characters; use a mix of numbers, upper- and Create one network for you, another for guests via email or text message lowercase letters and special characters and children -

5Tips for Securing Your Mobile Device for Telehealth
Tips for Securing your Mobile Device 5for Telehealth The Health Insurance Portability and Accountability Act (HIPAA) requires that providers protect your information and not share it without your permission. Telehealth providers are required by law to secure medical information that can be shared electronically by encrypting messages and adding other safeguards into the software they use. However, patients’ devices on the receiving end of care often do not always have these safeguards while some medical devices have been shown to be vulnerable to hackers. It is therefore the responsibility of the patient to secure personal devices. 01 Use a PIN or Passcode to secure device Securing your mobile device is important for ensuring that others do not have access to your confidential information and applications. To protect your iPad, iPhone, Android phone you need to set a passcode. It is a 4- to 6-digit PIN used to grant access to the device, like the code you use for an ATM bank card or a debit card. Securing your Apple (iPhone and iPad) and Android devices In addition to allowing you to secure your phone with a passcode, Newer Apple and Android devices also use biometrics called Touch ID and Face ID on Apple, and Face recognition, Irises, and Fingerprints on some Android devices. These tools use your Face, eyes, and fingerprints as unique identifiers to help secure your devices. Face ID and Face recognition use your facial features in order to unlock your device. Touch ID, which is no longer being used on newer versions of iPhone and iPad, and Fingerprints on Android is a fingerprinting tool. -

Implementation and Analysis of Key Reinstallation Attack
International Journal of Innovations in Engineering and Technology (IJIET) http://dx.doi.org/10.21172/ijiet.133.21 Implementation and Analysis of Key Reinstallation Attack Saba Khanum1, Ishita kalra2 1Department of Information Technology, MSIT, Janakpuri, New Delhi, India 2Department of Computer Science and Engineering, MSIT, Janakpuri, New Delhi, India Abstract- The objective of the paper is to implement and analyzed the impact of Key Reinstallation Attack (popularly dubbed as KRACK) on debian based machines. The paper elucidates on the capture of packets through the attack without being a part of the network and affecting the target machines with the help of an attack machine placed inside the network. It basically exploits the nonce of the network which ultimately paves way to the execution of the attack. The issue tends to gather more eyeballs as it affects all devices using Wi-Fi through WPA2 protocol. Hence, the catastrophe complimented along the attack is severe. The analysis of the impact is carried on by analyzing the type of packets visible as well as captured during the course of the implementation. Here, we have created a python script which identifies whether the targeted machine is vulnerable to KRACK or not and corresponding to that the packet capture starts and ultimately, the impact is measured. Keywords – KRACK, weakness, WPA2, attack, security I. INTRODUCTION The presence of the bug has been detected in the cryptographic nonce of the WPA2 and can be used to clone a connected party to reinstall a used key. The presence of the nonce is specifically intended to prevent reuse, but in this particular case, it gives malicious users the opportunity to replay, decrypt, or forge packets, ultimately enabling them to access all previously considered encrypted information without actually being part of the network. -

Laptop Policy, Procedures and Information
MacBook Computer Manual Procedures and Information Brandon Valley High School Brandon, South Dakota Brandon Valley High School MacBook Air Computer Program The Brandon Valley High School staff has been having on-going discussions about how we can move our school forward to better serve our students. As a staff, we feel that it is important to constantly be looking for ways to improve the educational experience for our students to help prepare them for their next step. Though we have been very successful in the past, based on certain indicators, it is key to the success of our future students that we continue to adapt, adjust, and innovate to meet the changing needs of our students in and out of the classroom. Based on this premise, the BVHS staff is excited to launch a learning initiative, iInvest, to begin with the 2016-2017 School Year. Providing all students with 24-7 access to computers is a major component of the iInvest Intiaitive. We believe that the use of the computers and access to available technology, integrated throughout our program of instruction, will help prepare students for their future. The use of technology will allow our students to collect, analyze, consider and communicate ideas and information from an enormous pool of available resources. Through effective planning, our staff will guide students in the analysis, synthesis and evaluation of this vast store of information and help them apply it to complex and practical real-world problems in the classroom. Through the use of the Mac Book Air computers, the teaching and learning process will change over time with students assuming more responsibility for their learning and teachers becoming coaches in the classroom rather than dispensers of knowledge. -
Everything You Need to Know About Apple File System for Macos
WHITE PAPER Everything you need to know about Apple File System for macOS Picture it: the ship date for macOS High Sierra has arrived. Sweat drips down your face; your hands shake as you push “upgrade.” How did I get here? What will happen to my policies? Is imaging dead? Fear not, because the move from HFS+ (the current Mac file system) to Apple File System (APFS) with macOS High Sierra is a good thing. And, with this handy guide, you’ll have everything you need to prepare your environment. In short, don’t fear APFS. To see how Jamf Pro can facilitate seamless macOS High Sierra upgrades in your environment, visit: www.jamf.com • After upgrading to macOS High Sierra, end users will Wait, how did we get here? likely see less total space consumed on a volume due to new cloning options. Bonus: End users can store HFS, and the little known MFS, were introduced in 1984 up to nine quintillion files on a single volume. with the original Macintosh. Fast forward 13 years, and • APFS provides us with a new feature called HFS+ served as a major file system upgrade for the Mac. snapshots. Snapshots make backups work more In fact, it was such a robust file system that it’s been the efficiently and offer a new way to revert changes primary file system on Apple devices. That is all about to back to a given point in time. As snapshots evolve change with APFS. and APIs become available, third-party vendors will Nineteen years after HFS+ was rolled out, Apple be able to build new workflows using this feature. -

Legal-Process Guidelines for Law Enforcement
Legal Process Guidelines Government & Law Enforcement within the United States These guidelines are provided for use by government and law enforcement agencies within the United States when seeking information from Apple Inc. (“Apple”) about customers of Apple’s devices, products and services. Apple will update these Guidelines as necessary. All other requests for information regarding Apple customers, including customer questions about information disclosure, should be directed to https://www.apple.com/privacy/contact/. These Guidelines do not apply to requests made by government and law enforcement agencies outside the United States to Apple’s relevant local entities. For government and law enforcement information requests, Apple complies with the laws pertaining to global entities that control our data and we provide details as legally required. For all requests from government and law enforcement agencies within the United States for content, with the exception of emergency circumstances (defined in the Electronic Communications Privacy Act 1986, as amended), Apple will only provide content in response to a search issued upon a showing of probable cause, or customer consent. All requests from government and law enforcement agencies outside of the United States for content, with the exception of emergency circumstances (defined below in Emergency Requests), must comply with applicable laws, including the United States Electronic Communications Privacy Act (ECPA). A request under a Mutual Legal Assistance Treaty or the Clarifying Lawful Overseas Use of Data Act (“CLOUD Act”) is in compliance with ECPA. Apple will provide customer content, as it exists in the customer’s account, only in response to such legally valid process. -
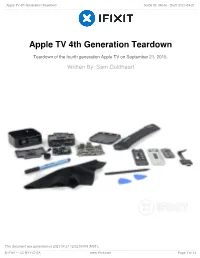
Apple TV 4Th Generation Teardown Guide ID: 49046 - Draft: 2021-04-21
Apple TV 4th Generation Teardown Guide ID: 49046 - Draft: 2021-04-21 Apple TV 4th Generation Teardown Teardown of the fourth generation Apple TV on September 21, 2015. Written By: Sam Goldheart This document was generated on 2021-04-21 12:02:09 PM (MST). © iFixit — CC BY-NC-SA www.iFixit.com Page 1 of 14 Apple TV 4th Generation Teardown Guide ID: 49046 - Draft: 2021-04-21 INTRODUCTION Apple fans are doing the happy dance, what with a slew of new devices coming out of Cupertino— including the first new Apple TV in more than three years. Our teardown engineers look pretty happy too. That's because we've got our hands on a 4th generation Apple TV. That's right, kids. It's teardown time! Don't touch that dial—unless you're looking for more teardown news on our Facebook, Instagram, or Twitter. [video: https://www.youtube.com/watch?v=lSA8uFwptJc] TOOLS: iFixit Opening Picks set of 6 (1) Spudger (1) T7 Torx Screwdriver (1) T3 Torx Screwdriver (1) This document was generated on 2021-04-21 12:02:09 PM (MST). © iFixit — CC BY-NC-SA www.iFixit.com Page 2 of 14 Apple TV 4th Generation Teardown Guide ID: 49046 - Draft: 2021-04-21 Step 1 — Apple TV 4th Generation Teardown We like to start with some specs, and in this case a lot of the good stuff is packed into the fancypants new remote. The box itself contains: Dual-core, 64-bit Apple A8 chip Ethernet, 802.11a/b/g/n/ac Wi-Fi, IR receiver, and HDMI 1.4 connectivity ...whilst the remote is packing: Glass Touch surface Dual microphones Accelerometer and gyroscope Bluetooth 4.0, IR transmitter, Lightning connector This document was generated on 2021-04-21 12:02:09 PM (MST). -

TSMC Integrated Fan-Out (Info) Package Apple A10
Electronic Costing & Technology Experts 21 rue la Nouë Bras de Fer 44200 Nantes – France Phone : +33 (0) 240 180 916 email : [email protected] www.systemplus.fr September 2016 – Version 1 – Written by Stéphane ELISABETH DISCLAIMER : System Plus Consulting provides cost studies based on its knowledge of the manufacturing and selling prices of electronic components and systems. The given values are realistic estimates which do not bind System Plus Consulting nor the manufacturers quoted in the report. System Plus Consulting is in no case responsible for the consequences related to the use which is made of the contents of this report. The quoted trademarks are property of their owners. © 2016 by SYSTEM PLUS CONSULTING, all rights reserved. 1 Return to TOC Glossary 1. Overview / Introduction 4 – A10 Die Analysis 57 – Executive Summary – A10 Die View, Dimensions & Marking – Reverse Costing Methodology – A10 Die Cross-Section – A10 Die Process Characteristics 2. Company Profile 7 – Comparison with previous generation 65 – Apple Inc. – A9 vs. A10 PoP – Apple Series Application processor – A9 vs. A10 Process – Fan-Out Packaging – TSMC Port-Folio 4. Manufacturing Process Flow 70 – TSMC inFO packaging – Chip Fabrication Unit – Packaging Fabrication Unit 3. Physical Analysis 15 – inFO Reconstitution Flow – Physical Analysis Methodology – iPhone 7 Plus Teardown 17 5. Cost Analysis 81 – A10 Die removal – Synthesis of the cost analysis – A10 Package-on-Package Analysis 23 – Main steps of economic analysis – A10 Package View, Dimensions – Yields Hypotheses – A10 Package XRay View – Die Cost Analysis 86 – A10 Package Opening – Wafer Cost – A10 Package Marking – Die Cost – A10 Package Cross-Section – inFO Packaging Cost Analysis 90 – A10 Package Cross-Section – Adhesive & Passivation – Packaging Wafer Cost – A10 package cross-Section - TIVs – Packaging Cost per process Steps – A10 package cross-Section – Solder Balls – Component Cost – A10 package cross-Section – RDL – Land-Side Decoupling Capacitor Analysis 48 6. -
Episode Engine User’S Guide
Note on License The accompanying Software is licensed and may not be distributed without writ- ten permission. Disclaimer The contents of this document are subject to revision without notice due to con- tinued progress in methodology, design, and manufacturing. Telestream shall have no liability for any error or damages of any kind resulting from the use of this doc- ument and/or software. The Software may contain errors and is not designed or intended for use in on-line facilities, aircraft navigation or communications systems, air traffic control, direct life support machines, or weapons systems (“High Risk Activities”) in which the failure of the Software would lead directly to death, personal injury or severe physical or environmental damage. You represent and warrant to Telestream that you will not use, distribute, or license the Software for High Risk Activities. Export Regulations. Software, including technical data, is subject to Swedish export control laws, and its associated regulations, and may be subject to export or import regulations in other countries. You agree to comply strictly with all such regulations and acknowledge that you have the responsibility to obtain licenses to export, re-export, or import Software. Copyright Statement ©Telestream, Inc, 2010 All rights reserved. No part of this document may be copied or distributed. This document is part of the software product and, as such, is part of the license agreement governing the software. So are any other parts of the software product, such as packaging and distribution media. The information in this document may be changed without prior notice and does not represent a commitment on the part of Telestream.