Nessus, Snort, & Ethereal Power Tools
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Overlaymeter: Robust System-Wide Monitoring and Capacity-Based Search in Peer-To-Peer Networks
OverlayMeter: Robust System-wide Monitoring and Capacity-based Search in Peer-to-Peer Networks Inaugural-Dissertation zur Erlangung des Doktorgrades der Mathematisch-Naturwissenschaftlichen Fakultät der Heinrich-Heine-Universität Düsseldorf vorgelegt von Andreas Disterhöft aus Duschanbe in Tadschikistan Düsseldorf, März 2018 aus dem Institut für Informatik der Heinrich-Heine-Universität Düsseldorf Gedruckt mit der Genehmigung der Mathematisch-Naturwissenschaftlichen Fakultät der Heinrich-Heine-Universität Düsseldorf Berichterstatter: 1. Jun.-Prof. Dr.-Ing. Kalman Graffi 2. Prof. Dr. Michael Schöttner Tag der mündlichen Prüfung: 24.09.2018 Abstract In the last decade many peer-to-peer research activities have taken place. Applications using the peer-to-peer paradigm are present and their traffic, depending on the region, accounts fora significant proportion of the total traffic on the Internet. The defined goal of the systemsisto deliver a certain quality of service, which is a challenge in decentralized systems. This is due to the fact that participants have to make decisions based on their locally available information. In order to make the best decisions, a solid and extensive data basis is indispensable. For this purpose the literature on the field of p2p networks proposes monitoring the system, an approach that we follow in this work. Monitoring refers to the gathering and dissemination of system- and peer-specific data. This dissertation deals with open research questions for the improvement and extension of monitoring approaches. Furthermore, issues to simplify procedures for putting such peer-to-peer systems into operation are addressed in this work. In the first part we deal with monitoring procedures in the system-specific context. -

Adaptive Distributed Firewall Using Intrusion Detection Lars Strand
UNIVERSITY OF OSLO Department of Informatics Adaptive distributed firewall using intrusion detection Lars Strand UniK University Graduate Center University of Oslo lars (at) unik no 1. November 2004 ABSTRACT Conventional firewalls rely on a strict outside/inside topology where the gateway(s) enforce some sort of traffic filtering. Some claims that with the evolving connectivity of the Internet, the tradi- tional firewall has been obsolete. High speed links, dynamic topology, end-to-end encryption, threat from internal users are all issues that must be addressed. Steven M. Bellovin was the first to propose a “distributed firewall” that addresses these shortcomings. In this master thesis, the design and implementation of a “distributed firewall” with an intrusion detection mechanism is presented using Python and a scriptable firewall (IPTables, IPFW, netsh). PREFACE This thesis is written as a part of my master degree in Computer Science at the University of Oslo, Department of Informatics. The thesis is written at the Norwegian Defence Research Establishment (FFI). Scripting has been one of my favourite activities since I first learned it. Combined with the art of Computer Security, which I find fascinating and non-exhaustive, it had to be an explosive combina- tion. My problem next was to find someone to supervise me. This is where Professor Hans Petter Langtangen at Simula Research Laboratory and Geir Hallingstad, researcher at FFI, stepped in. Hans Petter Langtangen is a masterful scripting guru and truly deserves the title “Hacker”. Geir Hallingstad is expert in the field of computer/network security and gave valuable input and support when designing this prototype. -

Addressing Contents
IPv4 - Wikipedia, the free encyclopedia Página 1 de 12 IPv4 From Wikipedia, the free encyclopedia The five-layer TCP/IP model Internet Protocol version 4 is the fourth iteration of 5. Application layer the Internet Protocol (IP) and it is the first version of the protocol to be widely deployed. IPv4 is the dominant DHCP · DNS · FTP · Gopher · HTTP · network layer protocol on the Internet and apart from IMAP4 · IRC · NNTP · XMPP · POP3 · IPv6 it is the only standard internetwork-layer protocol SIP · SMTP · SNMP · SSH · TELNET · used on the Internet. RPC · RTCP · RTSP · TLS · SDP · It is described in IETF RFC 791 (September 1981) SOAP · GTP · STUN · NTP · (more) which made obsolete RFC 760 (January 1980). The 4. Transport layer United States Department of Defense also standardized TCP · UDP · DCCP · SCTP · RTP · it as MIL-STD-1777. RSVP · IGMP · (more) 3. Network/Internet layer IPv4 is a data-oriented protocol to be used on a packet IP (IPv4 · IPv6) · OSPF · IS-IS · BGP · switched internetwork (e.g., Ethernet). It is a best effort IPsec · ARP · RARP · RIP · ICMP · protocol in that it does not guarantee delivery. It does ICMPv6 · (more) not make any guarantees on the correctness of the data; 2. Data link layer It may result in duplicated packets and/or packets out- 802.11 · 802.16 · Wi-Fi · WiMAX · of-order. These aspects are addressed by an upper layer ATM · DTM · Token ring · Ethernet · protocol (e.g., TCP, and partly by UDP). FDDI · Frame Relay · GPRS · EVDO · HSPA · HDLC · PPP · PPTP · L2TP · Contents ISDN · (more) 1. Physical layer -
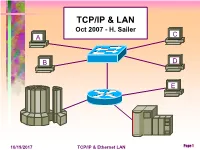
Ethernet and TCP/IP Presentation
TCP/IP & LAN Oct 2007 - H. Sailer A C B D E 10/19/2017 TCP/IP & Ethernet LAN Page 1 TCP/IP illustrated, Vol 1 • Muddle though the book, chapter by chap • General Internet backbone design • Domain Name System • IXIA box demonstration • Configuration of Cisco 2950 Lan switch • IP Subnetwork address • Autonomous System, BGP • IP L3 Routers • TCP layer 4 10/19/2017 TCP/IP & Ethernet LAN Page 2 Where to go for more info • IETF - Internet Engineering Task Force - www.ietf.org • Wikipedia - an online encylopedia – www.wikipedia.org http://en.wikipedia.org/wiki/Tcp/ip • ATM, Frame Relay, MPLS - http://www.mfaforum.org/ • http://www.cisco.com/univercd/cc/td/doc/cisintwk/ • http://www.cisco.com/univercd/home/home.htm • http://www.bgp4.as/ Border Gateway Protocol Stuff • http://www.iol.unh.edu/ University of New Hampshire • http://williamstallings.com/ Great author of TCP books • http://lw.pennnet.com/home.cfm Lightwave Magazine • http://www.ethernetalliance.org/home • http://www.kegel.com Dan Kegel Networking Guru • http://www.ethermanage.com/ethernet/ethernet.html • http://www.tcpipguide.com/index.htm 10/19/2017 TCP/IP & Ethernet LAN Page 3 47% of adults have broadband at home 10/19/2017 TCP/IP & Ethernet LAN Page 4 10/19/2017 TCP/IP & Ethernet LAN Page 5 10/19/2017 TCP/IP & Ethernet LAN Page 6 10/19/2017 TCP/IP & Ethernet LAN Page 7 The Internet Where do IP address Society come from? ( non-profit ) www.isoc.org Internet Internet Internet Architecture Engineering Corporation Board Task Force Assigned IAB IETF Names & Numbers www.iab.org www.ietf.org www.icann.org 10/19/2017 TCP/IP & Ethernet LAN Page 8 • Internet Society - provides a corporate governance to oversee the operation of individual groups, to accept input from outside, and delegate on policy issues. -

Pathspider Documentation Release 2.0
PATHspider Documentation Release 2.0 the pathspider authors Jan 19, 2018 Contents 1 Table of Contents 3 1.1 Introduction...............................................3 1.2 Installation................................................5 1.3 Command Line Usage Overview....................................6 1.4 Active Measurement Plugins.......................................9 1.5 Passive Observation........................................... 18 1.6 Resolving Target Lists.......................................... 30 1.7 Developing Plugins............................................ 31 1.8 PATHspider Internals........................................... 40 1.9 References................................................ 45 2 Citing PATHspider 47 3 Acknowledgements 49 Bibliography 51 Python Module Index 53 i ii PATHspider Documentation, Release 2.0 In today’s Internet we see an increasing deployment of middleboxes. While middleboxes provide in-network func- tionality that is necessary to keep networks manageable and economically viable, any packet mangling — whether essential for the needed functionality or accidental as an unwanted side effect — makes it more and more difficult to deploy new protocols or extensions of existing protocols. For the evolution of the protocol stack, it is important to know which network impairments exist and potentially need to be worked around. While classical network measurement tools are often focused on absolute performance values, PATHspider performs A/B testing between two different protocols or different protocol -

An Introduction to Computer Networks (Week 4) Stanford Univ CS144 Fall 2012
An Introduction to Computer Networks (week 4) Stanford Univ CS144 Fall 2012 PDF generated using the open source mwlib toolkit. See http://code.pediapress.com/ for more information. PDF generated at: Thu, 11 Oct 2012 19:28:39 UTC Contents Articles Names and addresses 1 Address Resolution Protocol 1 Dynamic Host Configuration Protocol 6 Domain Name System 18 IPv4 31 IPv6 41 Network address translation 54 Ebooks Dedicated to Richard Beckett 64 References Article Sources and Contributors 65 Image Sources, Licenses and Contributors 67 Article Licenses License 68 1 Names and addresses Address Resolution Protocol Address Resolution Protocol (ARP) is a telecommunications protocol used for resolution of network layer addresses into link layer addresses, a critical function in multiple-access networks. ARP was defined by RFC 826 in 1982.[1] It is Internet Standard STD 37. It is also the name of the program for manipulating these addresses in most operating systems. ARP has been implemented in many combinations of network and overlaying internetwork technologies, such as IPv4, Chaosnet, DECnet and Xerox PARC Universal Packet (PUP) using IEEE 802 standards, FDDI, X.25, Frame Relay and Asynchronous Transfer Mode (ATM), IPv4 over IEEE 802.3 and IEEE 802.11 being the most common cases. In Internet Protocol Version 6 (IPv6) networks, the functionality of ARP is provided by the Neighbor Discovery Protocol (NDP). Operating scope The Address Resolution Protocol is a request and reply protocol that runs encapsulated by the line protocol. It is communicated within the boundaries of a single network, never routed across internetwork nodes. This property places ARP into the Link Layer of the Internet Protocol Suite, while in the Open Systems Interconnection (OSI) model, it is often described as residing between Layers 2 and 3, being encapsulated by Layer 2 protocols. -

XMPP: the Definitive Guide Download at Boykma.Com XMPP: the Definitive Guide Building Real-Time Applications with Jabber Technologies
XMPP: The Definitive Guide Download at Boykma.Com XMPP: The Definitive Guide Building Real-Time Applications with Jabber Technologies Peter Saint-Andre, Kevin Smith, and Remko Tronçon Beijing • Cambridge • Farnham • Köln • Sebastopol • Taipei • Tokyo Download at Boykma.Com XMPP: The Definitive Guide by Peter Saint-Andre, Kevin Smith, and Remko Tronçon Copyright © 2009 Peter Saint-Andre, Kevin Smith, Remko Tronçon. All rights reserved. Printed in the United States of America. Published by O’Reilly Media, Inc., 1005 Gravenstein Highway North, Sebastopol, CA 95472. O’Reilly books may be purchased for educational, business, or sales promotional use. Online editions are also available for most titles (http://safari.oreilly.com). For more information, contact our corporate/ institutional sales department: (800) 998-9938 or [email protected]. Editor: Mary E. Treseler Indexer: Joe Wizda Production Editor: Loranah Dimant Cover Designer: Karen Montgomery Copyeditor: Genevieve d’Entremont Interior Designer: David Futato Proofreader: Loranah Dimant Illustrator: Robert Romano Printing History: April 2009: First Edition. Nutshell Handbook, the Nutshell Handbook logo, and the O’Reilly logo are registered trademarks of O’Reilly Media, Inc. XMPP: The Definitive Guide, the image of a kanchil mouse deer on the cover, and related trade dress are trademarks of O’Reilly Media, Inc. JABBER® is a registered trademark licensed through the XMPP Standards Foundation. Many of the designations used by manufacturers and sellers to distinguish their products are claimed as trademarks. Where those designations appear in this book, and O’Reilly Media, Inc. was aware of a trademark claim, the designations have been printed in caps or initial caps. While every precaution has been taken in the preparation of this book, the publisher and authors assume no responsibility for errors or omissions, or for damages resulting from the use of the information con- tained herein. -

Security Schemes for the OLSR Protocol for Ad Hoc Networks Daniele Raffo
Security Schemes for the OLSR Protocol for Ad Hoc Networks Daniele Raffo To cite this version: Daniele Raffo. Security Schemes for the OLSR Protocol for Ad Hoc Networks. Networking and Internet Architecture [cs.NI]. Université Pierre et Marie Curie - Paris VI, 2005. English. tel-00010678 HAL Id: tel-00010678 https://tel.archives-ouvertes.fr/tel-00010678 Submitted on 18 Oct 2005 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. THÈSE DE DOCTORAT DE L’UNIVERSITÉ PARIS 6 – PIERRE ET MARIE CURIE discussed by Daniele Raffo on September 15, 2005 to obtain the degree of Docteur de l’Université Paris 6 Discipline: Computer Science Host laboratory: INRIA Rocquencourt Security Schemes for the OLSR Protocol for Ad Hoc Networks Thesis Director: Dr. Paul Mühlethaler Jury Reviewers: Dr. Ana Cavalli Institut National des Télécommunications Dr. Ahmed Serhrouchni Ecole Nationale Supérieure des Télécommunications Examiners: Dr. François Baccelli Ecole Normale Supérieure Dr. François Morain Ecole Polytechnique Dr. Paul Mühlethaler INRIA Rocquencourt Dr. Guy Pujolle Université Paris 6 Guests: Dr. Daniel Augot INRIA Rocquencourt Dr. Philippe Jacquet INRIA Rocquencourt THÈSE DE DOCTORAT DE L’UNIVERSITÉ PARIS 6 – PIERRE ET MARIE CURIE présentée par Daniele Raffo le 15 Septembre 2005 pour obtenir le grade de Docteur de l’Université Paris 6 Spécialité: Informatique Laboratoire d’accueil: INRIA Rocquencourt Schémas de sécurité pour le protocole OLSR pour les réseaux ad hoc Directeur de Thèse: M. -

Ethernet 95 Link Aggregation 102 Power Over Ethernet 107 Gigabit Ethernet 116 10 Gigabit Ethernet 121 100 Gigabit Ethernet 127
Computer Networking PDF generated using the open source mwlib toolkit. See http://code.pediapress.com/ for more information. PDF generated at: Sat, 10 Dec 2011 02:24:44 UTC Contents Articles Networking 1 Computer networking 1 Computer network 16 Local area network 31 Campus area network 34 Metropolitan area network 35 Wide area network 36 Wi-Fi Hotspot 38 OSI Model 42 OSI model 42 Physical Layer 50 Media Access Control 52 Logical Link Control 54 Data Link Layer 56 Network Layer 60 Transport Layer 62 Session Layer 65 Presentation Layer 67 Application Layer 69 IEEE 802.1 72 IEEE 802.1D 72 Link Layer Discovery Protocol 73 Spanning tree protocol 75 IEEE 802.1p 85 IEEE 802.1Q 86 IEEE 802.1X 89 IEEE 802.3 95 Ethernet 95 Link aggregation 102 Power over Ethernet 107 Gigabit Ethernet 116 10 Gigabit Ethernet 121 100 Gigabit Ethernet 127 Standards 135 IP address 135 Transmission Control Protocol 141 Internet Protocol 158 IPv4 161 IPv4 address exhaustion 172 IPv6 182 Dynamic Host Configuration Protocol 193 Network address translation 202 Simple Network Management Protocol 212 Internet Protocol Suite 219 Internet Control Message Protocol 225 Internet Group Management Protocol 229 Simple Mail Transfer Protocol 232 Internet Message Access Protocol 241 Lightweight Directory Access Protocol 245 Routing 255 Routing 255 Static routing 260 Link-state routing protocol 261 Open Shortest Path First 265 Routing Information Protocol 278 IEEE 802.11 282 IEEE 802.11 282 IEEE 802.11 (legacy mode) 292 IEEE 802.11a-1999 293 IEEE 802.11b-1999 295 IEEE 802.11g-2003 297 -

Hobbes' Internet Timeline - the Definitive Arpanet & Internet History
Hobbes' Internet Timeline - the definitive ARPAnet & Internet history [ 1950s ] [ 1960s ] [ 1970s ] [ 1980s ] [ 1990s ] [ 2000s ] [ Growth ] [ FAQ ] [ Sources ] Hobbes' Internet Timeline v7.0 by Robert H'obbes' Zakon Zakon Group LLC Hobbes' Internet Timeline Copyright (c)1993-2004 by Robert H Zakon. Permission is granted for use of this document in whole or in part for non-commercial purposes as long as this Copyright notice and a link to this document, at the archive listed at the end, is included. A copy of the material the Timeline appears in is requested. For commercial uses, please contact the author first. Links to this document are welcome after e-mailing the author with the document URL where the link will appear. As the Timeline is frequently updated, copies to other locations on the Internet are not permitted. If you enjoy the Timeline or make use of it in some way, please consider a contribution. 1950s 1957 USSR launches Sputnik, first artificial earth satellite. In response, US forms the Advanced Research Projects Agency (ARPA), the following year, within the Department of Defense (DoD) to establish US lead in science and technology applicable to the military (:amk:) 1960s 1961 Leonard Kleinrock, MIT: "Information Flow in Large Communication Nets" (May 31) ❍ First paper on packet-switching (PS) theory 1962 J.C.R. Licklider & W. Clark, MIT: "On-Line Man Computer Communication" (August) ❍ Galactic Network concept encompassing distributed social interactions 1964 Paul Baran, RAND: "On Distributed Communications Networks" ❍ Packet-switching -
![April 20] “It Is Easier to Write an Team with Code for the Still- Incorrect Program Than April 1St Unfinished Computer](https://docslib.b-cdn.net/cover/5050/april-20-it-is-easier-to-write-an-team-with-code-for-the-still-incorrect-program-than-april-1st-unfinished-computer-9215050.webp)
April 20] “It Is Easier to Write an Team with Code for the Still- Incorrect Program Than April 1St Unfinished Computer
Project Whirlwind [April 20] “It is easier to write an team with code for the still- incorrect program than April 1st unfinished computer. understand a correct one.” “You think you KNOW when you learn, are more sure when Léon-Auguste- you can write, even more when you can teach, but Antoine Bollée certain when you can Born: April 1, 1870; Le program.” Mans, France Died: Dec. 16, 1913 Bollée’s Multiplier was the Norman Abramson second (or third) direct- multiplying calculator, which Born: April 1, 1932; (like the others) met with Boston, Massachusetts limited commercial success, Died: Dec. 1, 2020 although it did win a gold medal At the University of Hawaii, at the 1889 Paris Exposition. Alan J. Perlis. (c) 2019 ACM. Abramson led the team that The first commercially developed the ALOHAnet successful direct multiplication In early 1955, Perlis’ team at wireless computer calculator was the Millionaire Purdue began work on the IT communication system. The goal [May 7]. language ("Internal Translator"), was to use low-cost commercial The Multiplier’s main advantage a very early machine- radio equipment to connect was its speed. In 1892, Bollée independent language. This led users on Oahu and the other calculated the square root of an to him becoming the chairman Hawaiian islands with a central 18 digit number in about 30 of the ACM Programming time-sharing computer at the seconds. The same calculation Languages Committee in 1957, main Oahu campus. and a delegate to the Zurich with a more conventional ALOHAnet became operational conference [May 27] where calculator (that used repeated in June 1971, providing the first ALGOL 58 was defined. -

Computer Networks
LECTURE NOTES ON COMPUTER NETWORKS COURSE CODE: AIT003 BRANCH: IT B.Tech IV Semester Mr.N.BHASWANTH ASSISTANT PROFESSOR & Mr. RAHUL ASSISTANT PROFESSOR INFORMATION TECHNOLOGY INSTITUTE OF AERONAUTICAL ENGINEERING (Autonomous) DUNDIGAL, HYDERABAD - 500 043 SYLLABUS UNIT-I INTRODUCTION TO PHYSICAL LAYER Introduction: Networks, network types, internet history, standards and administration; Network models: Protocol layering, TCP/IP protocol suite, the OSI model; Introduction to physical layer: Data and signals, transmission impairment, data rate limits, performance; Transmission media: Introduction, guided media,unguided media; Switching: Introduction, circuit switched networks, packet switching. UNIT-II INTRODUCTION TO DATA LINK LAYER Introduction: Link layer addressing; Error detection and correction: Cyclic codes, checksum, forward error correction; Data link control: DLC services, data link layer protocols, HDLC, point to point protocol, media access control: Random access, controlled access, channelization, connecting devices and virtual LAN: Connecting devices, virtual LAN. UNIT-III THE NETWORK LAYER Network layer design issues, routing algorithms, congestion control algorithms, quality of service, and internetworking. The network layer in the internet: IPv4 addresses, IPv6, internet control protocols, OSPF (Open Shortest Path First), BGP (Border Gateway Protocol), IP, (Internet Protocol), ICMP (internet control message protocol. UNIT-IV THE TRANSPORT LAYER The transport service, elements of transport protocols, congestion control; The internet transport protocols: UDP (User Datagram Protocol), TCP (Transport Control Protocol), performance problems in computer networks, network performance measurement. UNIT-V INTRODUCTION TO APPLICATION LAYER Introduction, client server programming, WWW (World Wide Web) and HTTP (Hyper Text Transfer Protocol), FTP (File Transfer Protocol), E-mail, telnet, secure shell, DNS(Domain Naming System), SNMP (Simple Network Management Protocol).