Google Chrome OS VS Distribuciones GNU/Linux 18
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Google Security Chip H1 a Member of the Titan Family
Google Security Chip H1 A member of the Titan family Chrome OS Use Case [email protected] Block diagram ● ARM SC300 core ● 8kB boot ROM, 64kB SRAM, 512kB Flash ● USB 1.1 slave controller (USB2.0 FS) ● I2C master and slave controllers ● SPI master and slave controllers ● 3 UART channels ● 32 GPIO ports, 28 muxed pins ● 2 Timers ● Reset and power control (RBOX) ● Crypto Engine ● HW Random Number Generator ● RD Detection Flash Memory Layout ● Bootrom not shown ● Flash space split in two halves for redundancy ● Restricted access INFO space ● Header fields control boot flow ● Code is in Chrome OS EC repo*, ○ board files in board/cr50 ○ chip files in chip/g *https://chromium.googlesource.com/chromiumos/platform/ec Image Properties Chip Properties 512 byte space Used as 128 FW Updates INFO Space Bits 128 Bits Bitmap 32 Bit words Board ID 32 Bit words Bitmap Board ID ● Updates over USB or TPM Board ID Board ID ~ Board ID ● Rollback protections Board ID mask Version Board Flags ○ Header versioning scheme Board Flags ○ Flash map bitmap ● Board ID and flags Epoch ● RO public key in ROM Major ● RW public key in RO Minor ● Both ROM and RO allow for Timestamp node locked signatures Major Functions ● Guaranteed Reset ● Battery cutoff ● Closed Case Debugging * ● Verified Boot (TPM Services) ● Support of various security features * https://www.chromium.org/chromium-os/ccd Reset and power ● Guaranteed EC reset and battery cutoff ● EC in RW latch (guaranteed recovery) ● SPI Flash write protection TPM Interface to AP ● I2C or SPI ● Bootstrap options ● TPM -

Chromium OS Audio System
Chromium OS audio CRAS audio server Why another audio server? low end hardware (1 core atom, or Tegra 2) optimize for one user (chrome) dynamic stream re-routing maintainability, code size, security Basic Audio Flow Chromium dbus control Playback/Capture shm CRAS BlueZ ALSA Client Library API int cras_client_create(struct cras_client **client); int cras_client_run_thread(struct cras_client *client); struct cras_stream_params *cras_client_unified_params_create( enum CRAS_STREAM_DIRECTION direction, /* direction - CRAS_STREAM_OUTPUT or CRAS_STREAM_INPUT */ unsigned int block_size, /* block_size - The number of frames per callback(dictates latency). */ enum CRAS_STREAM_TYPE stream_type, /* not currently used */ uint32_t flags, /* not used either. */ void *user_data, /* user_data - Pointer that will be passed to the callback. */ cras_unified_cb_t unified_cb, /* unified_cb - Called for each block size samples */ cras_error_cb_t err_cb, /* err_cb - Called when there is an error with the stream. */ struct cras_audio_format *format); /* format - Specifies bits per sample, num chan, sample rate */ int cras_client_add_stream(struct cras_client *client, cras_stream_id_t *stream_id_out, struct cras_stream_params *config); Server side features Timer Based Wake-ups based on stream level Device Sample Rate Estimation Mixing, DSP, and format conversion Volume level tuning Device synchronization One audio thread Wake up timing Wakes up each stream based on a timer Timer rate set based on block size Adjusted based on estimated device clock Underrun handling -

2Nd USENIX Conference on Web Application Development (Webapps ’11)
conference proceedings Proceedings of the 2nd USENIX Conference Application on Web Development 2nd USENIX Conference on Web Application Development (WebApps ’11) Portland, OR, USA Portland, OR, USA June 15–16, 2011 Sponsored by June 15–16, 2011 © 2011 by The USENIX Association All Rights Reserved This volume is published as a collective work. Rights to individual papers remain with the author or the author’s employer. Permission is granted for the noncommercial reproduction of the complete work for educational or research purposes. Permission is granted to print, primarily for one person’s exclusive use, a single copy of these Proceedings. USENIX acknowledges all trademarks herein. ISBN 978-931971-86-7 USENIX Association Proceedings of the 2nd USENIX Conference on Web Application Development June 15–16, 2011 Portland, OR, USA Conference Organizers Program Chair Armando Fox, University of California, Berkeley Program Committee Adam Barth, Google Inc. Abdur Chowdhury, Twitter Jon Howell, Microsoft Research Collin Jackson, Carnegie Mellon University Bobby Johnson, Facebook Emre Kıcıman, Microsoft Research Michael E. Maximilien, IBM Research Owen O’Malley, Yahoo! Research John Ousterhout, Stanford University Swami Sivasubramanian, Amazon Web Services Geoffrey M. Voelker, University of California, San Diego Nickolai Zeldovich, Massachusetts Institute of Technology The USENIX Association Staff WebApps ’11: 2nd USENIX Conference on Web Application Development June 15–16, 2011 Portland, OR, USA Message from the Program Chair . v Wednesday, June 15 10:30–Noon GuardRails: A Data-Centric Web Application Security Framework . 1 Jonathan Burket, Patrick Mutchler, Michael Weaver, Muzzammil Zaveri, and David Evans, University of Virginia PHP Aspis: Using Partial Taint Tracking to Protect Against Injection Attacks . -

Universidad Carlos III De Madrid - I.T.I.G - Proyecto Fin De Carrera
Universidad Carlos III de Madrid - I.T.I.G - Proyecto Fin de Carrera Universidad Carlos III de Madrid Ingeniería Técnica en Informática de Gestión Proyecto de Fin de Carrera Estudio de la Evolución Web y Lenguajes Dinámicos. Rincón Carrera, Juan Manuel Estudio de la Evolución Web y Lenguajes Dinámicos 1 Juan Manuel Rincón Carrera Universidad Carlos III de Madrid - I.T.I.G - Proyecto Fin de Carrera INDICE 1 Introducción ................................................................................................................................... 3 2 Objetivos ........................................................................................................................................ 4 2.1 Planificación .......................................................................................................................... 4 2.2 Estimación económica ......................................................................................................... 5 3 Requisitos ...................................................................................................................................... 8 3.1 Restricciones globales ......................................................................................................... 8 3.2 Requisitos Funcionales ........................................................................................................ 9 3.3 Requisitos No Funcionales ............................................................................................... 10 3.4 Requisitos técnicos............................................................................................................ -

Towardsweb User-Centric Development Emilian Pascalau
TowardsWeb User-Centric Development Emilian Pascalau To cite this version: Emilian Pascalau. TowardsWeb User-Centric Development. Data Structures and Algorithms [cs.DS]. Conservatoire national des arts et metiers - CNAM, 2014. English. NNT : 2014CNAM0916. tel- 01062263 HAL Id: tel-01062263 https://tel.archives-ouvertes.fr/tel-01062263 Submitted on 9 Sep 2014 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. CONSERVATOIRE NATIONAL DES ARTS ET MÉTIERS ÉCOLE DOCTORALE INFORMATIQUE, TÉLÉCOMMUNICATION ET ÉLECTRONIQUE (EDITE - PARIS) ÉQUIPES VERTIGO - LABORATOIRE CEDRIC THÈSE DE DOCTORAT présentée par : Emilian PASCALAU soutenue le : 7 avril 2014 pour obtenir le grade de : Docteur du Conservatoire National des Arts et Métiers Discipline / Spécialité : Informatique Vers un développement Web orienté utilisateur Towards Web User-Centric Development THÈSE DIRIGÉE PAR M. RIGAUX Philippe PR, CNAM RAPPORTEURS M. GROSS-AMBLARD David PR, Univ. Rennes 1 Mme. GRIGORI Daniela PR, Univ. Paris-Dauphine EXAMINATEURS Mme. BENBERNOU Salima PR, Paris Descartes M. TRAVERS Nicolas MdC, CNAM M. ZAMFIROIU Michel Directeur, KarmicSoft inc. To my parents Emil and Iuliana Aknowledgements I feel obliged to first thank God for the health and strength He gave me through out the years of study. -

Cover V06 Rgb.Cdr
Security, Privacy and Cloud Computing Jose Tomas Robles Hahn Supervisor: Ralph Holz Future Internet Seminar - Winter Term 2010/2011 Chair for Network Architectures and Services Faculty of Computer Science, Technische Universität München Email: [email protected] ABSTRACT crime and terrorism. Cloud computing puts users' data at Cloud computing usage is growing every day as users dis- a higher risk of being accessed by unauthorized individuals, cover its many advantages. However, the move to the cloud since their information is now stored in datacenters which exposes users to new security and privacy threats. We give they do not control. This also allows governments to invade details on cloud-specific vulnerabilities and caveats and show users' privacy by getting their data directly from the cloud some technical ways to address them. We also note that provider, without informing the affected user [2]. users cannot rely on technology alone to completely solve all their problems: how to protect against government surveil- In this article we will discuss the security and privacy risks lance remains an open question. that users face by moving their data to the cloud and show how we can use technology to solve them. We will base our Keywords discussion on Christopher Soghoian's article Caught in the Cloud: Privacy, Encryption, and Government Back Doors Cloud computing, Security, Privacy, Surveillance, Encryp- in the Web 2.0 Era [2]. tion This article is organized as follows: First, in chapter 2 we 1. INTRODUCTION will talk about the definition and characteristics of cloud In the 1980s, the emergence of the personal computer (PC) computing. -

Dell Chromebook 3100 2-In-1 Setup and Specifications
Dell Chromebook 3100 2-in-1 Setup and Specifications October 2020 Rev. A00 Notes, cautions, and warnings NOTE: A NOTE indicates important information that helps you make better use of your product. CAUTION: A CAUTION indicates either potential damage to hardware or loss of data and tells you how to avoid the problem. WARNING: A WARNING indicates a potential for property damage, personal injury, or death. © 2019 - 2020 Dell Inc. or its subsidiaries. All rights reserved. Dell, EMC, and other trademarks are trademarks of Dell Inc. or its subsidiaries. Other trademarks may be trademarks of their respective owners. Contents Chapter 1: Chassis overview.......................................................................................................... 4 Front....................................................................................................................................................................................... 4 Left..........................................................................................................................................................................................4 Right........................................................................................................................................................................................4 Palmrest.................................................................................................................................................................................4 Bottom....................................................................................................................................................................................4 -

HP Chromebook 11 G7 EE
QuickSpecs HP Chromebook 11 G7 EE Overview HP Chromebook 11 G7 EE Left 1. Webcam LED 5. USB-A 3.1 Gen 1 2. Webcam 6. USB-C™ 3.1 Gen 1 (Supporting Power Delivery and Display Port) 3. Internal Microphone 7. Nano Security Lock Slot (Lock sold separately) 4. Touchpad Not all configuration components are available in all regions/countries. Page 1 c06219877 — DA 16397 —Worldwide — Version 5 — December 16, 2020 QuickSpecs HP Chromebook 11 G7 EE Overview Right 1. Power Button 4. USB-A 3.1 Gen 1 2. USB-C™ 3.1 Gen 1 (Supporting Power Delivery and Display 5. Micro SD Card Reader Port) 3. Power LED 6. Stereo Headphone / Microphone Combo Jack Not all configuration components are available in all regions/countries. Page 2 c06219877 — DA 16397 —Worldwide — Version 5 — December 16, 2020 QuickSpecs HP Chromebook 11 G7 EE Overview AT A GLANCE • Latest Intel® Celeron® N4000 and N4100 processors • Designed to pass MIL STD 810G1 test and increased drop height to 76cm drop on concrete3, and enhanced USB-C™ connectors to stand against daily uses of plug and unplug • Long battery life with HP Fast Charge technology to support 90% charge in 90 minutes • Pick proof keyboard to make it harder to pick the keys up • Intel® 2x2 AC WLAN with MIMO for easy connection in dense classroom environment • Choice of up to 8 GB memory and 64 GB eMMc storage • 2 USB-C™ ports for charging, power and data transfer, and 2 USB 3.1 Gen 1 ports for sleep and charge support • Enjoy Android™ Apps on Chrome OS™2 • Your Chromebook boots up within 10 seconds and you can be browsing online and working in Google Apps just moments later 1. -
Test Administrator Remote Testing Faqs
Test Administrator’s FAQs for Remote Testing Administration with Remote Monitoring Remote Testing and Web Meeting Questions Question: Why are remote testing sessions limited to 10-12 students? Answer: Remote testing requires the Test Administrator to manage a web meeting with multiple students, which involves validating credentials and close monitoring all of students in the web meeting. Currently, the number of simultaneous testers is limited to 10-12 students to keep web sessions manageable and more secure. Question: Does DRC provide web conference services? Answer: DRC does not provide web conference services. You need to use a third-party vendor web conferencing solution. Note: Most free or trial versions of web conference services do not provide sufficient functionality to meet remote test administration recommendations. Question: How long are the recordings of remote test sessions retained, and what is recorded? Answer: DRC does not provide, retain, or have access to recordings of remote testing sessions. Recordings are generally stored by the web conferencing service and are used to review testing sessions if any issues or test irregularities are reported locally. What is available for recording, including options and retention policies, varies by web conference service. Your web conference vendor should be able to provide clarification. If there are no issues during the assessment, recordings can be deleted. Question: What do I do if a student is dropped out of a web meeting? Answer: During web meetings, students may encounter technical or Internet problems caused by bandwidth issues in their local environment or by their connection to the Internet. These issues are beyond DRC’s control. -
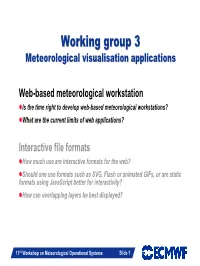
Working Group 3
WorkingWorking groupgroup 33 Meteorological visualisation applications Web-based meteorological workstation zIs the time right to develop web-based meteorological workstations? zWhat are the current limits of web applications? Interactive file formats zHow much use are interactive formats for the web? zShould one use formats such as SVG, Flash or animated GIFs, or are static formats using JavaScript better for interactivity? zHow can overlapping layers be best displayed? Slide 1 11th Workshop on Meteorological Operational Systems Slide 1 What has changed? z Web 2.0 with its (new) emerging technologies opens possibilities to implement new interactivities z More demands on visualisation on the web ÎScalable plots Æ vector graphics ÎInteraction Æselect further information ÎOperational Æ High availability z Fast changing world with high expectation through successful services (e.g. Google, Yahoo) z Cheap hardware might solve the availability issue z Role of forecaster and demands of end-user changed: Slide 2 Information from different fields of science are required 11th Workshop on Meteorological Operational Systems Slide 2 Meteorological user interface Classical desktop Web applications z Many advanced toolkits (e.g. z New emerging user interface APIs GTK, Qt) (e.g. jQuery, YUI) z Lots of tested and optimised z Lots of new developments and code Æ mature development experience needed tools z Different opinions on how heavy/rich z Make use of all system the applications should be resources z Can not use full advantage of local z Platform dependent -

Designing for Extensibility and Planning for Conflict
Designing for Extensibility and Planning for Conflict: Experiments in Web-Browser Design Benjamin S. Lerner A dissertation submitted in partial fulfillment of the requirements for the degree of Doctor of Philosophy University of Washington 2011 Program Authorized to Offer Degree: UW Computer Science & Engineering University of Washington Graduate School This is to certify that I have examined this copy of a doctoral dissertation by Benjamin S. Lerner and have found that it is complete and satisfactory in all respects, and that any and all revisions required by the final examining committee have been made. Chair of the Supervisory Committee: Daniel Grossman Reading Committee: Daniel Grossman Steven Gribble John Zahorjan Date: In presenting this dissertation in partial fulfillment of the requirements for the doctoral degree at the University of Washington, I agree that the Library shall make its copies freely available for inspection. I further agree that extensive copying of this dissertation is allowable only for scholarly purposes, consistent with “fair use” as prescribed in the U.S. Copyright Law. Requests for copying or reproduction of this dissertation may be referred to Proquest Information and Learning, 300 North Zeeb Road, Ann Arbor, MI 48106-1346, 1-800-521-0600, to whom the author has granted “the right to reproduce and sell (a) copies of the manuscript in microform and/or (b) printed copies of the manuscript made from microform.” Signature Date University of Washington Abstract Designing for Extensibility and Planning for Conflict: Experiments in Web-Browser Design Benjamin S. Lerner Chair of the Supervisory Committee: Associate Professor Daniel Grossman UW Computer Science & Engineering The past few years have seen a growing trend in application development toward “web ap- plications”, a fuzzy category of programs that currently (but not necessarily) run within web browsers, that rely heavily on network servers for data storage, and that are developed and de- ployed differently from traditional desktop applications. -

Harnessing Collective Intelligence for the Learning Communities; a Review of Web 2.0 and Social Computing Technologies
Journal of Computer Science and Information Technology June 2014, Vol. 2, No. 2, pp. 111-129 ISSN: 2334-2366 (Print), 2334-2374 (Online) Copyright © The Author(s). 2014. All Rights Reserved. Published by American Research Institute for Policy Development Harnessing Collective Intelligence for the Learning Communities; a Review of Web 2.0 and Social Computing Technologies R. K. Sungkur1 and D. Rungen1 Abstract Web 2.0 and Social Computing is based upon the knowledge of connecting people globally using adequate technologies to increase people interaction. Technology has always played a key role for innovation in education, and with the advent of Web 2.0 and social computing, educators have been quick in recognizing the great potential that this represents. There has been a dramatic shift of information power and everything is decentralized, participatory and collaborative. Properly filtering and harnessing ‘user-generated content’ in web 2.0 and social computing can represent a valuable repository of knowledge for the learning communities. Nowadays, the number of people accessing social websites is rising exponentially and educators are seriously contemplating the option of using these social websites to reach the learners, especially youngsters. The Facebook phenomenon is particularly true in this situation where we find many learners sharing notes, uploading learning materials, discussing on a particular topic related to learning and education. So in a way, we find that these social websites are no longer being used only for entertainment but also for learning purposes. This is limited not only to Facebook. So many social websites together with the accompanying web 2.0 tools and features if properly used, can represent an interesting repository of knowledge.