FROM GSM to LTE-ADVANCED Trim Size: 170Mm X 244Mm Sauter Ffirs.Tex V2 - 06/06/2014 1:55 P.M
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
NEXT GENERATION MOBILE WIRELESS NETWORKS: 5G CELLULAR INFRASTRUCTURE JULY-SEPT 2020 the Journal of Technology, Management, and Applied Engineering
VOLUME 36, NUMBER 3 July-September 2020 Article Page 2 References Page 17 Next Generation Mobile Wireless Networks: Authors Dr. Rendong Bai 5G Cellular Infrastructure Associate Professor Dept. of Applied Engineering & Technology Eastern Kentucky University Dr. Vigs Chandra Professor and Coordinator Cyber Systems Technology Programs Dept. of Applied Engineering & Technology Eastern Kentucky University Dr. Ray Richardson Professor Dept. of Applied Engineering & Technology Eastern Kentucky University Dr. Peter Ping Liu Professor and Interim Chair School of Technology Eastern Illinois University Keywords: The Journal of Technology, Management, and Applied Engineering© is an official Mobile Networks; 5G Wireless; Internet of Things; publication of the Association of Technology, Management, and Applied Millimeter Waves; Beamforming; Small Cells; Wi-Fi 6 Engineering, Copyright 2020 ATMAE 701 Exposition Place Suite 206 SUBMITTED FOR PEER – REFEREED Raleigh, NC 27615 www. atmae.org JULY-SEPT 2020 The Journal of Technology, Management, and Applied Engineering Next Generation Mobile Wireless Networks: Dr. Rendong Bai is an Associate 5G Cellular Infrastructure Professor in the Department of Applied Engineering and Technology at Eastern Kentucky University. From 2008 to 2018, ABSTRACT he served as an Assistant/ The requirement for wireless network speed and capacity is growing dramatically. A significant amount Associate Professor at Eastern of data will be mobile and transmitted among phones and Internet of things (IoT) devices. The current Illinois University. He received 4G wireless technology provides reasonably high data rates and video streaming capabilities. However, his B.S. degree in aircraft the incremental improvements on current 4G networks will not satisfy the ever-growing demands of manufacturing engineering users and applications. -
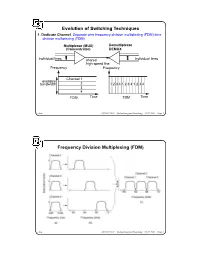
Evolution of Switching Techniques Frequency Division Multiplexing
Evolution of Switching Techniques 1. Dedicate Channel. Separate wire frequency division multiplexing (FDM) time division multiplexing (TDM) Multiplexor (MUX) Demultiplexor (Concentrator) DEMUX individual lines shared individual lines high speed line Frequency Frequency Channel 1 available bandwidth 2 1 2 3 4 1 2 3 4 1 2 3 4 3 4 FDM Time TDM Time chow CS522 F2001—Multiplexing and Switching—10/17/2001—Page 1 Frequency Division Multiplexing (FDM) chow CS522 F2001—Multiplexing and Switching—10/17/2001—Page 2 Wavelength Division Multiplexing chow CS522 F2001—Multiplexing and Switching—10/17/2001—Page 3 Impact of WDM z Many big organizations are starting projects to design WDM system or DWDN (Dense Wave Division Mutiplexing Network). We may see products appear in next three years.In Fujitsu and CCL/Taiwan, 128 different wavelengthes on the same strand of fiber was reported working in the lab. z We may have optical routers between end systems that can take one wavelenght signal, covert to different wavelenght, send it out on different links. Some are designing traditional routers that covert optical signal to electronical signal, and use time slot interchange based on high speed memory to do the switching, the convert the electronic signal back to optical signal. z With this type of optical networks, we will have a virtual circuit network, where each connection is assigned some wave length. Each connection can have 2.4 gbps tremedous bandwidth. z With inital 128 different wavelength, we can have about 10 end users. If each pair of end users needs to communicate simultaneously, it will use 10*10=100 different wavelength. -
Unlicensed Lte Interference to Wi-Fi When Operating Co-Channel
UNLICENSED LTE INTERFERENCE TO WI-FI WHEN OPERATING CO-CHANNEL Christopher Szymanski 1 | © 2016 Broadcom Limited. All rights reserved. WI-FI DEMAND EVER-INCREASING Wi-Fi Cumulative Product Shipments and Installed Base of Products 2000-2020 35,000.0 Installed Base 30,000.0 Cumulative Shipments Approaching 15 billion cumulative shipments and 7.5 billion Wi-Fi install base 25,000.0 20,000.0 15,000.0 10,000.0 5,000.0 - 2000 2001 2002 2003 2004 2005 2006 2007 2008 2009 2010 2011 2012 2013 2014 2015 2016 2017 2018 2019 2020 Source: ABI Research: Cumulative Wi-Fi-enabled Product Shipments and Installed Base of Wi-Fi-enabled Products World Market, Forecast: 2000 to 2020. 2 | © 2016 Broadcom Limited. All rights reserved. WI-FI IS PREDOMINATE WAY FOR PEOPLE TO ACCESS INTERNET; IN SOME INSTANCES THE ONLY WAY • Cisco: Mobile data traffic increased 74% in 2015, reaching 3.7 exabytes per month [1] • Over 80% of mobile data traffic goes over Wi-Fi – Strategy Analytics’ Telemetry Intelligence Platform: From 2H13 to 1H15 Wi-Fi traffic grew at over 2X the rate of cellular traffic, accounting for ~83% of wireless traffic [2] – Analysys Mason: 81% of smart phone traffic is carried over Wi-Fi [3] – Mobidia: “Wi-Fi dominating monthly data usage” [4] – iOS users consume 82% of wireless data over Wi-Fi – Android users consume 78% of wireless data over Wi-Fi • Pew Internet Research: In-home Broadband access decreasing, increasing number of “smartphone-only” adults (13% of Americans are smartphone-only, and shift most pronounced among lower income households) [5] -

Lecture 8: Overview of Computer Networking Roadmap
Lecture 8: Overview of Computer Networking Slides adapted from those of Computer Networking: A Top Down Approach, 5th edition. Jim Kurose, Keith Ross, Addison-Wesley, April 2009. Roadmap ! what’s the Internet? ! network edge: hosts, access net ! network core: packet/circuit switching, Internet structure ! performance: loss, delay, throughput ! media distribution: UDP, TCP/IP 1 What’s the Internet: “nuts and bolts” view PC ! millions of connected Mobile network computing devices: server Global ISP hosts = end systems wireless laptop " running network apps cellular handheld Home network ! communication links Regional ISP " fiber, copper, radio, satellite access " points transmission rate = bandwidth Institutional network wired links ! routers: forward packets (chunks of router data) What’s the Internet: “nuts and bolts” view ! protocols control sending, receiving Mobile network of msgs Global ISP " e.g., TCP, IP, HTTP, Skype, Ethernet ! Internet: “network of networks” Home network " loosely hierarchical Regional ISP " public Internet versus private intranet Institutional network ! Internet standards " RFC: Request for comments " IETF: Internet Engineering Task Force 2 A closer look at network structure: ! network edge: applications and hosts ! access networks, physical media: wired, wireless communication links ! network core: " interconnected routers " network of networks The network edge: ! end systems (hosts): " run application programs " e.g. Web, email " at “edge of network” peer-peer ! client/server model " client host requests, receives -

Efficient Channelization for PMR+4G and GSM Refarming Base Stations
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by MURAL - Maynooth University Research Archive Library ISSC 2012, NUI Maynooth, June 28-29 Efficient Channelization for PMR+4G and GSM Re-Farming Base Stations Álvaro Palomo Navarro, Rudi Villing, Ronan Farrell Callan Institute, Department of Electronic Engineering National University of Ireland, Maynooth email : [email protected], [email protected], [email protected] _______________________________________________________________________________ Abstract— Current trends in mobile communications look for a better usage of the frequency spectrum by diverging from the classic frequency bands division for each standard. Instead, sharing a same frequency band by several mobile standards has been motivated by several factors: under-utilisation of some frequency bands, better electromagnetic propagation properties and provision of new capabilities to existing standards. This new way to manage the electromagnetic spectrum has an influence in the devices which form the mobile radio interface: base stations and mobiles stations. In particular for base stations, channelization represents an important challenge. In this paper efficient channelization techniques are proposed as a practical solution for real world professional and commercial mobile communication cases where frequency bands are shared. Depending on each case, the most optimal solution is based on the application of one of these channelization techniques, or a combination of several of them. Keywords – Dynamic spectrum allocation, non-uniform channelization, PMR+4G, GSM re-farming _______________________________________________________________________________ Interoperability for Microwave Access (WiMAX) or I INTRODUCTION Long Term Evolution (LTE)—would be integrated with In wireless communications, spectrum has traditionally TETRA/TEDS [2]. Furthermore, the integration should been divided into different coarse frequency bands not require additional spectrum allocations. -

Circuit-Switched Coherence
Circuit-Switched Coherence ‡Natalie Enright Jerger, ‡Mikko Lipasti, and ?Li-Shiuan Peh ‡Electrical and Computer Engineering Department, University of Wisconsin-Madison ?Department of Electrical Engineering, Princeton University Abstract—Circuit-switched networks can significantly lower contention, overall system performance can degrade by 20% the communication latency between processor cores, when or more. This latency sensitivity coupled with low link uti- compared to packet-switched networks, since once circuits are set up, communication latency approaches pure intercon- lization motivates our exploration of circuit-switched fabrics nect delay. However, if circuits are not frequently reused, the for CMPs. long set up time and poorer interconnect utilization can hurt Our investigations show that traditional circuit-switched overall performance. To combat this problem, we propose a hybrid router design which intermingles packet-switched networks do not perform well, as circuits are not reused suf- flits with circuit-switched flits. Additionally, we co-design a ficiently to amortize circuit setup delay. This observation prediction-based coherence protocol that leverages the exis- motivates a network with a hybrid router design that sup- tence of circuits to optimize pair-wise sharing between cores. The protocol allows pair-wise sharers to communicate di- ports both circuit and packet switching with very fast circuit rectly with each other via circuits and drives up circuit reuse. reconfiguration (setup/teardown). Our preliminary results Circuit-switched coherence provides overall system perfor- show this leading to up to 8% improvement in overall system mance improvements of up to 17% with an average improve- performance over a packet-switched fabric. ment of 10% and reduces network latency by up to 30%. -

Medium Access Control Layer
Telematics Chapter 5: Medium Access Control Sublayer User Server watching with video Beispielbildvideo clip clips Application Layer Application Layer Presentation Layer Presentation Layer Session Layer Session Layer Transport Layer Transport Layer Network Layer Network Layer Network Layer Univ.-Prof. Dr.-Ing. Jochen H. Schiller Data Link Layer Data Link Layer Data Link Layer Computer Systems and Telematics (CST) Physical Layer Physical Layer Physical Layer Institute of Computer Science Freie Universität Berlin http://cst.mi.fu-berlin.de Contents ● Design Issues ● Metropolitan Area Networks ● Network Topologies (MAN) ● The Channel Allocation Problem ● Wide Area Networks (WAN) ● Multiple Access Protocols ● Frame Relay (historical) ● Ethernet ● ATM ● IEEE 802.2 – Logical Link Control ● SDH ● Token Bus (historical) ● Network Infrastructure ● Token Ring (historical) ● Virtual LANs ● Fiber Distributed Data Interface ● Structured Cabling Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.2 Design Issues Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.3 Design Issues ● Two kinds of connections in networks ● Point-to-point connections OSI Reference Model ● Broadcast (Multi-access channel, Application Layer Random access channel) Presentation Layer ● In a network with broadcast Session Layer connections ● Who gets the channel? Transport Layer Network Layer ● Protocols used to determine who gets next access to the channel Data Link Layer ● Medium Access Control (MAC) sublayer Physical Layer Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.4 Network Types for the Local Range ● LLC layer: uniform interface and same frame format to upper layers ● MAC layer: defines medium access .. -

4G to 5G Networks and Standard Releases
4G to 5G networks and standard releases CoE Training on Traffic engineering and advanced wireless network planning Sami TABBANE 30 September -03 October 2019 Bangkok, Thailand 1 Objectives Provide an overview of various technologies and standards of 4G and future 5G 2 Agenda I. 4G and LTE networks II. LTE Release 10 to 14 III. 5G 3 Agenda I. 4G and LTE networks 4 LTE/SAE 1. 4G motivations 5 Introduction . Geneva, 18 January 2012 – Specifications for next-generation mobile technologies – IMT-Advanced – agreed at the ITU Radiocommunications Assembly in Geneva. ITU determined that "LTELTELTE----AdvancedAdvancedAdvanced" and "WirelessMANWirelessMANWirelessMAN----AdvancedAdvancedAdvanced" should be accorded the official designation of IMTIMT----AdvancedAdvanced : . Wireless MANMAN- ---AdvancedAdvancedAdvanced:::: Mobile WiMax 2, or IEEE 802. 16m; . 3GPPLTE AdvancedAdvanced: LTE Release 10, supporting both paired Frequency Division Duplex (FDD) and unpaired Time Division Duplex (TDD) spectrum. 6 Needs for IMT-Advanced systems Need for higher data rates and greater spectral efficiency Need for a Packet Switched only optimized system Use of licensed frequencies to guarantee quality of services Always-on experience (reduce control plane latency significantly and reduce round trip delay) Need for cheaper infrastructure Simplify architecture of all network elements 7 Impact and requirements on LTE characteristics Architecture (flat) Frequencies (flexibility) Bitrates (higher) Latencies (lower) Cooperation with other technologies (all 3GPP and -

Network 2020: Mission Critical Communications NETWORK 2020 MISSION CRITICAL COMMUNICATIONS
Network 2020: Mission Critical Communications NETWORK 2020 MISSION CRITICAL COMMUNICATIONS About the GSMA Network 2020 The GSMA represents the interests of mobile operators The GSMA’s Network 2020 Programme is designed to help worldwide, uniting nearly 800 operators with almost 300 operators and the wider mobile industry to deliver all-IP companies in the broader mobile ecosystem, including handset networks so that everyone benefits regardless of where their and device makers, software companies, equipment providers starting point might be on the journey. and internet companies, as well as organisations in adjacent industry sectors. The GSMA also produces industry-leading The programme has three key work-streams focused on: The events such as Mobile World Congress, Mobile World Congress development and deployment of IP services, The evolution of the Shanghai, Mobile World Congress Americas and the Mobile 360 4G networks in widespread use today The 5G Journey, developing Series of conferences. the next generation of mobile technologies and service. For more information, please visit the GSMA corporate website For more information, please visit the Network 2020 website at www.gsma.com. Follow the GSMA on Twitter: @GSMA. at: www.gsma.com/network2020 Follow the Network 2020 on Twitter: #Network2020. With thanks to contributors: DISH Network Corporation EE Limited Ericsson Gemalto NV Huawei Technologies Co Ltd KDDI Corporation KT Corporation NEC Corporation Nokia Orange Qualcomm Incorporated SK Telecom Co., Ltd. Telecom Italia SpA TeliaSonera -
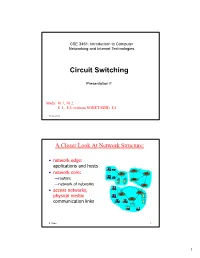
F. Circuit Switching
CSE 3461: Introduction to Computer Networking and Internet Technologies Circuit Switching Presentation F Study: 10.1, 10.2, 8 .1, 8.2 (without SONET/SDH), 8.4 10-02-2012 A Closer Look At Network Structure: • network edge: applications and hosts • network core: —routers —network of networks • access networks, physical media: communication links d. xuan 2 1 The Network Core • mesh of interconnected routers • the fundamental question: how is data transferred through net? —circuit switching: dedicated circuit per call: telephone net —packet-switching: data sent thru net in discrete “chunks” d. xuan 3 Network Layer Functions • transport packet from sending to receiving hosts application transport • network layer protocols in network data link network physical every host, router network data link network data link physical data link three important functions: physical physical network data link • path determination: route physical network data link taken by packets from source physical to dest. Routing algorithms network network data link • switching: move packets from data link physical physical router’s input to appropriate network data link application router output physical transport network data link • call setup: some network physical architectures require router call setup along path before data flows d. xuan 4 2 Network Core: Circuit Switching End-end resources reserved for “call” • link bandwidth, switch capacity • dedicated resources: no sharing • circuit-like (guaranteed) performance • call setup required d. xuan 5 Circuit Switching • Dedicated communication path between two stations • Three phases — Establish (set up connection) — Data Transfer — Disconnect • Must have switching capacity and channel capacity to establish connection • Must have intelligence to work out routing • Inefficient — Channel capacity dedicated for duration of connection — If no data, capacity wasted • Set up (connection) takes time • Once connected, transfer is transparent • Developed for voice traffic (phone) g. -

A Survey of Resource Allocation Techniques for Cellular Network's
electronics Review A Survey of Resource Allocation Techniques for Cellular Network’s Operation in the Unlicensed Band Mohammedhusen Manekiya 1 , Abhinav Kumar 2 , Ashish Yadav 3 and Massimo Donelli 1,* 1 Department of Information Engineering and Computer Science, University of Trento, 38123 Trento, Italy; [email protected] 2 Department of Electrical Engineering, Indian Institute of Technology Hyderabad, Telangana 502285, India; [email protected] 3 Department of Electrical and Computer Engineering, Tandon School of Engineering, New York University, Brooklyn, NY 11201, USA; [email protected] * Correspondence: [email protected]; Tel.: +39-3297-00-4115 Received: 1 August 2020; Accepted: 27 August 2020; Published: 7 September 2020 Abstract: With an ever increasing demand for data, better and efficient spectrum operation has become crucial in cellular networks. In this paper, we present a detailed survey of various resource allocation schemes that have been considered for the cellular network’s operation in the unlicensed spectrum. The key channel access mechanisms for cellular network’s operation in the unlicensed bands are discussed. The various channel selection techniques are explored and their operation explained. The prime issue of fairness between cellular and Wi-Fi networks is discussed, along with suitable resource allocation techniques that help in achieving this fairness. We analyze the coverage, capacity, and impact of coordination in LTE-U systems. Furthermore, we study and discuss the impact and discussed the impact of various traffic type, environments, latency, handover, and scenarios on LTE-U’s performance. The new upcoming 5G New Radio and MulteFire is briefly described along with some of the critical aspects of LTE-U which require further research. -

HD Voice Annex C Minimum Requirements with GSM/UMTS/LTE
GSM Association Non-Confidential Minimum Technical Requirements for use of the HD Voice Logo with GSM/UMTS/LTE issued by GSMA Minimum Technical Requirements for use of the HD Voice Logo with GSM/UMTS/LTE issued by GSMA Version 1.1 22nd March 2013 Security Classification – NON CONFIDENTIAL GSMA MATERIAL Copyright Notice Copyright © 2013 GSM Association. Antitrust Notice The information contain herein is in full compliance with the GSM Association’s antitrust compliance policy. Version 1.1 Page 1 of 18 GSM Association Non-Confidential Minimum Technical Requirements for use of the HD Voice Logo with GSM/UMTS/LTE issued by GSMA Table of Contents INTRODUCTION ..................................................................................................................... 3 ANNEX C: MINIMUM REQUIREMENTS FOR MOBILE NETWORKS AND TERMINALS FOR THE USAGE OF THE ‘HD VOICE’ LOGO WITH GSM/UMTS/LTE............................................................................................................... 3 DOCUMENT MANAGEMENT ............................................................................................... 18 Document History .................................................................................................................. 18 Other Information ................................................................................................................... 18 Version 1.1 Page 2 of 18 GSM Association Non-Confidential Minimum Technical Requirements for use of the HD Voice Logo with GSM/UMTS/LTE issued by GSMA INTRODUCTION