TESLA: a Transparent, Extensible Session-Layer Architecture for End-To-End Network Services
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Solutions to Chapter 2
CS413 Computer Networks ASN 4 Solutions Solutions to Assignment #4 3. What difference does it make to the network layer if the underlying data link layer provides a connection-oriented service versus a connectionless service? [4 marks] Solution: If the data link layer provides a connection-oriented service to the network layer, then the network layer must precede all transfer of information with a connection setup procedure (2). If the connection-oriented service includes assurances that frames of information are transferred correctly and in sequence by the data link layer, the network layer can then assume that the packets it sends to its neighbor traverse an error-free pipe. On the other hand, if the data link layer is connectionless, then each frame is sent independently through the data link, probably in unconfirmed manner (without acknowledgments or retransmissions). In this case the network layer cannot make assumptions about the sequencing or correctness of the packets it exchanges with its neighbors (2). The Ethernet local area network provides an example of connectionless transfer of data link frames. The transfer of frames using "Type 2" service in Logical Link Control (discussed in Chapter 6) provides a connection-oriented data link control example. 4. Suppose transmission channels become virtually error-free. Is the data link layer still needed? [2 marks – 1 for the answer and 1 for explanation] Solution: The data link layer is still needed(1) for framing the data and for flow control over the transmission channel. In a multiple access medium such as a LAN, the data link layer is required to coordinate access to the shared medium among the multiple users (1). -

OSI Model and Network Protocols
CHAPTER4 FOUR OSI Model and Network Protocols Objectives 1.1 Explain the function of common networking protocols . TCP . FTP . UDP . TCP/IP suite . DHCP . TFTP . DNS . HTTP(S) . ARP . SIP (VoIP) . RTP (VoIP) . SSH . POP3 . NTP . IMAP4 . Telnet . SMTP . SNMP2/3 . ICMP . IGMP . TLS 134 Chapter 4: OSI Model and Network Protocols 4.1 Explain the function of each layer of the OSI model . Layer 1 – physical . Layer 2 – data link . Layer 3 – network . Layer 4 – transport . Layer 5 – session . Layer 6 – presentation . Layer 7 – application What You Need To Know . Identify the seven layers of the OSI model. Identify the function of each layer of the OSI model. Identify the layer at which networking devices function. Identify the function of various networking protocols. Introduction One of the most important networking concepts to understand is the Open Systems Interconnect (OSI) reference model. This conceptual model, created by the International Organization for Standardization (ISO) in 1978 and revised in 1984, describes a network architecture that allows data to be passed between computer systems. This chapter looks at the OSI model and describes how it relates to real-world networking. It also examines how common network devices relate to the OSI model. Even though the OSI model is conceptual, an appreciation of its purpose and function can help you better understand how protocol suites and network architectures work in practical applications. The OSI Seven-Layer Model As shown in Figure 4.1, the OSI reference model is built, bottom to top, in the following order: physical, data link, network, transport, session, presentation, and application. -
OSI Model: the 7 Layers of Network Architecture
OSI Model: The 7 Layers of Network Architecture The Open Systems Interconnection (OSI) Reference Model is a conceptual framework that describes functions of the networking or telecommunication system independently from the underlying technology infrastructure. It divides data communication into seven abstraction layers and standardizes protocols into appropriate groups of networking functionality to ensure interoperability within the communication system regardless of the technology type, vendor, and model. The OSI model was originally developed to facilitate interoperability between vendors and to define clear standards for network communication. However, the olderTCP/IP model remains the ubiquitous reference framework for Internet communications today. The 7 layers of the OSI model This image illustrates the seven layers of the OSI model. Below, we’ll briefly describe each layer, from bottom to top. 1. Physical The lowest layer of the OSI model is concerned with data communication in the form of electrical, optic, or electromagnetic signals physically transmitting information between networking devices and infrastructure. The physical layer is responsible for the communication of unstructured raw data streams over a physical medium. It defines a range of aspects, including: Electrical, mechanical, and physical systems and networking devices that include specifications such as cable size, signal frequency, voltages, etc. Topologies such as Bus, Star, Ring, and Mesh Communication modes such as Simplex, Half Duplex, and Full Duplex Data transmission performance, such as Bit Rate and Bit Synchronization Modulation, switching, and interfacing with the physical transmission medium Common protocols including Wi-Fi, Ethernet, and others Hardware including networking devices, antennas, cables, modem, and intermediate devices such as repeaters and hubs 2. -

Medium Access Control Layer
Telematics Chapter 5: Medium Access Control Sublayer User Server watching with video Beispielbildvideo clip clips Application Layer Application Layer Presentation Layer Presentation Layer Session Layer Session Layer Transport Layer Transport Layer Network Layer Network Layer Network Layer Univ.-Prof. Dr.-Ing. Jochen H. Schiller Data Link Layer Data Link Layer Data Link Layer Computer Systems and Telematics (CST) Physical Layer Physical Layer Physical Layer Institute of Computer Science Freie Universität Berlin http://cst.mi.fu-berlin.de Contents ● Design Issues ● Metropolitan Area Networks ● Network Topologies (MAN) ● The Channel Allocation Problem ● Wide Area Networks (WAN) ● Multiple Access Protocols ● Frame Relay (historical) ● Ethernet ● ATM ● IEEE 802.2 – Logical Link Control ● SDH ● Token Bus (historical) ● Network Infrastructure ● Token Ring (historical) ● Virtual LANs ● Fiber Distributed Data Interface ● Structured Cabling Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.2 Design Issues Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.3 Design Issues ● Two kinds of connections in networks ● Point-to-point connections OSI Reference Model ● Broadcast (Multi-access channel, Application Layer Random access channel) Presentation Layer ● In a network with broadcast Session Layer connections ● Who gets the channel? Transport Layer Network Layer ● Protocols used to determine who gets next access to the channel Data Link Layer ● Medium Access Control (MAC) sublayer Physical Layer Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.4 Network Types for the Local Range ● LLC layer: uniform interface and same frame format to upper layers ● MAC layer: defines medium access .. -

The OSI Model: Understanding the Seven Layers of Computer Networks
Expert Reference Series of White Papers The OSI Model: Understanding the Seven Layers of Computer Networks 1-800-COURSES www.globalknowledge.com The OSI Model: Understanding the Seven Layers of Computer Networks Paul Simoneau, Global Knowledge Course Director, Network+, CCNA, CTP Introduction The Open Systems Interconnection (OSI) model is a reference tool for understanding data communications between any two networked systems. It divides the communications processes into seven layers. Each layer both performs specific functions to support the layers above it and offers services to the layers below it. The three lowest layers focus on passing traffic through the network to an end system. The top four layers come into play in the end system to complete the process. This white paper will provide you with an understanding of each of the seven layers, including their functions and their relationships to each other. This will provide you with an overview of the network process, which can then act as a framework for understanding the details of computer networking. Since the discussion of networking often includes talk of “extra layers”, this paper will address these unofficial layers as well. Finally, this paper will draw comparisons between the theoretical OSI model and the functional TCP/IP model. Although TCP/IP has been used for network communications before the adoption of the OSI model, it supports the same functions and features in a differently layered arrangement. An Overview of the OSI Model Copyright ©2006 Global Knowledge Training LLC. All rights reserved. Page 2 A networking model offers a generic means to separate computer networking functions into multiple layers. -

ADD WES/OSN CH 11 5Thprf
THE PRESENTATION AND 11 SESSION LAYERS The presentation and session layers collaborate to provide many of the distributed-processing capabilities presented to user elements by the ser- vice elements of the application layer; for this reason, they are discussed together. Presentation Layer Chapter 4 describes how ASN.1 provides the application programmer with a tool for creating data structures that are syntactically independent from the way in which data are stored in a computer and from the way in which they are transferred between computer systems. Transforming these abstract syntaxes into “concrete” data structures appropriate for a given operating system (e.g., UNIX, DOS, VMS, MVS) is typically han- dled by tools such as ASN.1 compilers. The task of preserving the seman- tics of the data exchanged between a sender and receiver across an OSI network is handled by the presentation layer, which performs the trans- formations from the local (concrete) syntax used by each application entity to a common transfer syntax. This leads us to the discussion of the notion of a presentation context set. Context Set The presentation layer is responsible for managing the transfer syntaxes Definition associated with the set of abstract syntaxes that will be used by applica- tion entities as they exchange information across a presentation connec- tion. As part of presentation connection establishment, application enti- ties must be sure that the presentation layer can support a transfer syntax 247 248 OPEN SYSTEMS NETWORKING: TCP/IP AND OSI for every abstract syntax required by the distributed-processing applica- tion(s) that will use this connection. -

1.2. OSI Model
1.2. OSI Model The OSI model classifies and organizes the tasks that hosts perform to prepare data for transport across the network. You should be familiar with the OSI model because it is the most widely used method for understanding and talking about network communications. However, remember that it is only a theoretical model that defines standards for programmers and network administrators, not a model of actual physical layers. Using the OSI model to discuss networking concepts has the following advantages: Provides a common language or reference point between network professionals Divides networking tasks into logical layers for easier comprehension Allows specialization of features at different levels Aids in troubleshooting Promotes standards interoperability between networks and devices Provides modularity in networking features (developers can change features without changing the entire approach) However, you must remember the following limitations of the OSI model: OSI layers are theoretical and do not actually perform real functions. Industry implementations rarely have a layer‐to‐layer correspondence with the OSI layers. Different protocols within the stack perform different functions that help send or receive the overall message. A particular protocol implementation may not represent every OSI layer (or may spread across multiple layers). To help remember the layer names of the OSI model, try the following mnemonic devices: Mnemonic Mnemonic Layer Name (Bottom to top) (Top to bottom) Layer 7 Application Away All Layer 6 Presentation Pizza People Layer 5 Session Sausage Seem Layer 4 Transport Throw To Layer 3 Network Not Need Layer 2 Data Link Do Data Layer 1 Physical Please Processing Have some fun and come up with your own mnemonic for the OSI model, but stick to just one so you don't get confused. -

ISO/OSI Model SSL: Security at Transport Layer
ISO/OSI Model SSL: Security at Transport Layer Peer-to-peer Application Layer Application Layer Presentation Layer Presentation Layer Network Security Session Layer Session Layer Assurance Transport Layer Transport Layer Network Layer Network Layer Network Layer Lecture 9 Data Link Layer Data Link Layer Data Link Layer Physical Layer Physical Layer Physical Layer October 30, 2003 Flow of bits Courtesy of Professors INFSCI 2935: Introduction of Computer Security 1 INFSCI 2935: Introduction to Computer Security 2 Chris Clifton & Matt Bishop 1 Security at the Transport Layer Secure Socket Layer (SSL) Secure Socket Layer (SSL) l Developed by Netscape to provide security in l Each party keeps session information ¡ Session identifier (unique) WWW browsers and servers ¡ The peer’s X.503(v3) certificate l SSL is the basis for the Internet standard ¡ Compression method used to reduce volume of data ¡ Cipher specification (parameters for cipher and MAC) protocol – Transport Layer Security (TLS) ¡ Master secret of 48 bits protocol (compatible with SSLv3) l Connection information ¡ Random data for the server & client l Key idea: Connections and Sessions ¡ Server and client keys (used for encryption) ¡A SSL session is an association between two peers ¡ Server and client MAC key ¡An SSL connection is the set of mechanisms used to ¡ Initialization vector for the cipher, if needed ¡ Server and client sequence numbers transport data in an SSL session l Provides a set of supported cryptographic mechanisms that are setup during negotiation (handshake protocol) -
Seven Layer OSI Model
InternationalInternational StandardsStandards OrganizationOrganization OpenOpen SystemsSystems InterconnectInterconnect (OSI)(OSI) ReferenceReference ModelModel Networks: OSI Reference Model 1 Application A Application B Application Application Layer Layer Presentation Presentation Layer Layer Session Session Layer Layer Transport Transport Layer Communication Network Layer Network Network Network Network Layer Layer Layer Layer Data Link Data Link Data Link Data Link Layer Layer Layer Layer Physical Physical Physical Physical Layer Layer Layer Layer Copyright ©2000 The McGraw Hill Companies Electrical and/or Optical Signals Leon-Garcia & Widjaja: Communication Networks Figure 2.6 Networks: OSI Reference Model 2 Copyright ©2000 The McGraw Hill Companies Leon-Garcia & Widjaja: Communication Networks Figure 2.9 Application A Application B data Application Application Layer data ah Layer Presentation Presentation Layer data ph Layer Session Session Layer data sh Layer Transport th Transport Layer data Layer Network Network Layer data nh Layer Data Link Data Link Layer dt data dh Layer Physical Physical Layer bits Layer Networks: OSI Reference Model 3 HTTP Request Header contains source and TCP destination port numbers Header Header contains source and destination IP addresses; IP transport protocol type Header Header contains source Frame and destination physical Ethernet addresses; network Check protocol type Header Sequence Copyright ©2000 The McGraw Hill Companies Leon-Garcia & Widjaja: Communication Networks Figure 2.15 Networks: OSI Reference Model 4 OSIOSI versusversus TCP/IPTCP/IP Figure 1-21. The TCP/IP reference model. Networks: OSI Reference Model 5 OSIOSI versusversus TCP/IPTCP/IP DCCDCC 66th Ed.,Ed., W.W. StallingsStallings FigureFigure 1.111.11 Networks: OSI Reference Model 6 SevenSeven LayerLayer OSIOSI ModelModel Application Layer Provides users access to the OSI environment and distributed information services.services. -

Security Protocols Overview an RSA Data Security Brief SSL &
Security Protocols Overview An RSA Data Security Brief SSL & TLS Secure Socket Layer & Transport Layer Security Secure Sockets Layer (SSL) is the that do not necessarily need to be Internet security protocol for on the same secure network. point-to-point connections. It pro- Where SSL secures two applica- vides protection against eaves- tions, IPSec secures an entire net- dropping, tampering, and forgery. work. Clients and servers are able to au- thenticate each other and to estab- Applications lish a secure link, or “pipe,” across SSL can be used in any situation the Internet or Intranets to protect where a link between two comput- the information transmitted. ers or applications needs to be pro- tected. The following are just a few The Need for SSL of the real-world, practical appli- With the growth of the Internet cations of SSL & TLS: and digital data transmission, many applications need to se- curely transmit data to remote applications and computers. • Client/Server Systems SSL was designed to solve this problem in an open standard. SSL in the browser is not enough to secure most systems. Systems such as secure database access, or remote object SSL is analogous to a secure “telephone call” between two systems such as CORBA, can all be securely improved computers on any network including the Internet. In SSL, a using SSL. Other applications include redirection of se- connection is made, parties authenticated, and data securely cure connections such as proxy servers, secure Webserver exchanged. The latest enhancement of SSL is called Trans- plug-ins, and Java “Servlets.” port Layer Security (TLS). -
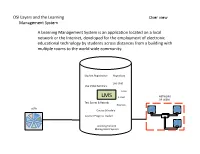
OSI & LMS Final Project.Pptx
OSI Layers and the Learning Over view Management System A Learning Management System is an applicaon located on a local network or the Internet, developed for the employment of electronic educaonal technology by students across distances from a building with mul7ple rooms to the world wide community. Student Registraon Repository Live Chat Live Video Seminars Tests LMS E-mail NETWORK OF USERS Test Scores & Records Courses USER Course Schedule Learner Progress Tracker Learning Content Management System OSI Layers and the Learning Physical Layer Management System DEVICE DEVICE CABLE MODEM FREQUENCY CABLE The physical layer supports the actual movement of bits and volts between devices (smart phone, computer, tablet, modem, repeater) through copper wire, fiber op7c cable, radio frequencies, or any other medium used to transmit data by a MODEM physical means. The physical layer is not concerned with the structure or organizaon of data, it is simply transming and receiving the data. Some devices func7on on other layers of the OSI model, so they do not fit neatly into physical layer because they conduct a CABLE func7on beyond simply moving bits and volts. However, all devices par7ally operate CABLE in the physical layer, but it is their primary func7on that solidly places them in one of CABLE REPEATER the other layers. REPEATER MODEM DEVICE OSI Layers and the Learning Data Link Layer Management System WIDE AREA NETWORK or LOCAL AREA NETWORK NODE NODE NIC NIC FRAMES—FRAMES—FRAMES—FRAMES FRAMES—FRAMES—FRAMES SWITCH / BRIDGE The data link layer is divided into two sub-layers; Logical Link Control (LLC) and Media Access Control (MAC). -

Session Layer OSI Reference Model Fatih SÜRER 2010514060
13.4.2015 OSI LAYER 5 - Session Layer OSI Reference Model Fatih SÜRER 2010514060 2 Review of the First Four Layer 3 4 Session Layer In the seven-layer OSI model of computer networking , the session layer is layer 5. This layer is primarily concerned with coordinating applications as they interact on different hosts. Support the dialog between cooperating application programs The session layer offers provisions for efficient data transfer. The session layer decides when to turn communication on and off between two computer Provides duplex, half-duplex, or simplex communications between devices. 5 6 1 13.4.2015 Session Layer Cont. The Session Layer provides services that allow to establish/manage/terminate a session-connection, to support orderly data exchange, to organize and to synchronize the dialogue and to release the connection in an orderly manner. The session’s layer objective is to hide the possible failures of transport-level connections to the upper layer higher. 7 8 Session Layer Cont. Session Layer Cont. Session layer provides a name space that is used to tie together the Sessions offer various services, including dialog potentially different transport streams that are part of a single control (keeping track of whose turn it is to application. For example, it might manage an audio stream and a video stream that are being combined in a teleconferencing transmit), token management (preventing two application. long story short, principal task of the session layer is parties from attempting the same critical operation to connect two processes together into a session. simultaneously), and synchronization (checkpointing The session layer whose overall function is to ensure the end to end integrity of the applications that are being supported.