G Suite Security and Trust
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Volume I Restoration of Historic Streetcar Service
VOLUME I ENVIRONMENTAL ASSESSMENT RESTORATION OF HISTORIC STREETCAR SERVICE IN DOWNTOWN LOS ANGELES J U LY 2 0 1 8 City of Los Angeles Department of Public Works, Bureau of Engineering Table of Contents Contents EXECUTIVE SUMMARY ............................................................................................................................................. ES-1 ES.1 Introduction ........................................................................................................................................................... ES-1 ES.2 Purpose and Need ............................................................................................................................................... ES-1 ES.3 Background ............................................................................................................................................................ ES-2 ES.4 7th Street Alignment Alternative ................................................................................................................... ES-3 ES.5 Safety ........................................................................................................................................................................ ES-7 ES.6 Construction .......................................................................................................................................................... ES-7 ES.7 Operations and Ridership ............................................................................................................................... -

Minutes of Claremore Public Works Authority Meeting Council Chambers, City Hall, 104 S
MINUTES OF CLAREMORE PUBLIC WORKS AUTHORITY MEETING COUNCIL CHAMBERS, CITY HALL, 104 S. MUSKOGEE, CLAREMORE, OKLAHOMA MARCH 03, 2008 CALL TO ORDER Meeting called to order by Mayor Brant Shallenburger at 6:00 P.M. ROLL CALL Nan Pope called roll. The following were: Present: Brant Shallenburger, Buddy Robertson, Tony Mullenger, Flo Guthrie, Mick Webber, Terry Chase, Tom Lehman, Paula Watson Absent: Don Myers Staff Present: City Manager Troy Powell, Nan Pope, Serena Kauk, Matt Mueller, Randy Elliott, Cassie Sowers, Phil Stowell, Steve Lett, Daryl Golbek, Joe Kays, Gene Edwards, Tim Miller, Tamryn Cluck, Mark Dowler Pledge of Allegiance by all. Invocation by James Graham, Verdigris United Methodist Church. ACCEPTANCE OF AGENDA Motion by Mullenger, second by Lehman that the agenda for the regular CPWA meeting of March 03, 2008, be approved as written. 8 yes, Mullenger, Lehman, Robertson, Guthrie, Shallenburger, Webber, Chase, Watson. ITEMS UNFORESEEN AT THE TIME AGENDA WAS POSTED None CALL TO THE PUBLIC None CURRENT BUSINESS Motion by Mullenger, second by Lehman to approve the following consent items: (a) Minutes of Claremore Public Works Authority meeting on February 18, 2008, as printed. (b) All claims as printed. (c) Approve budget supplement for upgrading the electric distribution system and adding an additional Substation for the new Oklahoma Plaza Development - $586,985 - Leasehold improvements to new project number assignment. (Serena Kauk) (d) Approve budget supplement for purchase of an additional concrete control house for new Substation #5 for Oklahoma Plaza Development - $93,946 - Leasehold improvements to new project number assignment. (Serena Kauk) (e) Approve budget supplement for electrical engineering contract with Ledbetter, Corner and Associates for engineering design phase for Substation #5 - Oklahoma Plaza Development - $198,488 - Leasehold improvements to new project number assignment. -

Los Angeles Transportation Transit History – South LA
Los Angeles Transportation Transit History – South LA Matthew Barrett Metro Transportation Research Library, Archive & Public Records - metro.net/library Transportation Research Library & Archive • Originally the library of the Los • Transportation research library for Angeles Railway (1895-1945), employees, consultants, students, and intended to serve as both academics, other government public outreach and an agencies and the general public. employee resource. • Partner of the National • Repository of federally funded Transportation Library, member of transportation research starting Transportation Knowledge in 1971. Networks, and affiliate of the National Academies’ Transportation • Began computer cataloging into Research Board (TRB). OCLC’s World Catalog using Library of Congress Subject • Largest transit operator-owned Headings and honoring library, forth largest transportation interlibrary loan requests from library collection after U.C. outside institutions in 1978. Berkeley, Northwestern University and the U.S. DOT’s Volpe Center. • Archive of Los Angeles transit history from 1873-present. • Member of Getty/USC’s L.A. as Subject forum. Accessing the Library • Online: metro.net/library – Library Catalog librarycat.metro.net – Daily aggregated transportation news headlines: headlines.metroprimaryresources.info – Highlights of current and historical documents in our collection: metroprimaryresources.info – Photos: flickr.com/metrolibraryarchive – Film/Video: youtube/metrolibrarian – Social Media: facebook, twitter, tumblr, google+, -

Commuter Express Nonstop to Center St Vista Del Mar Imperial Hwy F Downtown Union O
EFFECTIV E JULY 31 , 2021 A PATIR DEL 31 DEL JULIO, 2021 AM LEAVES MARINE ARRIVES PARK & RIDE TRANSITWAY & REDONDO 2ND BEACH 1ST H O 5:55 6:09 6:13 6:20 6:31 6:00 6:10 6:33 6:39 6:50 5:56 6:10 6:20 6:53 6:30 6:15 6:26 6:50 6:50 6:35 6:55 9:00 LEAVES MARINE ARRIVES TRANSITWAY PARK & RIDE & REDONDO 1ST BEACH 2ND O — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — City of Los Angeles Department of Transportation (213, 310, 323 or/o 818) 808-2273 www.ladottransit.com EFFECTIV E JULY 31 , 2021 A PATIR DEL 31 DEL JULIO, 2021 La Cienega Blvd Cienega La Commuter Express Nonstop to Center St Vista Del Mar Imperial Hwy F Downtown Union O Route 438 Main St 105 Los Angeles Station nd Ave Alternate Route ra Park & via Century G Vignes St to/from Redondo El Segundo Blvd Ride and Harbor Garey St Beach/Marine Transitways St iew St EL SEGUNDO Park & Ride 45th Seav Utah Ave 135th St Temple St M Commuter Express Rosecrans Ave N D Av ePacific Route 439 Highland Ave Music Center City 33rd St S 1st St L City Hall a Personnel n Bus Stop 30th St 405 Building County P e h St Douglas St Park & 2nd St Buildings 26t d Drop-O y Marine Ave Ride r o eBch Av eBch Aviation Blvd Sepulveda Blvd Sepulveda S Points of Interest Marine Ave 3rd St MOCA/ t Spring St Spring St California Park & Ride 18th St 4th St Manhattan Beach Blvd Plaza Redondo Time Point 14th St Los Angeles St C 5th St Manha Metro Green Line 10th St 1 Library Municipal Square 6th St Pier 4th St Metro Red Line ttan Ave 1st St Wilshire Blvd Main St Main St eVail Av eVail Metro Purple Line 33rd St MANHATTAN K yBroadwa 7th St Longfellow Ave BEACH J evAGrand evAGrand Metro Blue Line 29th St Hill St 8th St PACIFIC 27th St Artesia Blvd StaFiguero Metro Expo Line OCEAN 26th St 9th St H Hope St Hope Olive St Olive Metro Silver Line e Flower St r 22nd St Olympic Blvd m HERMOSA o s 19th St BEACH AT&T Metro Rail Sta n a A 16th St ve Center City 11th St ve r A Transitway Sta n ie Public P Staples 12th St Municipal P Pier Center Works a Bldg. -

The Neighborly Substation the Neighborly Substation Electricity, Zoning, and Urban Design
MANHATTAN INSTITUTE CENTER FORTHE RETHINKING DEVELOPMENT NEIGHBORLY SUBstATION Hope Cohen 2008 er B ecem D THE NEIGHBORLY SUBstATION THE NEIGHBORLY SUBstATION Electricity, Zoning, and Urban Design Hope Cohen Deputy Director Center for Rethinking Development Manhattan Institute In 1879, the remarkable thing about Edison’s new lightbulb was that it didn’t burst into flames as soon as it was lit. That disposed of the first key problem of the electrical age: how to confine and tame electricity to the point where it could be usefully integrated into offices, homes, and every corner of daily life. Edison then designed and built six twenty-seven-ton, hundred-kilowatt “Jumbo” Engine-Driven Dynamos, deployed them in lower Manhattan, and the rest is history. “We will make electric light so cheap,” Edison promised, “that only the rich will be able to burn candles.” There was more taming to come first, however. An electrical fire caused by faulty wiring seriously FOREWORD damaged the library at one of Edison’s early installations—J. P. Morgan’s Madison Avenue brownstone. Fast-forward to the massive blackout of August 2003. Batteries and standby generators kicked in to keep trading alive on the New York Stock Exchange and the NASDAQ. But the Amex failed to open—it had backup generators for the trading-floor computers but depended on Consolidated Edison to cool them, so that they wouldn’t melt into puddles of silicon. Banks kept their ATM-control computers running at their central offices, but most of the ATMs themselves went dead. Cell-phone service deteriorated fast, because soaring call volumes quickly drained the cell- tower backup batteries. -
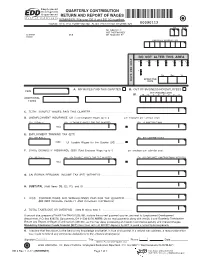
QUARTERLY CONTRIBUTION RETURN and REPORT of WAGES REMINDER: File Your DE 9 and DE 9C Together
QUARTERLY CONTRIBUTION RETURN AND REPORT OF WAGES REMINDER: File your DE 9 and DE 9C together. PLEASE TYPE THIS FORM—DO NOT ALTER PREPRINTED INFORMATION 00090112 YR QTR DELINQUENT IF NOT POSTMARKED QUARTER DUE OR RECEIVED BY ENDED EMPLOYER ACCOUNT NO. DO NOT ALTER THIS AREA Y ONL USET.DEP ONL Y P1 P2 C P U S A T Mo. Day Yr. EFFECTIVE DATE A. NO WAGES PAID THIS QUARTER B. OUT OF BUSINESS/NO EMPLOYEES FEIN OUT OF BUSINESS DATE B1. M M D D Y Y Y Y ADDITIONAL FEINS C. TOTAL SUBJECT WAGES PAID THIS QUARTER . D. UNEMPLOYMENT INSURANCE (UI) (Total Employee Wages up to $ per employee per calendar year) (D1) UI Rate % (D2) UI TAXABLE WAGES FOR THE QUARTER (D3) UI CONTRIBUTIONS TIMES E. EMPLOYMENT TRAINING TAX (ETT) (E1) ETT Rate % (E2) ETT CONTRIBUTIONS TIMES UI Taxable Wages for the Quarter (D2) . F. STATE DISABILITY INSURANCE (SDI) (Total Employee Wages up to $ per employee per calendar year) (F1) SDI Rate % (F2) SDI TAXABLE WAGES FOR THE QUARTER (F3) SDI EMPLOYEE CONTRIBUTIONS WITHHELD TIMES G. CALIFORNIA PERSONAL INCOME TAX (PIT) WITHHELD . H. SUBTOTAL (Add Items D3, E2, F3, and G) . I. LESS: CONTRIBUTIONS AND WITHHOLDINGS PAID FOR THE QUARTER . (DO NOT INCLUDE PENALTY AND INTEREST PAYMENTS) J. TOTAL TAXES DUE OR OVERPAID (Item H minus Item I) . If amount due, prepare a Payroll Tax Deposit (DE 88), include the correct payment quarter, and mail to: Employment Development Department, P.O. Box 826276, Sacramento, CA 94230-6276. NOTE: Do not mail payments along with the DE 9 and Quarterly Contribution Return and Report of Wages (Continuation) (DE 9C), as this may delay processing and result in erroneous penalty and interest charges. -
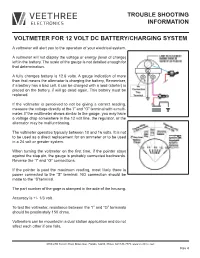
Trouble Shooting Information Voltmeter for 12 Volt Dc
TROUBLE SHOOTING INFORMATION VOLTMETER FOR 12 VOLT DC BATTERY/CHARGING SYSTEM A voltmeter will alert you to the operation of your electrical system. A voltmeter will not display the voltage or energy (level of charge) left in the battery. The scale of the gauge is not detailed enough for that determination. A fully changes battery is 12.6 volts. A gauge indication of more than that means the alternator is charging the battery, Remember, if a battery has a bad cell, it can be charged with a load (starter) is placed on the battery, if will go dead again. This battery must be replaced. If the voltmeter is perceived to not be giving a correct reading, measure the voltage directly at the ‘I” and “G” terminal with a multi- meter. If the multimeter shows similar to the gauge, you may have a voltage drop somewhere in the 12 volt line, the regulator, or the alternator may be malfunctioning. The voltmeter operates typically between 10 and 16 volts. It is not to be used as a direct replacement for an ammeter or to be used in a 24 volt or greater system. When turning the voltmeter on the first time, if the pointer stays against the stop pin, the gauge is probably connected backwards. Reverse the “I” and “G” connections. If the pointer is past the maximum reading, most likely there is power connected to the “S” terminal. NO connection should be made to the “S”terminal. The part number of the gage is stamped in the side of the housing. -

California Current Integrated Ecosystem
Agenda Item G.1.a IEA Team Report 1 March 2020 CALIFORNIA CURRENT INTEGRATED ECOSYSTEM ASSESSMENT (CCIEA) CALIFORNIA CURRENT ECOSYSTEM STATUS REPORT, 2020 A report of the NOAA CCIEA Team to the Pacific Fishery Management Council, March 5, 2020. Editors: Dr. Chris Harvey (NWFSC), Dr. Toby Garfield (SWFSC), Mr. Greg Williams (PSMFC), and Dr. Nick Tolimieri (NWFSC) 1 INTRODUCTION Section 1.4 of the 2013 Fishery Ecosystem Plan (FEP) established a reporting process wherein NOAA provides the Pacific Fishery Management Council (Council) with a yearly update on the status of the California Current Ecosystem (CCE), as derived from environmental, biological, economic and social indicators. NOAA’s California Current Integrated Ecosystem Assessment (CCIEA) team is responsible for this report. This is our 8th report, with prior reports in 2012 and 2014-2019. This report summarizes CCE status based on data and analyses that generally run through 2019. Highlights are summarized in Box 1.1. Appendices provide additional information or clarification, as requested by the Council, the Scientific and Statistical Committee (SSC), or other advisory bodies. Box 1.1: Highlights of this report • In 2019, the system experienced weak to neutral El Niño conditions, average to slightly positive Pacific Decadal Oscillation (PDO), and very weak North Pacific circulation • A large marine heatwave emerged in mid 2019, similar in size and intensity to the 2013- 2016 “Blob,” but it weakened by December, and we do not yet know what effects it had • Several ecological indicators -

California Assembly District 53 the Honorable John Perez Federal
California Assembly District 53 The Honorable John Perez Federal Historic Preservation Tax Incentive Projects in Los Angeles Certified Project Use Rehabilitation *Year represents Federal Fiscal Year Costs 2013 Boyle Hotel Affordable Housing $ 7,600,000 2011 901 S. Broadway/Blackstone’s Apartments $ 34,000,000 Department Store Metropolitan Building Retail and Residential $ 12,000,000 2010 Southern California Gas Company Retail and Residential $ 37,670,000 Complex Van Nuys Building Retail and Residential $ 15,000,000 2009 Hosfield Building (Victor Clothing Retail and Residential $ 8,000,000 Company) Pacific Electric Building Apartments $ 52,612,555 2008 Judson Rives Building Retail and Apartments $ 16,200,000 Title Guarantee Building Retail and Apartments $ 29,500,000 2007 Wm. G. Kerckhoff Bldg. & Annex Apartments and Artist $ 16,000,000 Lofts Security Building Apartments $ 38,178,708 Subway Terminal Building Commercial and $ 55,175,744 Housing 2006 Far East Cafe Commercial and $ 3,728,133 Senior Affordable Housing Hellman Building Multi-family Housing $ 8,606,500 Hotel Chancellor Multi-family Housing $ 4,530,000 Santa Fe Freight Depot School of Architecture $ 9,640,362 Young’s Market Retail and Apartments $ 8,000,000 2005 816 South Grand Avenue Live/Work Spaces $ 14,925,398 Continental Building Multi-Family Housing $ 5,014,322 General Petroleum Building Apartments $ 44,000,000 Mortgage Guarantee Building Apartments $ 2,400,000 Orpheum Theatre Theater and $ 9,900,000 Apartments U.S. Post Office, Los Angeles Terminal Technology Center $ 21,500,000 Annex 2004 Gerry Building Commercial $ 4,600,000 Continued on next page Federal Historic Preservation Tax Incentive Projects in Los Angeles, continued 2003 San Fernando Building Retail and Housing $ 5,014,322 TOTAL REHABILITATION COSTS (over years shown) $ 463,796,044 Attributed solely to the certified rehabilitation of historic structures TOTAL 20% Tax Credits Taken (on the above projects) $ 92,759,209 Certified Local Governments Los Angeles Los Angeles Certified Preservation Tax Incentives Projects Boyle Hotel 901 S. -
How Quiet Is a G:Link Tram?
You are receiving this newsletter because you subscribed to receive Light Rail updates on the Gold Coast Rapid Transit or GoldLinQ websites. This message contains graphics. If you do not see the graphics, click here to view. Tuesday 4 March 2014 How quiet is a G:Link tram? G:link trams are one of the quietest forms of transport available, making them ideal for a city such as the Gold Coast. A G:Link tram travelling at 70 kilometres per hour makes the same amount of noise as normal road traffic travelling at 40 kilometres per hour, around 75 decibels. When stationary, trams produce around 65 decibels of sound which is only slightly louder than an average office environment. The special design of the G:Link track helps make the trams quiet. The tracks are a continuous weld which eliminates the familiar “clickety clack” of heavy rail trains. The rail is also enclosed in a rubber boot which absorbs and dampens vibration when the trams travel along the tracks. Being embedded in concrete for the majority of the 13-kilmotre route also reduces the sound created by tram movements. The tram's warning bell has a volume of 80 decibels and is sounded for safety to warn pedestrians, motorists and cyclists of the tram’s approach. The bell is loud enough to be heard over surrounding ambient noise similar to emergency services’ sirens. During testing and commissioning the bell is sounded more frequently for driver training, but will reduce once operations commence in June of this year. All trams at home on the Coast 13 kilometres live Final tram arrives Tram testing reaches the completing the G:Link end of the system fleet GoldLinQ The final tram in the G:Link fleet has GoldLinQ will reach another historic arrived on the Gold Coast after a milestone this month with the entire Have you seen a pod? 25,000 kilometre journey from 13-kilometre system powered up and Germany. -

Railroad Electrification Activity a Summary Report
P6 ' 8 3 IMWI f T £ A / 0 A b - ^ Q / ^ 3 RAILROAD ELECTRIFICATION ACTIVITY A SUMMARY REPORT: 1980-1981 Prepared by Alice E. Kidder Ebon Research Systems 1118 9th St., N.W. Washington, D.C. 20001 Prepared for U.S. Department of Transportation Federal Railroad Administration Passenger Systems and Facilities, KRD-22 400 Seventh St., SW Washington, DC 20590 Contract # OTFR53-81-C-00226 April, 1982 -t f • i 13 - Electrification j t >.• • ' - ■ *-- *« wW^Tilf ~i fiSi*'. I’nV r‘‘rt J r Technical Report Documentation Page 1. Report No. 2. Government Accession No. 3. Recipient's Catalog No. r FRA/ORD-82/53 4. Title and Subtitle 5. Report Date RAILROAD ELECTRIFICATION ACTIVITY: A SUMMARY January, 1982 r REPORT, 1980-1981 6. Performing Orgonizotion Code 8. Performing Orgonizotion Report No. 7. Author's) r Alice E. Kidder FRA-1 9. Performing Organization Name and Address 10. Work Unit No. (TRAIS) f Ebon Research Systems 11. Controct or Grant No. 603 Southlawn Lane DTFR53-81-C-00226 Rockville, MD 20850 13. Type of Report and Period Covered 12. Sponsoring Agency Name and Address Final Report, June 1980- - June, 1981 14. Sponsoring Agency Code DOT/FRA/RRD-22 15. Supplementary Notes 16. Abstract This report reviews the status of railway electrification in North America and selected countries worldwide, for the period June, 1980 through June, 1981. Included in the report are updates on the extent of construction of electrifi cation; research completed on feasibility studies and technical developments in engineering and design? a summary of cost-effectiveness studies which have explored the economics of railroad electrification during the period in question; a review of activities of U.S. -

Terminal 1 E14 Lindbergh E15 E16 E12 E13 E10 Minneapolis-St
Terminal 1 E14 Lindbergh E15 E16 E12 E13 E10 Minneapolis-St. Paul International Airport E11 E8 D3 E9 E6 Down to: D1 D2 D4 Baggage Claim Inside Security E7 E4 D5 E5 E2 E3 D6 F13 Up to: Quiet Outside Security F11 Seating Area and C1 F15 F9 Conference Center E1 F16 F7 C2 F5 Down to: N Baggage Mall F14 F3 Claim C3 F12 Mezz F1 LEVEL 2 C4 F10 Ticketing Door 1 C5 F8 Ticketing / All Gates Thomson Reuters Concourse C Art F6 Door 2 C6 Gallery LEVEL 1 F4 Mall Door 3 Concourse Tram C7 Delta Air Lines Baggage Claim C8 Sky Club F2 Door 1 C9 Ticketing Baggage Claim Delta Air Lines Door 4 Door 2 C10 Up to: Taxis, Limos, Sky Club Mezz C11 Door 5 Door 3 Uber/Lyft/other G1 TNC’s & General Parking GREEN S To/From Baggage ClaimGREEN Ramp PINK Ramp C12 Short Short Film Space G2 Door 6 Door 4 BLUE LEVEL T Term Ramp G3 Baggage Claim Parking Door 5 Ground Transport To/From Ticketing & Parking C13 - C18 G4 Delta Delta Air Lines Door 6 Up to: G5 Up to: Check-in Short Term Parking Electronic Check-in Shuttles, PINK Ramp G6a Scheduled Skyway Security B1 - B16 Vans, Delta Checkpoint C19 - C27 G6b Check-in (Carry-on Concourse Tram General Parking Up to: Bags Only) GOLD Ramp Short Term Parking G7 BROWN Ramp G8 G9 BROWN Short GOLD Tram Exit from: G10 Term Ramp Legend International Parking RED Arrivals G11 Ramp TRANSIT CENTER Airline Clubs Limos G12 Metro and Charter Buses Armed Forces Lockers G13 Service Center G14 A1 - A14 ATM (Cash Machine) Lost and Found G15 LEVEL T Bicycle Rack Nursing Mothers/ Entrance/Exit Lactation Rooms for Light Rail Business Center Parking