A Baker's Dozen of Tips for Be Er Web Searches
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Duckduckgo Search Engines Android
Duckduckgo search engines android Continue 1 5.65.0 10.8MB DuckduckGo Privacy Browser 1 5.64.0 10.8MB DuckduckGo Privacy Browser 1 5.63.1 10.78MB DuckduckGo Privacy Browser 1 5.62.0 10.36MB DuckduckGo Privacy Browser 1 5.61.2 10.36MB DuckduckGo Privacy Browser 1 5.60.0 10.35MB DuckduckGo Privacy Browser 1 5.59.1 10.35MB DuckduckGo Privacy Browser 1 5.58.1 10.33MB DuckduckGo Privacy Browser 1 5.57.1 10.31MB DuckduckGo Privacy browser © DuckduckGo. Privacy, simplified. This article is about the search engine. For children's play, see duck, duck, goose. Internet search engine DuckDuckGoScreenshot home page DuckDuckGo on 2018Type search engine siteWeb Unavailable inMultilingualHeadquarters20 Paoli PikePaoli, Pennsylvania, USA Area servedWorldwideOwnerDuck Duck Go, Inc., createdGabriel WeinbergURLduckduckgo.comAlexa rank 158 (October 2020 update) CommercialRegregedSeptember 25, 2008; 12 years ago (2008-09-25) was an Internet search engine that emphasized the privacy of search engines and avoided the filter bubble of personalized search results. DuckDuckGo differs from other search engines by not profiling its users and showing all users the same search results for this search term. The company is based in Paoli, Pennsylvania, in Greater Philadelphia and has 111 employees since October 2020. The name of the company is a reference to the children's game duck, duck, goose. The results of the DuckDuckGo Survey are a compilation of more than 400 sources, including Yahoo! Search BOSS, Wolfram Alpha, Bing, Yandex, own web scanner (DuckDuckBot) and others. It also uses data from crowdsourcing sites, including Wikipedia, to fill in the knowledge panel boxes to the right of the results. -

EFF, Duckduckgo, and Internet Archive Amicus Brief
Case: 17-16783, 11/27/2017, ID: 10667942, DktEntry: 42, Page 1 of 39 NO. 17-16783 IN THE UNITED STATES COURT OF APPEALS FOR THE NINTH CIRCUIT HIQ LABS, INC., PLAINTIFF-APPELLEE, V. LINKEDIN CORPORATION, DEFENDANT-APPELLANT. On Appeal from the United States District Court for the Northern District of California Case No. 3:17-cv-03301-EMC The Honorable Edward M. Chen, District Court Judge BRIEF OF AMICI CURIAE ELECTRONIC FRONTIER FOUNDATION, DUCKDUCKGO, AND INTERNET ARCHIVE IN SUPPORT OF PLAINTIFF-APPELLEE Jamie Williams Corynne McSherry Cindy Cohn Nathan Cardozo ELECTRONIC FRONTIER FOUNDATION 815 Eddy Street San Francisco, CA 94109 Email: [email protected] Telephone: (415) 436-9333 Counsel for Amici Curiae Case: 17-16783, 11/27/2017, ID: 10667942, DktEntry: 42, Page 2 of 39 DISCLOSURE OF CORPORATE AFFILIATIONS AND OTHER ENTITIES WITH A DIRECT FINANCIAL INTEREST IN LITIGATION Pursuant to Rule 26.1 of the Federal Rules of Appellate Procedure, Amici Curiae Electronic Frontier Foundation, DuckDuckGo, and Internet Archive each individually state that they do not have a parent corporation and that no publicly held corporation owns 10 percent or more of their stock. i Case: 17-16783, 11/27/2017, ID: 10667942, DktEntry: 42, Page 3 of 39 TABLE OF CONTENTS CORPORATE DISCLOSURE STATEMENTS ..................................................... i TABLE OF CONTENTS ...................................................................................... ii TABLE OF AUTHORITIES ............................................................................... -
The Autonomous Surfer
Renée Ridgway The Autonomous Surfer CAIS Report Fellowship Mai bis Oktober 2018 GEFÖRDERT DURCH RIDGWAY The Autonomous Surfer Research Questions The Autonomous Surfer endeavoured to discover the unknown unknowns of alternative search through the following research questions: What are the alternatives to Google search? What are their hidden revenue models, even if they do not collect user data? How do they deliver divergent (and qualitative) results or knowledge? What are the criteria that determine ranking and relevance? How do p2p search engines such as YaCy work? Does it deliver alternative results compared to other search engines? Is there still a movement for a larger, public index? Can there be serendipitous search, which is the ability to come across books, articles, images, information, objects, and so forth, by chance? Aims and Projected Results My PhD research investigates Google search – its early development, its technological innovation, its business model of the past 20 years and how it works now. Furthermore, I have experimented with Tor (The Onion Router) in order to find out if I could be anonymous online, and if so, would I receive diver- gent results from Google with the same keywords. For my fellowship at CAIS I decided to first research search engines that were incorporated into the Tor browser as default (Startpage, Disconnect) or are the default browser now (DuckDuckGo). I then researched search engines in my original CAIS proposal that I had come across in my PhD but hadn’t had the time to research; some are from the Society of the Query Reader (2014) and others I found en route or on colleagues’ suggestions. -

GOGGLES: Democracy Dies in Darkness, and So Does the Web
GOGGLES: Democracy dies in darkness, and so does the Web Brave Search Team Brave Munich, Germany [email protected] Abstract of information has led to a significant transfer of power from cre- This paper proposes an open and collaborative system by which ators to aggregators. Access to information has been monopolized a community, or a single user, can create sets of rules and filters, by companies like Google and Facebook [27]. While everything is called Goggles, to define the space which a search engine can pull theoretically still retrievable, in practice we are looking at the world results from. Instead of a single ranking algorithm, we could have through the biases of a few providers, who act, unintentionally or as many as needed, overcoming the biases that a single actor (the not, as gatekeepers. Akin to the thought experiment about the tree search engine) embeds into the results. Transparency and openness, falling in the forest [3], if a page is not listed on Google’s results all desirable qualities, will become accessible through the deep re- page or in the Facebook feed, does it really exist? ranking capabilities Goggles would enable. Such system would be The biases of Google and Facebook, whether algorithmic, data made possible by the availability of a host search engine, providing induced, commercial or political dictate what version of the world the index and infrastructure, which are unlikely to be replicated we get to see. Reality becomes what the models we are fed depict without major development and infrastructure costs. Besides the it to be [24]. -

About Garlic and Onions a Little Journey…
About Garlic and Onions A little journey… Tobias Mayer, Technical Solutions Architect BRKSEC-2011 Cisco Webex Teams Questions? Use Cisco Webex Teams to chat with the speaker after the session How 1 Find this session in the Cisco Events Mobile App 2 Click “Join the Discussion” 3 Install Webex Teams or go directly to the team space 4 Enter messages/questions in the team space BRKSEC-2011 © 2020 Cisco and/or its affiliates. All rights reserved. Cisco Public 3 About Garlic and Onions We are all looking for privacy on the internet, for one or the other reason. This Session is about some technologies you can use to anonymise your network traffic, such as Tor (The Onion Router). The first part will give an introduction and explain the underlaying technology of Tor. We will take look at how you can not only use the Tor browser for access but also how the Tor network is working. We will learn how you can establish a Tor session and how we can find hidden websites and give examples of some websites...So we will enter the Darknet together. Beside Tor, we will also take a quick look at other techniques like I2P (Garlic Routing). In the last section we will make a quick sanity check what security technologies we can use to (maybe) detect such traffic in the network. This presentation is aimed at everyone who likes to learn about anonymization techniques and have a little bit of fun in the Darknet. BRKSEC-2011 © 2020 Cisco and/or its affiliates. All rights reserved. -

Mass Surveillance
Mass Surveillance Mass Surveillance What are the risks for the citizens and the opportunities for the European Information Society? What are the possible mitigation strategies? Part 1 - Risks and opportunities raised by the current generation of network services and applications Study IP/G/STOA/FWC-2013-1/LOT 9/C5/SC1 January 2015 PE 527.409 STOA - Science and Technology Options Assessment The STOA project “Mass Surveillance Part 1 – Risks, Opportunities and Mitigation Strategies” was carried out by TECNALIA Research and Investigation in Spain. AUTHORS Arkaitz Gamino Garcia Concepción Cortes Velasco Eider Iturbe Zamalloa Erkuden Rios Velasco Iñaki Eguía Elejabarrieta Javier Herrera Lotero Jason Mansell (Linguistic Review) José Javier Larrañeta Ibañez Stefan Schuster (Editor) The authors acknowledge and would like to thank the following experts for their contributions to this report: Prof. Nigel Smart, University of Bristol; Matteo E. Bonfanti PhD, Research Fellow in International Law and Security, Scuola Superiore Sant’Anna Pisa; Prof. Fred Piper, University of London; Caspar Bowden, independent privacy researcher; Maria Pilar Torres Bruna, Head of Cybersecurity, Everis Aerospace, Defense and Security; Prof. Kenny Paterson, University of London; Agustín Martin and Luis Hernández Encinas, Tenured Scientists, Department of Information Processing and Cryptography (Cryptology and Information Security Group), CSIC; Alessandro Zanasi, Zanasi & Partners; Fernando Acero, Expert on Open Source Software; Luigi Coppolino,Università degli Studi di Napoli; Marcello Antonucci, EZNESS srl; Rachel Oldroyd, Managing Editor of The Bureau of Investigative Journalism; Peter Kruse, Founder of CSIS Security Group A/S; Ryan Gallagher, investigative Reporter of The Intercept; Capitán Alberto Redondo, Guardia Civil; Prof. Bart Preneel, KU Leuven; Raoul Chiesa, Security Brokers SCpA, CyberDefcon Ltd.; Prof. -
Applying Library Values to Emerging Technology Decision-Making in the Age of Open Access, Maker Spaces, and the Ever-Changing Library
ACRL Publications in Librarianship No. 72 Applying Library Values to Emerging Technology Decision-Making in the Age of Open Access, Maker Spaces, and the Ever-Changing Library Editors Peter D. Fernandez and Kelly Tilton Association of College and Research Libraries A division of the American Library Association Chicago, Illinois 2018 The paper used in this publication meets the minimum requirements of Ameri- can National Standard for Information Sciences–Permanence of Paper for Print- ed Library Materials, ANSI Z39.48-1992. ∞ Cataloging-in-Publication data is on file with the Library of Congress. Copyright ©2018 by the Association of College and Research Libraries. All rights reserved except those which may be granted by Sections 107 and 108 of the Copyright Revision Act of 1976. Printed in the United States of America. 22 21 20 19 18 5 4 3 2 1 Contents Contents Introduction .......................................................................................................ix Peter Fernandez, Head, LRE Liaison Programs, University of Tennessee Libraries Kelly Tilton, Information Literacy Instruction Librarian, University of Tennessee Libraries Part I Contemplating Library Values Chapter 1. ..........................................................................................................1 The New Technocracy: Positioning Librarianship’s Core Values in Relationship to Technology Is a Much Taller Order Than We Think John Buschman, Dean of University Libraries, Seton Hall University Chapter 2. ........................................................................................................27 -

Online-Quellen Nutzen: Recherche Im Internet
ONLINE-QUELLEN NUTZEN: RECHERCHE IM INTERNET Katharina Gilarski, Verena Müller, Martin Nissen (Stand: 08/2020) Inhaltsverzeichnis 1 Recherche mit Universalsuchmaschinen ............................................................. 2 1.1 Clever googlen ......................................................................................................... 2 1.2 Suchoperatoren für die einfache Suche ................................................................... 2 1.3 Die erweiterte Suche mit Google .............................................................................. 3 1.4 Die umgekehrte Bildersuche mit Google .................................................................. 4 1.5 Das Geheimnis der Treffersortierung in Google ....................................................... 5 1.6 Alternative universelle Suchmaschinen .................................................................... 6 1.7 Surface vs. Deep Web ............................................................................................. 9 1.8 Vor- und Nachteile von universellen Suchmaschinen ............................................. 10 1.9 Bewertung von Internetquellen ............................................................................... 10 2 Recherche mit wissenschaftlichen Suchmaschinen ......................................... 11 2.1 Google Scholar: Googles Suchmaschine für Wissenschaftler ................................ 11 2.2 Suchmöglichkeiten von Google Scholar ................................................................ -

Merging Multiple Search Results Approach for Meta-Search Engines
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by D-Scholarship@Pitt MERGING MULTIPLE SEARCH RESULTS APPROACH FOR META-SEARCH ENGINES By Khaled Abd-El-Fatah Mohamed B.S-------- Cairo University, Egypt, 1995 M.A-------Cairo University, Egypt, 1999 M.A------- University of Pittsburgh 2001 Submitted to the Graduate Faculty of School of Information Sciences in Partial Fulfillment of the requirements for the degree of Doctor of Philosophy University of Pittsburgh 2004 UNIVERSITY OF PITTSBURGH INFORMATION SCIENCES This dissertation was presented by Khaled Abd-El-Fatah Mohamed It was defended on Janauary 29, 2004 and approved by Chris Tomer, PhD, Associate Professor, DLIS Jose-Marie Griffiths, PhD, Professor, DLIS Don King, Research Professor, DLIS Amy Knapp, PhD, ULS Dissertation Director: Chris Tomer, PhD, Associate Professor MERGING MULTIPLE SEARCH RESULTS APPROACH FOR META-SEARCH ENGINES Khaled A. Mohamed, PhD University of Pittsburgh, 2004 Meta Search Engines are finding tools developed for enhancing the search performance by submitting user queries to multiple search engines and combining the search results in a unified ranked list. They utilized data fusion technique, which requires three major steps: databases selection, the results combination, and the results merging. This study tries to build a framework that can be used for merging the search results retrieved from any set of search engines. This framework based on answering three major questions: 1. How meta-search developers could define the optimal rank order for the selected engines. 2. How meta-search developers could choose the best search engines combination. 3. What is the optimal heuristic merging function that could be used for aggregating the rank order of the retrieved documents form incomparable search engines. -

BRKSEC-2011.Pdf
#CLUS About Garlic and Onions A little journey… Tobias Mayer, Technical Solutions Architect BRKSEC-2011 #CLUS Me… CCIE Security #14390, CISSP & Motorboat driving license… Working in Content Security & TLS Security tmayer{at}cisco.com Writing stuff at “blogs.cisco.com” #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 3 Agenda • Why anonymization? • Using Tor (Onion Routing) • How Tor works • Introduction to Onion Routing • Obfuscation within Tor • Domain Fronting • Detect Tor • I2P – Invisible Internet Project • Introduction to Garlic Routing • Conclusion #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 4 Cisco Webex Teams Questions? Use Cisco Webex Teams (formerly Cisco Spark) to chat with the speaker after the session How 1 Find this session in the Cisco Events App 2 Click “Join the Discussion” 3 Install Webex Teams or go directly to the team space 4 Enter messages/questions in the team space Webex Teams will be moderated cs.co/ciscolivebot#BRKSEC-2011 by the speaker until June 18, 2018. #CLUS © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 5 Different Intentions Hide me from Government! Hide me from ISP! Hide me from tracking! Bypass Corporate Bypass Country Access Hidden policies restrictions (Videos…) Services #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 6 Browser Identity Tracking does not require a “Name” Tracking is done by examining parameters your browser reveals https://panopticlick.eff.org #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 7 Proxies EPIC Browser #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. -

Unveiling the I2P Web Structure: a Connectivity Analysis
Unveiling the I2P web structure: a connectivity analysis Roberto Magan-Carri´ on,´ Alberto Abellan-Galera,´ Gabriel Macia-Fern´ andez´ and Pedro Garc´ıa-Teodoro Network Engineering & Security Group Dpt. of Signal Theory, Telematics and Communications - CITIC University of Granada - Spain Email: [email protected], [email protected], [email protected], [email protected] Abstract—Web is a primary and essential service to share the literature have analyzed the content and services offered information among users and organizations at present all over through this kind of technologies [6], [7], [2], as well as the world. Despite the current significance of such a kind of other relevant aspects like site popularity [8], topology and traffic on the Internet, the so-called Surface Web traffic has been estimated in just about 5% of the total. The rest of the dimensions [9], or classifying network traffic and darknet volume of this type of traffic corresponds to the portion of applications [10], [11], [12], [13], [14]. Web known as Deep Web. These contents are not accessible Two of the most popular darknets at present are The Onion by search engines because they are authentication protected Router (TOR; https://www.torproject.org/) and The Invisible contents or pages that are only reachable through the well Internet Project (I2P;https://geti2p.net/en/). This paper is fo- known as darknets. To browse through darknets websites special authorization or specific software and configurations are needed. cused on exploring and investigating the contents and structure Despite TOR is the most used darknet nowadays, there are of the websites in I2P, the so-called eepsites. -
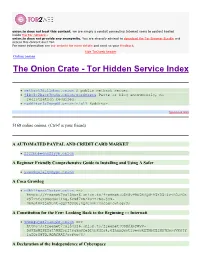
The Onion Crate - Tor Hidden Service Index Protected Onions Add New
onion.to does not host this content; we are simply a conduit connecting Internet users to content hosted inside the Tor network.. onion.to does not provide any anonymity. You are strongly advised to download the Tor Browser Bundle and access this content over Tor. For more information see our website for more details and send us your feedback. hide Tor2web header Online onions The Onion Crate - Tor Hidden Service Index Protected onions Add new nethack3dzllmbmo.onion A public nethack server. j4ko5c2kacr3pu6x.onion/wordpress Paste or blog anonymously, no registration required. redditor3a2spgd6.onion/r/all Redditor. Sponsored links 5168 online onions. (Ctrl-f is your friend) A AUTOMATED PAYPAL AND CREDIT CARD MARKET 2222bbbeonn2zyyb.onion A Beginner Friendly Comprehensive Guide to Installing and Using A Safer yuxv6qujajqvmypv.onion A Coca Growlog rdkhliwzee2hetev.onion ==> https://freenet7cul5qsz6.onion.to/freenet:USK@yP9U5NBQd~h5X55i4vjB0JFOX P97TAtJTOSgquP11Ag,6cN87XSAkuYzFSq-jyN- 3bmJlMPjje5uAt~gQz7SOsU,AQACAAE/cocagrowlog/3/ A Constitution for the Few: Looking Back to the Beginning ::: Internati 5hmkgujuz24lnq2z.onion ==> https://freenet7cul5qsz6.onion.to/freenet:USK@kpFWyV- 5d9ZmWZPEIatjWHEsrftyq5m0fe5IybK3fg4,6IhxxQwot1yeowkHTNbGZiNz7HpsqVKOjY 1aZQrH8TQ,AQACAAE/acftw/0/ A Declaration of the Independence of Cyberspace ufbvplpvnr3tzakk.onion ==> https://freenet7cul5qsz6.onion.to/freenet:CHK@9NuTb9oavt6KdyrF7~lG1J3CS g8KVez0hggrfmPA0Cw,WJ~w18hKJlkdsgM~Q2LW5wDX8LgKo3U8iqnSnCAzGG0,AAIC-- 8/Declaration-Final%5b1%5d.html A Dumps Market