Linux Programming
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Unix (And Linux)
AWK....................................................................................................................................4 BC .....................................................................................................................................11 CHGRP .............................................................................................................................16 CHMOD.............................................................................................................................19 CHOWN ............................................................................................................................26 CP .....................................................................................................................................29 CRON................................................................................................................................34 CSH...................................................................................................................................36 CUT...................................................................................................................................71 DATE ................................................................................................................................75 DF .....................................................................................................................................79 DIFF ..................................................................................................................................84 -
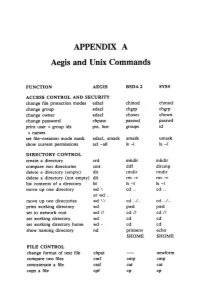
APPENDIX a Aegis and Unix Commands
APPENDIX A Aegis and Unix Commands FUNCTION AEGIS BSD4.2 SYSS ACCESS CONTROL AND SECURITY change file protection modes edacl chmod chmod change group edacl chgrp chgrp change owner edacl chown chown change password chpass passwd passwd print user + group ids pst, lusr groups id +names set file-creation mode mask edacl, umask umask umask show current permissions acl -all Is -I Is -I DIRECTORY CONTROL create a directory crd mkdir mkdir compare two directories cmt diff dircmp delete a directory (empty) dlt rmdir rmdir delete a directory (not empty) dlt rm -r rm -r list contents of a directory ld Is -I Is -I move up one directory wd \ cd .. cd .. or wd .. move up two directories wd \\ cd . ./ .. cd . ./ .. print working directory wd pwd pwd set to network root wd II cd II cd II set working directory wd cd cd set working directory home wd- cd cd show naming directory nd printenv echo $HOME $HOME FILE CONTROL change format of text file chpat newform compare two files emf cmp cmp concatenate a file catf cat cat copy a file cpf cp cp Using and Administering an Apollo Network 265 copy std input to std output tee tee tee + files create a (symbolic) link crl In -s In -s delete a file dlf rm rm maintain an archive a ref ar ar move a file mvf mv mv dump a file dmpf od od print checksum and block- salvol -a sum sum -count of file rename a file chn mv mv search a file for a pattern fpat grep grep search or reject lines cmsrf comm comm common to 2 sorted files translate characters tic tr tr SHELL SCRIPT TOOLS condition evaluation tools existf test test -

GNU Coreutils Cheat Sheet (V1.00) Created by Peteris Krumins ([email protected], -- Good Coders Code, Great Coders Reuse)
GNU Coreutils Cheat Sheet (v1.00) Created by Peteris Krumins ([email protected], www.catonmat.net -- good coders code, great coders reuse) Utility Description Utility Description arch Print machine hardware name nproc Print the number of processors base64 Base64 encode/decode strings or files od Dump files in octal and other formats basename Strip directory and suffix from file names paste Merge lines of files cat Concatenate files and print on the standard output pathchk Check whether file names are valid or portable chcon Change SELinux context of file pinky Lightweight finger chgrp Change group ownership of files pr Convert text files for printing chmod Change permission modes of files printenv Print all or part of environment chown Change user and group ownership of files printf Format and print data chroot Run command or shell with special root directory ptx Permuted index for GNU, with keywords in their context cksum Print CRC checksum and byte counts pwd Print current directory comm Compare two sorted files line by line readlink Display value of a symbolic link cp Copy files realpath Print the resolved file name csplit Split a file into context-determined pieces rm Delete files cut Remove parts of lines of files rmdir Remove directories date Print or set the system date and time runcon Run command with specified security context dd Convert a file while copying it seq Print sequence of numbers to standard output df Summarize free disk space setuidgid Run a command with the UID and GID of a specified user dir Briefly list directory -

UNIX Administration Course
UNIX Administration Course Copyright 1999 by Ian Mapleson BSc. Version 1.0 [email protected] Tel: (+44) (0)1772 893297 Fax: (+44) (0)1772 892913 WWW: http://www.futuretech.vuurwerk.nl/ Detailed Notes for Day 1 (Part 3) UNIX Fundamentals: File Ownership UNIX has the concept of file ’ownership’: every file has a unique owner, specified by a user ID number contained in /etc/passwd. When examining the ownership of a file with the ls command, one always sees the symbolic name for the owner, unless the corresponding ID number does not exist in the local /etc/passwd file and is not available by any system service such as NIS. Every user belongs to a particular group; in the case of the SGI system I run, every user belongs to either the ’staff’ or ’students’ group (note that a user can belong to more than one group, eg. my network has an extra group called ’projects’). Group names correspond to unique group IDs and are listed in the /etc/group file. When listing details of a file, usually the symbolic group name is shown, as long as the group ID exists in the /etc/group file, or is available via NIS, etc. For example, the command: ls -l / shows the full details of all files in the root directory. Most of the files and directories are owned by the root user, and belong to the group called ’sys’ (for system). An exception is my home account directory /mapleson which is owned by me. Another example command: ls -l /home/staff shows that every staff member owns their particular home directory. -

The Linux Command Line
The Linux Command Line Second Internet Edition William E. Shotts, Jr. A LinuxCommand.org Book Copyright ©2008-2013, William E. Shotts, Jr. This work is licensed under the Creative Commons Attribution-Noncommercial-No De- rivative Works 3.0 United States License. To view a copy of this license, visit the link above or send a letter to Creative Commons, 171 Second Street, Suite 300, San Fran- cisco, California, 94105, USA. Linux® is the registered trademark of Linus Torvalds. All other trademarks belong to their respective owners. This book is part of the LinuxCommand.org project, a site for Linux education and advo- cacy devoted to helping users of legacy operating systems migrate into the future. You may contact the LinuxCommand.org project at http://linuxcommand.org. This book is also available in printed form, published by No Starch Press and may be purchased wherever fine books are sold. No Starch Press also offers this book in elec- tronic formats for most popular e-readers: http://nostarch.com/tlcl.htm Release History Version Date Description 13.07 July 6, 2013 Second Internet Edition. 09.12 December 14, 2009 First Internet Edition. 09.11 November 19, 2009 Fourth draft with almost all reviewer feedback incorporated and edited through chapter 37. 09.10 October 3, 2009 Third draft with revised table formatting, partial application of reviewers feedback and edited through chapter 18. 09.08 August 12, 2009 Second draft incorporating the first editing pass. 09.07 July 18, 2009 Completed first draft. Table of Contents Introduction....................................................................................................xvi -

Gnu Coreutils Core GNU Utilities for Version 5.93, 2 November 2005
gnu Coreutils Core GNU utilities for version 5.93, 2 November 2005 David MacKenzie et al. This manual documents version 5.93 of the gnu core utilities, including the standard pro- grams for text and file manipulation. Copyright c 1994, 1995, 1996, 2000, 2001, 2002, 2003, 2004, 2005 Free Software Foundation, Inc. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.1 or any later version published by the Free Software Foundation; with no Invariant Sections, with no Front-Cover Texts, and with no Back-Cover Texts. A copy of the license is included in the section entitled “GNU Free Documentation License”. Chapter 1: Introduction 1 1 Introduction This manual is a work in progress: many sections make no attempt to explain basic concepts in a way suitable for novices. Thus, if you are interested, please get involved in improving this manual. The entire gnu community will benefit. The gnu utilities documented here are mostly compatible with the POSIX standard. Please report bugs to [email protected]. Remember to include the version number, machine architecture, input files, and any other information needed to reproduce the bug: your input, what you expected, what you got, and why it is wrong. Diffs are welcome, but please include a description of the problem as well, since this is sometimes difficult to infer. See section “Bugs” in Using and Porting GNU CC. This manual was originally derived from the Unix man pages in the distributions, which were written by David MacKenzie and updated by Jim Meyering. -

Adding Users
Adding Users Mechanically, the process of adding a new user consists of three steps required by the system, two steps that establish a useful environment for the new user and several extra steps for your own convenience as a sysadmin. Required: Edit the passwd and shadow files to define the user’s account Set an initial password Create the user’s home directory For the user: Copy default startup files to the user’s home directory Set the user’s mail home and establish mail aliases For the sysadmin: Add the user to the /etc/group file Configure disk quotas if you have them Verify that the account is set up correctly Solaris provides tools that can do some of these steps for you. The next section contains the steps that you will need to do by hand. You must perform each step as root or use a program such as sudo that allows you to run commands as root. Editing the passwd and shadow Files To safely edit the passwd file, use vipw to invoke a text editor on a copy of /etc/passwd. The default editor is vi, but you can specify a different one by setting the value of the EDITOR environment variable. The existence of the temporary edit file serves as a lock. vipw allows only one person to edit the passwd file at a time. When the editor terminates, vipw replaces the original passwd file with your edited copy of it. On Solaris systems vipw will ask if you want to edit the shadow file after you have edited the passwd file. -

Gnu Coreutils Core GNU Utilities for Version 6.9, 22 March 2007
gnu Coreutils Core GNU utilities for version 6.9, 22 March 2007 David MacKenzie et al. This manual documents version 6.9 of the gnu core utilities, including the standard pro- grams for text and file manipulation. Copyright c 1994, 1995, 1996, 2000, 2001, 2002, 2003, 2004, 2005, 2006 Free Software Foundation, Inc. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or any later version published by the Free Software Foundation; with no Invariant Sections, with no Front-Cover Texts, and with no Back-Cover Texts. A copy of the license is included in the section entitled \GNU Free Documentation License". Chapter 1: Introduction 1 1 Introduction This manual is a work in progress: many sections make no attempt to explain basic concepts in a way suitable for novices. Thus, if you are interested, please get involved in improving this manual. The entire gnu community will benefit. The gnu utilities documented here are mostly compatible with the POSIX standard. Please report bugs to [email protected]. Remember to include the version number, machine architecture, input files, and any other information needed to reproduce the bug: your input, what you expected, what you got, and why it is wrong. Diffs are welcome, but please include a description of the problem as well, since this is sometimes difficult to infer. See section \Bugs" in Using and Porting GNU CC. This manual was originally derived from the Unix man pages in the distributions, which were written by David MacKenzie and updated by Jim Meyering. -
Etrust SSO Selang Command Reference Guide the Selang Command Shell
eTrust Single Sign-On selang Command Reference Guide 7.0 G00108-2E This documentation and related computer software program (hereinafter referred to as the “Documentation”) is for the end user’s informational purposes only and is subject to change or withdrawal by Computer Associates International, Inc. (“CA”) at any time. This documentation may not be copied, transferred, reproduced, disclosed or duplicated, in whole or in part, without the prior written consent of CA. This documentation is proprietary information of CA and protected by the copyright laws of the United States and international treaties. Notwithstanding the foregoing, licensed users may print a reasonable number of copies of this documentation for their own internal use, provided that all CA copyright notices and legends are affixed to each reproduced copy. Only authorized employees, consultants, or agents of the user who are bound by the confidentiality provisions of the license for the software are permitted to have access to such copies. This right to print copies is limited to the period during which the license for the product remains in full force and effect. Should the license terminate for any reason, it shall be the user’s responsibility to return to CA the reproduced copies or to certify to CA that same have been destroyed. To the extent permitted by applicable law, CA provides this documentation “as is” without warranty of any kind, including without limitation, any implied warranties of merchantability, fitness for a particular purpose or noninfringement. In no event will CA be liable to the end user or any third party for any loss or damage, direct or indirect, from the use of this documentation, including without limitation, lost profits, business interruption, goodwill, or lost data, even if CA is expressly advised of such loss or damage. -

Using Custom Users/Groups in Yocto
Scott Garman <[email protected]> 1 Previously, custom users/groups could only be created in postinstall scripts run at image first boot There was no framework to ensure that these user/group additions were not in conflict with other packages As a result, almost no recipes made use of this, so nearly everything in our rootfs images were owned by root:root 2 System daemons in particular make heavy use of custom users/groups in order to enforce privilege separation – a fundamental security model The lack of this feature has been a significant flaw with Yocto until now 3 A recipe needs to be able to define: ◦ One or more custom user names ◦ One or more custom group names ◦ Associate any/all files in a package with the above users/groups ◦ Allow for full control over the useradd/groupadd commands (e.g, specify home directory and other options) ◦ Cannot require builds to be run with root privileges (i.e, make appropriate use of pseudo) 4 Logic is encapsulated in useradd.bbclass A custom /etc/passwd and /etc/group are maintained in the target sysroot during builds Pseudo has a PSEUDO_PASSWD environment variable which is pointed to the target sysroot The useradd and groupadd utilities from shadow-native are run under pseudo when generating images Package preinstall scripts are generated which run when a package is manually installed on the target 5 Example recipe can be found in meta- skeleton/recipes-skeleton/useradd/ inherit useradd Specify output packages which include custom users/groups in the USERADD_PACKAGES variable -
Linux Command Cheat Sheet
Linux commands cheat sheet Basic navigation Command Purpose Examples cd change working directory cd .. Change to parent directory cd /course/cs017 Change to /course/cs017 cd - Change to previous directory cd ~/course Change to /home/YOUR_USERNAME/course cd ~dap/pub Change to /home/dap/pub ls list files in a directory ls list files in current directory ls dir1 list files in dir1 ls -l dir1 show details for each file in dir1 ls -a dir1 show all files (even hidden files) pwd print the current working directory©s name People Command Purpose Examples floor see who©s logged in where floor ta print a map of who©s logged into TA areas finger find out about a person finger dap snoop find out about a person snoop dap anyone find your friends logged in anyone Add logins, 1 per line to your ~/.anyone zwrite send a message to a person zwrite dap su switch to user Don©t use this. Use sux. sux switch to user (can use graphical apps) sux ± dap Switch to user ©dap© Permissions Command Purpose Examples chgrp change the group which owns a file chgrp GROUP file Change group of ©file© to GROUP chmod change the user who owns a file chmod MODE file Change mode of ©file© to MODE umask change your umask umask MODE Change default umask to MODE Use "man <command>" for more details [email protected] Page 1/2 Linux commands cheat sheet Specific file types Command Purpose Command Purpose acroread Views pdf files gzip/gunzip Gzip compression xpdf Views pdf files zip/unzip Windows-compatible compression xdvi Views dvi files gv Views postscript files (.ps) Miscellaneous -

User Commands Chown ( 1 ) Chown – Change File Ownership Chown [-Fhr
User Commands chown ( 1 ) NAME chown – change file ownership SYNOPSIS chown [-fhR] owner [ : group] file... DESCRIPTION The chown utility will set the user ID of the file named by each file to the user ID specified by owner, and, optionally, will set the group ID to that specified by group. If chown is invoked by other than the super-user, the set-user-ID bit is cleared. Only the owner of a file (or the super-user) may change the owner of that file. The operating system has a configuration option {_POSIX_CHOWN_RESTRICTED}, to restrict own- ership changes. When this option is in effect the owner of the file is prevented from changing the owner ID of the file. Only the super-user can arbitrarily change owner IDs whether or not this option is in effect. To set this configuration option, include the following line in /etc/system: set rstchown = 1 To disable this option, include the following line in /etc/system: set rstchown = 0 {_POSIX_CHOWN_RESTRICTED} is enabled by default. See system(4) and fpathconf(2). OPTIONS The following options are supported: -f Do not report errors. -h If the file is a symbolic link, change the owner of the symbolic link. Without this option, the owner of the file referenced by the symbolic link is changed. -R Recursive. chown descends through the directory, and any subdirectories, setting the ownership ID as it proceeds. When a symbolic link is encountered, the owner of the target file is changed (unless the -h option is specified), but no recursion takes place. OPERANDS The following operands are supported: owner[: group] A user ID and optional group ID to be assigned to file.