Mobile Privacy: Tor on the Iphone and Other Unusual Devices
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Tor and Circumvention: Lessons Learned
Tor and circumvention: Lessons learned Nick Mathewson The Tor Project https://torproject.org/ 1 What is Tor? Online anonymity 1) open source software, 2) network, 3) protocol Community of researchers, developers, users, and relay operators Funding from US DoD, Electronic Frontier Foundation, Voice of America, Google, NLnet, Human Rights Watch, NSF, US State Dept, SIDA, ... 2 The Tor Project, Inc. 501(c)(3) non-profit organization dedicated to the research and development of tools for online anonymity and privacy Not secretly evil. 3 Estimated ~250,000? daily Tor users 4 Anonymity in what sense? “Attacker can’t learn who is talking to whom.” Bob Alice Alice Anonymity network Bob Alice Bob 5 Threat model: what can the attacker do? Alice Anonymity network Bob watch Alice! watch (or be!) Bob! Control part of the network! 6 Anonymity isn't cryptography: Cryptography just protects contents. “Hi, Bob!” “Hi, Bob!” Alice <gibberish> attacker Bob 7 Anonymity isn't just wishful thinking... “You can't prove it was me!” “Promise you won't look!” “Promise you won't remember!” “Promise you won't tell!” “I didn't write my name on it!” “Isn't the Internet already anonymous?” 8 Anonymity serves different interests for different user groups. Anonymity “It's privacy!” Private citizens 9 Anonymity serves different interests for different user groups. Anonymity Businesses “It's network security!” “It's privacy!” Private citizens 10 Anonymity serves different interests for different user groups. “It's traffic-analysis resistance!” Governments Anonymity Businesses “It's network security!” “It's privacy!” Private citizens 11 Anonymity serves different interests for different user groups. -

Wireless Mesh Networks 10 Steps to Speedup Your Mesh-Network by Factor 5
Overview CPU/Architecture Airtime Compression Cache QoS future wireless mesh networks 10 steps to speedup your mesh-network by factor 5 Bastian Bittorf http://www.bittorf-wireless.com berlin, c-base, 4. june 2011 B.Bittorf bittorf wireless )) mesh networking Overview CPU/Architecture Airtime Compression Cache QoS future 1 Agenda 2 CPU/Architecture efficient use of CPU rate-selection 3 Airtime avoid slow rates separate channels 4 Compression like modem: V.42bis iproute2/policy-routing compress data to inet-gateway slow DSL-lines? 5 Cache local HTTP-Proxy Gateway HTTP-Proxy B.Bittorf DNS-Cache bittorf wireless )) mesh networking synchronise everything compress to zero 6 QoS Layer8 7 future ideas ressources Overview CPU/Architecture Airtime Compression Cache QoS future 1 Agenda 2 CPU/Architecture efficient use of CPU rate-selection 3 Airtime avoid slow rates separate channels 4 Compression like modem: V.42bis iproute2/policy-routing compress data to inet-gateway slow DSL-lines? 5 Cache local HTTP-Proxy Gateway HTTP-Proxy B.Bittorf DNS-Cache bittorf wireless )) mesh networking synchronise everything compress to zero 6 QoS Layer8 7 future ideas ressources Overview CPU/Architecture Airtime Compression Cache QoS future 1 Agenda 2 CPU/Architecture efficient use of CPU rate-selection 3 Airtime avoid slow rates separate channels 4 Compression like modem: V.42bis iproute2/policy-routing compress data to inet-gateway slow DSL-lines? 5 Cache local HTTP-Proxy Gateway HTTP-Proxy B.Bittorf DNS-Cache bittorf wireless )) mesh networking synchronise everything -

Freelab: a Free Experimentation Platform
FreeLab: A Free Experimentation Platform Matteo Varvello|; Diego Perino? |AT&T Labs – Research, ?Telefónica Research ABSTRACT In this work, we set out to build a free experimentation As researchers, we are aware of how hard it is to obtain access platform which can also be reliable and up-to-date. In classic to vantage points in the Internet. Experimentation platforms experimentation platforms applications run directly at vantage are useful tools, but they are also: 1) paid, either via a mem- points; we revert this rationale by proposing to use vantage bership fee or by resource sharing, 2) unreliable, nodes come points as traffic relays while running the application at theex- and go, 3) outdated, often still run on their original hardware perimenter’s machine(s). By leveraging free Internet relays as and OS. While one could build yet-another platform with vantage points, we can make such experimentation platform up-to-date and reliable hardware and software, it is hard to free. The drawback of this approach is the introduction of imagine one which is free. This is the goal of this paper: we extra errors (path inflation, header manipulation, bandwidth set out to build FreeLab, a free experimentation platform shrinkage) which need to be carefully corrected. which also aims to be reliable and up-to-date. The key idea This paper presents FreeLab, a free experimentation plat- behind FreeLab is that experiments run directly at its user form built atop of thousand of free HTTP(S) and SOCKS(5) machines, while traffic is relayed by free vantage points inthe Internet proxies [38]—to enable experiments based on TCP, Internet (web and SOCKS proxies, and DNS resolvers). -
Attacking Tor at the Application Layer
Attacking Tor at the Application Layer Gregory Fleischer gfl[email protected] http://pseudo-flaw.net/ Friday, July 31, 2009 Introduction Friday, July 31, 2009 Introduction • What this talk is about • identifying Tor web traffic • fingerprinting users • attacking at the application layers • There is a heavy emphasis on the client- side, web browsers attacks and JavaScript Friday, July 31, 2009 Introduction • What this talk is NOT about • passive monitoring at exit nodes • network attacks against path selection • using application functionality to increase the likelihood of network attacks • breaking SSL Friday, July 31, 2009 Introduction • Software tested • The Tor Browser Bundle • Vidalia Bundle for Windows • Vidalia Bundle for Mac OS X • Firefox 2, Firefox 3.0 and Firefox 3.5 • Torbutton • miscellaneous add-ons Friday, July 31, 2009 Does your browser... Friday, July 31, 2009 ... look like this? Friday, July 31, 2009 Background Friday, July 31, 2009 Background • Brief overview of Tor • free software developed by The Tor Project • volunteer effort on the Internet and anyone can run a Tor server • uses onion routing and encryption to provide network anonymity • can be used to circumvent local ISP surveillance and network blocking • can also be used to hide originating IP address from remote servers Friday, July 31, 2009 Friday, July 31, 2009 Background • Application stack for Tor web surfing • web browser (most likely Firefox) • local HTTP proxy (Privoxy or Polipo) • Tor client as SOCKS proxy • Tor exit node proxies request • remote web server -
Bsdploy Documentation Release 2.4.0.Dev0
bsdploy Documentation Release 2.4.0.dev0 Tom Lazar Dec 22, 2017 Contents 1 Main Features 3 2 How it works 5 3 Example Session 7 4 Best of both worlds 9 5 Under the hood 11 6 Full documentation 13 7 Dive in 15 7.1 Client requirements........................................... 15 7.2 Server requirements........................................... 15 7.3 Client Installation............................................ 16 7.4 Quickstart................................................ 17 8 Tutorial 23 8.1 Tutorial.................................................. 23 8.2 Webserver................................................ 24 8.3 Transmission............................................... 27 8.4 Staging.................................................. 29 9 Setup 31 9.1 Overview................................................. 31 9.2 Bootstrapping.............................................. 38 9.3 Configuring a jailhost.......................................... 42 10 General usage 45 10.1 Managing jails.............................................. 45 10.2 Ansible integration............................................ 46 10.3 Fabric integration............................................. 48 10.4 Combining Ansible and Fabric...................................... 49 11 Special use cases 51 11.1 Staging.................................................. 51 11.2 Updating................................................. 53 i 11.3 Customizing bootstrap.......................................... 53 12 Contribute 55 13 License 57 14 TODO 59 ii bsdploy -
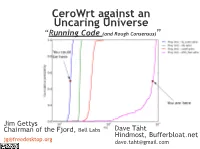
Cerowrt Against an Uncaring Universe “Running Code (And Rough Consensus)”
CeroWrt against an Uncaring Universe “Running Code (and Rough Consensus)” Jim Gettys Chairman of the Fjord, Bell Labs Dave Täht Hindmost, Bufferbloat.net [email protected] [email protected] March, 2011: Bufferbloat project starts CeroWrt ● We needed to attack the bufferbloat problem at the theory, OS, network stack and engineering level. ● In particular, we needed to know new algorithms were deployable on consumer hw and edge devices ● And we needed some ground truth about what was in the marketplace – in other words Why did home gateways suck so badly? The sad Ground Truth on home CPE and home routers ● Vendors shipping 5+ year old kernels (2.6.32? WTF?) and often even older packages ● Operating on razor thin margins... with no perceived demand for features like IPv6 ● Most coding outsourced... but usually dependent on ancient ports by the chip vendor ● Total disconnect between retail, academia, ISPs, IETF, and hw vendors ● Binary blobs everywhere resulting in field non-updateble firmware. ● Result: GRIDLOCK. How to get obsolete software fixed on CPE? ● Open Resolver ● 350051 'skbroadband' ● 236311 'dnsmasq-2.40' Released 10 YEARS AGO ● 212406 '.' ● ● 187012 'Nominum Vantio 5.3.0.0' Note: DNSMasq runs on about a ● 169557 'TelecomItaliaDNS' billion boxes ! now – home and ● 168460 'PowerDNS Recursor 3.3 $Id: ● 159537 'Go away!' commercial routers, a ton of CPE, ● 158940 'Cyber World Leader Kornet!' ● 151151 'DNS server' used heavily in Virtual Machines, ● 136084 'N/A' it's the default in ubuntu, and, um, ● 125645 'Nominum Vantio 5.3.2.2' ● 123798 '9.7.3' android uses it. ● 119653 'cdns5-asd2-1-100823-1441' ● 104603 'Dns Server' ● ● 95402 'unknown' ● 87458 'dnsmasq-2.52' ● And it's not broken here, just ● 76437 'x.x.x' ● 74282 'None of your business' misconfigured by the vendor.. -

Analisa Kecepatan Proxy Squid, Safesquid Dan Polipo Pada Ubuntu Server
Jurnal Emitor Vol. 13 No. 02 ISSN 1411-8890 ANALISA KECEPATAN PROXY SQUID, SAFESQUID DAN POLIPO PADA UBUNTU SERVER Fatah Yasin Al Irsyadi, Yusuf Sulistyo Nugroho, Dadik Wuryanto Teknik Informatika, Fakultas Komunikasi dan Informatika Universitas Muhammadiyah Surakarta Jl. A. Yani Tromol Pos 1 Pabelan Kartasura – Surakarta [email protected] ABSTRAKSI Bagi masyarakat modern, internet merupakan kebutuhan primer dan mempunyai peranan yang begitu penting. Ada beberapa hal pokok yang perlu dipertimbangkan ketika menggunakan internet, antara lain biaya dan kecepatan, karena berkaitan dengan efisiensi materi dan waktu. Banyak usaha yang dilakukan untuk mendapatkan efisiensi materi dan waktu. Penggunaan cache proxy server merupakan salah satu solusi untuk meningkatkan efisiensi. Data internet yang melalui cache proxy server disimpan dalam cache. Suatu saat ketika data tersebut diminta kembali oleh client yang sama atau client lain maka tinggal mengambil yang tersedia pada cache dan server proxy tidak perlu mengambil data dari server web aslinya. Penelitian ini melakukan pembandingan beberapa sistem operasi pada proxy server yaitu squid, safesquid dan polipo untuk mendapatkan sistem operasi proxy server yang cocok pada jaringan yang dirancang. Ketiga system operasi tersebut akan diuji dan dibandingkan kehandalannya dan performanya sebagai cache proxy server, dengan cara mengamati kecepatan ketiga-tiganya ketika membuka seluruh konten website. Stopwatch numion yang merupakan tool online yang tersedia pada website www.numion.com digunakan untuk membandingkan kecepatan membuka seluruh konten website . Browser yang digunakan adalah mozilla firefox dengan 3 client, sedangkan file yang akan diproses adalah file teks berformat html. Berdasarkan rancangan yang telah diimplementasikan, proxy server ini berhasil mempercepat membuka halaman website yang diinginkan ketika file dari website yang diakses tersebut telah tersimpan didalam cache proxy server. -

Measuring and Mitigating Web Performance Bottlenecks in Broadband Access Networks
Measuring and Mitigating Web Performance Bottlenecks in Broadband Access Networks Srikanth Sundaresan Nick Feamster Georgia Tech Georgia Tech [email protected] [email protected] Renata Teixeira Nazanin Magharei CNRS & UPMC Cisco Systems [email protected] [email protected] ABSTRACT As downstream throughput continues to increase, one might expect We measure Web performance bottlenecks in home broadband ac- the Web to get faster at home, as well. Meanwhile, Internet ser- cess networks and evaluate ways to mitigate these bottlenecks with vice providers and application providers are increasingly cognizant caching within home networks. We first measure Web performance of the importance of reducing Web page load times; even seem- bottlenecks to nine popular Web sites from more than 5,000 broad- ingly small differences in latency can introduce significant effects band access networks and demonstrate that when the downstream on usability (and revenue). The Bing search engine experiences re- throughput of the access link exceeds about 16 Mbits/s, latency is duced revenue of 1.2% with just a 500-millisecond delay [53], and the main bottleneck for Web page load time. Next, we use a router- a 400-millisecond delay resulted in a 0.74% decrease in searches based Web measurement tool, Mirage, to deconstruct Web page on the Google search engine [14]. Forrester research found that load time into its constituent components (DNS lookup, TCP con- most users expected online shopping sites to load in two seconds nection setup, object download) and show that simple latency opti- or fewer [40]. Content providers struggle to mitigate any network mizations can yield significant improvements in overall page load performance bottleneck that can slow down Web page loads in ac- times. -

Load-Balance & Proxies
Load-Balance & Proxies Networking Pierre-Philipp Braun <[email protected]> Table of contents ▶ Scalability (recap) ▶ Load-Balance ▶ Forward & Reverse Proxies Scalability First, how to be DoS resilient?… ==> infrastructure and code done right ▶ Principle of least privilege ▶ firewall policy ▶ cluster services need to listen internally only ▶ service/app authentication & authorization ▶ KISS / no hype required, less code == less vulns == less bugs ▶ Code harden & pay devs to REMOVE lines ▶ Fast incident response (about monitoring and well-established HA processes, not about forensics) Second, how to be high-load resilient?… ==> load-balance ready ▶ Load-balance cluster – apps are stateless and/or cluster-aware ▶ Distributing the network load is the true active/active ▶ Shared data storage ▶ Big-enough pipes X XX XX public network X X XXX XXX XX X X X X XX X X 9.9.9.9 +---------+ +---------+ +---------+ | | | | | | | node1 | | node2 | | node3 | | | | | | | +---------+ +---------+ +---------+ ▶ got Swarm or K8S cluster ▶ one application end-point with public IP 9.9.9.9 ▶ DNS record app.example.net IN A 9.9.9.9 Everything is fine there? ==> NO – all the load goes to only one node ▶ Swarm and K8S do have a network overlay by default, which re-distributes load to other nodes ▶ however node1 becomes a load-balancer ipso-facto here ▶ node1 is not necessarily sized for that purpose How to design app.example.net so the traffic gets shuffled around the nodes?… ==> TWO SOLUTIONS ▶ either by means of DNS round-robin ▶ –or– by means of a load-balancer -
Ipv6 Tutorial János Mohácsi
IPv6 Tutorial János Mohácsi Alcatel-Lucent Szeminárium 2009 - IPv6 tutorial 6DEPLOY Partners NRENs Industry Renater France Cisco Netherlands GRNET Greece FCCN Portugal Universities NIIF/HUNGARNET Hungary UNINETT Norway BREN Bulgaria UCL United Kingdom Soton ECS United Kingdom SMEs Non-European Partners Consulintel Spain AfriNIC Mauritius Martel Consulting (coordinator) Switzerland LACNIC Uruguay Associated partners: RIPE NCC, APNIC Nov 2009 Alcatel-Lucent Szeminárium 2009 - IPv6 tutorial 2 Project Objectives Support of EU policy The Internet is now the main telecommunications technology that underpins all aspects of business and leisure, and as such is central to the economic growth of a country. Awareness of the evolution of the Internet, and providing support for the introduction of IPv6 is therefore crucial as ICT becomes a major theme in FP7 Specific technical focus on supporting the deployment of IPv6 in: • research infrastructures, for supporting all fields of science and technology • FP7 projects (especially in the areas of emergency services, healthcare, transport, gaming) • developing countries (Africa, Latin America, Asia and E. Europe), and • commercial organisations in Europe Nov 2009 Alcatel-Lucent Szeminárium 2009 - IPv6 tutorial 3 History FP4: 6INIT, 6WINIT FP5: 6NET, Euro6IX, Occasion, 6Power, IPv6 TF FP6: 6DISS, Sponge, IPv6 TF (continued) FP7: 6DEPLOY 6DEPLOY is the one we exploit the most, in terms of partners and material Nov 2009 Alcatel-Lucent Szeminárium 2009 - IPv6 tutorial 4 Technical Approach Remote testbeds -

The Tao of .Net and Powershell Malware Analysis Pontiroli & Martinez
THE TAO OF .NET AND POWERSHELL MALWARE ANALYSIS PONTIROLI & MARTINEZ THE TAO OF .NET AND adopted proven practices from agile software development and business administration that focus on maximizing profi ts while POWERSHELL MALWARE minimizing the development time and maintenance cost of ANALYSIS these dreadful concoctions. Santiago M. Pontiroli In 2002, Microsoft released a game-changing framework that Kaspersky Lab, Argentina revolutionized the software development industry and unwittingly provided malware writers with an unimaginable F. Roberto Martinez arsenal of weapons. While ‘script kiddies’ resorted to builders and automated environments to cobble together variations of Kaspersky Lab, Mexico already-available malware samples, seasoned malware writers now had access to forums with approachable lessons on how Email {santiago.pontiroli; roberto.martinez}@ to write fresh pieces of malicious code, all with an eye to the kaspersky.com most desirable feature of all: avoiding anti-virus detection for as long as possible. Intended to compete directly with Oracle’s JAVA platform, the .NET framework provided not only a ABSTRACT comprehensive library of built-in functions but also an accompanying development environment capable of With the ubiquitous adoption of Microsoft’s .NET and supporting several high-level programming languages PowerShell frameworks, an ever increasing number of including Microsoft’s soon-to-be-fl agship C# and the evolution software development and IT ninjas are joining a nascent of Visual Basic, dubbed VB .NET. tradition of professionals leveraging these powerful environments for added effi cacy in their everyday jobs. With a Available by default in most Windows installations, the .NET wide array of libraries and cmdlets at their fi ngertips, the need framework has become the de facto standard for software to reinvent the wheel is long forgotten. -
WISE-3610 Lora Gateway SDK Build Procedure
Advantech Co., LTD. WISE-3610 LoRa Gateway SDK Build Procedure Quick Start Guide 2017/11/1 Content 1. BUILD CODE ENVIRONMENT .................................................................................................................................................... 1 2. PREPARE SDK SOURCE .............................................................................................................................................................. 1 3. TO MAKE IMAGE ...................................................................................................................................................................... 1 4. SDK TREE .................................................................................................................................................................................. 2 5. FIRMWARE UPGRADE VIA RS-232 CONSOLE ............................................................................................................................. 4 6. FIRMWARE UPGRADE VIA SSH ............................................................................................................................................... 12 7. FIRMWARE UPGRADE VIA WEB GUI ....................................................................................................................................... 19 8. TO ENABLE TASKSET IN BUSYBOX ........................................................................................................................................... 20 9. TO INCLUDE A SAMPLE TASK INTO FIRMWARE