Move Beyond Passwords Index
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Comparative Analysis and Framework Evaluating Web Single Sign-On Systems
Comparative Analysis and Framework Evaluating Web Single Sign-On Systems FURKAN ALACA, School of Computing, Queen’s University, [email protected] PAUL C. VAN OORSCHOT, School of Computer Science, Carleton University, [email protected] We perform a comprehensive analysis and comparison of 14 web single sign-on (SSO) systems proposed and/or deployed over the last decade, including federated identity and credential/password management schemes. We identify common design properties and use them to develop a taxonomy for SSO schemes, highlighting the associated trade-offs in benefits (positive attributes) offered. We develop a framework to evaluate the schemes, in which weidentify14 security, usability, deployability, and privacy benefits. We also discuss how differences in priorities between users, service providers (SPs), and identity providers (IdPs) impact the design and deployment of SSO schemes. 1 INTRODUCTION Password-based authentication has numerous documented drawbacks. Despite the many password alternatives, no scheme has thus far offered improved security without trading off deployability or usability [8]. Single Sign-On (SSO) systems have the potential to strengthen web authentication while largely retaining the benefits of conventional password-based authentication. We analyze in depth the state-of-the art ofwebSSO through the lens of usability, deployability, security, and privacy, to construct a taxonomy and evaluation framework based on different SSO architecture design properties and their associated benefits and drawbacks. SSO is an umbrella term for schemes that allow users to rely on a single master credential to access a multitude of online accounts. We categorize SSO schemes across two broad categories: federated identity systems (FIS) and credential managers (CM). -

A Decentralized Framework for Verifiable Credentials on the Web by Kayode Yadilichi Ezike S.B
SolidVC - A Decentralized Framework for Verifiable Credentials on the Web by Kayode Yadilichi Ezike S.B. EECS | Massachusetts Institute of Technology | 2017 Submitted to the Department of Electrical Engineering and Computer Science in Partial Fulfillment of the Requirements for the Degree of Master of Engineering in Electrical Engineering and Computer Science at the MASSACHUSETTS INSTITUTE OF TECHNOLOGY February 2019 ○c Massachusetts Institute of Technology 2019. All rights reserved. Author................................................................ Department of Electrical Engineering and Computer Science February 20, 2019 Certified by. Lalana Kagal Principal Research Scientist Thesis Supervisor Accepted by . Katrina LaCurts Chair, Master of Engineering Thesis Committee 2 SolidVC - A Decentralized Framework for Verifiable Credentials on the Web by Kayode Yadilichi Ezike Submitted to the Department of Electrical Engineering and Computer Science on February 20, 2019, in Partial Fulfillment of the Requirements for the Degree of Master of Engineering in Electrical Engineering and Computer Science Abstract Credentials are an integral part of our lives, as they express our capabilities and enable access to restricted services and benefits. In the early 2010s, the Verifiable Claims Working Group of the World Wide Web Consortium (W3C) proposed a specifica- tion for what is now the Verifiable Credentials Data Model. This living specification, which is still in development, outlines a cogent framework for the issuance, storage, presentation, and verification of credentials on the Web. Many of the leading Verifi- able Credentials projects leverage Distributed Ledger Technology (DLT), potentially compromising Web interoperability and sometimes exposing otherwise personal data. SolidVC is a decentralized Verifiable Credentials platform built with the open pro- tocols of the Web. -

Indeni Insight
Indeni 6 User Guide Part 1: Understanding the Basics 1.1 Requirements 1.2 Installation 1.3 Indeni Insight Part 2: Getting Started 2.1 Creating Users on Vendor Devices 2.2 Device Communication Part 3: Navigating the User Interface 3.1 Summary Tab 3.2 Current Tab 3.3 Archived Tab 3.4 Rules Tab Part 4: Analysis and Reporting 4.1 Custom Reports Part 5: Device Management 5.1 Credential Sets 5.2 Adding Devices 5.3 Device Backup Part 6: Settings 6.1: Centralized Authentication 6.2: Role Based Access Control 6.3: Configuring a Proxy Server to access Indeni Insight 6.4: SNMP Integration Part 7: Security Open Source Credits 2 | Page Part 1: Understanding the Basics This Introductory Guide is geared towards technical users with a strong working knowledge of networking and network security administration. Users should have the ability to set up network devices on their own, and also be familiar with how to use the various Command Line Interfaces (CLI). The guide is designed to take you from start to finish, in an order that will help you succeed. If you are a first time Indeni user, you will want to go through each step of the guide, and at the end, you should be able to add devices with a good understanding of how to use the system successfully. We highly encourage interested users, students, and IT professionals testing new technologies to download and use Indeni for free! If you do not have networking devices to test with, but are interested in trying out our system, you can use other tools such as GNS3, since Indeni works with both physical and virtual devices. -

Netiq Securelogin Installation Guide
SecureLogin 8.7 Installation Guide February, 2019 Legal Notice For information about NetIQ legal notices, disclaimers, warranties, export and other use restrictions, U.S. Government restricted rights, patent policy, and FIPS compliance, see https://www.netiq.com/company/legal/. © 2018 NetIQ Corporation. All Rights Reserved. For information about NetIQ trademarks, see https://www.netiq.com/company/legal/. All third-party trademarks are the property of their respective owners. 2 Contents About This Guide 7 1 Getting Started 9 Prerequisites . 9 Setting Up a Passphrase . 9 2 Introduction 11 Features of SecureLogin Installer. .11 Installation Overview . .11 Logging Event Messages. .13 Disabling Logging to Windows Event Log By Using Installation Wizard . .13 Disabling Logging to Windows Event Log After the Installation. .14 Logging of Syslog Audit Messages . .14 Installing and Configuring Syslog Auditing . .14 Enabling Logging to Syslog . .16 Managing Log Settings for SecureLogin Components . .17 Understanding the NSLLogManager Functionality . .17 Using NSLLogManager. .17 Installing SecureLogin with Advanced Authentication. .17 Installing SecureLogin Browser Extensions . .18 Installing Single Sign-on Assistant in Google Chrome. .18 Installing Single Sign-on Assistant in Microsoft Edge (Chromium-based) . .19 Installing Single Sign-on Assistant in Microsoft Edge (HTML-based). .19 Installing Single Sign-on Assistant in Mozilla Firefox. .20 Installing NetIQ SecureLogin Extension in Google Chrome . .20 Installing NetIQ SecureLogin Extension in Mozilla Firefox . .20 3 Installing and Configuring in Active Directory Environment 23 Before You Begin . .23 Prerequisites . .23 Requirements for Microsoft Windows Server . .24 Installation Overview. .25 Microsoft Active Directory . .25 Configuring . .26 Extending the Active Directory Schema and Assigning Rights . .26 Configuring a User’s Environment . -
Cybersecurity in a Digital Era.Pdf
Digital McKinsey and Global Risk Practice Cybersecurity in a Digital Era June 2020 Introduction Even before the advent of a global pandemic, executive teams faced a challenging and dynamic environ- ment as they sought to protect their institutions from cyberattack, without degrading their ability to innovate and extract value from technology investments. CISOs and their partners in business and IT functions have had to think through how to protect increasingly valuable digital assets, how to assess threats related to an increasingly fraught geopolitical environment, how to meet increasingly stringent customer and regulatory expectations and how to navigate disruptions to existing cybersecurity models as companies adopt agile development and cloud computing. We believe there are five areas for CIOs, CISOs, CROs and other business leaders to address in particular: 1. Get a strategy in place that will activate the organization. Even more than in the past cybersecurity is a business issue – and cybersecurity effectiveness means action not only from the CISO organiza- tion, but also from application development, infrastructure, product development, customer care, finance, human resources, procurement and risk. A successful cybersecurity strategy supports the business, highlights the actions required from across the enterprise – and perhaps most importantly captures the imagination of the executive in how it can manage risk and also enable business innovation. 2. Create granular, analytic risk management capabilities. There will always be more vulnerabilities to address and more protections you can consider than you will have capacity to implement. Even companies with large and increasing cybersecurity budgets face constraints in how much change the organization can absorb. -

Implementing a Web Application for W3C Webauthn Protocol Testing †
proceedings Proceedings Implementing a Web Application for W3C WebAuthn Protocol Testing † Martiño Rivera Dourado 1,* , Marcos Gestal 1,2 and José M. Vázquez-Naya 1,2 1 Grupo RNASA-IMEDIR, Departamento de Computación, Facultade de Informática, Universidade da Coruña, Elviña, 15071 A Coruña, Spain; [email protected] (M.G.); [email protected] (J.M.V.-N.) 2 Centro de Investigación CITIC, Universidade da Coruña, Elviña, 15071 A Coruña, Spain * Correspondence: [email protected] † Presented at the 3rd XoveTIC Conference, A Coruña, Spain, 8–9 October 2020. Published: 18 August 2020 Abstract: During the last few years, the FIDO Alliance and the W3C have been working on a new standard called WebAuthn that aims to substitute the obsolete password as an authentication method by using physical security keys instead. Due to its recent design, the standard is still changing and so are the needs for protocol testing. This research has driven the development of a web application that supports the standard and gives extensive information to the user. This tool can be used by WebAuthn developers and researchers, helping them to debug concrete use cases with no need for an ad hoc implementation. Keywords: WebAuthn; authentication; testing 1. Introduction Authentication is one of the most critical parts of an application. It is a security service that aims to guarantee the authenticity of an identity. This can be done by using several security mechanisms but currently, without a doubt, the most common is the username and password method. Although this method is easy for a user to conceptually understand, it constitutes many security problems. -
Derived Personal Identity Verification (PIV) Credentials
NIST SPECIAL PUBLICATION 1800-12 Derived Personal Identity Verification (PIV) Credentials Includes Executive Summary (A); Approach, Architecture, and Security Characteristics (B); and How-To Guides (C) William Newhouse Michael Bartock Jeffrey Cichonski Hildegard Ferraiolo Murugiah Souppaya Christopher Brown Spike E. Dog Susan Prince Julian Sexton This publication is available free of charge from https://doi.org/10.6028/NIST.SP.1800-12 Previous drafts of this publication are available free of charge from https://www.nccoe.nist.gov/library/derived-piv-credentials-nist-sp-1800-12-practice-guide NIST SPECIAL PUBLICATION 1800-12 Derived Personal Identity Verification (PIV) Credentials Includes Executive Summary (A); Approach, Architecture, and Security Characteristics (B); and How-To Guides (C) William Newhouse National Cybersecurity Center of Excellence Information Technology Laboratory Michael Bartock Jeffrey Cichonski Hildegard Ferraiolo Murugiah Souppaya National Institute of Standards and Technology Information Technology Laboratory Christopher Brown Spike E. Dog Susan Prince Julian Sexton The MITRE Corporation McLean, Virginia August 2019 U.S. Department of Commerce Wilbur Ross, Secretary National Institute of Standards and Technology Walter Copan, NIST Director and Undersecretary of Commerce for Standards and Technology NIST SPECIAL PUBLICATION 1800-12A Derived Personal Identity Verification (PIV) Credentials Volume A: Executive Summary William Newhouse National Cybersecurity Center of Excellence Information Technology Laboratory Michael -

8 Steps for Effectively Deploying
8 Steps for Effectively Deploying MFA Table of Contents The value of MFA 3 1. Educate your users 4 2. Consider your MFA policies 5 3. Plan and provide for a variety of access needs 7 4. Think twice about using SMS for OTP 10 5. Check compliance requirements carefully 11 6. Plan for lost devices 12 7. Plan to deploy MFA to remote workers 14 8. Phase your deployment: Be prepared to review and revise 16 8 Steps for Effectively Deploying MFA 2 The value of MFA Multi-factor authentication (MFA) has never been more important. With the growing number of data breaches and cybersecurity threats—and the steep financial and reputational costs that come with them—organizations need to prioritize MFA deployment for their workforce and customers alike. Not doing so could spell disaster; an invitation for bad actors to compromise accounts and breach your systems. Adopting modern MFA means implementing a secure, simple, and context-aware solution that ensures that only the right people have access to the right resources. It adds a layer of security, giving your security team, your employees, and your customers peace of mind. Unfortunately, while the benefits are clear, implementing MFA can be a complex project. In our Multi-factor Authentication Deployment Guide, we’ve outlined eight steps that you can take to better enable your MFA deployment: Educate your users Consider your MFA policies Plan and provide for a variety of access needs Think twice about using SMS for OTP Check compliance requirements carefully Plan for lost devices Plan to deploy MFA to remote workers Phase your deployment: be prepared to review and revise In this eBook, we’ll take a deeper dive into each of these elements, giving you tactical advice and best practices for how to implement each step as you get ready to roll out Okta MFA. -

Mfaproxy: a Reverse Proxy for Multi-Factor Authentication
Iowa State University Capstones, Theses and Creative Components Dissertations Fall 2019 MFAProxy: A reverse proxy for multi-factor authentication Alan Schmitz Follow this and additional works at: https://lib.dr.iastate.edu/creativecomponents Part of the Digital Communications and Networking Commons Recommended Citation Schmitz, Alan, "MFAProxy: A reverse proxy for multi-factor authentication" (2019). Creative Components. 425. https://lib.dr.iastate.edu/creativecomponents/425 This Creative Component is brought to you for free and open access by the Iowa State University Capstones, Theses and Dissertations at Iowa State University Digital Repository. It has been accepted for inclusion in Creative Components by an authorized administrator of Iowa State University Digital Repository. For more information, please contact [email protected]. MFAProxy: A reverse proxy for multi-factor authentication by Alan Schmitz A Creative Component submitted to the graduate faculty in partial fulfillment of the requirements for the degree of MASTER OF SCIENCE Major: Information Assurance Program of Study Committee: Doug Jacobson, Major Professor The student author, whose presentation of the scholarship herein was approved by the program of study committee, is solely responsible for the content of this Creative Component. The Graduate College will ensure this Creative Component is globally accessible and will not permit alterations after a degree is conferred. Iowa State University Ames, Iowa 2019 Copyright c Alan Schmitz, 2019. All rights reserved. ii TABLE OF CONTENTS Page LIST OF FIGURES . iii ABSTRACT . iv CHAPTER 1. INTRODUCTION . .1 CHAPTER 2. BACKGROUND . .3 2.1 Passwords and PINs . .3 2.2 Short Message Service . .4 2.3 One-Time Passwords . .5 2.4 U2F and WebAuthn . -

Strong Authentication Based on Mobile Application
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by Helsingin yliopiston digitaalinen arkisto STRONG AUTHENTICATION BASED ON MOBILE APPLICATION Helsingin yliopisto Faculty of Science Department of Computer Science Master's thesis Spring 2020 Harri Salminen Supervisor: Valtteri Niemi Tiedekunta - Fakultet - Faculty Osasto - Avdelning - Department Faculty of Science The Department of Computer Science Tekijä - Författare - Author Harri Salminen Työn nimi - Arbetets titel Title STRONG AUTHENTICATION BASED ON MOBILE APPLICATION Oppiaine - Läroämne – Subject Computer Science Työn laji/ Ohjaaja - Arbetets art/Handledare - Aika - Datum - Month and Sivumäärä - Sidoantal - Number of Level/Instructor year pages Master's thesis / Valtteri Niemi June, 2020 58 Tiivistelmä - Referat - Abstract The user authentication in online services has evolved over time from the old username and password-based approaches to current strong authentication methodologies. Especially, the smartphone app has become one of the most important forms to perform the authentication. This thesis describes various authentication methods used previously and discusses about possible factors that generated the demand for the current strong authentication approach. We present the concepts and architectures of mobile application based authentication systems. Furthermore, we take closer look into the security of the mobile application based authentication approach. Mobile apps have various attack vectors that need to be taken under consideration when designing an authentication system. Fortunately, various generic software protection mechanisms have been developed during the last decades. We discuss how these mechanisms can be utilized in mobile app environment and in the authentication context. The main idea of this thesis is to gather relevant information about the authentication history and to be able to build a view of strong authentication evolution. -
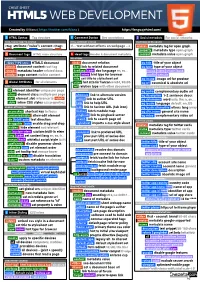
HTML5 Cheatsheet 2019
CHEAT SHEET HTML5 WEB DEVELOPMENT Created by @Manz ( https://twitter.com/Manz ) https://lenguajehtml.com/ S HTML Syntax Tag structure C Comment Syntax Dev annotations S Social metadata For social networks HTML TAG/ATTRIBUTE SYNTAX HTML COMMENT SYNTAX FACEBOOK OPEN GRAPH <tag attribute="value"> content </tag> <!-- text without effects on webpage --> <meta> metadata tag for open graph property metadata type open graph D Document tags HTML main structure H Head tags Header & document metadata content metadata value open graph MAIN TAGS RELATIONS REQUIRED METADATA PROPERTIES <!DOCTYPE html> HTML5 document <link> document relation og:title title of your object <html> document content root tag href link to related document og:type type of your object <head> metadata header related docs hreflang code doc language en, es... music video article book <body> page content visible content type mime hint type for browser profile website title set title to stylesheet set og:image image url for preview G Global Attributes for all elements sizes hint size for favicon 64x64, 96x96 og:url canonical & absolute url DOM / STYLE ATTRIBUTES rel relation type with other document OPTIONAL METADATA PROPERTIES id element identifier unique per page BASIC RELATION og:audio complementary audio url class element class multiple per page alternate link to alternate version og:description 1-2 sentence descr. slot element slot reference to <slot> author link to author URL og:determiner word auto, the, a, an, ... style inline CSS styles css properties help link to help URL -

EL PASSO: Efficient and Lightweight Privacy-Preserving Single Sign On
Proceedings on Privacy Enhancing Technologies ; 2021 (2):70–87 Zhiyi Zhang, Michał Król, Alberto Sonnino, Lixia Zhang, and Etienne Rivière EL PASSO: Efficient and Lightweight Privacy-preserving Single Sign On Abstract: Anonymous credentials are a solid founda- 1 Introduction tion for privacy-preserving Single Sign-On (SSO). They enable unlinkable authentication across domains and al- Single Sign-On (SSO) is an answer to the complexity low users to prove their identity without revealing more and fragility of using individual passwords on the web, than necessary. Unfortunately, anonymous credentials i.e., leading to reuse and leaks [1]. SSO enables the use schemes remain difficult to use and complex to deploy. of a unique identity provided by an Identity Provider They require installation and use of complex software at (IdP). Users authenticate themselves to services (called the user side, suffer from poor performance, and do not Relying Parties–RP) with tokens provided by their IdP. support security features that are now common, such SSO improves overall web security [2] and enables the as two-factor authentication, secret recovery, or sup- generalization of good security practices such as the use port for multiple devices. In contrast, Open ID Con- of 2-factor authentication (2FA) [3]. nect (OIDC), the de facto standard for SSO is widely deployed and used despite its lack of concern for users’ Limitations of OpenID Connect. OpenID Connect privacy. We present EL PASSO, a privacy-preserving (OIDC) is a dominant SSO solution used by over a mil- SSO system based on anonymous credentials that does lion websites in 2020 [4].