By Israa Alsars
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Poster: Introducing Massbrowser: a Censorship Circumvention System Run by the Masses
Poster: Introducing MassBrowser: A Censorship Circumvention System Run by the Masses Milad Nasr∗, Anonymous∗, and Amir Houmansadr University of Massachusetts Amherst fmilad,[email protected] ∗Equal contribution Abstract—We will present a new censorship circumvention sys- side the censorship regions, which relay the Internet traffic tem, currently being developed in our group. The new system of the censored users. This includes systems like Tor, VPNs, is called MassBrowser, and combines several techniques from Psiphon, etc. Unfortunately, such circumvention systems are state-of-the-art censorship studies to design a hard-to-block, easily blocked by the censors by enumerating their limited practical censorship circumvention system. MassBrowser is a set of proxy server IP addresses [14]. (2) Costly to operate: one-hop proxy system where the proxies are volunteer Internet To resist proxy blocking by the censors, recent circumven- users in the free world. The power of MassBrowser comes from tion systems have started to deploy the proxies on shared-IP the large number of volunteer proxies who frequently change platforms such as CDNs, App Engines, and Cloud Storage, their IP addresses as the volunteer users move to different a technique broadly referred to as domain fronting [3]. networks. To get a large number of volunteer proxies, we This mechanism, however, is prohibitively expensive [11] provide the volunteers the control over how their computers to operate for large scales of users. (3) Poor QoS: Proxy- are used by the censored users. Particularly, the volunteer based circumvention systems like Tor and it’s variants suffer users can decide what websites they will proxy for censored from low quality of service (e.g., high latencies and low users, and how much bandwidth they will allocate. -

Threat Modeling and Circumvention of Internet Censorship by David Fifield
Threat modeling and circumvention of Internet censorship By David Fifield A dissertation submitted in partial satisfaction of the requirements for the degree of Doctor of Philosophy in Computer Science in the Graduate Division of the University of California, Berkeley Committee in charge: Professor J.D. Tygar, Chair Professor Deirdre Mulligan Professor Vern Paxson Fall 2017 1 Abstract Threat modeling and circumvention of Internet censorship by David Fifield Doctor of Philosophy in Computer Science University of California, Berkeley Professor J.D. Tygar, Chair Research on Internet censorship is hampered by poor models of censor behavior. Censor models guide the development of circumvention systems, so it is important to get them right. A censor model should be understood not just as a set of capabilities|such as the ability to monitor network traffic—but as a set of priorities constrained by resource limitations. My research addresses the twin themes of modeling and circumvention. With a grounding in empirical research, I build up an abstract model of the circumvention problem and examine how to adapt it to concrete censorship challenges. I describe the results of experiments on censors that probe their strengths and weaknesses; specifically, on the subject of active probing to discover proxy servers, and on delays in their reaction to changes in circumvention. I present two circumvention designs: domain fronting, which derives its resistance to blocking from the censor's reluctance to block other useful services; and Snowflake, based on quickly changing peer-to-peer proxy servers. I hope to change the perception that the circumvention problem is a cat-and-mouse game that affords only incremental and temporary advancements. -

BRKSEC-2011.Pdf
#CLUS About Garlic and Onions A little journey… Tobias Mayer, Technical Solutions Architect BRKSEC-2011 #CLUS Me… CCIE Security #14390, CISSP & Motorboat driving license… Working in Content Security & TLS Security tmayer{at}cisco.com Writing stuff at “blogs.cisco.com” #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 3 Agenda • Why anonymization? • Using Tor (Onion Routing) • How Tor works • Introduction to Onion Routing • Obfuscation within Tor • Domain Fronting • Detect Tor • I2P – Invisible Internet Project • Introduction to Garlic Routing • Conclusion #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 4 Cisco Webex Teams Questions? Use Cisco Webex Teams (formerly Cisco Spark) to chat with the speaker after the session How 1 Find this session in the Cisco Events App 2 Click “Join the Discussion” 3 Install Webex Teams or go directly to the team space 4 Enter messages/questions in the team space Webex Teams will be moderated cs.co/ciscolivebot#BRKSEC-2011 by the speaker until June 18, 2018. #CLUS © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 5 Different Intentions Hide me from Government! Hide me from ISP! Hide me from tracking! Bypass Corporate Bypass Country Access Hidden policies restrictions (Videos…) Services #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 6 Browser Identity Tracking does not require a “Name” Tracking is done by examining parameters your browser reveals https://panopticlick.eff.org #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 7 Proxies EPIC Browser #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. -
People's Tech Movement to Kick Big Tech out of Africa Could Form a Critical Part of the Global Protests Against the Enduring Legacy of Racism and Colonialism
CONTENTS Acronyms ................................................................................................................................................ 1 1 Introduction: The Rise of Digital Colonialism and Surveillance Capitalism ..................... 2 2 Threat Modeling .......................................................................................................................... 8 3 The Basics of Information Security and Software ............................................................... 10 4 Mobile Phones: Talking and Texting ...................................................................................... 14 5 Web Browsing ............................................................................................................................ 18 6 Searching the Web .................................................................................................................... 23 7 Sharing Data Safely ................................................................................................................... 25 8 Email Encryption ....................................................................................................................... 28 9 Video Chat ................................................................................................................................... 31 10 Online Document Collaboration ............................................................................................ 34 11 Protecting Your Data ................................................................................................................ -

Blocking-Resistant Communication Through Domain Fronting
Proceedings on Privacy Enhancing Technologies 2015; 2015 (2):46–64 David Fifield*, Chang Lan, Rod Hynes, Percy Wegmann, and Vern Paxson Blocking-resistant communication through domain fronting Abstract: We describe “domain fronting,” a versatile 1 Introduction censorship circumvention technique that hides the re- mote endpoint of a communication. Domain fronting Censorship is a daily reality for many Internet users. works at the application layer, using HTTPS, to com- Workplaces, schools, and governments use technical and municate with a forbidden host while appearing to com- social means to prevent access to information by the net- municate with some other host, permitted by the cen- work users under their control. In response, those users sor. The key idea is the use of different domain names at employ technical and social means to gain access to the different layers of communication. One domain appears forbidden information. We have seen an ongoing conflict on the “outside” of an HTTPS request—in the DNS re- between censor and censored, with advances on both quest and TLS Server Name Indication—while another sides, more subtle evasion countered by more powerful domain appears on the “inside”—in the HTTP Host detection. header, invisible to the censor under HTTPS encryp- Circumventors, at a natural disadvantage because tion. A censor, unable to distinguish fronted and non- the censor controls the network, have a point working fronted traffic to a domain, must choose between allow- in their favor: the censor’s distaste for “collateral dam- ing circumvention traffic and blocking the domain en- age,” incidental overblocking committed in the course of tirely, which results in expensive collateral damage. -
Download Or Upload
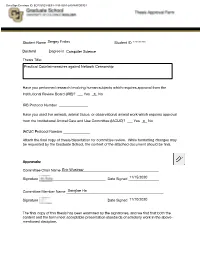
DocuSign Envelope ID: ECF321E3-5E94-4153-9254-2A048AFD03E4 Student Name ______________________________Sergey Frolov _______ Student ID___________________********* ___ Doctoral______________ Degree in ______________________________Computer Science _____________________________ Thesis Title: Practical Countermeasures against Network Censorship Have you performed research involving human subjects which requires approval from the Institutional Review Board (IRB)? ___ Yes ___X No IRB Protocol Number ________________ Have you used live animals, animal tissue, or observational animal work which requires approval from the Institutional Animal Care and Use Committee (IACUC)? ___ Yes ___X No IACUC Protocol Number _______________ Attach the final copy of thesis/dissertation for committee review. While formatting changes may be requested by the Graduate School, the content of the attached document should be final. Approvals: Committee Chair Name ______________________________________________________Eric Wustrow Signature _____________________________________ Date Signed _________________11/15/2020 Committee Member Name ______________________________________________________Sangtae Ha Signature _____________________________________ Date Signed _________________11/10/2020 The final copy of this thesis has been examined by the signatories, and we find that both the content and the form meet acceptable presentation standards of scholarly work in the above- mentioned discipline. DocuSign Envelope ID: ECF321E3-5E94-4153-9254-2A048AFD03E4 Practical Countermeasures -

Domain Shadowing: Leveraging Content Delivery Networks for Robust Blocking-Resistant Communications
Domain Shadowing: Leveraging Content Delivery Networks for Robust Blocking-Resistant Communications Mingkui Wei Cybersecurity Engineering George Mason University, Fairfax, VA, 22030 Abstract according to the Host header but have the TLS connection still appear to belong to the allowed domain. The blocking- We debut domain shadowing, a novel censorship evasion resistance of domain fronting derives from the significant technique leveraging content delivery networks (CDNs). Do- “collateral damage”, i.e., to disable domain fronting, the censor main shadowing exploits the fact that CDNs allow their cus- needs to block users from accessing the entire CDN, resulting tomers to claim arbitrary domains as the back-end. By set- in all domains on the CDN inaccessible. Because today’s ting the front-end of a CDN service as an allowed domain Internet relies heavily on web caches and many high-profile and the back-end a blocked one, a censored user can access websites also use CDNs to distribute their content, completely resources of the blocked domain with all “indicators”, includ- blocking access to a particular CDN may not be a feasible ing the connecting URL, the SNI of the TLS connection, and option for the censor. Because of its strong blocking-resistant the Host header of the HTTP(S) request, appear to belong power, domain fronting has been adopted by many censorship to the allowed domain. Furthermore, we demonstrate that evasion systems since it has been proposed [24, 28, 34, 36]. domain shadowing can be proliferated by domain fronting, In the last two years, however, many CDNs began to disable a censorship evasion technique popularly used a few years domain fronting by enforcing the match between the SNI and ago, making it even more difficult to block. -

Conjure: Summoning Proxies from Unused Address Space
Conjure: Summoning Proxies from Unused Address Space Sergey Frolov Jack Wampler Sze Chuen Tan University of Colorado Boulder University of Colorado Boulder UIUC J. Alex Halderman Nikita Borisov Eric Wustrow University of Michigan UIUC University of Colorado Boulder ABSTRACT Refraction Networking (formerly known as “Decoy Routing”) has emerged as a promising next-generation approach for circumvent- ing Internet censorship. Rather than trying to hide individual cir- cumvention proxy servers from censors, proxy functionality is implemented in the core of the network, at cooperating ISPs in friendly countries. Any connection that traverses these ISPs could be a conduit for the free flow of information, so censors cannot eas- ily block access without also blocking many legitimate sites. While one Refraction scheme, TapDance, has recently been deployed at ISP-scale, it suffers from several problems: a limited number of “decoy” sites in realistic deployments, high technical complexity, Figure 1: Conjure Overview — An ISP deploys a Conjure station, which and undesirable tradeoffs between performance and observability sees a passive tap of passing traffic. Following a steganographic registration by the censor. These challenges may impede broader deployment process, a client can connect to an unused IP address in the ISP’s AS, and and ultimately allow censors to block such techniques. the station will inject packets to communicate with the client as if there were a proxy server at that address. We present Conjure, an improved Refraction Networking ap- proach that overcomes these limitations by leveraging unused ad- dress space at deploying ISPs. Instead of using real websites as the decoy destinations for proxy connections, our scheme connects 1 INTRODUCTION to IP addresses where no web server exists leveraging proxy func- Over half of Internet users globally now live in countries that block tionality from the core of the network. -

Draft of October 2, 2017
i Draft of October 2, 2017 1 Introduction 1 1.1 Scope . 1 2 Principles of circumvention 4 2.1 Collateral damage . 5 2.2 Bridge distribution . 6 2.3 Early censorship and circumvention . 7 2.4 Open problems in censor modeling . 7 3 Measurement studies and measurement platforms 8 4 Studies of censors 9 4.1 Summary of circumvention systems . 14 5 Empirically testing real-world censors 16 6 Domain fronting 18 6.1 An unvarnished history of meek deployment . 19 7 Building circumvention systems 28 7.1 Flash proxy, a circumvention system . 28 7.2 OSS, a circumvention prototype . 29 7.3 Snowflake, a circumvention system . 30 8 How circumvention technologies are evaluated 31 8.1 Flash proxy . 32 8.2 Domain fronting and meek . 32 8.3 Snowflake: flash proxy revisited . 32 Chapter 1 Introduction This is a thesis about Internet censorship. In it, I will expand on two threads of research that have occupied my attention for the past several years: better understanding how censors work, and fielding systems that circumvent their restrictions. These two threads fuel each other: better understanding censors enables us to build better circumvention systems that take into account their strengths and weaknesses; and the deployment of a circumvention system affords an opportunity to observe how censors themselves react to changing circumstances. If I am successful, the output of my research is useful models that describe not only how censors behave today but how they may evolve in the future, and tools for circumvention that are not only sound in theory but also effective in practice. -

IP Because of DNS Prefetching • Despite Using a VPN Service…
BRKSEC-2011 About Garlic and Onions A little journey… Tobias Mayer, Technical Solutions Architect About Garlic and Onions We are all looking for privacy on the internet, for one or the other reason. This Session is about some technologies you can use to anonymise your network traffic, such as Tor (The Onion Router). The first part will give an introduction and explain the underlaying technology of Tor. We will take look at how you can not only use the Tor browser for access but also how the Tor network is working. We will learn how you can establish a Tor session and how we can find hidden websites and give examples of some websites...So we will enter the Darknet together. Beside Tor, we will also take a quick look at other techniques like I2P (Garlic Routing). In the last section we will make a quick sanity check what security technologies we can use to (maybe) detect such traffic in the network. This presentation is aimed at everyone who likes to learn about anonymization techniques and have a little bit of fun in the Darknet. BRKSEC-2011 © 2019 Cisco and/or its affiliates. All rights reserved. Cisco Public 3 Me… CCIE Security #14390, CISSP & Motorboat driving license… Working in Content Security & TLS Security tmayer{at}cisco.com Writing stuff at “blogs.cisco.com” BRKSEC-2011 © 2019 Cisco and/or its affiliates. All rights reserved. Cisco Public 4 Cisco Webex Teams Questions? Use Cisco Webex Teams (formerly Cisco Spark) to chat with the speaker after the session How 1 Find this session in the Cisco Events Mobile App 2 Click “Join the Discussion” 3 Install Webex Teams or go directly to the team space 4 Enter messages/questions in the team space cs.co/ciscolivebot#BRKSEC-2011 BRKSEC-2011 © 2019 Cisco and/or its affiliates. -

Analyzing China's Blocking of Unpublished Tor Bridges
Analyzing China’s Blocking of Unpublished Tor Bridges Arun Dunna Ciaran´ O’Brien University of Massachusetts Amherst University of Massachusetts Amherst Phillipa Gill University of Massachusetts Amherst Abstract Great Firewall (GFW) detects and filters Tor, following in the line of related work carried out over the past six At the end of 2011, China’s Great Firewall (GFW) began years [6, 20]. To gain access to a vantage point in China, to block unpublished Tor bridges. Past studies of this we use a virtual private server (VPS) located in a Chinese blocking have found that the firewall implements both cloud provider’s infrastructure. We also deploy three deep packet inspection (DPI) and active probing in order servers that act as bridge relays to allow us to monitor to identify and block usage of the Tor protocol. We build how the GFW probes/scans suspected bridge nodes. upon the information from previous studies conducted We use this infrastructure to answer the following in 2012 and 2015, using a vantage point in China, and questions about how the GFW blocks Tor. Specifically, bridge relays that we deploy in the US, Canada, and the we investigate to what extent the public Tor network is UK. We determine the extent to which both published reachable (§4.1); how unpublished (bridge) relays are and unpublished relays, specifically bridges, are cur- blocked (§4.2); and how GFW scanners have changed rently blocked by the GFW. We also analyze the active from previous studies (§4.3). Finally, we investigate how scanners employed by the GFW, and determine the via- Tor users can circumvent today’s GFW and investigate bility of various deployed circumvention methods. -

Active Techniques for Revealing and Analyzing the Security of Hidden Servers
UNIVERSITA` DEGLI STUDI DI MILANO Facolta` di Scienze Matematiche, Fisiche e Naturali Dipartimento di Informatica DOCTOR OF PHILOSOPHY IN COMPUTER SCIENCE XXVIII CICLO Active Techniques for Revealing and Analyzing the Security of Hidden Servers Ph.D. Candidate Srdjan Matic Adviser Prof. D. Bruschi Co-adviser Dr. J. Caballero Ph.D. Coordinator Prof. P. Boldi Academical Year 2015/2016 b Copyright c September 2016 by Srdjan Matic (rev. 138) � Abstract of the dissertation In the last years we have witnessed a boom in the use of techniques and tools that provide anonymity. Such techniques and tools are used by clients that want their communication to stay anonymous or to access censored content, as well as by administrators to hide the location of their servers. All those activities can be easily performed with the support of an anonymity network. An important component of an anonymity network is the hidden server, a machine whose IP address is kept secret. Such hidden servers are the target of research in this thesis. More specifically, we focus on different types of hidden servers used in the Tor anonymity network. Tor hidden services (HSes) are anonymous services hosted in the Tor Network. The HS itself is a hidden server because users that connect to it are not aware of its IP address, and thus its location. Another equally important kind of hidden servers are Tor bridges. Bridges are entry nodes of the Tor Network, whose IP address is not publicly disclosed to avoid blocking traffic towards them. Bridges are meant to be used by clients that connect from countries where governments perform selectivefiltering over the contents that users can access, and for this reason governments try to block connections to those nodes.