Proof-Of-Work Sidechains
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Introducing Ethereum and Solidity Foundations of Cryptocurrency and Blockchain Programming for Beginners
C. Dannen Introducing Ethereum and Solidity Foundations of Cryptocurrency and Blockchain Programming for Beginners ▶ First book on the market that teaches Ethereum and Solidity for technical thinkers of all types ▶ Written by a technology journalist trained in breaking down technical concepts into easy-to-understand prose ▶ Updates you on the last three years of progress since Bitcoin became popular - a new frontier replete with opportunity for new products and services Learn how to use Solidity and the Ethereum project – second only to Bitcoin in market capitalization. Blockchain protocols are taking the world by storm, and the Ethereum project, with its Turing-complete scripting language Solidity, has rapidly become a front-runner. This book presents the blockchain phenomenon in context; then situates Ethereum in a world pioneered by Bitcoin. 1st ed., XXI, 185 p. 34 illus., 31 illus. in color. A product of Apress See why professionals and non-professionals alike are honing their skills in smart contract patterns and distributed application development. You'll review the fundamentals of programming and networking, alongside its introduction to the new discipline of crypto- Printed book economics. You'll then deploy smart contracts of your own, and learn how they can serve as a back-end for JavaScript and HTML applications on the Web. Softcover ISBN 978-1-4842-2534-9 Many Solidity tutorials out there today have the same flaw: they are written for“advanced” ▶ 44,99 € | £39.99 JavaScript developers who want to transfer their skills to a blockchain environment. ▶ *48,14 € (D) | 49,49 € (A) | CHF 53.50 Introducing Ethereum and Solidity is accessible to technology professionals and enthusiasts of “all levels.” You’ll find exciting sample code that can move forward real world assets in both the academic and the corporate arenas. -

Beauty Is Not in the Eye of the Beholder
Insight Consumer and Wealth Management Digital Assets: Beauty Is Not in the Eye of the Beholder Parsing the Beauty from the Beast. Investment Strategy Group | June 2021 Sharmin Mossavar-Rahmani Chief Investment Officer Investment Strategy Group Goldman Sachs The co-authors give special thanks to: Farshid Asl Managing Director Matheus Dibo Shahz Khatri Vice President Vice President Brett Nelson Managing Director Michael Murdoch Vice President Jakub Duda Shep Moore-Berg Harm Zebregs Vice President Vice President Vice President Shivani Gupta Analyst Oussama Fatri Yousra Zerouali Vice President Analyst ISG material represents the views of ISG in Consumer and Wealth Management (“CWM”) of GS. It is not financial research or a product of GS Global Investment Research (“GIR”) and may vary significantly from those expressed by individual portfolio management teams within CWM, or other groups at Goldman Sachs. 2021 INSIGHT Dear Clients, There has been enormous change in the world of cryptocurrencies and blockchain technology since we first wrote about it in 2017. The number of cryptocurrencies has increased from about 2,000, with a market capitalization of over $200 billion in late 2017, to over 8,000, with a market capitalization of about $1.6 trillion. For context, the market capitalization of global equities is about $110 trillion, that of the S&P 500 stocks is $35 trillion and that of US Treasuries is $22 trillion. Reported trading volume in cryptocurrencies, as represented by the two largest cryptocurrencies by market capitalization, has increased sixfold, from an estimated $6.8 billion per day in late 2017 to $48.6 billion per day in May 2021.1 This data is based on what is called “clean data” from Coin Metrics; the total reported trading volume is significantly higher, but much of it is artificially inflated.2,3 For context, trading volume on US equity exchanges doubled over the same period. -
Blockchain Interoperability (Part 3) Polkadot
December 2020 Blockchain Interoperability (Part 3) Polkadot The Digital Investor Redefining Finance for the New Economy The Digital Investor January 2021 Table of Contents Abstract 2 1. Introduction 3 2. The foundation of Web 3.0 3 3. Architecture 4 4. Consensus mechanism 4 5. Stakeholders 5 6. Economics 5 7. Valuation 7 8. Conclusion 9 Abstract Polkadot is a promising project that should interest investors. First, interoperability increas- es digital asset utilisation, and Polkadot offers all the broadest type of interoperability. The success of DeFi, as a specific interoperability application, shows the potential of these types of solutions. Second, Polkadot and its framework Substrate democratise blockchain Authors development. We expect developers to use this platform to populate the ecosystem with new applications. Both these points together are likely to help Polkadot achieve higher Yves Longchamp network effect. Head of Research SEBA Bank AG Saurabh Deshpande Research Analyst B&B Analytics Private Limited Contact [email protected] 2 Blockchain Interoperability (Part 3) Polkadot 1. Interoperability may take Introduction many forms. In this edition of the Digital Investor, we focus In the November 2020 Digital Investor, we introduced blockchain interoperability or block- on interoperability in a broad chains’ ability to exchange information between different ecosystems. We concluded that interoperability facilitates secure and trustless value exchange, and we expect interop- sense. Polkadot aims to erability solutions to capture value in the future. Therefore, we think that interoperability connect all types of solutions demand investor attention. blockchains and transfer all Interoperability may take many forms. In this edition of The Digital Investor, we focus on types of messages between interoperability in a broad sense. -

Formal Specification and Verification of Solidity Contracts with Events
Formal Specification and Verification of Solidity Contracts with Events Ákos Hajdu Budapest University of Technology and Economics, Hungary [email protected] Dejan Jovanović SRI International, New York City, NY, USA [email protected] Gabriela Ciocarlie SRI International, New York City, NY, USA [email protected] Abstract Events in the Solidity language provide a means of communication between the on-chain services of decentralized applications and the users of those services. Events are commonly used as an abstraction of contract execution that is relevant from the users’ perspective. Users must, therefore, be able to understand the meaning and trust the validity of the emitted events. This paper presents a source-level approach for the formal specification and verification of Solidity contracts with the primary focus on events. Our approach allows the specification of events in terms of the on-chain data that they track, and the predicates that define the correspondence between the blockchain state and the abstract view provided by the events. The approach is implemented in solc-verify, a modular verifier for Solidity, and we demonstrate its applicability with various examples. 2012 ACM Subject Classification Software and its engineering → Formal methods Keywords and phrases Smart contracts, Solidity, events, specification, verification Digital Object Identifier 10.4230/OASIcs.FMBC.2020.2 Category Short Paper Related Version Preprint is available at https://arxiv.org/abs/2005.10382. Supplementary Material https://github.com/SRI-CSL/solidity 1 Introduction Ethereum is a public, blockchain-based computing platform that provides a single-world- computer abstraction for developing decentralized applications [17]. The core of such applications are programs – termed smart contracts [15] – deployed on the blockchain. -
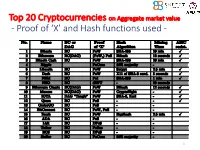
Proof of 'X' and Hash Functions Used
Top 20 Cryptocurrencies on Aggregate market value - Proof of ‘X’ and Hash functions used - 1 ISI Kolkata BlockChain Workshop, Nov 30th, 2017 CRYPTOGRAPHY with BlockChain - Hash Functions, Signatures and Anonymization - Hiroaki ANADA*1, Kouichi SAKURAI*2 *1: University of Nagasaki, *2: Kyushu University Acknowledgements: This work is supported by: Grants-in-Aid for Scientific Research of Japan Society for the Promotion of Science; Research Project Number: JP15H02711 Top 20 Cryptocurrencies on Aggregate market value - Proof of ‘X’ and Hash functions used - 3 Table of Contents 1. Cryptographic Primitives in Blockchains 2. Hash Functions a. Roles b. Various Hash functions used for Proof of ‘X’ 3. Signatures a. Standard Signatures (ECDSA) b. Ring Signatures c. One-Time Signatures (Winternitz) 4. Anonymization Techniques a. Mixing (CoinJoin) b. Zero-Knowledge proofs (zk-SNARK) 5. Conclusion 4 Brief History of Proof of ‘X’ 1992: “Pricing via Processing or Combatting Junk Mail” Dwork, C. and Naor, M., CRYPTO ’92 Pricing Functions 2003: “Moderately Hard Functions: From Complexity to Spam Fighting” Naor, M., Foundations of Soft. Tech. and Theoretical Comp. Sci. 2008: “Bitcoin: A peer-to-peer electronic cash system” Nakamoto, S. Proof of Work 5 Brief History of Proof of ‘X’ 2008: “Bitcoin: A peer-to-peer electronic cash system” Nakamoto, S. Proof of Work 2012: “Peercoin” Proof of Stake (& Proof of Work) ~ : Delegated Proof of Stake, Proof of Storage, Proof of Importance, Proof of Reserves, Proof of Consensus, ... 6 Proofs of ‘X’ 1. Proof of Work 2. Proof of Stake Hash-based Proof of ‘X’ 3. Delegated Proof of Stake 4. Proof of Importance 5. -

Cryptocurrency: the Economics of Money and Selected Policy Issues
Cryptocurrency: The Economics of Money and Selected Policy Issues Updated April 9, 2020 Congressional Research Service https://crsreports.congress.gov R45427 SUMMARY R45427 Cryptocurrency: The Economics of Money and April 9, 2020 Selected Policy Issues David W. Perkins Cryptocurrencies are digital money in electronic payment systems that generally do not require Specialist in government backing or the involvement of an intermediary, such as a bank. Instead, users of the Macroeconomic Policy system validate payments using certain protocols. Since the 2008 invention of the first cryptocurrency, Bitcoin, cryptocurrencies have proliferated. In recent years, they experienced a rapid increase and subsequent decrease in value. One estimate found that, as of March 2020, there were more than 5,100 different cryptocurrencies worth about $231 billion. Given this rapid growth and volatility, cryptocurrencies have drawn the attention of the public and policymakers. A particularly notable feature of cryptocurrencies is their potential to act as an alternative form of money. Historically, money has either had intrinsic value or derived value from government decree. Using money electronically generally has involved using the private ledgers and systems of at least one trusted intermediary. Cryptocurrencies, by contrast, generally employ user agreement, a network of users, and cryptographic protocols to achieve valid transfers of value. Cryptocurrency users typically use a pseudonymous address to identify each other and a passcode or private key to make changes to a public ledger in order to transfer value between accounts. Other computers in the network validate these transfers. Through this use of blockchain technology, cryptocurrency systems protect their public ledgers of accounts against manipulation, so that users can only send cryptocurrency to which they have access, thus allowing users to make valid transfers without a centralized, trusted intermediary. -
Ethereum Introduction
Cryptocurrencies & Security on the Blockchain Ethereum Introduction Prof. Tom Austin San José State University Some Brief Ethereum Facts • Number 2 cryptocurrency by market cap. – Not why we are studying it • Core developers – Vitalik Buterin (creator) – Gavin Wood • Block 0 mined July 30, 2015 Ethereum Prehistory: Mastercoin • Protocol layer on top of Bitcoin • Focused on financial contracts – Two-party contracts with enforced terms • October 2013: Vitalik suggested a more flexible scripting language – More limited vision – Not Turing-complete December 2013: Ethereum Proposal • The name "Ethereum" first appears in print • Transaction fees for different actions included – Computational steps paid for in ether (this concept changed later) – Once fees exhausted, processing stops • Contracts became accounts in their own right More History • Gavin Wood joins project – Designs the Ethereum Virtual Machine (EVM). – Writes "The Yellow Paper" in 2014. • Gas model changes – Miners explicitly vote on gas price. – Previous approaches allowed them to implicitly do this anyway. Account Types • Externally owned accounts (EOAs) – Equivalent to accounts in Bitcoin – Have a private key • Contract accounts – Have contract code – No private key • Cannot initiate transactions – Can react to transactions and call other contracts – Contain data Common Features with Bitcoin • Digital currency – Called ether (ETH) • Not "ethereum" – Smallest unit: wei • Proof-of-work blockchain – Ethash – designed to be ASIC-resistant – Much quicker: 14-15 second block time – Plans to move to proof-of-stake (Casper) • Peer-to-peer network Differences from Bitcoin • Turing-complete virtual machine – Almost… – Brings up a lot of security issues • Gas – Prevents denial-of-service attacks – Transactions specify • ETH earmarked for gas • gas-rate • Less conservative development culture – "Move fast and break things" – More frequent hard-forks – Expect changes Lab, Part 1 Create Ethereum MetaMask wallet. -
Txspector: Uncovering Attacks in Ethereum from Transactions
TXSPECTOR: Uncovering Attacks in Ethereum from Transactions Mengya Zhang, Xiaokuan Zhang, Yinqian Zhang, and Zhiqiang Lin, The Ohio State University https://www.usenix.org/conference/usenixsecurity20/presentation/zhang-mengya This paper is included in the Proceedings of the 29th USENIX Security Symposium. August 12–14, 2020 978-1-939133-17-5 Open access to the Proceedings of the 29th USENIX Security Symposium is sponsored by USENIX. TXSPECTOR: Uncovering Attacks in Ethereum from Transactions Mengya Zhang∗, Xiaokuan Zhang∗, Yinqian Zhang, Zhiqiang Lin The Ohio State University Abstract However, greater usability also comes with greater risks. The invention of Ethereum smart contract has enabled the Two features have made smart contracts more vulnerable blockchain users to customize computing logic in transactions. to software attacks than traditional software programs. (i) However, similar to traditional computer programs, smart con- Smart contracts are immutable once deployed. This feature tracts have vulnerabilities, which can be exploited to cause is required by any immutable distributed ledgers. As a result, financial loss of contract owners. While there are many soft- vulnerabilities in smart contracts cannot be easily fixed as they ware tools for detecting vulnerabilities in the smart contract cannot be patched. (ii) Ethereum is driven by cryptocurrency; bytecode, few have focused on transactions. In this paper, many popular smart contracts also involve transfers of cryp- we propose TXSPECTOR, a generic, logic-driven framework tocurrency. Therefore, exploitation of smart contracts often to investigate Ethereum transactions for attack detection. At leads to huge financial losses. For instance, in the notorious a high level, TXSPECTOR replays history transactions and DAO attack, the attacker utilized the re-entrancy vulnerability records EVM bytecode-level traces, and then encodes the in The DAO contract and stole more than $50 million [27,42]. -
![Arxiv:1907.02434V1 [Cs.CY] 4 Jul 2019 1 Introduction](https://docslib.b-cdn.net/cover/6379/arxiv-1907-02434v1-cs-cy-4-jul-2019-1-introduction-716379.webp)
Arxiv:1907.02434V1 [Cs.CY] 4 Jul 2019 1 Introduction
Cryptocurrency Egalitarianism: A Quantitative Approach Dimitris Karakostas1,3, Aggelos Kiayias1,3, Christos Nasikas2,4, and Dionysis Zindros2,3 1 University of Edinburgh 2 University of Athens 3 IOHK 4 “ATHENA” Research Center Abstract. Since the invention of Bitcoin one decade ago, numerous cryptocurrencies have sprung into existence. Among these, proof-of-work is the most common mechanism for achieving consensus, whilst a num- ber of coins have adopted “ASIC-resistance” as a desirable property, claiming to be more “egalitarian,” where egalitarianism refers to the power of each coin to participate in the creation of new coins. While proof-of-work consensus dominates the space, several new cryptocurren- cies employ alternative consensus, such as proof-of-stake in which block minting opportunities are based on monetary ownership. A core criti- cism of proof-of-stake revolves around it being less egalitarian by making the rich richer, as opposed to proof-of-work in which everyone can con- tribute equally according to their computational power. In this paper, we give the first quantitative definition of a cryptocurrency’s egalitarian- ism. Based on our definition, we measure the egalitarianism of popular cryptocurrencies that (may or may not) employ ASIC-resistance, among them Bitcoin, Ethereum, Litecoin, and Monero. Our simulations show, as expected, that ASIC-resistance increases a cryptocurrency’s egalitar- ianism. We also measure the egalitarianism of a stake-based protocol, Ouroboros, and a hybrid proof-of-stake/proof-of-work cryptocurrency, Decred. We show that stake-based cryptocurrencies, under correctly se- lected parameters, can be perfectly egalitarian, perhaps contradicting folklore belief. arXiv:1907.02434v1 [cs.CY] 4 Jul 2019 1 Introduction In 2008, Satoshi Nakamoto proposed Bitcoin [25], the first and most suc- cessful cryptocurrency to date. -
A Regulatory System for Optimal Legal Transaction Throughput in Cryptocurrency Blockchains
A Regulatory System for Optimal Legal Transaction Throughput in Cryptocurrency Blockchains Aditya Ahuja Vinay J. Ribeiro Ranjan Pal Indian Institute of Technology Indian Institute of Technology University of Michigan Delhi Bombay Ann Arbor, USA New Delhi, India Mumbai, India [email protected] [email protected] [email protected] ABSTRACT correctness of the underlying computational principles, which are a Permissionless blockchain consensus protocols have been designed basis of the efficacy of these economies. More specifically, in order primarily for defining decentralized economies for the commercial to sustain these cryptocurrency based decentralized economies, trade of assets, both virtual and physical, using cryptocurrencies. blockchain consensus protocols serve as a technical foundation. In most instances, the assets being traded are regulated, which man- Existing blockchain protocols for cryptocurrencies address one dates that the legal right to their trade and their trade value are of (or any combination of) the following system goals: speed, se- determined by the governmental regulator of the jurisdiction in curity and decentralization. Unfortunately, these system goals are which the trade occurs. Unfortunately, existing blockchains do not necessary but insufficient. Illegal activities propelled through the formally recognise proposal of legal cryptocurrency transactions, as strategic use of blockchain based cryptocurrencies, is a serious part of the execution of their respective consensus protocols, result- problem staring at the face of many world governments today ing in rampant illegal activities in the associated crypto-economies. [47]. These illegal activities exploit the permissionless nature of In this contribution, we motivate the need for regulated blockchain the blockchain networks for illegal trade, to strategically defeat consensus protocols with a case study of the illegal, cryptocurrency regulation by obfuscating the jurisdictions of the blockchain users based, Silk Road darknet market. -

Incentives in Ethereum's Hybrid Casper Protocol
Incentives in Ethereum’s Hybrid Casper Protocol Vitalik Buterin∗, Daniel¨ Reijsbergeny, Stefanos Leonardosy, Georgios Piliourasy ∗Ethereum Foundation ySingapore University of Technology and Design Abstract We present an overview of hybrid Casper the Friendly Finality Gadget (FFG): a Proof-of-Stake checkpointing protocol overlaid onto Ethereum’s Proof-of-Work blockchain. We describe its core functionalities and reward scheme, and explore its properties. Our findings indicate that Casper’s implemented incentives mechanism ensures liveness, while providing safety guarantees that improve over standard Proof-of-Work protocols. Based on a minimal-impact implementation of the protocol as a smart contract on the blockchain, we discuss additional issues related to parametrisation, funding, throughput and network overhead and detect potential limitations. Index Terms Proof of Stake, Ethereum, Consensus I. INTRODUCTION In 2008, the seminal Bitcoin paper by Satoshi Nakamoto [50] introduced the blockchain as a means for an open network to extend and reach consensus about a distributed ledger of digital token transfers. The main innovation of Ethereum [16] was to use the blockchain to maintain a history of code creation and execution. As such, Ethereum functions as a global computer that executes code uploaded by users in the form of smart contracts. Like Bitcoin [31], [32], Ethereum’s block proposal mechanism is based on the concept of Proof-of-Work (PoW). In PoW, network participants utilise computational power to win the right to add blocks to the blockchain. However, the alarming global energy consumption of PoW-based blockchains has made the concept increasingly controversial [22], [45], [65]. One of the main alternatives to PoW is virtual mining or Proof-of-Stake (PoS) [1], [5], [46], [55]. -

Building Applications on the Ethereum Blockchain
Building Applications on the Ethereum Blockchain Eoin Woods Endava @eoinwoodz licensed under a Creative Commons Attribution-ShareAlike 4.0 International License 1 Agenda • Blockchain Recap • Ethereum • Application Design • Development • (Solidity – Ethereum’s Language) • Summary 3 Blockchain Recap 4 What is Blockchain? • Enabling technology of Bitcoin, Ethereum, … • Distributed database without a controlling authority • Auditable database with provable lineage • A way to collaborate with parties without direct trust • Architectural component for highly distributed Internet-scale systems 5 Architectural Characteristics of a Blockchain • P2P distributed • (Very) eventual consistency • Append only “ledger” • Computationally expensive • Cryptographic security • Limited query model (key only) (integrity & non-repudiation) • Lack of privacy (often) • Eventual consistency • low throughput scalability • Smart contracts (generally – 10s txn/sec) • Fault tolerant reliability 6 What Makes a Good Blockchain Application? • Multi-organisational • No complex query requirement • No trusted intermediary • Multiple untrusted writers • Need shared source of state • Latency insensitive (e.g. transactions, identity) • Relatively low throughput • Need for immutability (e.g. proof • Need for resiliency of existence) • Transaction interactions • Fairly small data size “If your requirements are fulfilled by today’s relational databases, you’d be insane to use a blockchain” – Gideon Greenspan 7 What is Blockchain being Used For? digital ledger that tracks and derivatives post- verifiable supply chains supply chain efficiency protects valuable assets trade processing Keybase Georgia government Identity management verified data post-trade processing records 8 Public and Permissioned Blockchains Public Permissioned Throughput Low Medium Latency High Medium # Readers High High # Writers High Low Centrally Managed No Yes Transaction Cost High “Free” Based on: Do you need a Blockchain? Karl Wüst, Arthur Gervaisy IACR Cryptology ePrint Archive, 2017, p.375.