An Interview with Tony Hoare ACM 1980 A.M. Turing Award Recipient
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Typology of Programming Languages E Early Languages E
Typology of programming languages e Early Languages E Typology of programming languages Early Languages 1 / 71 The Tower of Babel Typology of programming languages Early Languages 2 / 71 Table of Contents 1 Fortran 2 ALGOL 3 COBOL 4 The second wave 5 The finale Typology of programming languages Early Languages 3 / 71 IBM Mathematical Formula Translator system Fortran I, 1954-1956, IBM 704, a team led by John Backus. Typology of programming languages Early Languages 4 / 71 IBM 704 (1956) Typology of programming languages Early Languages 5 / 71 IBM Mathematical Formula Translator system The main goal is user satisfaction (economical interest) rather than academic. Compiled language. a single data structure : arrays comments arithmetics expressions DO loops subprograms and functions I/O machine independence Typology of programming languages Early Languages 6 / 71 FORTRAN’s success Because: programmers productivity easy to learn by IBM the audience was mainly scientific simplifications (e.g., I/O) Typology of programming languages Early Languages 7 / 71 FORTRAN I C FIND THE MEAN OF N NUMBERS AND THE NUMBER OF C VALUES GREATER THAN IT DIMENSION A(99) REAL MEAN READ(1,5)N 5 FORMAT(I2) READ(1,10)(A(I),I=1,N) 10 FORMAT(6F10.5) SUM=0.0 DO 15 I=1,N 15 SUM=SUM+A(I) MEAN=SUM/FLOAT(N) NUMBER=0 DO 20 I=1,N IF (A(I) .LE. MEAN) GOTO 20 NUMBER=NUMBER+1 20 CONTINUE WRITE (2,25) MEAN,NUMBER 25 FORMAT(11H MEAN = ,F10.5,5X,21H NUMBER SUP = ,I5) STOP TypologyEND of programming languages Early Languages 8 / 71 Fortran on Cards Typology of programming languages Early Languages 9 / 71 Fortrans Typology of programming languages Early Languages 10 / 71 Table of Contents 1 Fortran 2 ALGOL 3 COBOL 4 The second wave 5 The finale Typology of programming languages Early Languages 11 / 71 ALGOL, Demon Star, Beta Persei, 26 Persei Typology of programming languages Early Languages 12 / 71 ALGOL 58 Originally, IAL, International Algebraic Language. -

Kathleen Fisher Question: Interesting Answer in Algol
10/21/08 cs242! Lisp! Algol 60! Algol 68! Pascal! Kathleen Fisher! ML! Modula! Reading: “Concepts in Programming Languages” Chapter 5 except 5.4.5! Haskell! “Real World Haskell”, Chapter 0 and Chapter 1! (http://book.realworldhaskell.org/)! Many other languages:! Algol 58, Algol W, Euclid, EL1, Mesa (PARC), …! Thanks to John Mitchell and Simon Peyton Jones for some of these slides. ! Modula-2, Oberon, Modula-3 (DEC)! Basic Language of 1960! Simple imperative language + functions! Successful syntax, BNF -- used by many successors! real procedure average(A,n); statement oriented! real array A; integer n; No array bounds.! begin … end blocks (like C { … } )! begin if … then … else ! real sum; sum := 0; Recursive functions and stack storage allocation! for i = 1 step 1 until n Fewer ad hoc restrictions than Fortran! do General array references: A[ x + B[3] * y ] sum := sum + A[i]; Type discipline was improved by later languages! average := sum/n No “;” here.! Very influential but not widely used in US! end; Tony Hoare: “Here is a language so far ahead of its time that it was not only an improvement on its predecessors Set procedure return value by assignment.! but also on nearly all of its successors.”! Question:! Holes in type discipline! Is x := x equivalent to doing nothing?! Parameter types can be arrays, but! No array bounds! Interesting answer in Algol:! Parameter types can be procedures, but! No argument or return types for procedure parameters! integer procedure p; begin Problems with parameter passing mechanisms! -
A Universal Modular ACTOR Formalism for Artificial
Artificial Intelligence A Universal Modular ACTOR Formalism for Artificial Intelligence Carl Hewitt Peter Bishop Richard Steiger Abstract This paper proposes a modular ACTOR architecture and definitional method for artificial intelligence that is conceptually based on a single kind of object: actors [or, if you will, virtual processors, activation frames, or streams]. The formalism makes no presuppositions about the representation of primitive data structures and control structures. Such structures can be programmed, micro-coded, or hard wired 1n a uniform modular fashion. In fact it is impossible to determine whether a given object is "really" represented as a list, a vector, a hash table, a function, or a process. The architecture will efficiently run the coming generation of PLANNER-like artificial intelligence languages including those requiring a high degree of parallelism. The efficiency is gained without loss of programming generality because it only makes certain actors more efficient; it does not change their behavioral characteristics. The architecture is general with respect to control structure and does not have or need goto, interrupt, or semaphore primitives. The formalism achieves the goals that the disallowed constructs are intended to achieve by other more structured methods. PLANNER Progress "Programs should not only work, but they should appear to work as well." PDP-1X Dogma The PLANNER project is continuing research in natural and effective means for embedding knowledge in procedures. In the course of this work we have succeeded in unifying the formalism around one fundamental concept: the ACTOR. Intuitively, an ACTOR is an active agent which plays a role on cue according to a script" we" use the ACTOR metaphor to emphasize the inseparability of control and data flow in our model. -

Edsger Dijkstra: the Man Who Carried Computer Science on His Shoulders
INFERENCE / Vol. 5, No. 3 Edsger Dijkstra The Man Who Carried Computer Science on His Shoulders Krzysztof Apt s it turned out, the train I had taken from dsger dijkstra was born in Rotterdam in 1930. Nijmegen to Eindhoven arrived late. To make He described his father, at one time the president matters worse, I was then unable to find the right of the Dutch Chemical Society, as “an excellent Aoffice in the university building. When I eventually arrived Echemist,” and his mother as “a brilliant mathematician for my appointment, I was more than half an hour behind who had no job.”1 In 1948, Dijkstra achieved remarkable schedule. The professor completely ignored my profuse results when he completed secondary school at the famous apologies and proceeded to take a full hour for the meet- Erasmiaans Gymnasium in Rotterdam. His school diploma ing. It was the first time I met Edsger Wybe Dijkstra. shows that he earned the highest possible grade in no less At the time of our meeting in 1975, Dijkstra was 45 than six out of thirteen subjects. He then enrolled at the years old. The most prestigious award in computer sci- University of Leiden to study physics. ence, the ACM Turing Award, had been conferred on In September 1951, Dijkstra’s father suggested he attend him three years earlier. Almost twenty years his junior, I a three-week course on programming in Cambridge. It knew very little about the field—I had only learned what turned out to be an idea with far-reaching consequences. a flowchart was a couple of weeks earlier. -

The Turing Approach Vs. Lovelace Approach
Connecting the Humanities and the Sciences: Part 2. Two Schools of Thought: The Turing Approach vs. The Lovelace Approach* Walter Isaacson, The Jefferson Lecture, National Endowment for the Humanities, May 12, 2014 That brings us to another historical figure, not nearly as famous, but perhaps she should be: Ada Byron, the Countess of Lovelace, often credited with being, in the 1840s, the first computer programmer. The only legitimate child of the poet Lord Byron, Ada inherited her father’s romantic spirit, a trait that her mother tried to temper by having her tutored in math, as if it were an antidote to poetic imagination. When Ada, at age five, showed a preference for geography, Lady Byron ordered that the subject be replaced by additional arithmetic lessons, and her governess soon proudly reported, “she adds up sums of five or six rows of figures with accuracy.” Despite these efforts, Ada developed some of her father’s propensities. She had an affair as a young teenager with one of her tutors, and when they were caught and the tutor banished, Ada tried to run away from home to be with him. She was a romantic as well as a rationalist. The resulting combination produced in Ada a love for what she took to calling “poetical science,” which linked her rebellious imagination to an enchantment with numbers. For many people, including her father, the rarefied sensibilities of the Romantic Era clashed with the technological excitement of the Industrial Revolution. Lord Byron was a Luddite. Seriously. In his maiden and only speech to the House of Lords, he defended the followers of Nedd Ludd who were rampaging against mechanical weaving machines that were putting artisans out of work. -
CODEBREAKING Suggested Reading List (Can Also Be Viewed Online at Good Reads)
MARSHALL LEGACY SERIES: CODEBREAKING Suggested Reading List (Can also be viewed online at Good Reads) NON-FICTION • Aldrich, Richard. Intelligence and the War against Japan. Cambridge: Cambridge University Press, 2000. • Allen, Robert. The Cryptogram Challenge: Over 150 Codes to Crack and Ciphers to Break. Philadelphia: Running Press, 2005 • Briggs, Asa. Secret Days Code-breaking in Bletchley Park. Barnsley: Frontline Books, 2011 • Budiansky, Stephen. Battle of Wits: The Complete Story of Codebreaking in World War Two. New York: Free Press, 2000. • Churchhouse, Robert. Codes and Ciphers: Julius Caesar, the Enigma, and the Internet. Cambridge: Cambridge University Press, 2001. • Clark, Ronald W. The Man Who Broke Purple. London: Weidenfeld and Nicholson, 1977. • Drea, Edward J. MacArthur's Ultra: Codebreaking and the War Against Japan, 1942-1945. Kansas: University of Kansas Press, 1992. • Fisher-Alaniz, Karen. Breaking the Code: A Father's Secret, a Daughter's Journey, and the Question That Changed Everything. Naperville, IL: Sourcebooks, 2011. • Friedman, William and Elizebeth Friedman. The Shakespearian Ciphers Examined. Cambridge: Cambridge University Press, 1957. • Gannon, James. Stealing Secrets, Telling Lies: How Spies and Codebreakers Helped Shape the Twentieth century. Washington, D.C.: Potomac Books, 2001. • Garrett, Paul. Making, Breaking Codes: Introduction to Cryptology. London: Pearson, 2000. • Hinsley, F. H. and Alan Stripp. Codebreakers: the inside story of Bletchley Park. Oxford: Oxford University Press, 1993. • Hodges, Andrew. Alan Turing: The Enigma. New York: Walker and Company, 2000. • Kahn, David. Seizing The Enigma: The Race to Break the German U-boat Codes, 1939-1943. New York: Barnes and Noble Books, 2001. • Kahn, David. The Codebreakers: The Comprehensive History of Secret Communication from Ancient Times to the Internet. -
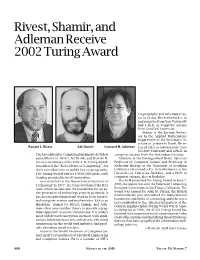
Rivest, Shamir, and Adleman Receive 2002 Turing Award, Volume 50
Rivest, Shamir, and Adleman Receive 2002 Turing Award Cryptography and Information Se- curity Group. He received a B.A. in mathematics from Yale University and a Ph.D. in computer science from Stanford University. Shamir is the Borman Profes- sor in the Applied Mathematics Department of the Weizmann In- stitute of Science in Israel. He re- Ronald L. Rivest Adi Shamir Leonard M. Adleman ceived a B.S. in mathematics from Tel Aviv University and a Ph.D. in The Association for Computing Machinery (ACM) has computer science from the Weizmann Institute. named RONALD L. RIVEST, ADI SHAMIR, and LEONARD M. Adleman is the Distinguished Henry Salvatori ADLEMAN as winners of the 2002 A. M. Turing Award, Professor of Computer Science and Professor of considered the “Nobel Prize of Computing”, for Molecular Biology at the University of Southern their contributions to public key cryptography. California. He earned a B.S. in mathematics at the The Turing Award carries a $100,000 prize, with University of California, Berkeley, and a Ph.D. in funding provided by Intel Corporation. computer science, also at Berkeley. As researchers at the Massachusetts Institute of The ACM presented the Turing Award on June 7, Technology in 1977, the team developed the RSA 2003, in conjunction with the Federated Computing code, which has become the foundation for an en- Research Conference in San Diego, California. The tire generation of technology security products. It award was named for Alan M. Turing, the British mathematician who articulated the mathematical has also inspired important work in both theoret- foundation and limits of computing and who was a ical computer science and mathematics. -

Optimizing the Block Cipher Resource Overhead at the Link Layer Security Framework in the Wireless Sensor Networks
Proceedings of the World Congress on Engineering 2008 Vol I WCE 2008, July 2 - 4, 2008, London, U.K. Optimizing the Block Cipher Resource Overhead at the Link Layer Security Framework in the Wireless Sensor Networks Devesh C. Jinwala, Dhiren R. Patel and Kankar S. Dasgupta, data collected from different sensor nodes. Since the Abstract—The security requirements in Wireless Sensor processing of the data is done on-the-fly, while being Networks (WSNs) and the mechanisms to support the transmitted to the base station; the overall communication requirements, demand a critical examination. Therefore, the costs are reduced [2]. Due to the multi-hop communication security protocols employed in WSNs should be so designed, as and the in-network processing demanding applications, the to yield the optimum performance. The efficiency of the block cipher is, one of the important factors in leveraging the conventional end-to-end security mechanisms are not performance of any security protocol. feasible for the WSN [3]. Hence, the use of the standard In this paper, therefore, we focus on the issue of optimizing end-to-end security protocols like SSH, SSL [4] or IPSec [5] the security vs. performance tradeoff in the security protocols in WSN environment is rejected. Instead, appropriate link in WSNs. As part of the exercise, we evaluate the storage layer security architecture, with low associated overhead is requirements of the block ciphers viz. the Advanced Encryption required. Standard (AES) cipher Rijndael, the Corrected Block Tiny Encryption Algorithm (XXTEA) using the Output Codebook There are a number of research attempts that aim to do so. -

Welcome to AI Matters 5(1)
AI MATTERS, VOLUME 5, ISSUE 1 5(1) 2019 Welcome to AI Matters 5(1) Amy McGovern, co-editor (University of Oklahoma; [email protected]) Iolanda Leite, co-editor (Royal Institute of Technology (KTH); [email protected]) DOI: 10.1145/3320254.3320255 Issue overview receiving the 2018 ACM A.M. Turing Award! Welcome to the first issue of the fifth vol- ume of the AI Matters Newsletter! This issue opens with some news on a new SIGAI Stu- Submit to AI Matters! dent Travel Scholarship where we aim to en- Thanks for reading! Don’t forget to send courage students from traditionally underrep- your ideas and future submissions to AI resented geographic locations to apply and at- Matters! We’re accepting articles and an- tend SIGAI supported events. We also sum- nouncements now for the next issue. De- marize the fourth AAAI/ACM SIGAI Job Fair, tails on the submission process are avail- which continues to grow with the increasing able at http://sigai.acm.org/aimatters. popularity of AI. In our interview series, Marion Neumann interviews Tom Dietterich, an Emer- itus Professor at Oregon State University and one of the pioneers in Machine Learning. Amy McGovern is co- In our regular columns, we have a summary editor of AI Matters. She of recent and upcoming AI conferences and is a Professor of com- events from Michael Rovatsos. Our educa- puter science at the Uni- tional column this issue is dedicated to “biduc- versity of Oklahoma and tive computing”, one of Prolog’s most distinc- an adjunct Professor of tive features. -

Turing's Influence on Programming — Book Extract from “The Dawn of Software Engineering: from Turing to Dijkstra”
Turing's Influence on Programming | Book extract from \The Dawn of Software Engineering: from Turing to Dijkstra" Edgar G. Daylight∗ Eindhoven University of Technology, The Netherlands [email protected] Abstract Turing's involvement with computer building was popularized in the 1970s and later. Most notable are the books by Brian Randell (1973), Andrew Hodges (1983), and Martin Davis (2000). A central question is whether John von Neumann was influenced by Turing's 1936 paper when he helped build the EDVAC machine, even though he never cited Turing's work. This question remains unsettled up till this day. As remarked by Charles Petzold, one standard history barely mentions Turing, while the other, written by a logician, makes Turing a key player. Contrast these observations then with the fact that Turing's 1936 paper was cited and heavily discussed in 1959 among computer programmers. In 1966, the first Turing award was given to a programmer, not a computer builder, as were several subsequent Turing awards. An historical investigation of Turing's influence on computing, presented here, shows that Turing's 1936 notion of universality became increasingly relevant among programmers during the 1950s. The central thesis of this paper states that Turing's in- fluence was felt more in programming after his death than in computer building during the 1940s. 1 Introduction Many people today are led to believe that Turing is the father of the computer, the father of our digital society, as also the following praise for Martin Davis's bestseller The Universal Computer: The Road from Leibniz to Turing1 suggests: At last, a book about the origin of the computer that goes to the heart of the story: the human struggle for logic and truth. -
Simula Mother Tongue for a Generation of Nordic Programmers
Simula! Mother Tongue! for a Generation of! Nordic Programmers! Yngve Sundblad HCI, CSC, KTH! ! KTH - CSC (School of Computer Science and Communication) Yngve Sundblad – Simula OctoberYngve 2010Sundblad! Inspired by Ole-Johan Dahl, 1931-2002, and Kristen Nygaard, 1926-2002" “From the cold waters of Norway comes Object-Oriented Programming” " (first line in Bertrand Meyer#s widely used text book Object Oriented Software Construction) ! ! KTH - CSC (School of Computer Science and Communication) Yngve Sundblad – Simula OctoberYngve 2010Sundblad! Simula concepts 1967" •# Class of similar Objects (in Simula declaration of CLASS with data and actions)! •# Objects created as Instances of a Class (in Simula NEW object of class)! •# Data attributes of a class (in Simula type declared as parameters or internal)! •# Method attributes are patterns of action (PROCEDURE)! •# Message passing, calls of methods (in Simula dot-notation)! •# Subclasses that inherit from superclasses! •# Polymorphism with several subclasses to a superclass! •# Co-routines (in Simula Detach – Resume)! •# Encapsulation of data supporting abstractions! ! KTH - CSC (School of Computer Science and Communication) Yngve Sundblad – Simula OctoberYngve 2010Sundblad! Simula example BEGIN! REF(taxi) t;" CLASS taxi(n); INTEGER n;! BEGIN ! INTEGER pax;" PROCEDURE book;" IF pax<n THEN pax:=pax+1;! pax:=n;" END of taxi;! t:-NEW taxi(5);" t.book; t.book;" print(t.pax)" END! Output: 7 ! ! KTH - CSC (School of Computer Science and Communication) Yngve Sundblad – Simula OctoberYngve 2010Sundblad! -

Submission Data for 2020-2021 CORE Conference Ranking Process International Symposium on Formal Methods (Was Formal Methods Europe FME)
Submission Data for 2020-2021 CORE conference Ranking process International Symposium on Formal Methods (was Formal Methods Europe FME) Ana Cavalcanti, Stefania Gnesi, Lars-Henrik Eriksson, Nico Plat, Einar Broch Johnsen, Maurice ter Beek Conference Details Conference Title: International Symposium on Formal Methods (was Formal Methods Europe FME) Acronym : FM Rank: A Data and Metrics Google Scholar Metrics sub-category url: https://scholar.google.com.au/citations?view_op=top_venues&hl=en&vq=eng_theoreticalcomputerscienceposition in sub-category: 20+Image of top 20: ACM Metrics Not Sponsored by ACM Aminer Rank 1 Aminer Rank: 28Name in Aminer: World Congress on Formal MethodsAcronym or Shorthand: FMh-5 Index: 17CCF: BTHU: âĂŞ Top Aminer Cites: http://portal.core.edu.au/core/media/conf_submissions_citations/extra_info1804_aminer_top_cite.png Other Rankings Not aware of any other Rankings Conferences in area: 1. Formal Methods Symposium (FM) 2. Software Engineering and Formal Methods (SEFM), Integrated Formal Methods (IFM) 3. Fundamental Approaches to Software Engineering (FASE), NASA Formal Methods (NFM), Runtime Verification (RV) 4. Formal Aspects of Component Software (FACS), Automated Technology for Verification and Analysis (ATVA) 5. International Conference on Formal Engineering Methods (ICFEM), FormaliSE, Formal Methods in Computer-Aided Design (FMCAD), Formal Methods for Industrial Critical Systems (FMICS) 6. Brazilian Symposium on Formal Methods (SBMF), Theoretical Aspects of Software Engineering (TASE) 7. International Symposium On Leveraging Applications of Formal Methods, Verification and Validation (ISoLA) Top People Publishing Here name: Frank de Boer justification: h-index: 42 ( https://www.cwi.nl/people/frank-de-boer) Frank S. de Boer is senior researcher at the CWI, where he leads the research group on Formal Methods, and Professor of Software Correctness at Leiden University, The Netherlands.