PRE LIM INARY KDII-D Processor Manual (PDP-Ll/04)
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

University of California at Berkeley College of Engineering Department of Electrical Engineering and Computer Science
University of California at Berkeley College of Engineering Department of Electrical Engineering and Computer Science EECS 61C, Fall 2003 Lab 2: Strings and pointers; the GDB debugger PRELIMINARY VERSION Goals To learn to use the gdb debugger to debug string and pointer programs in C. Reading Sections 5.1-5.5, in K&R GDB Reference Card (linked to class page under “resources.”) Optional: Complete GDB documentation (http://www.gnu.org/manual/gdb-5.1.1/gdb.html) Note: GDB currently only works on the following machines: • torus.cs.berkeley.edu • rhombus.cs.berkeley.edu • pentagon.cs.berkeley.edu Please ssh into one of these machines before starting the lab. Basic tasks in GDB There are two ways to start the debugger: 1. In EMACS, type M-x gdb, then type gdb <filename> 2. Run gdb <filename> from the command line The following are fundamental operations in gdb. Please make sure you know the gdb commands for the following operations before you proceed. 1. How do you run a program in gdb? 2. How do you pass arguments to a program when using gdb? 3. How do you set a breakpoint in a program? 4. How do you set a breakpoint which which only occurs when a set of conditions is true (eg when certain variables are a certain value)? 5. How do you execute the next line of C code in the program after a break? 1 6. If the next line is a function call, you'll execute the call in one step. How do you execute the C code, line by line, inside the function call? 7. -

M32R Debugger and Trace
M32R Debugger and Trace TRACE32 Online Help TRACE32 Directory TRACE32 Index TRACE32 Documents ...................................................................................................................... ICD In-Circuit Debugger ................................................................................................................ Processor Architecture Manuals .............................................................................................. M32R ......................................................................................................................................... M32R Debugger and Trace .................................................................................................. 1 Introduction ....................................................................................................................... 4 Brief Overview of Documents for New Users 4 Warning .............................................................................................................................. 5 Quick Start ......................................................................................................................... 6 Troubleshooting ................................................................................................................ 9 SYStem.Up Errors 9 Memory Access Errors 9 FAQ ..................................................................................................................................... 9 CPU specific SYStem Settings and Restrictions .......................................................... -

Tricore™ Tricore™ V1.6 Microcontrollers User Manual
TriCore™ 32-bit TriCore™ V1.6 Core Architecture 32-bit Unified Processor Core User Manual (Volume 1) V1.0, 2012-05 Microcontrollers Edition 2012-05 Published by Infineon Technologies AG 81726 Munich, Germany © 2012 Infineon Technologies AG All Rights Reserved. Legal Disclaimer The information given in this document shall in no event be regarded as a guarantee of conditions or characteristics. With respect to any examples or hints given herein, any typical values stated herein and/or any information regarding the application of the device, Infineon Technologies hereby disclaims any and all warranties and liabilities of any kind, including without limitation, warranties of non-infringement of intellectual property rights of any third party. Information For further information on technology, delivery terms and conditions and prices, please contact the nearest Infineon Technologies Office (www.infineon.com). Warnings Due to technical requirements, components may contain dangerous substances. For information on the types in question, please contact the nearest Infineon Technologies Office. Infineon Technologies components may be used in life-support devices or systems only with the express written approval of Infineon Technologies, if a failure of such components can reasonably be expected to cause the failure of that life-support device or system or to affect the safety or effectiveness of that device or system. Life support devices or systems are intended to be implanted in the human body or to support and/or maintain and sustain and/or protect human life. If they fail, it is reasonable to assume that the health of the user or other persons may be endangered. -
Mac OS 8 Update
K Service Source Mac OS 8 Update Known problems, Internet Access, and Installation Mac OS 8 Update Document Contents - 1 Document Contents • Introduction • About Mac OS 8 • About Internet Access What To Do First Additional Software Auto-Dial and Auto-Disconnect Settings TCP/IP Connection Options and Internet Access Length of Configuration Names Modem Scripts & Password Length Proxies and Other Internet Config Settings Web Browser Issues Troubleshooting • About Mac OS Runtime for Java Version 1.0.2 • About Mac OS Personal Web Sharing • Installing Mac OS 8 • Upgrading Workgroup Server 9650 & 7350 Software Mac OS 8 Update Introduction - 2 Introduction Mac OS 8 is the most significant update to the Macintosh operating system since 1984. The updated system gives users PowerPC-native multitasking, an efficient desktop with new pop-up windows and spring-loaded folders, and a fully integrated suite of Internet services. This document provides information about Mac OS 8 that supplements the information in the Mac OS installation manual. For a detailed description of Mac OS 8, useful tips for using the system, troubleshooting, late-breaking news, and links for online technical support, visit the Mac OS Info Center at http://ip.apple.com/infocenter. Or browse the Mac OS 8 topic in the Apple Technical Library at http:// tilsp1.info.apple.com. Mac OS 8 Update About Mac OS 8 - 3 About Mac OS 8 Read this section for information about known problems with the Mac OS 8 update and possible solutions. Known Problems and Compatibility Issues Apple Language Kits and Mac OS 8 Apple's Language Kits require an updater for full functionality with this version of the Mac OS. -

Debugging a Program
Debugging a Program SunPro A Sun Microsystems, Inc. Business 2550 Garcia Avenue Mountain View, CA 94043 U.S.A. Part No: 801-5106-10 Revision A December 1993 1993 Sun Microsystems, Inc. 2550 Garcia Avenue, Mountain View, California 94043-1100 U.S.A. All rights reserved. This product and related documentation are protected by copyright and distributed under licenses restricting its use, copying, distribution, and decompilation. No part of this product or related documentation may be reproduced in any form by any means without prior written authorization of Sun and its licensors, if any. Portions of this product may be derived from the UNIX® and Berkeley 4.3 BSD systems, licensed from UNIX System Laboratories, Inc. and the University of California, respectively. Third-party font software in this product is protected by copyright and licensed from Sun’s Font Suppliers. RESTRICTED RIGHTS LEGEND: Use, duplication, or disclosure by the United States Government is subject to the restrictions set forth in DFARS 252.227-7013 (c)(1)(ii) and FAR 52.227-19. The product described in this manual may be protected by one or more U.S. patents, foreign patents, or pending applications. TRADEMARKS Sun, Sun Microsystems, the Sun logo, SunPro, SunPro logo, Sun-4, SunOS, Solaris, ONC, OpenWindows, ToolTalk, AnswerBook, and Magnify Help are trademarks or registered trademarks of Sun Microsystems, Inc. UNIX and OPEN LOOK are registered trademarks of UNIX System Laboratories, Inc., a wholly owned subsidiary of Novell, Inc. All other product names mentioned herein are the trademarks of their respective owners. All SPARC trademarks, including the SCD Compliant Logo, are trademarks or registered trademarks of SPARC International, Inc. -

Exceptions and Processes
Exceptions and Processes! Jennifer Rexford! The material for this lecture is drawn from! Computer Systems: A Programmerʼs Perspective (Bryant & O"Hallaron) Chapter 8! 1 Goals of this Lecture! •#Help you learn about:! •# Exceptions! •# The process concept! … and thereby…! •# How operating systems work! •# How applications interact with OS and hardware! The process concept is one of the most important concepts in systems programming! 2 Context of this Lecture! Second half of the course! Previously! Starting Now! C Language! Application Program! language! service! levels! Assembly Language! levels! Operating System! tour! tour! Machine Language! Hardware! Application programs, OS,! and hardware interact! via exceptions! 3 Motivation! Question:! •# How does a program get input from the keyboard?! •# How does a program get data from a (slow) disk?! Question:! •# Executing program thinks it has exclusive control of CPU! •# But multiple programs share one CPU (or a few CPUs)! •# How is that illusion implemented?! Question:! •# Executing program thinks it has exclusive use of memory! •# But multiple programs must share one memory! •# How is that illusion implemented?! Answers: Exceptions…! 4 Exceptions! •# Exception! •# An abrupt change in control flow in response to a change in processor state! •# Examples:! •# Application program:! •# Requests I/O! •# Requests more heap memory! •# Attempts integer division by 0! •# Attempts to access privileged memory! Synchronous! •# Accesses variable that is not$ in real memory (see upcoming $ “Virtual Memory” lecture)! •# User presses key on keyboard! Asynchronous! •# Disk controller finishes reading data! 5 Exceptions Note! •# Note:! ! !Exceptions in OS % exceptions in Java! Implemented using! try/catch! and throw statements! 6 Exceptional Control Flow! Application! Exception handler! program! in operating system! exception! exception! processing! exception! return! (optional)! 7 Exceptions vs. -

Providing Memory Performance Feedback in Modern Processors
Informing Memory Operations: Providing Memory Performance Feedback in Modern Processors Mark Horowitz Margaret Martonosi Todd C. Mowry Michael D. Smith Computer Systems Department of Department of Electrical Division of Laboratory Electrical Engineering and Computer Engineering Applied Sciences Stanford University Princeton University University of Toronto Harvard University [email protected] [email protected] [email protected] [email protected] Abstract other purely hardware-based mechanisms (e.g., stream buffers [Jou90]) are complete solutions. Memory latency is an important bottleneck in system performance that cannot be adequately solved by hardware alone. Several prom- In addition to hardware mechanisms, a number of promising soft- ising software techniques have been shown to address this problem ware techniques have been proposed to avoid or tolerate memory successfully in specific situations. However, the generality of these latency. These software techniques have resorted to a variety of software approaches has been limited because current architectures different approaches for gathering information and reasoning about do not provide a fine-grained, low-overhead mechanism for memory performance. Compiler-based techniques, such as cache observing and reacting to memory behavior directly. To fill this blocking [AKL79,GJMS87,WL91] and prefetching [MLG92, need, we propose a new class of memory operations called inform- Por89] use static program analysis to predict which references are ing memory operations, which essentially consist of a memory likely to suffer misses. Memory performance tools have relied on operation combined (either implicitly or explicitly) with a condi- sampling or simulation-based approaches to gather memory statis- tional branch-and-link operation that is taken only if the reference tics [CMM+88,DBKF90,GH93,LW94,MGA95]. -
Processes, System Calls and More
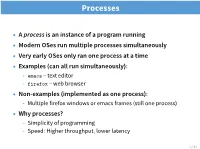
Processes • A process is an instance of a program running • Modern OSes run multiple processes simultaneously • Very early OSes only ran one process at a time • Examples (can all run simultaneously): - emacs – text editor - firefox – web browser • Non-examples (implemented as one process): - Multiple firefox windows or emacs frames (still one process) • Why processes? - Simplicity of programming - Speed: Higher throughput, lower latency 1 / 43 A process’s view of the world • Each process has own view of machine - Its own address space - Its own open files - Its own virtual CPU (through preemptive multitasking) • *(char *)0xc000 dierent in P1 & P2 • Simplifies programming model - gcc does not care that firefox is running • Sometimes want interaction between processes - Simplest is through files: emacs edits file, gcc compiles it - More complicated: Shell/command, Window manager/app. 2 / 43 Outline 1 Application/Kernel Interface 2 User view of processes 3 Kernel view of processes 3 / 43 System Calls • Systems calls are the interface between processes and the kernel • A process invokes a system call to request operating system services • fork(), waitpid(), open(), close() • Note: Signals are another common mechanism to allow the kernel to notify the application of an important event (e.g., Ctrl-C) - Signals are like interrupts/exceptions for application code 4 / 43 System Call Soware Stack Application 1 5 Syscall Library unprivileged code 4 2 privileged 3 code Kernel 5 / 43 Kernel Privilege • Hardware provides two or more privilege levels (or protection rings) • Kernel code runs at a higher privilege level than applications • Typically called Kernel Mode vs. User Mode • Code running in kernel mode gains access to certain CPU features - Accessing restricted features (e.g. -

NI Vxipc-486 500 Series Lynxos Manual
Full-service, independent repair center -~ ARTISAN® with experienced engineers and technicians on staff. TECHNOLOGY GROUP ~I We buy your excess, underutilized, and idle equipment along with credit for buybacks and trade-ins. Custom engineering Your definitive source so your equipment works exactly as you specify. for quality pre-owned • Critical and expedited services • Leasing / Rentals/ Demos equipment. • In stock/ Ready-to-ship • !TAR-certified secure asset solutions Expert team I Trust guarantee I 100% satisfaction Artisan Technology Group (217) 352-9330 | [email protected] | artisantg.com All trademarks, brand names, and brands appearing herein are the property o f their respective owners. Find the National Instruments VXIpc-486 Model 566 at our website: Click HERE Getting Started with Your NI-VXI™ Software for the VXIpc™-486 Model 500 Series and LynxOS bus September 1995 Edition Part Number 321006A-01 © Copyright 1995 National Instruments Corporation. All Rights Reserved. National Instruments Corporate Headquarters 6504 Bridge Point Parkway Austin, TX 78730-5039 (512) 794-0100 Technical support fax: (800) 328-2203 (512) 794-5678 Branch Offices: Australia 03 9 879 9422, Austria 0662 45 79 90 0, Belgium 02 757 00 20, Canada (Ontario) 519 622 9310, Canada (Québec) 514 694 8521, Denmark 45 76 26 00, Finland 90 527 2321, France 1 48 14 24 24, Germany 089 741 31 30, Hong Kong 2645 3186, Italy 02 48301892, Japan 03 5472 2970, Korea 02 596 7456, Mexico 95 800 010 0793, Netherlands 0348 433466, Norway 32 84 84 00, Singapore 2265886, Spain 91 640 0085, Sweden 08 730 49 70, Switzerland 056 200 51 51, Taiwan 02 377 1200, U.K. -

Chapter 3 Protected-Mode Memory Management
CHAPTER 3 PROTECTED-MODE MEMORY MANAGEMENT This chapter describes the Intel 64 and IA-32 architecture’s protected-mode memory management facilities, including the physical memory requirements, segmentation mechanism, and paging mechanism. See also: Chapter 5, “Protection” (for a description of the processor’s protection mechanism) and Chapter 20, “8086 Emulation” (for a description of memory addressing protection in real-address and virtual-8086 modes). 3.1 MEMORY MANAGEMENT OVERVIEW The memory management facilities of the IA-32 architecture are divided into two parts: segmentation and paging. Segmentation provides a mechanism of isolating individual code, data, and stack modules so that multiple programs (or tasks) can run on the same processor without interfering with one another. Paging provides a mech- anism for implementing a conventional demand-paged, virtual-memory system where sections of a program’s execution environment are mapped into physical memory as needed. Paging can also be used to provide isolation between multiple tasks. When operating in protected mode, some form of segmentation must be used. There is no mode bit to disable segmentation. The use of paging, however, is optional. These two mechanisms (segmentation and paging) can be configured to support simple single-program (or single- task) systems, multitasking systems, or multiple-processor systems that used shared memory. As shown in Figure 3-1, segmentation provides a mechanism for dividing the processor’s addressable memory space (called the linear address space) into smaller protected address spaces called segments. Segments can be used to hold the code, data, and stack for a program or to hold system data structures (such as a TSS or LDT). -

Definition of Terms Introduction Trap Are a Mechanism To
Eidgenössische Definition of Terms Technische Hochschule Zürich Interrupt: Asynchronous interruption of the instruction flow Programming in Systems Caused by external event! (37-023) Hit program execution in Programming in Assembler «between» 2 Instructions Basics of Operating Systems Exception: Unexpected event during Models of Computer Architecture program execution (division by zero, page fault) Lecturer today: Prof. Thomas M. Stricker Hits «during» an instruction Text-/Reference-Books: Trap: Software generated Inter- R.P.Paul: SPARC Architecture... and C rupt Sun SPARC V8 Manual and K&R C Reference Caused by an exception or by an explicit trap instruction Topics of Today: (e.g. for a system call) • Traps, Exceptions and Supervisor Mode Supervisor Privileged execution mode • SPARC V8 Trap Model Mode: in contrast to User Mode • Traps in tkisem System Calls, Interrupt-, • Register Window Trap-Handlers Exception- and Traphandler execute in supervisor mode. 9/14.1.02 - 1 37-023 Systemprogrammierung © Alonso/Stricker 9/14.1.02 - 2 37-023 Systemprogrammierung © Alonso/Stricker Introduction Trap are a mechanism to... Standard library in C (libc.a) provides ... avoid programming mistakes with sys- two different kind of functions: tem resources. • pure library functions ... share common system resources in a fair way under OS control. • self contained code (sin, printf...) ... prevent access to protected memory • «visible» execution in user mode. segments. • examination in single-step mode of ... catch Instructions which would lead to the debugger possible. error conditions and inconsistent sys- • glue code to system calls tem state (z.B. Division by 0, Window- (read, write, open, close...) Overflow). • «invisible» execution ➜ Two modes of execution: Supervisor and User Mode • call some code in the operating system (Trap) ➜ Traps: • execute in supervisor mode Mechanism to get into/return from supervisor mode. -

Low-Overhead Call Path Profiling of Unmodified, Optimized Code
Low-Overhead Call Path Profiling of Unmodified, Optimized Code Nathan Froyd John Mellor-Crummey Rob Fowler [email protected] [email protected] [email protected] Rice University, Houston, TX ABSTRACT tiple places. To understand the performance implications of Call path profiling associates resource consumption with data copying in such applications, it can thus be necessary the calling context in which resources were consumed. We to attribute costs at all of these levels. To do this in general describe the design and implementation of a low-overhead requires an efficient data collection mechanism that tracks call path profiler based on stack sampling. The profiler costs along entire call paths. Since understanding and im- uses a novel sample-driven strategy for collecting frequency proving the on-node performance of MPI programs is a key counts for call graph edges without instrumenting every pro- factor in overall performance, context-sensitive profiling is cedure’s code to count them. The data structures and al- of particular importance for large-scale parallel systems. gorithms used are efficient enough to construct the com- An ideal profiler should have the following properties. plete calling context tree exposed during sampling. The First, it should collect performance measurements with low, profiler leverages information recorded by compilers for de- controllable overhead; this makes it feasible to collect pro- bugging or exception handling to record call path profiles file information during production runs as well as during even for highly-optimized code. We describe an implemen- development. Second, it should identify differences in the tation for the Tru64/Alpha platform.