Differentiating Code from Data in X86 Binaries
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Fill Your Boots: Enhanced Embedded Bootloader Exploits Via Fault Injection and Binary Analysis
IACR Transactions on Cryptographic Hardware and Embedded Systems ISSN 2569-2925, Vol. 2021, No. 1, pp. 56–81. DOI:10.46586/tches.v2021.i1.56-81 Fill your Boots: Enhanced Embedded Bootloader Exploits via Fault Injection and Binary Analysis Jan Van den Herrewegen1, David Oswald1, Flavio D. Garcia1 and Qais Temeiza2 1 School of Computer Science, University of Birmingham, UK, {jxv572,d.f.oswald,f.garcia}@cs.bham.ac.uk 2 Independent Researcher, [email protected] Abstract. The bootloader of an embedded microcontroller is responsible for guarding the device’s internal (flash) memory, enforcing read/write protection mechanisms. Fault injection techniques such as voltage or clock glitching have been proven successful in bypassing such protection for specific microcontrollers, but this often requires expensive equipment and/or exhaustive search of the fault parameters. When multiple glitches are required (e.g., when countermeasures are in place) this search becomes of exponential complexity and thus infeasible. Another challenge which makes embedded bootloaders notoriously hard to analyse is their lack of debugging capabilities. This paper proposes a grey-box approach that leverages binary analysis and advanced software exploitation techniques combined with voltage glitching to develop a powerful attack methodology against embedded bootloaders. We showcase our techniques with three real-world microcontrollers as case studies: 1) we combine static and on-chip dynamic analysis to enable a Return-Oriented Programming exploit on the bootloader of the NXP LPC microcontrollers; 2) we leverage on-chip dynamic analysis on the bootloader of the popular STM8 microcontrollers to constrain the glitch parameter search, achieving the first fully-documented multi-glitch attack on a real-world target; 3) we apply symbolic execution to precisely aim voltage glitches at target instructions based on the execution path in the bootloader of the Renesas 78K0 automotive microcontroller. -
Radare2 Book
Table of Contents introduction 1.1 Introduction 1.2 History 1.2.1 Overview 1.2.2 Getting radare2 1.2.3 Compilation and Portability 1.2.4 Compilation on Windows 1.2.5 Command-line Flags 1.2.6 Basic Usage 1.2.7 Command Format 1.2.8 Expressions 1.2.9 Rax2 1.2.10 Basic Debugger Session 1.2.11 Contributing to radare2 1.2.12 Configuration 1.3 Colors 1.3.1 Common Configuration Variables 1.3.2 Basic Commands 1.4 Seeking 1.4.1 Block Size 1.4.2 Sections 1.4.3 Mapping Files 1.4.4 Print Modes 1.4.5 Flags 1.4.6 Write 1.4.7 Zoom 1.4.8 Yank/Paste 1.4.9 Comparing Bytes 1.4.10 Visual mode 1.5 Visual Disassembly 1.5.1 2 Searching bytes 1.6 Basic Searches 1.6.1 Configurating the Search 1.6.2 Pattern Search 1.6.3 Automation 1.6.4 Backward Search 1.6.5 Search in Assembly 1.6.6 Searching for AES Keys 1.6.7 Disassembling 1.7 Adding Metadata 1.7.1 ESIL 1.7.2 Scripting 1.8 Loops 1.8.1 Macros 1.8.2 R2pipe 1.8.3 Rabin2 1.9 File Identification 1.9.1 Entrypoint 1.9.2 Imports 1.9.3 Symbols (exports) 1.9.4 Libraries 1.9.5 Strings 1.9.6 Program Sections 1.9.7 Radiff2 1.10 Binary Diffing 1.10.1 Rasm2 1.11 Assemble 1.11.1 Disassemble 1.11.2 Ragg2 1.12 Analysis 1.13 Code Analysis 1.13.1 Rahash2 1.14 Rahash Tool 1.14.1 Debugger 1.15 3 Getting Started 1.15.1 Registers 1.15.2 Remote Access Capabilities 1.16 Remoting Capabilities 1.16.1 Plugins 1.17 Plugins 1.17.1 Crackmes 1.18 IOLI 1.18.1 IOLI 0x00 1.18.1.1 IOLI 0x01 1.18.1.2 Avatao 1.18.2 R3v3rs3 4 1.18.2.1 .intro 1.18.2.1.1 .radare2 1.18.2.1.2 .first_steps 1.18.2.1.3 .main 1.18.2.1.4 .vmloop 1.18.2.1.5 .instructionset 1.18.2.1.6 -

Reverse Software Engineering As a Project-Based Learning Tool
Paper ID #33764 Reverse Software Engineering as a Project-Based Learning Tool Ms. Cynthia C. Fry, Baylor University CYNTHIA C. FRY is currently a Senior Lecturer of Computer Science at Baylor University. She worked at NASA’s Marshall Space Flight Center as a Senior Project Engineer, a Crew Training Manager, and the Science Operations Director for STS-46. She was an Engineering Duty Officer in the U.S. Navy (IRR), and worked with the Naval Maritime Intelligence Center as a Scientific/Technical Intelligence Analyst. She was the owner and chief systems engineer for Systems Engineering Services (SES), a computer systems design, development, and consultation firm. She joined the faculty of the School of Engineering and Computer Science at Baylor University in 1997, where she teaches a variety of engineering and computer science classes, she is the Faculty Advisor for the Women in Computer Science (WiCS), the Director of the Computer Science Fellows program, and is a KEEN Fellow. She has authored and co- authored over fifty peer-reviewed papers. Mr. Zachary Michael Steudel Zachary Steudel is a 2021 graduate of Baylor University’s computer science department. In his time at Baylor, he worked as a Teaching Assistant under Ms. Cynthia C. Fry. As part of the Teaching Assistant role, Zachary designed and created the group project for the Computer Systems course. Zachary Steudel worked as a Software Developer Intern at Amazon in the Summer of 2019, a Software Engineer Intern at Microsoft in the Summer of 2020, and begins his full-time career with Amazon in the summer of 2021 as a software engineer. -

Reassembleable Disassembling
Reassembleable Disassembling Shuai Wang, Pei Wang, and Dinghao Wu College of Information Sciences and Technology The Pennsylvania State University fszw175, pxw172, [email protected] Abstract struction level to enforce certain security policies. To ensure program control-flow integrity (CFI, meaning that Reverse engineering has many important applications in program execution is dictated to a predetermined control- computer security, one of which is retrofitting software flow graph) [1,4, 43, 17, 29, 37] without source code, the for safety and security hardening when source code is not original control-flow graph must be recovered from a bi- available. By surveying available commercial and aca- nary executable and the binary must be retrofitted with demic reverse engineering tools, we surprisingly found the CFI enforcement facility embedded [50, 49]. Sym- that no existing tool is able to disassemble executable bolic taint analysis [34] on binaries must recover assem- binaries into assembly code that can be correctly assem- bly code and data faithfully. The defending techniques bled back in a fully automated manner, even for simple against return-oriented programming (ROP) attacks also programs. Actually in many cases, the resulted disas- rely on binary analysis and reconstruction to identify and sembled code is far from a state that an assembler ac- eliminate ROP gadgets [44,9, 47, 22, 39]. cepts, which is hard to fix even by manual effort. This Despite the fact that many security hardening tech- has become a severe obstacle. People have tried to over- niques are highly dependent on reverse engineering, flex- come it by patching or duplicating new code sections for ible and easy-to-use binary manipulation itself remains retrofitting of executables, which is not only inefficient an unsolved problem. -

A Survey of Reverse Engineering Tools for the 32-Bit Microsoft Windows Environment
A Survey of Reverse Engineering Tools for the 32-Bit Microsoft Windows Environment RAYMOND J. CANZANESE, JR., MATTHEW OYER, SPIROS MANCORIDIS, and MOSHE KAM College of Engineering Drexel University, Philadelphia, PA, USA Reverse engineering is defined by Chikosfky and Cross as the process of analyzing a subject system to identify the system's components and their relationships, and to create representations of the system in another form or at a higher level of abstraction. The process of reverse engineering is accomplished using specific tools that, for the 32-bit Microsoft Windows environment, are categorized as hex editors, disassemblers/debuggers, decompilers, or related technologies such as code obfuscators, unpackers, and PE editors. An evaluation of each tool is provided that identifies its domain of applicability and usability. Categories and Subject Descriptors: A.1 [General]: Introductory and Survey; D.2.5 [Software Engineering]: Testing and Debugging General Terms: Security, Documentation Additional Key Words and Phrases: Reverse Engineering, Disassemblers, Debuggers, Decompilers, Code Obfuscators, PE Editors Unpackers, Hex Editors 1. INTRODUCTION 1.1 The Reverse Engineering Process Software engineers are sometimes asked to understand the behavior of a program given that program's binary executable file. If they have access to the appropriate reverse engineering tools, they might choose to adhere to the following process. First, a general disassembler/debugger is used to determine the basic functionality of the program. If disassembly and debugging shows that the binary code has been obfuscated, the next step would be to determine whether the obfuscator used is a common commercial obfuscator or a custom protection scheme. A PE editor would be used to make this determination. -

Implementing the UCSD PASCAL System on the MODCOMP Computer
TDA Progress Report 42-60 September and October 1960 Implementing the UCSD PASCAL System on the MODCOMP Computer T. Wolfe DSN Data Systems Section This article describes the UCSD PASCAL system developed by the University of California, San Diego, now available on the MODCOMP computer. The system includes a Pascal compiler and many useful utility programs. A BASIC compiler and a FORTRAN 77 compiler are also avatkble. There is currently a large amount of software availabie written in UCSD PASCAL, including a data base system, word processing systems and a MODULA compiler. I. Introduction Assembly language subroutines thus produced may also be called from either Pascal or FORTRAN. Currently the assem- The UCSD PASCAL* System is a complete interactive bler has not been modified to produce MODCOMP machine software development system consisting of an operating sys- code. A system library program may be used to build libraries tem, compilers (Pascal, BASIC, FORTRAN 77) two text of useful subroutines and the system linker used to link them editors (screen editor and line-oriented editor), a linker and to user programs. many useful utility programs. The system is written and main- tained in Pascal. The compiler generates code for an idealized processor known as the “pseudo-machine.” The “pseudo- Interpreters currently exist for Z80/8080, PDP 11 /LSI-1 1, code” (p-code) generated by the compiler is interpreted at 6800, 9900 and 6502 computers and are being developed for runtime by a program (known as the interpreter) which emu- other computers. Thus, software could be developed on an lates the pseudo-machine. -
V850 Series Development Environment Pamphlet
To our customers, Old Company Name in Catalogs and Other Documents On April 1st, 2010, NEC Electronics Corporation merged with Renesas Technology Corporation, and Renesas Electronics Corporation took over all the business of both companies. Therefore, although the old company name remains in this document, it is a valid Renesas Electronics document. We appreciate your understanding. Renesas Electronics website: http://www.renesas.com April 1st, 2010 Renesas Electronics Corporation Issued by: Renesas Electronics Corporation (http://www.renesas.com) Send any inquiries to http://www.renesas.com/inquiry. Notice 1. All information included in this document is current as of the date this document is issued. Such information, however, is subject to change without any prior notice. Before purchasing or using any Renesas Electronics products listed herein, please confirm the latest product information with a Renesas Electronics sales office. Also, please pay regular and careful attention to additional and different information to be disclosed by Renesas Electronics such as that disclosed through our website. 2. Renesas Electronics does not assume any liability for infringement of patents, copyrights, or other intellectual property rights of third parties by or arising from the use of Renesas Electronics products or technical information described in this document. No license, express, implied or otherwise, is granted hereby under any patents, copyrights or other intellectual property rights of Renesas Electronics or others. 3. You should not alter, modify, copy, or otherwise misappropriate any Renesas Electronics product, whether in whole or in part. 4. Descriptions of circuits, software and other related information in this document are provided only to illustrate the operation of semiconductor products and application examples. -
X86-64 Calling Conventions
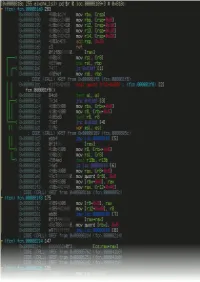
CSE 351: The Hardware/Software Interface Section 4 Procedure calls Procedure calls In x86 assembly, values are passed to function calls on the stack Perks: Concise, easy to remember Drawbacks: Always requires memory accesses In x86-64 assembly, values are passed to function calls in registers Perks: Less wasted space, faster Drawbacks: Potentially requires a lot of register manipulation 2/23/2014 2 x86 calling conventions Simply push arguments onto the stack in order, then “call” the function! Suppose we define the following function: int sum(int a, int b) { return a + b; } (See also sum.c from the provided code) 2/23/2014 3 x86 calling conventions int sum(int a, int b) { return a + b; } In assembly, we have something like this: sum: pushl %ebp # Save base pointer movl %esp, %ebp # Save stack pointer movl 12(%ebp), %eax # Load b movl 8(%ebp), %edx # Load a addl %edx, %eax # Compute a + b popl %ebp # Restore base pointer ret # Return 2/23/2014 4 x86 calling conventions What is happening with %ebp and %esp? pushl %ebp The base pointer %ebp is the address of the caller, which is the location to which “ret” returns. The function pushes it into the stack so that it won’t be overwritten movl %esp, %ebp Functions often shift the stack pointer to allocate temporary stack space, so this instruction makes a backup of the original location. In the body of the function, %ebp is now the original start of the stack ret When sum() returns, execution picks up at the stored base pointer address. -

X86 Disassembly Exploring the Relationship Between C, X86 Assembly, and Machine Code
x86 Disassembly Exploring the relationship between C, x86 Assembly, and Machine Code PDF generated using the open source mwlib toolkit. See http://code.pediapress.com/ for more information. PDF generated at: Sat, 07 Sep 2013 05:04:59 UTC Contents Articles Wikibooks:Collections Preface 1 X86 Disassembly/Cover 3 X86 Disassembly/Introduction 3 Tools 5 X86 Disassembly/Assemblers and Compilers 5 X86 Disassembly/Disassemblers and Decompilers 10 X86 Disassembly/Disassembly Examples 18 X86 Disassembly/Analysis Tools 19 Platforms 28 X86 Disassembly/Microsoft Windows 28 X86 Disassembly/Windows Executable Files 33 X86 Disassembly/Linux 48 X86 Disassembly/Linux Executable Files 50 Code Patterns 51 X86 Disassembly/The Stack 51 X86 Disassembly/Functions and Stack Frames 53 X86 Disassembly/Functions and Stack Frame Examples 57 X86 Disassembly/Calling Conventions 58 X86 Disassembly/Calling Convention Examples 64 X86 Disassembly/Branches 74 X86 Disassembly/Branch Examples 83 X86 Disassembly/Loops 87 X86 Disassembly/Loop Examples 92 Data Patterns 95 X86 Disassembly/Variables 95 X86 Disassembly/Variable Examples 101 X86 Disassembly/Data Structures 103 X86 Disassembly/Objects and Classes 108 X86 Disassembly/Floating Point Numbers 112 X86 Disassembly/Floating Point Examples 119 Difficulties 121 X86 Disassembly/Code Optimization 121 X86 Disassembly/Optimization Examples 124 X86 Disassembly/Code Obfuscation 132 X86 Disassembly/Debugger Detectors 137 Resources and Licensing 139 X86 Disassembly/Resources 139 X86 Disassembly/Licensing 141 X86 Disassembly/Manual of Style 141 References Article Sources and Contributors 142 Image Sources, Licenses and Contributors 143 Article Licenses License 144 Wikibooks:Collections Preface 1 Wikibooks:Collections Preface This book was created by volunteers at Wikibooks (http:/ / en. -
Sample Applications User Guides Release 20.05.0
Sample Applications User Guides Release 20.05.0 May 26, 2020 CONTENTS 1 Introduction to the DPDK Sample Applications1 1.1 Running Sample Applications...............................1 1.2 The DPDK Sample Applications..............................1 2 Compiling the Sample Applications3 2.1 To compile all the sample applications...........................3 2.2 To compile a single application..............................3 2.3 To cross compile the sample application(s)........................4 3 Command Line Sample Application5 3.1 Overview..........................................5 3.2 Compiling the Application.................................5 3.3 Running the Application..................................6 3.4 Explanation.........................................6 4 Ethtool Sample Application8 4.1 Compiling the Application.................................8 4.2 Running the Application..................................8 4.3 Using the application....................................8 4.4 Explanation.........................................9 4.5 Ethtool interface......................................9 5 Hello World Sample Application 11 5.1 Compiling the Application................................. 11 5.2 Running the Application.................................. 11 5.3 Explanation......................................... 11 6 Basic Forwarding Sample Application 13 6.1 Compiling the Application................................. 13 6.2 Running the Application.................................. 13 6.3 Explanation........................................ -
Cubesuite+ V1.00.00 Integrated Development Environment User's Manual: V850 Build
User’s Manual User’s CubeSuite+ V1.00.00 Integrated Development Environment User’s Manual: V850 Build Target Device V850 Microcontroller All information contained in these materials, including products and product specifications, represents information on the product at the time of publication and is subject to change by Renesas Electronics Corp. without notice. Please review the latest information published by Renesas Electronics Corp. through various means, including the Renesas Electronics Corp. website (http://www.renesas.com). www.renesas.com Rev.1.00 Apr 2011 Notice 1. All information included in this document is current as of the date this document is issued. Such information, however, is subject to change without any prior notice. Before purchasing or using any Renesas Electronics products listed herein, please confirm the latest product information with a Renesas Electronics sales office. Also, please pay regular and careful attention to additional and different information to be disclosed by Renesas Electronics such as that disclosed through our website. 2. Renesas Electronics does not assume any liability for infringement of patents, copyrights, or other intellectual property rights of third parties by or arising from the use of Renesas Electronics products or technical information described in this document. No license, express, implied or otherwise, is granted hereby under any patents, copyrights or other intellectual property rights of Renesas Electronics or others. 3. You should not alter, modify, copy, or otherwise misappropriate any Renesas Electronics product, whether in whole or in part. 4. Descriptions of circuits, software and other related information in this document are provided only to illustrate the operation of semiconductor products and application examples. -

X86 Assembly Language Reference Manual
x86 Assembly Language Reference Manual Part No: 817–5477–11 March 2010 Copyright ©2010 Oracle and/or its affiliates. All rights reserved. This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without notice and is not warranted to be error-free. If you find any errors, please report them to us in writing. If this is software or related software documentation that is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, the following notice is applicable: U.S. GOVERNMENT RIGHTS Programs, software, databases, and related documentation and technical data delivered to U.S. Government customers are “commercial computer software” or “commercial technical data” pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, the use, duplication, disclosure, modification, and adaptation shall be subject to the restrictions and license terms setforth in the applicable Government contract, and, to the extent applicable by the terms of the Government contract, the additional rights set forth in FAR 52.227-19, Commercial Computer Software License (December 2007). Oracle USA, Inc., 500 Oracle Parkway, Redwood City, CA 94065.