Katalog Elektronskih Knjiga
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Open Source Ethos Guiding Beliefs Or Ideals That Characterize a Community
Open Source Ethos guiding beliefs or ideals that characterize a community Patrick Masson Open Source Initiative [email protected] What is the mission of the conference? …bring smart and creative people together; …inspire and motivate them to create new and amazing things; …with an intimate group of like minded individuals. What is the mission of the conference? …bring smart and creative people together; …inspire and motivate them to create new and amazing things; …with an intimate group of like minded individuals. This is the open source ethos – guiding beliefs, ideals of a community It's a great time to be working with open source 1.5 Million Projects 78% of companies run on open source 64% of companies participate It's a great time to be working with open source 88% expect contributions to grow 66% consider before proprietary <3% Don't use OSS 2015 Future of Open Source Survey Black Duck, Northbridge It's a great time to be working with open source It's a great time to be working with open source It's a great time to be working with open source It's a great time to be working with open source Open-course/Open-source Marc Wathieu CC-BY-NC-SA https://www.flickr.com/photos/marcwathieu/2412755417/ _____ College first Massive Open source Online Course (MOOC) Are you seeing other examples of this Mini-MOOC trend (free, I began but did not finish my first The Gates grantees aren’t the only ones open source courses by a MOOC (Massive Open-Source, startup or organization)? Online Course). -

Mac OS X Server Administrator's Guide
034-9285.S4AdminPDF 6/27/02 2:07 PM Page 1 Mac OS X Server Administrator’s Guide K Apple Computer, Inc. © 2002 Apple Computer, Inc. All rights reserved. Under the copyright laws, this publication may not be copied, in whole or in part, without the written consent of Apple. The Apple logo is a trademark of Apple Computer, Inc., registered in the U.S. and other countries. Use of the “keyboard” Apple logo (Option-Shift-K) for commercial purposes without the prior written consent of Apple may constitute trademark infringement and unfair competition in violation of federal and state laws. Apple, the Apple logo, AppleScript, AppleShare, AppleTalk, ColorSync, FireWire, Keychain, Mac, Macintosh, Power Macintosh, QuickTime, Sherlock, and WebObjects are trademarks of Apple Computer, Inc., registered in the U.S. and other countries. AirPort, Extensions Manager, Finder, iMac, and Power Mac are trademarks of Apple Computer, Inc. Adobe and PostScript are trademarks of Adobe Systems Incorporated. Java and all Java-based trademarks and logos are trademarks or registered trademarks of Sun Microsystems, Inc. in the U.S. and other countries. Netscape Navigator is a trademark of Netscape Communications Corporation. RealAudio is a trademark of Progressive Networks, Inc. © 1995–2001 The Apache Group. All rights reserved. UNIX is a registered trademark in the United States and other countries, licensed exclusively through X/Open Company, Ltd. 062-9285/7-26-02 LL9285.Book Page 3 Tuesday, June 25, 2002 3:59 PM Contents Preface How to Use This Guide 39 What’s Included -

Bibliography of Erik Wilde
dretbiblio dretbiblio Erik Wilde's Bibliography References [1] AFIPS Fall Joint Computer Conference, San Francisco, California, December 1968. [2] Seventeenth IEEE Conference on Computer Communication Networks, Washington, D.C., 1978. [3] ACM SIGACT-SIGMOD Symposium on Principles of Database Systems, Los Angeles, Cal- ifornia, March 1982. ACM Press. [4] First Conference on Computer-Supported Cooperative Work, 1986. [5] 1987 ACM Conference on Hypertext, Chapel Hill, North Carolina, November 1987. ACM Press. [6] 18th IEEE International Symposium on Fault-Tolerant Computing, Tokyo, Japan, 1988. IEEE Computer Society Press. [7] Conference on Computer-Supported Cooperative Work, Portland, Oregon, 1988. ACM Press. [8] Conference on Office Information Systems, Palo Alto, California, March 1988. [9] 1989 ACM Conference on Hypertext, Pittsburgh, Pennsylvania, November 1989. ACM Press. [10] UNIX | The Legend Evolves. Summer 1990 UKUUG Conference, Buntingford, UK, 1990. UKUUG. [11] Fourth ACM Symposium on User Interface Software and Technology, Hilton Head, South Carolina, November 1991. [12] GLOBECOM'91 Conference, Phoenix, Arizona, 1991. IEEE Computer Society Press. [13] IEEE INFOCOM '91 Conference on Computer Communications, Bal Harbour, Florida, 1991. IEEE Computer Society Press. [14] IEEE International Conference on Communications, Denver, Colorado, June 1991. [15] International Workshop on CSCW, Berlin, Germany, April 1991. [16] Third ACM Conference on Hypertext, San Antonio, Texas, December 1991. ACM Press. [17] 11th Symposium on Reliable Distributed Systems, Houston, Texas, 1992. IEEE Computer Society Press. [18] 3rd Joint European Networking Conference, Innsbruck, Austria, May 1992. [19] Fourth ACM Conference on Hypertext, Milano, Italy, November 1992. ACM Press. [20] GLOBECOM'92 Conference, Orlando, Florida, December 1992. IEEE Computer Society Press. http://github.com/dret/biblio (August 29, 2018) 1 dretbiblio [21] IEEE INFOCOM '92 Conference on Computer Communications, Florence, Italy, 1992. -

Producing Open Source Software How to Run a Successful Free Software Project
Producing Open Source Software How to Run a Successful Free Software Project Karl Fogel Producing Open Source Software: How to Run a Successful Free Software Project by Karl Fogel Copyright © 2005-2018 Karl Fogel, under the CreativeCommons Attribution-ShareAlike (4.0) license. Version: 2.3098 Home site: http://producingoss.com/ Dedication This book is dedicated to two dear friends without whom it would not have been possible: Karen Under- hill and Jim Blandy. i Table of Contents Preface ............................................................................................................................. vi Why Write This Book? ............................................................................................... vi Who Should Read This Book? .................................................................................... vii Sources ................................................................................................................... vii Acknowledgements ................................................................................................... viii For the first edition (2005) ................................................................................ viii For the second edition (2017) ............................................................................... x Disclaimer .............................................................................................................. xiii 1. Introduction ................................................................................................................... -
Printed Program
rd International Conference 43 on Software Engineering goes Virtual PROGRAM May 25th –28th 2021 Co-located events: May 17th –May 24th Workshops: May 24th , May 29th –June 4th https://conf.researchr.org/home/icse-2021 @ICSEconf Table of Contents Conference overviews ............................................................... 3 Sponsors and Supporters ......................................................... 11 Welcome letter ........................................................................ 13 Keynotes ................................................................................. 18 Technical Briefings ................................................................. 28 Co-located events .................................................................... 35 Workshops .............................................................................. 36 New Faculty Symposium ........................................................ 37 Doctoral Symposium .............................................................. 39 Detailed Program - Tuesday, May 25th .................................................... 42 - Wednesday, May 26th ............................................... 53 - Thursday, May 27th .................................................. 66 - Friday, May 28th ....................................................... 80 Awards .................................................................................... 91 Social and Networking events ................................................. 94 Organizing Committee ........................................................ -

Capsicum: Practical Capabilities for UNIX
Capsicum: practical capabilities for UNIX Robert N. M. Watson Jonathan Anderson Ben Laurie University of Cambridge University of Cambridge Google UK Ltd. Kris Kennaway Google UK Ltd. Abstract significant technical limitations: current OS facilities are simply not designed for this purpose. Capsicum is a lightweight operating system capabil- The access control systems in conventional (non- ity and sandbox framework planned for inclusion in capability-oriented) operating systems are Discretionary FreeBSD 9. Capsicum extends, rather than replaces, Access Control (DAC) and Mandatory Access Control UNIX APIs, providing new kernel primitives (sandboxed (MAC). DAC was designed to protect users from each capability mode and capabilities) and a userspace sand- other: the owner of an object (such as a file) can specify box API. These tools support compartmentalisation of permissions for it, which are checked by the OS when monolithic UNIX applications into logical applications, the object is accessed. MAC was designed to enforce an increasingly common goal supported poorly by dis- system policies: system administrators specify policies cretionary and mandatory access control. We demon- (e.g. “users cleared to Secret may not read Top Secret strate our approach by adapting core FreeBSD utilities documents”), which are checked via run-time hooks in- and Google’s Chromium web browser to use Capsicum serted into many places in the operating system’s kernel. primitives, and compare the complexity and robustness Neither of these systems was designed to address the of Capsicum with other sandboxing techniques. case of a single application processing many types of in- formation on behalf of one user. For instance, a mod- 1 Introduction ern web browser must parse HTML, scripting languages, images and video from many untrusted sources, but be- Capsicum is an API that brings capabilities to UNIX. -

Sandboxing with Capsicum
SECURITY Sandboxing with Capsicum PAWEL JAKUB DAWIDEK AND MARIUSZ ZABORSKI Pawel Jakub Dawidek is a ery few programmers have managed to successfully use the principle co-founder and CTO at Wheel of least privilege, as found in OpenSSH, Postfix, and djbdns. Capsi- Systems and a FreeBSD cum, introduced in 2010, adds a capability model designed to make it committer who lives and works V easier for programmers to reason about how to split a program into privileged in Warsaw, Poland. He is the and unprivileged portions. In this article, we describe the changes made in author of various GEOM classes, including the disk-encryption class GELI; he implemented Capsicum since 2010, compare Capsicum to earlier sandboxing techniques, the Highly Available Storage (HAST) daemon and look at the new Casperd, which makes it simpler to split programs. for distributing audit trail files (auditdistd), and Long ago, people started to recognize that security models proposed by the mainstream nowadays is mostly working on the Capsicum operating systems, including Windows, Mac OS X, and all kinds of UNIX-like systems, are framework and the Casper daemon. simply naive: All you need to do is to write programs that have no bugs. That’s indeed naive. [email protected] Let’s also state an obvious rule: The more code we write, the more bugs we introduce, some of which may jeopardize the security of our system. Once we accept this fact, where do we go? Mariusz Zaborski is currently We could only develop very small programs, which are easy to audit, but this again would be working as a software a bit naive. -
Linux Lunacy V & Perl Whirl
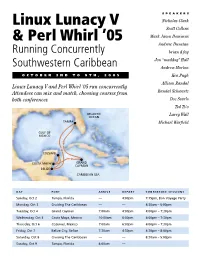
SPEAKERS Linux Lunacy V Nicholas Clark Scott Collins & Perl Whirl ’05 Mark Jason Dominus Andrew Dunstan Running Concurrently brian d foy Jon “maddog” Hall Southwestern Caribbean Andrew Morton OCTOBER 2ND TO 9TH, 2005 Ken Pugh Allison Randal Linux Lunacy V and Perl Whirl ’05 run concurrently. Attendees can mix and match, choosing courses from Randal Schwartz both conferences. Doc Searls Ted Ts’o Larry Wall Michael Warfield DAY PORT ARRIVE DEPART CONFERENCE SESSIONS Sunday, Oct 2 Tampa, Florida — 4:00pm 7:15pm, Bon Voyage Party Monday, Oct 3 Cruising The Caribbean — — 8:30am – 5:00pm Tuesday, Oct 4 Grand Cayman 7:00am 4:00pm 4:00pm – 7:30pm Wednesday, Oct 5 Costa Maya, Mexico 10:00am 6:00pm 6:00pm – 7:30pm Thursday, Oct 6 Cozumel, Mexico 7:00am 6:00pm 6:00pm – 7:30pm Friday, Oct 7 Belize City, Belize 7:30am 4:30pm 4:30pm – 8:00pm Saturday, Oct 8 Cruising The Caribbean — — 8:30am – 5:00pm Sunday, Oct 9 Tampa, Florida 8:00am — Perl Whirl ’05 and Linux Lunacy V Perl Whirl ’05 are running concurrently. Attendees can mix and match, choosing courses Seminars at a Glance from both conferences. You may choose any combination Regular Expression Mastery (half day) Programming with Iterators and Generators of full-, half-, or quarter-day seminars Speaker: Mark Jason Dominus Speaker: Mark Jason Dominus (half day) for a total of two-and-one-half Almost everyone has written a regex that failed Sometimes you’ll write a function that takes too (2.5) days’ worth of sessions. The to match something they wanted it to, or that long to run because it produces too much useful conference fee is $995 and includes matched something they thought it shouldn’t, and information. -

When Geeks Cruise
COMMUNITY Geek Cruise: Linux Lunacy Linux Lunacy, Perl Whirl, MySQL Swell: Open Source technologists on board When Geeks Cruise If you are on one of those huge cruising ships and, instead of middle-aged ladies sipping cocktails, you spot a bunch of T-shirt touting, nerdy looking guys hacking on their notebooks in the lounges, chances are you are witnessing a “Geek Cruise”. BY ULRICH WOLF eil Baumann, of Palo Alto, Cali- and practical tips on application develop- The dedicated Linux track comprised a fornia, has been organizing geek ment – not only for Perl developers but meager spattering of six lectures, and Ncruises since 1999 (http://www. for anyone interested in programming. though there was something to suit geekcruises.com/), Neil always finds everyone’s taste, the whole thing tended enough open source and programming Perl: Present and to lack detail. Ted T’so spent a long time celebrities to hold sessions on Linux, (Distant?) Future talking about the Ext2 and Ext3 file sys- Perl, PHP and other topics dear to geeks. In contrast, Allison Randal’s tutorials on tems, criticizing ReiserFS along the way, Parrot Assembler and Perl6 features were but had very little to say about network Open Source Celebs hardcore. Thank goodness Larry Wall file systems, an increasingly vital topic. on the Med summed up all the major details on Perl6 Developers were treated to a lecture on I was lucky enough to get on board the in a brilliant lecture that was rich with developing shared libraries, and admins first Geek Cruise on the Mediterranean, metaphors and bursting with informa- enjoyed sessions on Samba and hetero- scaring the nerds to death with my tion. -

A Dataset of Open-Source Safety-Critical Software⋆
A Dataset of Open-Source Safety-Critical Software? Rafaila Galanopoulou[0000−0002−5318−9017] and Diomidis Spinellis[0000−0003−4231−1897] Department of Management Science and Technology Athens University of Economics and Business Patission 76, Athens, 10434, Greece ft8160018,[email protected] https://www.aueb.gr Abstract. We describe the method used to create a dataset of open- source safety-critical software, such as that used for autonomous cars, healthcare, and autonomous aviation, through a systematic and rigorous selection process. The dataset can be used for empirical studies regard- ing the quality assessment of safety-critical software, its dependencies, and its development process, as well as comparative studies considering software from other domains. Keywords: open-source · safety-critical · dataset 1 Introduction Safety-critical systems (SCS) are those whose failure could result in loss of life, significant property damage, or damage to the environment [5]. Over the past decades ever more software is developed and released as open-source software (OSS) | with licenses that allow its free use, study, change, and distribution [1]. The increasing adoption of open-source software in safety-critical systems [10], such as those used in the medical, aerospace, and automotive industries, poses an interesting challenge. On the one hand, it shortens time to delivery and lowers development costs [6]. On the other hand, it introduces questions regarding the system's quality. For a piece of software to be part of a safety-critical application it requires quality assurance, because quality is a crucial factor of an SCS's software [3]. This assurance demands that evidence regarding OSS quality is supplied, and an analysis is needed to assess if the certification cost is worthwhile. -

Curriculum Vitae
CURRICULUM VITAE Diomidis Spinellis Professor of Software Engineering Department of Management Science and Technology Athens University of Economics and Business September 17, 2021 CV — Diomidis Spinellis CONTENTS Contents 1 Personal and Contact Details 5 2 Education 5 3 Research Interests 5 4 Honours and Awards 5 5 Teaching Experience 7 6 Scientific, Professional, and Technical Activities 7 6.1 Memberships of Professional and Learned Societies .................... 7 6.2 Journal and Magazine Editorial Board Member ...................... 7 6.3 Service in Conference Committees ............................. 7 6.4 Other Professional Society Service ............................. 11 6.5 Selected Open Source Software Development ....................... 12 7 Publications 12 7.1 Books: Monographs and Edited Volumes .......................... 12 7.2 Theses ............................................ 13 7.3 Peer‐reviewed Journal Articles ............................... 13 7.4 Editor‐in‐Chief and Guest Editor Introductions ....................... 17 7.5 Magazine Columns ..................................... 18 7.6 Book Chapters ........................................ 20 7.7 Conference Publications .................................. 20 7.8 Letters Published in Scholarly Journals and Newspapers .................. 29 7.9 Technical Reports and Working Papers ........................... 29 7.10 Book Reviews ........................................ 30 7.11 Articles in the Technical Press and SIG Publications .................... 32 7.12 Invited Talks -

Design Principles and Patterns for Computer Systems That Are
Bibliography [AB04] Tom Anderson and David Brady. Principle of least astonishment. Ore- gon Pattern Repository, November 15 2004. http://c2.com/cgi/wiki? PrincipleOfLeastAstonishment. [Acc05] Access Data. Forensic toolkit—overview, 2005. http://www.accessdata. com/Product04_Overview.htm?ProductNum=04. [Adv87] Display ad 57, February 8 1987. [Age05] US Environmental Protection Agency. Wastes: The hazardous waste mani- fest system, 2005. http://www.epa.gov/epaoswer/hazwaste/gener/ manifest/. [AHR05a] Ben Adida, Susan Hohenberger, and Ronald L. Rivest. Fighting Phishing Attacks: A Lightweight Trust Architecture for Detecting Spoofed Emails (to appear), 2005. Available at http://theory.lcs.mit.edu/⇠rivest/ publications.html. [AHR05b] Ben Adida, Susan Hohenberger, and Ronald L. Rivest. Separable Identity- Based Ring Signatures: Theoretical Foundations For Fighting Phishing Attacks (to appear), 2005. Available at http://theory.lcs.mit.edu/⇠rivest/ publications.html. [AIS77] Christopher Alexander, Sara Ishikawa, and Murray Silverstein. A Pattern Lan- guage: towns, buildings, construction. Oxford University Press, 1977. (with Max Jacobson, Ingrid Fiksdahl-King and Shlomo Angel). [AKM+93] H. Alvestrand, S. Kille, R. Miles, M. Rose, and S. Thompson. RFC 1495: Map- ping between X.400 and RFC-822 message bodies, August 1993. Obsoleted by RFC2156 [Kil98]. Obsoletes RFC987, RFC1026, RFC1138, RFC1148, RFC1327 [Kil86, Kil87, Kil89, Kil90, HK92]. Status: PROPOSED STANDARD. [Ale79] Christopher Alexander. The Timeless Way of Building. Oxford University Press, 1979. 429 430 BIBLIOGRAPHY [Ale96] Christopher Alexander. Patterns in architecture [videorecording], October 8 1996. Recorded at OOPSLA 1996, San Jose, California. [Alt00] Steven Alter. Same words, different meanings: are basic IS/IT concepts our self-imposed Tower of Babel? Commun. AIS, 3(3es):2, 2000.