How to Evade Application Whitelisting Using REGSVR32
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Attacker Antics Illustrations of Ingenuity
ATTACKER ANTICS ILLUSTRATIONS OF INGENUITY Bart Inglot and Vincent Wong FIRST CONFERENCE 2018 2 Bart Inglot ◆ Principal Consultant at Mandiant ◆ Incident Responder ◆ Rock Climber ◆ Globetrotter ▶ From Poland but live in Singapore ▶ Spent 1 year in Brazil and 8 years in the UK ▶ Learning French… poor effort! ◆ Twitter: @bartinglot ©2018 FireEye | Private & Confidential 3 Vincent Wong ◆ Principal Consultant at Mandiant ◆ Incident Responder ◆ Baby Sitter ◆ 3 years in Singapore ◆ Grew up in Australia ©2018 FireEye | Private & Confidential 4 Disclosure Statement “ Case studies and examples are drawn from our experiences and activities working for a variety of customers, and do not represent our work for any one customer or set of customers. In many cases, facts have been changed to obscure the identity of our customers and individuals associated with our customers. ” ©2018 FireEye | Private & Confidential 5 Today’s Tales 1. AV Server Gone Bad 2. Stealing Secrets From An Air-Gapped Network 3. A Backdoor That Uses DNS for C2 4. Hidden Comment That Can Haunt You 5. A Little Known Persistence Technique 6. Securing Corporate Email is Tricky 7. Hiding in Plain Sight 8. Rewriting Import Table 9. Dastardly Diabolical Evil (aka DDE) ©2018 FireEye | Private & Confidential 6 AV SERVER GONE BAD Cobalt Strike, PowerShell & McAfee ePO (1/9) 7 AV Server Gone Bad – Background ◆ Attackers used Cobalt Strike (along with other malware) ◆ Easily recognisable IOCs when recorded by Windows Event Logs ▶ Random service name – also seen with Metasploit ▶ Base64-encoded script, “%COMSPEC%” and “powershell.exe” ▶ Decoding the script yields additional PowerShell script with a base64-encoded GZIP stream that in turn contained a base64-encoded Cobalt Strike “Beacon” payload. -
Powershell Integration with Vmware View 5.0
PowerShell Integration with VMware® View™ 5.0 TECHNICAL WHITE PAPER PowerShell Integration with VMware View 5.0 Table of Contents Introduction . 3 VMware View. 3 Windows PowerShell . 3 Architecture . 4 Cmdlet dll. 4 Communication with Broker . 4 VMware View PowerCLI Integration . 5 VMware View PowerCLI Prerequisites . 5 Using VMware View PowerCLI . 5 VMware View PowerCLI cmdlets . 6 vSphere PowerCLI Integration . 7 Examples of VMware View PowerCLI and VMware vSphere PowerCLI Integration . 7 Passing VMs from Get-VM to VMware View PowerCLI cmdlets . 7 Registering a vCenter Server . .. 7 Using Other VMware vSphere Objects . 7 Advanced Usage . 7 Integrating VMware View PowerCLI into Your Own Scripts . 8 Scheduling PowerShell Scripts . 8 Workflow with VMware View PowerCLI and VMware vSphere PowerCLI . 9 Sample Scripts . 10 Add or Remove Datastores in Automatic Pools . 10 Add or Remove Virtual Machines . 11 Inventory Path Manipulation . 15 Poll Pool Usage . 16 Basic Troubleshooting . 18 About the Authors . 18 TECHNICAL WHITE PAPER / 2 PowerShell Integration with VMware View 5.0 Introduction VMware View VMware® View™ is a best-in-class enterprise desktop virtualization platform. VMware View separates the personal desktop environment from the physical system by moving desktops to a datacenter, where users can access them using a client-server computing model. VMware View delivers a rich set of features required for any enterprise deployment by providing a robust platform for hosting virtual desktops from VMware vSphere™. Windows PowerShell Windows PowerShell is Microsoft’s command line shell and scripting language. PowerShell is built on the Microsoft .NET Framework and helps in system administration. By providing full access to COM (Component Object Model) and WMI (Windows Management Instrumentation), PowerShell enables administrators to perform administrative tasks on both local and remote Windows systems. -

Run-Commands-Windows-10.Pdf
Run Commands Windows 10 by Bettertechtips.com Command Action Command Action documents Open Documents Folder devicepairingwizard Device Pairing Wizard videos Open Videos Folder msdt Diagnostics Troubleshooting Wizard downloads Open Downloads Folder tabcal Digitizer Calibration Tool favorites Open Favorites Folder dxdiag DirectX Diagnostic Tool recent Open Recent Folder cleanmgr Disk Cleanup pictures Open Pictures Folder dfrgui Optimie Drive devicepairingwizard Add a new Device diskmgmt.msc Disk Management winver About Windows dialog dpiscaling Display Setting hdwwiz Add Hardware Wizard dccw Display Color Calibration netplwiz User Accounts verifier Driver Verifier Manager azman.msc Authorization Manager utilman Ease of Access Center sdclt Backup and Restore rekeywiz Encryption File System Wizard fsquirt fsquirt eventvwr.msc Event Viewer calc Calculator fxscover Fax Cover Page Editor certmgr.msc Certificates sigverif File Signature Verification systempropertiesperformance Performance Options joy.cpl Game Controllers printui Printer User Interface iexpress IExpress Wizard charmap Character Map iexplore Internet Explorer cttune ClearType text Tuner inetcpl.cpl Internet Properties colorcpl Color Management iscsicpl iSCSI Initiator Configuration Tool cmd Command Prompt lpksetup Language Pack Installer comexp.msc Component Services gpedit.msc Local Group Policy Editor compmgmt.msc Computer Management secpol.msc Local Security Policy: displayswitch Connect to a Projector lusrmgr.msc Local Users and Groups control Control Panel magnify Magnifier -
View the Slides (Smith)
Network Shells Michael Smith Image: https://commons.wikimedia.org/wiki/File:Network-connections.png What does a Shell give us? ● A REPL ● Repeatability ● Direct access to system operations ● User-focused design ● Hierarchical context & sense of place Image: https://upload.wikimedia.org/wikipedia/commons/8/84/Bash_demo.png What does a Shell give us? ● A REPL ● Repeatability ● Direct access to system operations ● User-focused design ● Hierarchical context & sense of place Image: https://upload.wikimedia.org/wikipedia/commons/8/84/Bash_demo.png Management at a distance (netsh) Netsh: Configure DHCP servers with netsh -r RemoteMachine -u domain\username [RemoteMachine] netsh>interface [RemoteMachine] netsh interface>ipv6 [RemoteMachine] netsh interface ipv6>show interfaces Reference: https://docs.microsoft.com/en-us/windows-server/networking/technologies/netsh/netsh-contexts Management at a distance (netsh) Netsh: Configure DHCP servers with netsh Location-r RemoteMachine -u domain\username Hierarchical [RemoteMachine] netsh>interfacecontext Simpler [RemoteMachine] netsh interface>ipv6 commands [RemoteMachine] netsh interface ipv6>show interfaces Reference: https://docs.microsoft.com/en-us/windows-server/networking/technologies/netsh/netsh-contexts Management at a distance (WSMan) WSMan (in Powershell): Manage Windows remotely with Set-Location -Path WSMan:\SERVER01 Get-ChildItem -Path . Set-Item Client\TrustedHosts *.domain2.com -Concatenate Reference: https://docs.microsoft.com/en-us/powershell/module/microsoft.wsman.management/about/about_wsman_provider -

Invalid Class String Error
Tib4231 July, 2001 TECHNICAL INFORMATION BULLETIN Invalid Class String Error KODAK DC215, KODAK DC240, KODAK DC280, DC3400, and DC5000 Zoom Digital Cameras An Invalid Class String error may occur when you try to launch the camera software for the first time, or the Mounter or Camera Properties software may not operate properly.This error is caused when the program RegSvr32.exe is not located in the C:\Windows\System folder, preventing the DLL files from being registered. Use this document to help you properly locate the RegSvr32.exe program in your system, and if necessary, manually register the DLL files. The instructions in this document assume that you are familiar with copying and moving files in your computer, and installing software. Relocating RegSvr32.exe 1. Go to Start > Find > Files and Folders and search for regsvr32*.* Note the location of the program. 2. In WINDOWS Explorer or My Computer, copy RegSvr32.exe to the C:\Windows\System folder if it is not already there. When the file is in place, go on to Step 3. 3. Uninstall the KODAK software using the KODAK Uninstall application, or go to Start > Settings > Control Panel > Add / Remove Programs. 4. Close all background programs except Explorer and Systray by pressing Ctrl Alt Del, selecting each program one at a time, and clicking End Task after each. 5. Install the KODAK camera software. 6. Start the KODAK Camera Mounter and Camera Properties software for your camera. If the Invalid Class String error appears, manually register the DLL file using the procedure that follows for your camera. -

Copyrighted Material
Index Numerics Address Resolution Protocol (ARP), 1052–1053 admin password, SOHO network, 16-bit Windows applications, 771–776, 985, 1011–1012 900, 902 Administrative Tools window, 1081–1083, 32-bit (x86) architecture, 124, 562, 769 1175–1176 64-bit (x64) architecture, 124, 562, 770–771 administrative tools, Windows, 610 administrator account, 1169–1170 A Administrators group, 1171 ADSL (Asynchronous Digital Subscriber Absolute Software LoJack feature, 206 Line), 1120 AC (alternating current), 40 Advanced Attributes window, NTFS AC adapters, 311–312, 461, 468–469 partitions, 692 Accelerated Graphics Port (AGP), 58 Advanced Computing Environment (ACE) accelerated video cards (graphics initiative, 724 accelerator cards), 388 Advanced Confi guration and Power access points, wireless, 996, 1121 Interface (ACPI) standard, 465 access time, hard drive, 226 Advanced Graphics Port (AGP) card, access tokens, 1146–1147 391–392 Account Operators group, 1172 Advanced Graphics Port (AGP) port, 105 ACE (Advanced Computing Environment) Advanced Host Controller Interface (AHCI), initiative, 724 212–213 ACPI (Advanced Confi guration and Power Advanced Micro Devices (AMD), 141–144 Interface) standard, 465 Advanced Packaging Tool (APT), 572 Action Center, 1191–1192 Advanced Power Management (APM) Active Directory Database, 1145–1146, 1183 standard, 465 active heat sink, 150 Advanced Programmable Interrupt active matrix display, LCD (thin-fi lm Controller (APIC), 374 transistor (TFT) display), 470 Advanced RISC Computing Specifi cation active partition, 267, -

Revoke Obfuscation Report
Revoke-Obfuscation: PowerShell Obfuscation Detection Using Science Daniel Bohannon @danielhbohannon | Lee Holmes @Lee_Holmes Revoke-Obfuscation is the result of industry research collaboration between Daniel Bohannon - Senior Applied Security Researcher at Mandiant/FireEye, and Lee Holmes – Lead Security Architect of Azure ManaGement at Microsoft. Background By far the most prevalent delivery and execution vehicle for malware in the industry today is basic malicious executables and malicious documents. While not represented accurately by its popularity in the news, a small portion of the current malware ecosystem leverages PowerShell as part of its attack chain. Of malware that uses PowerShell, the most prevalent use is the garden-variety stager: an executable or document macro that launches PowerShell to download another executable and run it. Despite its relative statistical rarity, development of malicious and offense-focused PowerShell techniques has been a rich field of innovation. Commercial products have started to react to these techniques in several ways. Because they are often delivered as script files, Antivirus vendors have long had the ability to write signatures that block malicious PowerShell scripts. With the release of Windows 10, some vendors have additionally begun to implement support for Windows’ Antimalware Scan Interface. This interface gives Antivirus vendors the ability to implement deep content scanning, providing visibility as each stage of malware fetches and dynamically executes new instructions from a remote network location. In addition to antivirus signatures, many SIEM vendors have started to implement alerting based on command-line parameters that are frequently used in malicious contexts. Palo Alto provides an excellent survey of commonly-used malicious PowerShell command-line arguments in their post, Pulling Back the Curtains on EncodedCommand PowerShell Attacks. -
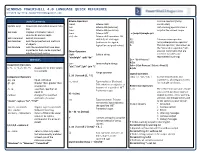
WINDOWS POWERSHELL 4.0 LANGUAGE QUICK REFERENCE Created By
WINDOWS POWERSHELL 4.0 LANGUAGE QUICK REFERENCE Created by http://powershellmagazine.com Useful Commands Bitwise Operators , Comma operator (Array -band Bitwise AND constructor) Update-Help Downloads and installs newest help -bor Bitwise OR (inclusive) . Dot-sourcing operator runs a files -bxor Bitwise OR (exclusive) script in the current scope Get-Help Displays information about -bnot Bitwise NOT . c:\scripts\sample.ps1 commands and concepts -shl, -shr Bitwise shift operators. Bit Get-Command Gets all commands shift left, bit shift right $( ) Subexpression operator Get-Member Gets the properties and methods (arithmetic for signed, @( ) Array subexpression operator of objects logical for unsigned values) & The call operator, also known as Get-Module Gets the modules that have been the "invocation operator," lets imported or that can be imported Other Operators you run commands that are into the current session -Split Splits a string stored in variables and “abcdefghi” -split “de” represented by strings. Operators $a = "Get-Process" -join Joins multiple strings & $a Assignment Operators “abc”,”def”,”ghi” -join “;” $sb = { Get-Process | Select –First 2 } =, +=, -=, *=, /=, %=, ++, -- Assigns one or more values & $sb to a variable .. Range operator Logical Operators 1..10 | foreach {$_ * 5} Comparison Operators -and, -or, -xor, -not, ! Connect expressions and -eq, -ne Equal, not equal statements, allowing you to test -is, -isnot Type evaluator (Boolean). -gt, -ge Greater than, greater than for multiple conditions Tells whether an object is an or equal to Redirection Operators instance of a specified .NET -lt, -le Less than, less than or >, >> The redirection operators enable Framework type. equal to you to send particular types of 42 –is [int] -replace changes the specified output (success, error, warning, elements of a value verbose, and debug) to files and -as Type convertor. -

Conversion Server User Guide
www.AutoDWG.com Thank you for using AutoDWG Conversion Server Software AutoDWG Conversion Server With AutoDWG Conversion Server, companies can convert dwg to pdf, dwg to image automatically at high speed in a centrally-managed server. Users upload or drop dwg files into a watched folder, the drawing will be convert into pdf, dwf or image automatcially at once, Users can set up different folders in different output policy to specify output file type, and others setting. Features • Windows Service Program, no AutoCAD required in the server. • Supports dwg to pdf, dwg to jpg, dwg to bmp, dwg to gif, dwg to bmp, dwg to png conversion. • Supports AutoCAD drawing format from R2.5 to the latest version R2008. Email us [email protected] for more information and pricing. Download Free Trial Quick Start: • Install the software, register the DLL files and the acs.exe service o RUN: Regsvr32 “Full path\DWG2PDFX.dll” o RUN: Regsvr32 “Full path\DWG2imageX.dll” o RUN: Regsvr32 “Full path\mfc42.dll” o Set up the PS path, copy the whole folder of “PS” to C:\windows\system32\PS o RUN: acs.exe /service o Start the service from the [Windows control panel\Administrative tools\Services] • Launch AcsCtrl.exe to set up profiles of the watched folders and output file formats o Click menu button “File/New Profile” to create new watched folder o Right click on the existing listed input folder, click “add a profile” to create more out put file formats or copy files without convert • Click on the button “Start Server” to start the conversion service Æ Go to Trouble Shooting and learn more on the installation www.AutoDWG.com User’s manual The AutoDWG Conversion server is enterprise class software, and recommended to installed with a server, the requirements to the server listed as below: Hard ware requirements, CPU: PIII 1GHz or greater, a modern processor is recommended, since the conversion calculation will be kind of heavy loading to the CPU. -

Cxspectra How to Fix Hasp Com Windows.Dll Is Missing / Not Found Error Messages
CXSpectra How To Fix Hasp_com_windows.dll is Missing / Not Found Error Messages Overview of Hasp_com_windows.dll What Is Hasp_com_windows.dll? Hasp_com_windows.dll is a type of DLL file associated with HASP SRM Assembly for Microsoft .NET developed by Windows Software Developer for the Windows Operating System. The latest known version of Hasp_com_windows.dll is 3.5, which was produced for Windows. This DLL file carries a popularity rating of 1 stars and a security rating of "UNKNOWN". What Are DLL Files? DLL ("dynamic link library") files such as hasp_com_windows.dll are small programs, similar to EXE ("executable") files, which allow multiple software programs to share the same functionality (eg. printing). For example, let's say you are running Windows and editing a document in Microsoft Word. The DLL file that controls printing does not need to load unless it's function is needed - eg. you decide to print your document. When you select "Print", Microsoft Word calls the printer DLL file, and it is loaded into memory (RAM) at that time. If you want to print a document in another program, Adobe Acrobat for example, that same printer DLL file will be used as well. Why Do I Have DLL Errors? Because they are shared files, DLL files exist outside of the software application itself. Although this provides many benefits for software developers, this separation also provides an opportunity for problems to occur. Quite simply, if Windows cannot properly load your hasp_com_windows.dll file, you will encounter an error message. Please see "Causes of hasp_com_windows.dll Errors" below for more information. -

Windows Powershell 1.0 Essentials
Windows PowerShell Essentials Windows PowerShell Essentials Windows PowerShell Essentials – Edition 1.0 © 2009 Payload Media. This eBook is provided for personal use only. Unauthorized use, reproduction and/or distribution strictly prohibited. All rights reserved. The content of this book is provided for informational purposes only. Neither the publisher nor the author offers any warranties or representation, express or implied, with regard to the accuracy of information contained in this book, nor do they accept any liability for any loss or damage arising from any errors or omissions. Find more eBooks at www.ebookfrenzy.com 2 © 2009 Payload Media Windows PowerShell Essentials Table of Contents Chapter 1. Installing Windows PowerShell ............................................................................... 10 1.1 Installing Windows PowerShell on Windows Server 2008 ............................................ 10 1.2 Performing a Windows Server 2008 PowerShell Command Line Installation ............... 10 1.3 Installing PowerShell on Windows Server 2003, XP and Vista Systems ........................ 11 Chapter 2. The Basics of the Windows PowerShell Interactive Shell ....................................... 13 2.1 The Windows PowerShell Command Prompt ................................................................ 13 2.2 PowerShell Command Line Editing Keys ........................................................................ 14 2.3 PowerShell Command Completion ............................................................................... -
Windows Powershell Best Practices Windows Powershell Best Practices
Windows PowerShell Best Practices Windows PowerShell Best Practices Expert recommendations, pragmatically applied Automate system administration using Windows PowerShell best practices—and optimize your operational efficiency. With this About the Author practical guide, Windows PowerShell expert and instructor Ed Ed Wilson, MCSE, CISSP, is a well-known Wilson delivers field-tested tips, real-world examples, and candid scripting expert and author of “Hey Windows Scripting Guy!”—one of the most popular advice culled from administrators across a range of business and blogs on Microsoft TechNet. He’s written technical scenarios. If you’re an IT professional with Windows several books on Windows scripting PowerShell experience, this book is ideal. for Microsoft Press, including Windows PowerShell 2.0 Best Practices and Windows PowerShell Scripting Guide. Discover how to: PowerShell • Use Windows PowerShell to automate Active Directory tasks • Explore available WMI classes and methods with CIM cmdlets • Identify and track scripting opportunities to avoid duplication • Use functions to encapsulate business logic and reuse code • Design your script’s best input method and output destination • Test scripts by checking their syntax and performance • Choose the most suitable method for running remote commands • Manage software services with Desired State Configuration Wilson BEST PRACTICES microsoft.com/mspress ISBN 978-0-7356-6649-8 U.S.A. $59.99 55999 Canada $68.99 [Recommended] 9 780735 666498 Operating Systems/Windows Server Celebrating 30 years! Ed Wilson 666498_Win_PowerShell_Best_Practices.indd 1 4/11/14 10:30 AM Windows PowerShell Best Practices Ed Wilson 666498_book.indb 1 12/20/13 10:50 AM Published with the authorization of Microsoft Corporation by: O’Reilly Media, Inc.