Introduction-To-Mainframes.Pdf
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Cloud Enabling CICS
Front cover Cloud Enabling IBM CICS Discover how to quickly cloud enable a traditional IBM 3270-COBOL-VSAM application Use CICS Explorer to develop and deploy a multi-versioned application Understand the benefits of threshold policy Rufus Credle Isabel Arnold Andrew Bates Michael Baylis Pradeep Gohil Christopher Hodgins Daniel Millwood Ian J Mitchell Catherine Moxey Geoffrey Pirie Inderpal Singh Stewart Smith Matthew Webster ibm.com/redbooks International Technical Support Organization Cloud Enabling IBM CICS December 2014 SG24-8114-00 Note: Before using this information and the product it supports, read the information in “Notices” on page vii. First Edition (December 2014) This edition applies to CICS Transaction Server for z/OS version 5.1, 3270-COBOL-VSAM application. © Copyright International Business Machines Corporation 2014. All rights reserved. Note to U.S. Government Users Restricted Rights -- Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents Notices . vii Trademarks . viii IBM Redbooks promotions . ix Preface . xi Authors. xii Now you can become a published author, too! . .xv Comments welcome. .xv Stay connected to IBM Redbooks . xvi Part 1. Introduction . 1 Chapter 1. Cloud enabling your CICS TS applications . 3 1.1 Did you know?. 4 1.2 Business value . 4 1.3 Solution overview . 5 1.4 Cloud computing in a CICS TS context. 6 1.5 Overview of the cloud-enabling technologies in CICS TS V5 . 11 1.5.1 Platform overview . 12 1.5.2 Application overview . 13 Chapter 2. GENAPP introduction. 15 2.1 CICS TS topology . 16 2.2 Application architecture. 17 2.2.1 GENAPP in a single managed region. -

1 ICT Fundamentals Lesson 1: Computing Fundamentals
ICT Fundamentals - Lesson 1: Computing Fundamentals 1-1 1 ICT Fundamentals Lesson 1: Computing Fundamentals LESSON SKILLS After completing this lesson, you will be able to: Define "computer" and explain how computers work. Describe functions of the computing cycle (i.e. input, processing, output, storage). Describe uses of computers (i.e. home, school, business). Identify the main types of computers (i.e. supercomputer, mainframe, microcomputer, notebook, tablet, handheld). Describe the four parts of a computer (i.e. hardware, software, data, user). List computer input and output devices (i.e. monitor, printer, projector, speakers, mice, keyboards) and describe their uses. Define "network," and explain network usage (i.e. home, school, work). Identify types of networks (i.e. LAN, WAN, MAN, VPN, intranet, extranet, the internet). KEY TERMS computer intranet server computer network mainframe computers software data microcomputers storage extranet notebook computers supercomputers handheld computers output tablet computer hardware processing user input SAMPLE © 2021 Certification Partners, LLC. — All Rights Reserved. Version 1.0 ICT Fundamentals - Lesson 1: Computing Fundamentals 1-2 Overview In this lesson, you will explain computing functions, systems and devices. You will also explain networking types and uses at home, school and work. What Is a Computer? Objectives 1.1.1: Define "computer" and explain how computers work. 1.1.2: Describe functions of the computing cycle (i.e. input, processing, output, storage). According to Dictionary.com (2016) a computer is, "a programmable electronic device designed to accept data, perform prescribed mathematical and logical operations at high speed and display the results of these operations. Mainframes, desktop and laptop computers, tablets, and smartphones are some of the different types of computers." As we can see from this definition, there are many different kinds of computers that are used in today’s world. -

Operating Systems
Operating Systems Interface between User & Computer Hardware Applications Programs Utilities Operating System Hardware Utilities Memory Resident File Access & Control Program Creation Memory Resident File Format Structures o Editors Access Management o Compilers Protection Schemes o Debuggers System Access & Control File Manipulation System-Wide Access o File Manipulation Resource Access o File Deletion Error Detection & Response Mechanism Program Execution Error Detection Link-Loaders Error Correction Run-Time Management Response to Unrecoverable Error I/O Device Access & Control Accounting Storage File Format Structures System Usage Collection Access Management System Performance Tuning Protection Schemes Forecasting Enhancement Requirements Billing Users for Usage Resource Manager O/S KernelKernel I/O Controller Printers, Keyboards, I/O Controller Monitors, Portions of Cameras, the O/S Etc. currently in use Computer Main System Memory Portions of Various I/O Application Devices Programs Currently in use Operating System Data Application Programs I/O Controller Storage Processor Processor Data Processor Processor Operation Allocation of Main Memory is made jointly by both the O/S and Memory Management Hardware O/S controls access to I/O devices by Application Programs O/S controls access to and use of files O/S controls access to and use of the processors, i.e., how much time can be allocated to the execution of a particular Application Program Classification of Operating Systems Interactive O/S Keyboard & Monitor Access to O/S Immediate, -

Facility/370: Introduction
File No. S370-20 Order No. GC20-1800=9 IDl\n \/:u+ •• ".1 I\n"n"': ..... ft IDIVI V IIlUQI .Via"'lllIlv Facility/370: Systems Introduction Release 6 PLC 4 This publication introduces VM/370, and is intended for anyone who is interested in VM/370. However, the reader should have a basic understanding of I BM data processing. VM/370 (Virtual Machine Facility/370) is a system control program (SCP) that tailors the resources and capabilities of a single System/370 computer to provide concurrent users their one unique (virtual) machine. VM/370 consists of a Control Program (CP), which manages the real computer, a Conversational Monitor System (CMS), which is a general-purpose conversational time-sharing system that executes in a virtual machine, a Remote Spooling Communications Subsystem (RSCS), which spools files to and from geographically remote locations, and a Interactive Problem Control System (I PCS), which provides problem analysis and management faci I ities. The first section of the publication is an introduction; it describes what VM/370 can do. The second, third, fourth, and fifth sections describe the Control Program, Conversational Monitor System, Remote Spooling Communications Subsystem, and Interactive Problem Control System respectively. The appendixes include information about VM/370 publication-to-audience relationship and VM/370-related publications for CMS users. , This publication is a prerequisite for the VM/370 system library. --...- --- ---.-- ------- ------ --..- --------- -~-y- Page of GC20-1800-9 As Updated Aug 1, 1979 by TNL GN25-0U89 ~b Edition (Karch 1919) This edition (GC20-1800-~ together with Technical Newsletter GN25-0489. dated August 1, 1919, applies to Release 6 PLC 4 (Program Level Change) of IBM Virtual Machine Facility/310 and to all subsequent releases until otherwise indicated in new editions or Technical Newsletters. -

Chapter 10 Introduction to Batch Files
Instructor’s Manual Chapter 10 Lecture Notes Introduction to Batch Files Chapter 10 Introduction to Batch Files LEARNING OBJECTIVES 1. Compare and contrast batch and interactive processing. 2. Explain how batch files work. 3. Explain the purpose and function of the REM, ECHO, and PAUSE commands. 4. Explain how to stop or interrupt the batch file process. 5. Explain the function and use of replaceable parameters in batch files. 6. Explain the function of pipes, filters, and redirection in batch files. STUDENT OUTCOMES 1. Use Edit to write batch files. 2. Use COPY CON to write batch files. 3. Write and execute a simple batch file. 4. Write a batch file to load an application program. 5. Use the REM, PAUSE, and ECHO commands in batch files. 6. Terminate a batch file while it is executing. 7. Write batch files using replaceable parameters. 8. Write a batch file using pipes, filters, and redirection. CHAPTER SUMMARY 1. Batch processing means running a series of instructions without interruption. 2. Interactive processing allows the user to interface directly with the computer and update records immediately. 3. Batch files allow a user to put together a string of commands and execute them with one command. 4. Batch files must have the .BAT or .CMD file extension. 5. Windows looks first internally for a command, then for a .COM files extension, then for a .EXE file extension, and finally for a .BAT or .CMD file extension. 6. Edit is a full-screen text editor used to write batch files. 7. A word processor, if it has a means to save files in ASCII, can be used to write batch files. -
Uni Hamburg – Mainframe Summit 2010 Z/OS – the Mainframe Operating System
Uni Hamburg – Mainframe Summit 2010 z/OS – The Mainframe Operating System Appendix 2 – JES and Batchprocessing Redelf Janßen IBM Technical Sales Mainframe Systems [email protected] © Copyright IBM Corporation 2010 Course materials may not be reproduced in whole or in part without the prior written permission of IBM. 4.0.1 Introduction to the new mainframe Chapter 7: Batch processing and the Job Entry Subsystem (JES) © Copyright IBM Corp., 2010. All rights reserved. Introduction to the new mainframe Chapter 7 objectives Be able to: • Give an overview of batch processing and how work is initiated and managed in the system. • Explain how the job entry subsystem (JES) governs the flow of work through a z/OS system. © Copyright IBM Corp., 2010. All rights reserved. 3 Introduction to the new mainframe Key terms in this chapter • batch processing • procedure • execution • purge • initiator • queue • job • spool • job entry subsystem (JES) • symbolic reference • output • workload manager (WLM) © Copyright IBM Corp., 2010. All rights reserved. 4 Introduction to the new mainframe What is batch processing? Much of the work running on z/OS consists of programs called batch jobs. Batch processing is used for programs that can be executed: • With minimal human interaction • At a scheduled time or on an as-needed basis. After a batch job is submitted to the system for execution, there is normally no further human interaction with the job until it is complete. © Copyright IBM Corp., 2010. All rights reserved. 5 Introduction to the new mainframe What is JES? In the z/OS operating system, JES manages the input and output job queues and data. -
Z/OS ♦ Z Machines Hardware ♦ Numbers and Numeric Terms ♦ the Road to Z/OS ♦ Z/OS.E ♦ Z/OS Futures ♦ Language Environment ♦ Current Compilers ♦ UNIX System Services
Mainframes The Future of Mainframes Is Now ♦ z/Architecture ♦ z/OS ♦ z Machines Hardware ♦ Numbers and Numeric Terms ♦ The Road to z/OS ♦ z/OS.e ♦ z/OS Futures ♦ Language Environment ♦ Current Compilers ♦ UNIX System Services by Steve Comstock The Trainer’s Friend, Inc. http://www.trainersfriend.com 800-993-8716 [email protected] Copyright © 2002 by Steven H. Comstock 1 Mainframes z/Architecture z/Architecture ❐ The IBM 64-bit mainframe has been named "z/Architecture" to contrast it to earlier mainframe hardware architectures ♦ S/360 ♦ S/370 ♦ 370-XA ♦ ESA/370 ♦ ESA/390 ❐ Although there is a clear continuity, z/Architecture also brings significant changes... ♦ 64-bit General Purpose Registers - so 64-bit integers and 64-bit addresses ♦ 64-bit Control Registers ♦ 128-bit PSW ♦ Tri-modal addressing (24-bit, 31-bit, 64-bit) ♦ Over 140 new instructions, including instructions to work with ASCII and UNICODE strings Copyright © 2002 by Steven H. Comstock 2 z/Architecture z/OS ❐ Although several operating systems can run on z/Architecture machines, z/OS is the premier, target OS ❐ z/OS is the successor to OS/390 ♦ The last release of OS/390 was V2R10, available 9/2000 ♦ The first release of z/OS was V1R1, available 3/2001 ❐ z/OS can also run on G5/G6 and MP3000 series machines ♦ But only in 31-bit or 24-bit mode ❐ Note these terms: ♦ The Line - the 16MiB address limit of MVS ♦ The Bar - the 2GiB limit of OS/390 ❐ For some perspective, realize that 16EiB is... ♦ 8 billion times 2GiB ♦ 1 trillion times 16MiB ❐ The current release of z/OS is V1R4; V1R5 is scheduled for 1Q2004 Copyright © 2002 by Steven H. -
Approaches to Optimize Batch Processing on Z/OS
Front cover Approaches to Optimize Batch Processing on z/OS Apply the latest z/OS features Analyze bottlenecks Evaluate critical path Alex Louwe Kooijmans Elsie Ramos Jan van Cappelle Lydia Duijvestijn Tomohiko Kaneki Martin Packer ibm.com/redbooks Redpaper International Technical Support Organization Approaches to Optimize Batch Processing on z/OS October 2012 REDP-4816-00 Note: Before using this information and the product it supports, read the information in “Notices” on page v. First Edition (October 2012) This edition applies to all supported z/OS versions and releases. This document created or updated on October 24, 2012. © Copyright International Business Machines Corporation 2012. All rights reserved. Note to U.S. Government Users Restricted Rights -- Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents Notices . .v Trademarks . vi Preface . vii The team who wrote this paper . vii Now you can become a published author, too! . viii Comments welcome. viii Stay connected to IBM Redbooks . ix Chapter 1. Getting started . 1 1.1 The initial business problem statement. 2 1.2 How to clarify the problem statement . 3 1.3 Process to formulate a good problem statement . 3 1.4 How to create a good business case . 5 1.5 Analysis methodology . 6 1.5.1 Initialization . 6 1.5.2 Analysis. 6 1.5.3 Implementation . 10 Chapter 2. Analysis steps. 13 2.1 Setting the technical strategy . 14 2.2 Understanding the batch landscape . 15 2.2.1 Identifying where batch runs and the available resources . 15 2.2.2 Job naming conventions . 15 2.2.3 Application level performance analysis. -
Managing a VSE Console Under VM from a Remote Location
BY DAN ASKEW Managing a VSE Console Under VM From a Remote Location hen working remotely, it is sometimes necessary to make changes to the system or talk an W operator through a problem. Using the techniques presented here, you can manage a VSE console under VM. you ever tried to talk an operator through a VSEPROD. You can display the virtual machine name by HAVE problem from a remote site and thought to issuing the following commands. yourself, “If I could only see the console”? As this article will This command redisplays the last 20 lines from partition BG: examine, there are several ways you can do this if you are VSECMD VSEPROD RED 20L,BG running VSE under VM. The first method I will examine allows you to communicate with the VSE con- This command displays the last line from sole in a crude line mode. The other two the console: methods allow you to actually “steal” the VSECMD VSEPROD RED existing console away from the operator. Have you ever tried to This command displays the last 20 METHOD #1 talk an operator through occurrences of EOJ: VSECMD VSEPROD RED 20l,’EOJ’ The first method I tried used a problem from a remote IBM’s VMCF modules supplied by The syntax of these commands is VSE. ICCF Library 59 contains a site and thought to as follows: member named SKVMVSE. The yourself, “If I could only VSECMD (VSE machine name) comments at the beginning of the RED (number of lines (default is member provide you with the installa- see the console”? 1)), (redisplay command) tion instructions. -
Classification of Computers
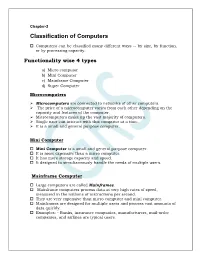
Chapter-2 Classification of Computers Computers can be classified many different ways -- by size, by function, or by processing capacity. Functionality wise 4 types a) Micro computer b) Mini Computer c) Mainframe Computer d) Super Computer Microcomputers Microcomputers are connected to networks of other computers. The price of a microcomputer varies from each other depending on the capacity and features of the computer. Microcomputers make up the vast majority of computers. Single user can interact with this computer at a time. It is a small and general purpose computer. Mini Computer Mini Computer is a small and general purpose computer. It is more expensive than a micro computer. It has more storage capacity and speed. It designed to simultaneously handle the needs of multiple users. Mainframe Computer Large computers are called Mainframes. Mainframe computers process data at very high rates of speed, measured in the millions of instructions per second. They are very expensive than micro computer and mini computer. Mainframes are designed for multiple users and process vast amounts of data quickly. Examples: - Banks, insurance companies, manufacturers, mail-order companies, and airlines are typical users. Super Computers The largest computers are Super Computers. They are the most powerful, the most expensive, and the fastest. They are capable of processing trillions of instructions per second. It uses governmental agencies, such as:- Chemical analysis in laboratory Space exploration National Defense Agency National Weather Service Bio-Medical research Design of many other machines Limitations of Computer Computer cannot take over all activities simply because they are less flexible than humans. It does not hold intelligence of its own. -

Parallel Processing Here at the School of Statistics
Parallel Processing here at the School of Statistics Charles J. Geyer School of Statistics University of Minnesota http://www.stat.umn.edu/~charlie/parallel/ 1 • batch processing • R package multicore • R package rlecuyer • R package snow • grid engine (CLA) • clusters (MSI) 2 Batch Processing This is really old stuff (from 1975). But not everyone knows it. If you do the following at a unix prompt nohup nice -n 19 some job & where \some job" is replaced by an actual job, then • the job will run in background (because of &). • the job will not be killed when you log out (because of nohup). • the job will have low priority (because of nice -n 19). 3 Batch Processing (cont.) For example, if foo.R is a plain text file containing R commands, then nohup nice -n 19 R CMD BATCH --vanilla foo.R & executes the commands and puts the printout in the file foo.Rout. And nohup nice -n 19 R CMD BATCH --no-restore foo.R & executes the commands, puts the printout in the file foo.Rout, and saves all created R objects in the file .RData. 4 Batch Processing (cont.) nohup nice -n 19 R CMD BATCH foo.R & is a really bad idea! It reads in all the objects in the file .RData (if one is present) at the beginning. So you have no idea whether the results are reproducible. Always use --vanilla or --no-restore except when debugging. 5 Batch Processing (cont.) This idiom has nothing to do with R. If foo is a compiled C or C++ or Fortran main program that doesn't have command line arguments (or a shell, Perl, Python, or Ruby script), then nohup nice -n 19 foo & runs it. -

IBM Z/VSE 6.2 Brings Storage, Processing, Security, Recovery, and Data Transfer Enhancements
IBM United States Software Announcement 221-201, dated May 4, 2021 IBM z/VSE 6.2 brings storage, processing, security, recovery, and data transfer enhancements Table of contents 1 Overview 5 Technical information 2 Key requirements 7 Ordering information 2 Planned availability date 7 Terms and conditions 2 Description 8 Order now 5 Program number Overview IBM(R) z/VSE(R) is an operating system for the IBM Z(R) platform used for traditional batch and online transaction processing applications. The following hardware support is available with z/VSE 6.2: • Exploitation of the latest IBM System Storage technology: – z/VSE 6.2 supports IBM System Storage TS7700 R5.1. • Exploitation of latest IBM z15TM Model T01 and T02 technology: – z/VSE 6.2 provides native support for System Recovery Boost (APAR DY47832). This enables z/VSE to temporarily boost general-purpose central processors (CPs) running at sub-capacity to full capacity in a logical partition (LPAR) during system IPL and shutdown. – z/VSE 6.2 supports the configurable IBM Crypto Express7S (APAR DY47834), which enables data encryption and Secure Sockets Layer (SSL) acceleration. Elliptic Curve Cryptography (ECC) with a Crypto Express7S can result in accelerated data-in-flight encryption. The following support is already available with z/VSE 6.2: • z/VSE supports the IBM Fibre Connection (FICON(R)) Express16S+ and FICON Express16SA, as well as the OSA-Express6S/7S family. • z/VSE supports IBM Fibre Channel Endpoint Security, which provides server authentication and data encryption to protect the integrity and confidentiality of data. z/VSE support for Transport Layer Security (TLS) 1.3: • TLS 1.3 support (APAR DY30239) is based on VSE Crypto Services/OpenSSL 1.1.1d update (APAR DY47825, in March 2020).