13347 CICS Introduction and Overview
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Cloud Enabling CICS
Front cover Cloud Enabling IBM CICS Discover how to quickly cloud enable a traditional IBM 3270-COBOL-VSAM application Use CICS Explorer to develop and deploy a multi-versioned application Understand the benefits of threshold policy Rufus Credle Isabel Arnold Andrew Bates Michael Baylis Pradeep Gohil Christopher Hodgins Daniel Millwood Ian J Mitchell Catherine Moxey Geoffrey Pirie Inderpal Singh Stewart Smith Matthew Webster ibm.com/redbooks International Technical Support Organization Cloud Enabling IBM CICS December 2014 SG24-8114-00 Note: Before using this information and the product it supports, read the information in “Notices” on page vii. First Edition (December 2014) This edition applies to CICS Transaction Server for z/OS version 5.1, 3270-COBOL-VSAM application. © Copyright International Business Machines Corporation 2014. All rights reserved. Note to U.S. Government Users Restricted Rights -- Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents Notices . vii Trademarks . viii IBM Redbooks promotions . ix Preface . xi Authors. xii Now you can become a published author, too! . .xv Comments welcome. .xv Stay connected to IBM Redbooks . xvi Part 1. Introduction . 1 Chapter 1. Cloud enabling your CICS TS applications . 3 1.1 Did you know?. 4 1.2 Business value . 4 1.3 Solution overview . 5 1.4 Cloud computing in a CICS TS context. 6 1.5 Overview of the cloud-enabling technologies in CICS TS V5 . 11 1.5.1 Platform overview . 12 1.5.2 Application overview . 13 Chapter 2. GENAPP introduction. 15 2.1 CICS TS topology . 16 2.2 Application architecture. 17 2.2.1 GENAPP in a single managed region. -

Introduction-To-Mainframes.Pdf
Mainframe The term ‘MainFrame’ brings to mind a giant room of electronic parts that is a computer, referring to the original CPU cabinet in a computer of the mid-1960’s. Today, Mainframe refers to a class of ultra-reliable large and medium-scale servers designed for carrier-class and enterprise-class systems operations. Mainframes are costly, due to the support of symmetric multiprocessing (SMP) and dozens of central processors existing within in a single system. Mainframes are highly scalable. Through the addition of clusters, high-speed caches and volumes of memory, they connect to terabyte holding data subsystems. Mainframe computer Mainframe is a very large and expensive computer capable of supporting hundreds, or even thousands, of users simultaneously. In the hierarchy that starts with a simple microprocessor at the bottom and moves to supercomputers at the top, mainframes are just below supercomputers. In some ways, mainframes are more powerful than supercomputers because they support more simultaneous programs. But supercomputers can execute a single program faster than a mainframe. The distinction between small mainframes and minicomputers is vague, depending really on how the manufacturer wants to market its machines. Modern mainframe computers have abilities not so much defined by their single task computational speed (usually defined as MIPS — Millions of Instructions Per Second) as by their redundant internal engineering and resulting high reliability and security, extensive input-output facilities, strict backward compatibility with older software, and high utilization rates to support massive throughput. These machines often run for years without interruption, with repairs and hardware upgrades taking place during normal operation. -

CICS Transaction Server for OS/390 Installation Guide
CICS® Transaction Server for OS/390® Installation Guide Release 3 GC33-1681-30 CICS® Transaction Server for OS/390® Installation Guide Release 3 GC33-1681-30 Note! Before using this information and the product it supports, be sure to read the general information under “Notices” on page xi. Third edition (June 1999) This edition applies to Release 3 of CICS Transaction Server for OS/390, program number 5655-147, and to all subsequent versions, releases, and modifications until otherwise indicated in new editions. Make sure you are using the correct edition for the level of the product. This edition replaces and makes obsolete the previous edition, SC33-1681-00. The technical changes for this edition are summarized under ″Summary of changes″ and are indicated by a vertical bar to the left of a change. Order publications through your IBM representative or the IBM branch office serving your locality. Publications are not stocked at the address given below. At the back of this publication is a page entitled “Sending your comments to IBM”. If you want to make comments, but the methods described are not available to you, please address them to: IBM United Kingdom Laboratories, Information Development, Mail Point 095, Hursley Park, Winchester, Hampshire, England, SO21 2JN. When you send information to IBM, you grant IBM a nonexclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. © Copyright International Business Machines Corporation 1989, 1999. All rights reserved. US Government Users Restricted Rights – Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. -
CA Datacom CICS Services Best Practices Guide
CA Datacom® CICS Services Best Practices Guide Version 14.02 This Documentation, which includes embedded help systems and electronically distributed materials (hereinafter referred to as the “Documentation”), is for your informational purposes only and is subject to change or withdrawal by CA at any time. This Documentation may not be copied, transferred, reproduced, disclosed, modified or duplicated, in whole or in part, without the prior written consent of CA. This Documentation is confidential and proprietary information of CA and may not be disclosed by you or used for any purpose other than as may be permitted in (i) a separate agreement between you and CA governing your use of the CA software to which the Documentation relates; or (ii) a separate confidentiality agreement between you and CA. Notwithstanding the foregoing, if you are a licensed user of the software product(s) addressed in the Documentation, you may print or otherwise make available a reasonable number of copies of the Documentation for internal use by you and your employees in connection with that software, provided that all CA copyright notices and legends are affixed to each reproduced copy. The right to print or otherwise make available copies of the Documentation is limited to the period during which the applicable license for such software remains in full force and effect. Should the license terminate for any reason, it is your responsibility to certify in writing to CA that all copies and partial copies of the Documentation have been returned to CA or destroyed. TO THE EXTENT PERMITTED BY APPLICABLE LAW, CA PROVIDES THIS DOCUMENTATION “AS IS” WITHOUT WARRANTY OF ANY KIND, INCLUDING WITHOUT LIMITATION, ANY IMPLIED WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE, OR NONINFRINGEMENT. -

Enterprise PL/I for Z/OS V5.3 Compiler and Runtime Migration Guide Part 1
Enterprise PL/I for z/OS Version 5 Release 3 Compiler and Run-Time Migration Guide IBM GC27-8930-02 Note Before using this information and the product it supports, be sure to read the general information under “Notices” on page 181. Third Edition (September 2019) This edition applies to Version 5 Release 3 of Enterprise PL/I for z/OS, 5655-PL5, and to any subsequent releases until otherwise indicated in new editions or technical newsletters. Make sure you are using the correct edition for the level of the product. Order publications through your IBM representative or the IBM branch office serving your locality. Publications are not stocked at the address below. A form for readers' comments is provided at the back of this publication. If the form has been removed, address your comments to: IBM Corporation, Department H150/090 555 Bailey Ave San Jose, CA, 95141-1099 United States of America When you send information to IBM, you grant IBM a nonexclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. Because IBM® Enterprise PL/I for z/OS® supports the continuous delivery (CD) model and publications are updated to document the features delivered under the CD model, it is a good idea to check for updates once every three months. © Copyright International Business Machines Corporation 1999, 2019. US Government Users Restricted Rights – Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents Tables.................................................................................................................. xi Figures............................................................................................................... xiii About this book....................................................................................................xv Using your documentation........................................................................................................................ -
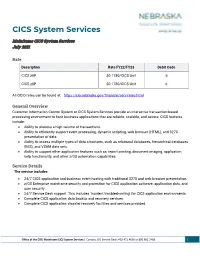
CICS System Services
CICS System Services Mainframe CICS System Services July 2021 Rate Description Rate FY22/FY23 Debit Code CICS zIIP $0.1780/CICS Unit 5 CICS zIIP $0.1780/CICS Unit 6 All OCIO rates can be found at: https://cio.nebraska.gov/financial/serv-rates.html General Overview Customer Information Control System or CICS System Services provide an interactive transaction-based processing environment to host business applications that are reliable, scalable, and secure. CICS features include: • Ability to process a high volume of transactions. • Ability to efficiently support event processing, dynamic scripting, web browser (HTML), and 3270 presentation of data. • Ability to access multiple types of data structures, such as relational databases, hierarchical databases (IMS), and VSAM data sets. • Ability to support other application features such as; report printing, document imaging, application help functionality, and other z/OS automation capabilities. Service Details The service includes: • 24/7 CICS application and business event hosting with traditional 3270 and web browser presentation. • z/OS Enterprise mainframe security and protection for CICS application software, application data, and user security. • 24/7 Service Desk support. This includes ‘incident troubleshooting’ for CICS application environments. • Complete CICS application data backup and recovery services. • Complete CICS application disaster recovery facilities and services provided. Office of the CIO/ Mainframe CICS System Services | Contact: CIO Service Desk: 402.471.4636 or 800.982.2468 1 CICS System Services • z/OS System automation available for unique CICS application mainframe requirements. • CICS automated services to coordinate application “On-line” and “Batch” processes. • Automated software to generate CICS maps. • Automated software to assist applications with reporting (style sheets). -

Appendix A: Current Environment Overview the Following Subsections Provide an Overview of the Current Technical Environment
1 Appendix A: Current Environment Overview The following subsections provide an overview of the current technical environment. N-FOCUS – Nebraska’s Legacy Integrated Health and Human Services and Benefits Application Nebraska Family Online Client User System (N-FOCUS) is an integrated system that automates benefit/service delivery and case management for more than 30 DHHS programs, including Aid to Dependent Children (ADC), Supplemental Nutrition Assistance Program (SNAP), Child Welfare and Medicaid. The system was initially developed in partnership with Accenture as the prime Systems Integrator. N-FOCUS functions include client/case intake, eligibility determination, case management, service authorization, benefit payments, claims processing and payments, provider contract management, interfacing with other private, state and federal organizations, and management and government reporting. N-FOCUS was implemented in production in mid-1996 and is operational statewide. The typical N-FOCUS user is a DHHS or contracted employee. N-FOCUS supports over 2500 workers, operating from offices around the State as well as from 4 customer service centers and a centralized scanning facility. Some cases are assigned to specific workers; however, the majority of cases are managed via a universal caseload methodology coordinated by the customer service centers. N-FOCUS has both batch and online components and stores data in Db2 and SQL Server. The Db2 database has over 650 tables, some with a corresponding archive table. There are over 785 relationships between tables, 1278 indexes, and over 9665 attributes. There are over 1.7 billion rows of production data with over 193 million rows in one table with an average table size of 3.2 million rows. -

Writing a Web-Enabled CICS/COBOL Program SHARE March 2011
User Experience: Writing a web-enabled CICS/COBOL program SHARE March 2011 Craig Schneiderwent State of Wisconsin Department of Transportation [email protected] #include <std/disclaimer.h> 1 Any opinions expressed are my own and do not necessarily reflect those of my employer. You wouldn’t believe the amount of red tape that one statement gets me out of. What You Will See • Web-enabled CICS/COBOL code (CICS Web Support as opposed to Services) • Other cool, webby stuff – COBOL to generate XML – COBOL to parse XML • The COBOL is just snippets, an entire working application is available on the SHARE website with the materials for this session 2 This presentation grew out of a proof of concept application I wrote to help out our development staff. Please note the bit about CICS Web Support vs. CICS Web Services. The former is what I’m going to talk about, the latter is the more formal SOAP and WSDL stuff. Many people think these cannot coexist, they can. Many people think the latter supersedes the former, it does not. Both have their uses, both have their place, both have their adherents to varying degrees of zealotry. The proof of concept application receives parameters and based on those will send HTML, XML, an HTML form, or an image from CICS back to the requesting web browser. Main entry point in the application is J7200544. Environment (at the Time) • z/OS 1.6, CICS TS 2.2, DB2 7.1, Enterprise COBOL 3.4 • WebSphere Application Server (WAS) 5.x on Windows • 20 years worth of CASE tool generated business logic in CICS • CASE tool runtime uses CICS COMMAREAs to pass data out of CICS 3 Since then we've been migrated to WAS 6, z/OS 1.11, DB2 v8, and CICS TS 3.2. -

CICS TS for Z/OS: What's New Chapter 1
CICS Transaction Server for z/OS 5.5 What's New IBM Note Before using this information and the product it supports, read the information in “Notices” on page 49. This edition applies to the IBM® CICS® Transaction Server for z/OS® Version 5 Release 5 (product number 5655-Y04) and to all subsequent releases and modifications until otherwise indicated in new editions. © Copyright International Business Machines Corporation 1974, 2020. US Government Users Restricted Rights – Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents About this PDF.......................................................................................................v Chapter 1. What's new?......................................................................................... 1 Chapter 2. Changes to externals in this release.....................................................25 Notices................................................................................................................49 iii iv About this PDF "What's New" is a summary of the new features and capabilities of the latest version of CICS Transaction Server for z/OS. Details of how to use these features is provided in the rest of the product documentation. It also summarizes any changes to CICS externals, such as the application programming interface, for this version of CICS TS. "What's New" is primarily aimed at application programmers and system programmers who need to understand the scope of the new release. For details of the terms and notation used in this book, see Conventions and terminology used in the CICS documentation in IBM Knowledge Center. Date of this PDF This PDF was created on October 19th 2020. © Copyright IBM Corp. 1974, 2020 v vi CICS TS for z/OS: What's New Chapter 1. What's new? CICS Transaction Server for z/OS, Version 5 Release 5 enables development teams to create powerful, mixed-language applications while allowing the operational teams to manage these applications from a single point of control. -

Language Environment for Dummies: What Is LE and How Do I Get There?
Language Environment for Dummies: What is LE and How Do I Get There? Thomas Petrolino IBM Poughkeepsie [email protected] SHARE in Boston August, 2010 Trademarks The following are trademarks of the International Business Machines Corporation in the United States and/or other countries. •CICS® •DB2® •Language Environment® •OS/390® •z/OS® * Registered trademarks of IBM Corporation The following are trademarks or registered trademarks of other companies. Java and all Java-related trademarks and logos are trademarks of Sun Microsystems, Inc., in the United States and other countries. Linux is a registered trademark of Linus Torvalds in the United States, other countries, or both. Microsoft, Windows and Windows NT are registered trademarks of Microsoft Corporation. UNIX is a registered trademark of The Open Group in the United States and other countries. SET and Secure Electronic Transaction are trademarks owned by SET Secure Electronic Transaction LLC. * All other products may be trademarks or registered trademarks of their respective companies. Notes : Performance is in Internal Throughput Rate (ITR) ratio based on measurements and projections using standard IBM benchmarks in a controlled environment. The actual throughput that any user will experience will vary depending upon considerations such as the amount of multiprogramming in the user's job stream, the I/O configuration, the storage configuration, and the workload processed. Therefore, no assurance can be given that an individual user will achieve throughput improvements equivalent to the performance ratios stated here. IBM hardware products are manufactured from new parts, or new and serviceable used parts. Regardless, our warranty terms apply. All customer examples cited or described in this presentation are presented as illustrations of the manner in which some customers have used IBM products and the results they may have achieved. -

Transforming Mainframe Performance Management
Transforming Mainframe Performance Management Mainframes still run nearly 70 percent of modern workloads, Deliver at speed with including 90 percent of the Fortune 500’s core business complete transparency processes. They are the systems of record for most of the insurance, aviation, health care, financial, and government More than 90 of the world’s top 100 banks rely on sectors worldwide, managing billions of transactions every mainframes to process over seven trillion dollars in credit day. They host more data with greater economic value than all card transactions alone every year. If your mainframe keeps other platforms combined. Clearly, mainframes are absolutely your business running, you need to understand how each vital to business. subsystem is performing. IBM Z® APM Connect enables Enterprises must innovate on top of their mainframes to AppDynamics to track detailed transactions between ensure stability and still keep up with the pace of change. individual z/OS® subsystems. This gateway, tightly integrated But transaction volumes are exploding, with distributed and with AppDynamics, empowers users to incorporate these containerized applications driving ever-increasing workloads transactional performance metrics into their greater down to these systems of record. Already stretched IT teams application monitoring ecosystem. Until now, mainframes are further strained tracking down and isolating the source of were the black box “endpoint” for transaction monitoring, issues within the mainframe’s multiple subsystems. They need only allowing a surface view of issues impacting application to pinpoint the component quickly and act, or the business performance. Today, AppDynamics users can finally will suffer. So, while most APM solutions see mainframes as understand the true end-to-end structure of their most black boxes, AppDynamics and IBM® understand what’s complex applications, including every mainframe component going on inside. -

Brief Intro to Mainframe and Z/OS Administration
Brief Intro to Mainframe and z/OS Administration By Luis F. Bustamante What is a mainframe? What is a mainframe? What is a mainframe? • Developed in 1950s • First mass-produced digital, all-transistorized, business computer that could be afforded by many businesses worldwide. • 1st general purpose computers • Designed with business applications in mind What is a mainframe? • Market dominated by IBM (90%+) – Made in Poughkeepsie, NY • Large-Scale computing • Large Enterprises • z Architecture (not x86 or x64) • Run various Operating Systems – z/OS – z/VM – Linux What is a mainframe? • Runs Multiple OS instances - LPAR • Serves tens of thousands of users • Manages petabytes of data • Very reliable • Used for Mission Critical Applications • Expensive (Cost Savings from Consolidation) • Scalable (After initial investment) • Highly secure • Large Data processing • Central data repository What is a mainframe? Typical Mainframe Workloads Batch Workload •Reports •Data consolidation •Billing •Account statements •Data Analytics Transactions • Quick interactions - Seconds, or fractions of seconds • Millions/billions transactions per day • Thousand of concurrent users • Require high availability • Examples: – Banks: ATM, Tellers, Financial Records – Airline reservations – Inventory control – Government: Tax processing, license issuance and management Transactions • Usually under CICS in z/OS: • CICS – Transaction Server – HTTP (REST, SOAP) – Web – Java – Cobol – C/C++ Roles in the Mainframe World Who uses mainframes? • 80% of fortune 500 companies • Banking • Finance • Health care • Insurance • Public utilities • Government What is z/OS? • Most common mainframe OS • EBCDIC (Extended Binary Coded Decimal Interchange Code) character set as opposed to ASCII • Implements POSIX compliant UNIX kernel to run UNIX type applications. • All kinds of workloads: – COBOL: usually legacy applications – Web services/interfaces.