The Hardware Hacker
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Report to the President: MIT and the Prosecution of Aaron Swartz
Report to the President MIT and the Prosecution of Aaron Swartz Review Panel Harold Abelson Peter A. Diamond Andrew Grosso Douglas W. Pfeiffer (support) July 26, 2013 © Copyright 2013, Massachusetts Institute of Technology This worK is licensed under a Creative Commons Attribution 3.0 Unported License. PRESIDENT REIF’S CHARGE TO HAL ABELSON | iii L. Rafael Reif, President 77 Massachusetts Avenue, Building 3-208 Cambridge, MA 02139-4307 U.S.A. Phone 1-617-253-0148 !"#$"%&'(()'(*+,' ' -."%'/%01.220%'34.520#6' ' 78#9.'1"55'(*+*)':;<'="2'4..#'8#>05>.?'8#'.>.#@2'"%828#A'1%0B'"9@80#2'@"C.#'4&'3"%0#'7D"%@E'@0' "99.22'!7<FG'@=%0$A='@=.':;<'90BH$@.%'#.@D0%CI';'=">.'"2C.?'&0$)'"#?'&0$'=">.'A%"980$25&' "A%..?)'@0'%.>8.D':;<J2'8#>05>.B.#@I' ' <=.'H$%H02.'01'@=82'%.>8.D'82'@0'?.29%84.':;<J2'"9@80#2'"#?'@0'5."%#'1%0B'@=.BI'K0$%'%.>8.D' 2=0$5?'L+M'?.29%84.':;<J2'"9@80#2'"#?'?.98280#2'?$%8#A'@=.'H.%80?'4.A8##8#A'D=.#':;<'18%2@' 4.9"B.'"D"%.'01'$#$2$"5'!7<FGN%.5"@.?'"9@8>8@&'0#'8@2'#.@D0%C'4&'"'@=.#N$#8?.#@818.?'H.%20#)' $#@85'@=.'?."@='01'3"%0#'7D"%@E'0#'!"#$"%&'++)'(*+,)'L(M'%.>8.D'@=.'90#@.O@'01'@=.2.'?.98280#2'"#?' @=.'0H@80#2'@="@':;<'90#28?.%.?)'"#?'L,M'8?.#@81&'@=.'822$.2'@="@'D"%%"#@'1$%@=.%'"#"5&282'8#'0%?.%' @0'5."%#'1%0B'@=.2.'.>.#@2I' ' ;'@%$2@'@="@'@=.':;<'90BB$#8@&)'8#95$?8#A'@=02.'8#>05>.?'8#'@=.2.'.>.#@2)'"5D"&2'"9@2'D8@='=8A=' H%01.2280#"5'8#@.A%8@&'"#?'"'2@%0#A'2.#2.'01'%.2H0#284858@&'@0':;<I'P0D.>.%)':;<'@%8.2'90#@8#$0$25&' @0'8BH%0>.'"#?'@0'B..@'8@2'=8A=.2@'"2H8%"@80#2I';@'82'8#'@="@'2H8%8@'@="@';'"2C'&0$'@0'=.5H':;<'5."%#' 1%0B'@=.2.'.>.#@2I' -

Keeping Secrets in Hardware: the Microsoft Xboxtm Case Study
Keeping Secrets in Hardware: The Microsoft XboxTM Case Study Andrew Huang Massachusetts Institute of Technology, Cambridge MA 02139, USA, [email protected], http://www.xenatera.com/bunnie/ Abstract. This paper discusses the hardware foundations of the cryp- tosystem employed by the XboxTM video game console from Microsoft. A secret boot block overlay is buried within a system ASIC. This secret boot block decrypts and verifies portions of an external FLASH-type ROM. The presence of the secret boot block is camouflaged by a decoy boot block in the external ROM. The code contained within the secret boot block is transferred to the CPU in the clear over a set of high-speed busses where it can be extracted using simple custom hardware. The paper concludes with recommendations for improving the Xbox security system. One lesson of this study is that the use of a high-performance bus alone is not a sufficient security measure, given the advent of inexpensive rapid prototyping services and affordable high-performance FPGAs. 1 Introduction and Background Every cryptosystem is based on some kind of secret, such as a key. Regardless of the cipher, the security of a cryptosystem is only as strong as the secrecy of the key. Thus, some of the most startlingly effective attacks on a cryptosystem involve no ciphertext analysis, but instead find flaws in the protocols that manage the keys. Cryptosystems based on symmetric ciphers are particularly vulnerable to protocol attacks, since both the sender and the receiver must be trusted to have a copy of the same secret key. -

A Study of the Application of Free and Open Source Software Licensing Ideas to Art and Cultural Production
Sandbox Culture A Study of the Application of Free and Open Source Software Licensing Ideas to Art and Cultural Production Aymeric Mansoux Supervisor: Matthew Fuller Thesis presented for the degree of Doctor of Philosophy Centre for Cultural Studies, Goldsmiths, University of London, February 2017 I, Aymeric Mansoux, confirm that the work presented in this thesis ismy own. Where information has been derived from other sources, I confirm that this has been indicated in the thesis. Date: February 19, 2017 Signed: Abstract In partial response to the inability of intellectual property laws to adapt to data-sharing over computer networks, several initiatives have proposed techno-legal alternatives to encourage the free circulation and transfor- mation of digital works. These alternatives have shaped part of contem- porary digital culture for more than three decades and are today often associated with the “free culture” movement. The different strands of this movement are essentially derived from a narrower concept of soft- ware freedom developed in the nineteen-eighties, and which is enforced within free and open source software communities. This principle was the first significant effort to articulate a reusable techno-legal template to work around the limitations of intellectual property laws. It also of- fered a vision of network culture where community participation and sharing was structural. From alternate tools and workflow systems, artist-run servers, net- work publishing experiments, open data and design lobbies, cooperative and collaborative frameworks, but also novel copyright licensing used by both non-profit organisations and for-profit corporations, the impact on cultural production of practices developed in relation to the ideas of iii free and open source software has been both influential and broadly ap- plied. -

A Hands-On Security Course
A HANDS-ON SECURITY COURSE by ANDREW HENNESSY Submitted in partial fulfillment of the requirements for the degree of Master of Science Department of Electrical Engineering and Computer Science CASE WESTERN RESERVE UNIVERSITY May 2017 CASE WESTERN RESERVE UNIVERSITY SCHOOL OF GRADUATE STUDIES We hereby approve the thesis of Andrew Hennessy candidate for the degree of Master of Science*. Committee Chair Dr. Kenneth Loparo Committee Member Dr. Francis Merat Committee Member Dr. Gregory Lee Date of Defense April 6, 2017 *We also certify that written approval has been obtained for any proprietary material contained therein. Contents List of Tables v List of Figures vi Acknowledgments viii Abstract x 1 Introduction 1 1.1 Other Courses at Different Universities . .2 1.2 Organization of the Thesis . .3 2 Laboratory Environment 4 2.1 Equipment and Tools Needed . .5 2.2 Experimental Board . .6 2.2.1 Purpose-Designed Board . .6 2.2.2 Off-the-shelf Boards . 18 3 Syllabus 20 3.1 Prerequisites . 20 3.2 Credit Hours . 20 3.3 Course Description . 20 3.4 Key Concepts . 21 i CONTENTS 3.5 Course Requirements . 21 3.6 Student Expectations . 21 3.7 Lecture Schedule . 22 3.8 Grading . 22 3.9 Student Conduct and Academic Integrity . 23 3.10 Expected Outcomes . 23 4 Lab #1: Buffer Overflows 24 4.1 Objectives . 24 4.2 Assignment . 24 4.2.1 Introduction . 24 4.2.2 Instructions . 25 4.3 Assignment Files . 26 4.4 Solutions . 29 5 Lab #2: Diffie-Hellman Key Exchange 32 5.1 Objectives . 32 5.2 Assignment . -
Hacking the Xbox
$24.99 ($34.99 CDN) SHELVE IN: PC HARDWARE/GENERAL HACKING THE XBOX Get Hacking the Xbox before Microsoft Does! qANQR1DBwU4DiyVm0iq7P8gQB/9IoylwNnOxHExELKfHCTyOxX1m/eKe3+bgN/kc afpcdG1BR0ZV3degJhP2ru8h58Tw/MLU+h+jMYPUOCulwRAMyhxqX+0K1fU0oNAd 1UKi0e8sju0mks0XXzEOXNpM6BO8L90/NCSUTWPBUMgR6/KtezsFJUDAIOlxVuBX IpN1x+6A3O6Tayrg0+Qp+hD3FDRSIVKoD/uiaCnxkp5wxXh3JPRU3JMHWtUcwsr2 ThN1xhandO6Tn gg0dep+hDhackingKwas iaCcekledxby3JheUoriginalwsr2 This hands-on guide to hacking was canceled by the original Hacking publisher out of fear of DMCA-related lawsuits. Following the author’s self-publication of the book (during which time he sold thousands directly), Hacking the Xbox is now brought to you by No Starch Press. Hacking the Xbox begins with a few step-by-step tutorials on the Xbox hardware modifications that teach basic hacking techniques as well as essential reverse engineering skills. It progresses into An Introduction to Reverse Engineering a discussion of the Xbox security mechanisms and other advanced hacking topics, emphasizing the important subjects of computer security and reverse engineering. The book includes numerous practical guides, such as where to get hacking gear, soldering techniques, debugging tips, and an Xbox hardware reference guide. Hacking the Xbox confronts the social and political issues facing today’s hacker, and introduces readers to the humans behind the hacks through several interviews with master hackers. It looks at the potential impact of today’s legal challenges to legitimate Andrew “bunnie” Huang reverse engineering -

1 United States District Court District of Columbia Matthew Green 4506
Case 1:16-cv-01492 Document 1 Filed 07/21/16 Page 1 of 32 UNITED STATES DISTRICT COURT DISTRICT OF COLUMBIA MATTHEW GREEN 4506 Roland Ave. Baltimore, MD 21210, ANDREW HUANG 233 Bain St. #10-01 Singapore 180233 Singapore, and ALPHAMAX, LLC Civil Case No. __________ 560 Lodge Lane Kalamazoo, MI 49009, COMPLAINT FOR DECLARATORY Plaintiffs, AND INJUNCTIVE RELIEF v. U.S. DEPARTMENT OF JUSTICE, LORETTA LYNCH 950 Pennsylvania Ave., NW Washington, D.C. 20530, LIBRARY OF CONGRESS, CARLA HAYDEN 101 Independence Ave., SE Washington, D.C. 20540 U.S. COPYRIGHT OFFICE, MARIA PALLANTE 101 Independence Ave., SE Washington, D.C. 20559-600, Defendants. 1 Case 1:16-cv-01492 Document 1 Filed 07/21/16 Page 2 of 32 Plaintiffs Matthew Green, Andrew “bunnie” Huang, and Alphamax, LLC, by and through their attorneys, allege as follows: INTRODUCTION 1. This lawsuit challenges the “anti-circumvention” and “anti-trafficking” provisions of the Digital Millennium Copyright Act (“DMCA”), 17 U.S.C. §§ 1201(a), 1203, and 1204 (collectively “the DMCA Anti-Circumvention Provisions”). Enacted in 1998, these provisions broadly restrict the public’s ability to access, speak about, and use copyrighted materials, without the traditional safeguards—such as the fair use doctrine—that are necessary to protect free speech and allow copyright law to coexist with the First Amendment. The threat of enforcement of these provisions chills protected and noninfringing speech that relies on copyrighted works, including independent technical research into computer security systems and the discussion of that research, and accessing copyrighted works in order to shift the content to a different format, space, or time. -
"Bunnie" Huang, and "The Linux Command Line"
Stories Firehose All Popular Polls Deals Submit Search Login or Sign4 5up Topics: Devices Build Entertainment Technology Open Source Science YRO Follow us: Catch up on stories from the past week (and beyond) at the Slashdot story archive Nickname: Password: 6-20 characters long Public Terminal Log In Forgot your password? Sign in with Google Facebook Twitter LinkedIn Close 403 Forbidden nginx 403 Forbidden Learn to Build 14 Websites with 28 Hours of Instruction on HTML, JavaScript, MySQL & More for $14 × nginx Humble Bundle Announces 'Hacker' Pay-What-You-Want Sale (humblebundle.com) Posted by EditorDavid on Saturday April 30, 2016 @01:30PM from the supporting-the-EFF dept. An anonymous reader writes: Humble Bundle announced a special "pay what you want" sale for four ebooks from No Starch Press, with proceeds going to the Electronic Frontier Foundation (or to the charity of your choice). This "hacker edition" sale includes two relatively new titles from 2015 -- "Automate the Boring Stuff with Python" and Violet Blue's "Smart Girl's Guide to Privacy," as well as "Hacking the Xbox: An Introduction to Reverse Engineering" by Andrew "bunnie" Huang, and "The Linux Command Line". Hackers who are willing to pay "more than the average" -- currently $14.87 -- can also unlock a set of five more books, which includes "The Maker's Guide to the Zombie Apocalypse: Defend Your Base with Simple Circuits, Arduino, and Raspberry Pi". (This level also includes "Bitcoin for the Befuddled" and "Designing BSD Rootkits: An Introduction to Kernel Hacking".) And at the $15 level -- just 13 cents more -- four additional books are unlocked. -
Brian M. Willen (D.C
Case 1:16-cv-01492-EGS Document 16-1 Filed 09/29/16 Page 1 of 40 BRIAN M. WILLEN (D.C. BN 490471) CORYNNE MCSHERRY WILSON SONSINI (CA SBN 221504) GOODRICH & ROSATI, P.C. KIT WALSH (CA SBN 303598) 1301 Avenue of the Americas ADAM SCHWARTZ (CA SBN 309491) 40th Floor ELECTRONIC FRONTIER New York, NY 10019 FOUNDATION Tel. (212) 999-5800 815 Eddy Street San Francisco, CA 94109 STEPHEN GIKOW (CA SBN 302484) Tel. (415) 436-9333 LAUREN GALLO WHITE (CA SBN 309075) WILSON SONSINI GOODRICH & ROSATI, P.C. One Market Plaza Spear Tower, Suite 3300 San Francisco, CA 94105 Tel. (415) 947-2000 Counsel for Plaintiffs UNITED STATES DISTRICT COURT DISTRICT OF COLUMBIA Matthew Green, Andrew Huang, and ) Alphamax, LLC, ) Civil Case No. 16-cv-01492-EGS ) Plaintiff, ) ) MEMORANDUM OF POINTS AND v. ) AUTHORITIES IN SUPPORT OF ) MOTION FOR PRELIMINARY U.S. Department Of Justice, Loretta Lynch, ) INJUNCTION ON BEHALF OF ) PLAINTIFF MATTHEW GREEN Library Of Congress, Carla Hayden, ) PURSUANT TO FED. R. CIV. P. 65(a) U.S. Copyright Office, and ) Maria Pallante, ) Judge: Emmet G. Sullivan ) Defendants. ) Hearing Requested ) ) MEM OF POINTS AND AUTHORITIES ISO MOT. FOR PRELIMINARY INJUNCTION CASE NO. 16-CV-01492-EGS Case 1:16-cv-01492-EGS Document 16-1 Filed 09/29/16 Page 2 of 40 TABLE OF CONTENTS Page INTRODUCTION ...................................................................................................................... 1 FACTUAL BACKGROUND ...................................................................................................... 2 A. To Perform His Important Security Research, Dr. Green Must Be Able to Circumvent Access Controls On The Works He Studies ....................................... 2 B. For His Research To Be Effective, Dr. Green Must Be Able To Discuss How To Circumvent Access Controls and Publish His Results ............................ -

Tajana Simunic Rosing, ”Optimal Distributed Nonlinear Battery Control”, IEEE Journal of Emerging and Selected Topics in Power Electronics, 2017
Tajana Šimunić Rosing [email protected] http://www.cse.ucsd.edu/~trosing/ ( 858 ) 534-4868 INTERESTS energy-efficient computing, embedded systems hardware and software design PROFESSIONAL EXPERIENCE 05-pres. UCSD Full Professor and Fratamico Endowed Chair in the CSE Department; Adjunct Professor in ECE, 08-pres Executive board member of San Diego Supercomputing Center • leading a diverse research team on projects related to system energy-efficiency: o management and optimization of computing systems . $40M JUMP CRISP center focusing on accelerating machine learning workloads . head of the Large Scale Systems thrust in MuSyC center; faculty from 11 top USA universities . 10 year NSF ERC CIAN; lead of thrust on energy efficient datacenters; 30 companies, 12 universities . funded by NSF, DARPA via MARCO-GSRC & FCRP MuSyC, Oracle, CNS, Google, Microsoft, TI, SRC, Cisco, Qualcomm, CEC, Futurewei, Panasonic, Ericson, Broadcom, Intel, IBM. in collaboration with: Google, HP Labs, Oracle, Qualcomm, Broadcom, Cisco, Intel, Texas Instruments, IBM Zurich & TJ Watson, Microsoft, Yahoo, EPFL, ETH, IBM, SDSC, Futurewei, NVidia, AMD. o resource management and design of heterogeneous wireless sensor-control-actuator networks . director of $16.3M AI for Healthy Living Center, with faculty from School of Engineering, School of Social Sciences, School of Medicine, Contextual Robotics Institute, Center for Healthy Aging, Center for Microbiome Innovation, Qualcomm Institute & Design Lab . $28M TerraSwarm center; 22 faculty from 10 top institutions in the USA; leading the SmartCities theme . led context-aware distributed optimization thrust as a part of ARPA-E NODES grant . NSF MetaSense project focused on in-field calibration & NSF CitiSense project focused on mobile air quality sensing; coverage in NY Times and the Wall Street Journal, December 2012 . -
Hacking the Xbox: an Introduction to Reverse Engineering
(Pdf free) Hacking the Xbox: An Introduction to Reverse Engineering Hacking the Xbox: An Introduction to Reverse Engineering Von Andrew Huang ePub | *DOC | audiobook | ebooks | Download PDF Produktinformation -Verkaufsrang: #906459 in BcherVerffentlicht am: 2003-08-01Anzahl der Produkte: 1Abmessungen: 9.04 x .84b x 6.06l, 1.04 Pfund Einband: Taschenbuch273 Seiten | File size: 43.Mb Von Andrew Huang : Hacking the Xbox: An Introduction to Reverse Engineering before purchasing it in order to gage whether or not it would be worth my time, and all praised Hacking the Xbox: An Introduction to Reverse Engineering: KundenrezensionenHilfreichste Kundenrezensionen12 von 18 Kunden fanden die folgende Rezension hilfreich. XBOX unter die Haube guckenVon Ein Kunde"Hacking the XBOX" ist das Werk von Andrew "Bunnie" Huang,einem Doktoranden am hoch anerkannten Massachusetts Institute of Technology(MIT) der sich neben seiner Doktor-Arbeit mit der Microsoft Konsole und deren Sicherheitsmechanismen bzw. Schwachstellen beschftigt hat.Der Inhalt erstreckt sich von der Aufklrung des Garantieverlustesber das bauen eines USB Adapters sowie dem Entwickeln eigener Software fr die XBOX bis zu allgemeinen Debugging/Hacking Tips.An dieser Stelle sei schon einmal erwhnt dass sich das Buch ausschliesslich an Leser mit fundierten elektronischen Vorkenntnissen richtet. Wenn sie ihre 170EUR teures Spielzeug mit einem Ltkolben bearbeiten, sollten Sie wissen was sie tun- Die Ltstellen sind oftmals sehr nah beieinander oder sind an sehr kleinen Pins die bei zu hoher Temperatur -
![Effectively Controls Access to a Work Protected [By Copyright].” 17 U.S.C](https://docslib.b-cdn.net/cover/2848/effectively-controls-access-to-a-work-protected-by-copyright-17-u-s-c-9182848.webp)
Effectively Controls Access to a Work Protected [By Copyright].” 17 U.S.C
Case 1:16-cv-01492-EGS Document 18 Filed 10/18/16 Page 1 of 54 UNITED STATES DISTRICT COURT DISTRICT OF COLUMBIA Matthew Green, Andrew Huang, and Alphamax, LLC, Plaintiffs, Civil Case No.: 1:16-cv-01492-EGS v. Hon. Emmet G. Sullivan U.S. Department of Justice, Loretta Lynch, Hearing Requested Library of Congress, U.S. Copyright Office, and Maria Pallante, Defendants. PLAINTIFFS’ OPPOSITION TO MOTION TO DISMISS Brian M. Willen (D.C. BN 490471) Corynne McSherry (CA SBN 221504) WILSON SONSINI Kit Walsh (CA SBN 303598) GOODRICH & ROSATI, P.C. Adam Schwartz (CA SBN 309491) 1301 Avenue of the Americas 40th Floor ELECTRONIC FRONTIER New York, NY 10019 FOUNDATION Tel. (212) 999-5800 815 Eddy Street San Francisco, CA 94109 Tel. (415) 436-9333 Stephen Gikow (CA SBN 302484) Lauren Gallo White (CA SBN 309075) WILSON SONSINI GOODRICH & ROSATI, P.C. One Market Plaza Spear Tower, Suite 3300 San Francisco, CA 94105 Tel. (415) 947-2000 Counsel for Plaintiffs Matthew Green, Andrew Huang, and Alphamax, LLC Case 1:16-cv-01492-EGS Document 18 Filed 10/18/16 Page 2 of 54 TABLE OF CONTENTS Page INTRODUCTION .......................................................................................................................... 1 BACKGROUND ............................................................................................................................ 3 A. Section 1201’s Anti-Circumvention and Anti-Trafficking Provisions................... 3 B. Plaintiff Matthew Green ........................................................................................ -
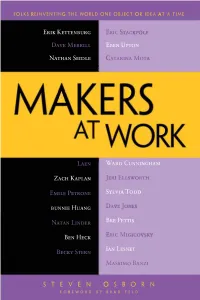
Makers at Work 3
For your convenience Apress has placed some of the front matter material after the index. Please use the Bookmarks and Contents at a Glance links to access them. Contents Foreword vii About the Author xi Acknowledgments ����������������������������������������������������������������������������������������xiii Introduction ���������������������������������������������������������������������������������������������������xv Chapter 1: Erik Kettenburg, Founder, Digistump ������������������������������������������������ 1 Chapter 2: David Merrill, Cofounder, Sifteo ������������������������������������������������������ 21 Chapter 3: Nathan Seidle, CEO, SparkFun Electronics �����������������������������������������37 Chapter 4: Laen, Founder, OSH Park 51 Chapter 5: Zach Kaplan, Founder and CEO, Inventables 61 Chapter 6: Emile Petrone, Founder, Tindie ������������������������������������������������������ 71 Chapter 7: bunnie Huang, Founder, bunnie studios ���������������������������������������������83 Chapter 8: Natan Linder, Founder, Formlabs �����������������������������������������������������99 Chapter 9: Ben Heck, Host, The Ben Heck Show �����������������������������������������������115 Chapter 10: Becky Stern, Director of Wearable Electronics, Adafruit Industries �����������127 Chapter 11: Eric Stackpole, Cofounder, OpenROV ���������������������������������������������139 Chapter 12: