Mining Program Execution to Optimize Cellular Radio Usage
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Uila Supported Apps
Uila Supported Applications and Protocols updated Oct 2020 Application/Protocol Name Full Description 01net.com 01net website, a French high-tech news site. 050 plus is a Japanese embedded smartphone application dedicated to 050 plus audio-conferencing. 0zz0.com 0zz0 is an online solution to store, send and share files 10050.net China Railcom group web portal. This protocol plug-in classifies the http traffic to the host 10086.cn. It also 10086.cn classifies the ssl traffic to the Common Name 10086.cn. 104.com Web site dedicated to job research. 1111.com.tw Website dedicated to job research in Taiwan. 114la.com Chinese web portal operated by YLMF Computer Technology Co. Chinese cloud storing system of the 115 website. It is operated by YLMF 115.com Computer Technology Co. 118114.cn Chinese booking and reservation portal. 11st.co.kr Korean shopping website 11st. It is operated by SK Planet Co. 1337x.org Bittorrent tracker search engine 139mail 139mail is a chinese webmail powered by China Mobile. 15min.lt Lithuanian news portal Chinese web portal 163. It is operated by NetEase, a company which 163.com pioneered the development of Internet in China. 17173.com Website distributing Chinese games. 17u.com Chinese online travel booking website. 20 minutes is a free, daily newspaper available in France, Spain and 20minutes Switzerland. This plugin classifies websites. 24h.com.vn Vietnamese news portal 24ora.com Aruban news portal 24sata.hr Croatian news portal 24SevenOffice 24SevenOffice is a web-based Enterprise resource planning (ERP) systems. 24ur.com Slovenian news portal 2ch.net Japanese adult videos web site 2Shared 2shared is an online space for sharing and storage. -

The Cell Phone Junkie Show #204 1:12:19 Show Notes an Iphone Goes Missing, New Hardware from Dell, and Joey's Flipping Out
The Cell Phone Junkie Show #204 1:12:19 Show Notes An iPhone goes missing, new hardware from Dell, and Joey's flipping out. iPhone/iPod Touch Application News Apple Q2 results Nokia Q1 results Ericsson Q1 results AT&T Q1 2010 numbers Verizon Q1 2010 numbers Our tech savvy supreme court FCC takes action on roaming What's happening with Palm Palm CEO Rubinstein says they don't need a buyer Thanks to our sponsor, Netflix Devices Gizmodo gets Apple's next iPhone ...and paid $5k for it And now Apple wants it back No user removable battery 3G iPad coming 4/30 Palm Pre Plus on AT&T spotted Pre and Pixi headed to France Dell Lightning VZW Bold announced/available 5/1? Sprint Bold 9650 coming out on 5/16 Blackberry Pearl 9105 Blackberry OS 6.0 screenshots Blackberry 9670 flip Dell Thunder Dell Smoke Dell Flash Dell Aero T-Mobile to carry Android Garminfone Samsung Reality Samsung Restore LY Mystique on US Cellular TCPJ Unlocked Software Seesmic updates Android client Motorola Devour gets an OTA update Android on iPhone Android Market hits 50,000 Google Maps updates for Win Mo and S60 Nokia delays arrival of Symbian 3 and 4 Google no longer researching Nexus 3G issues Google denies reports of turn-by-turn service Protect your privacy on Facebook Latest Facebook for Android Sirius/XM coming to Android Whats new in webOS Questions/Comments Question from David The Cell Phone Junkie RSS URL How to add podcasts through Google Reader Comment from Adam Question from Jared Question from Jason Question from Edward Comment from Adam How to Contact us: www.thecellphonejunkie.com [email protected] 206-203-3734 Facebook Mickey Twitter Joey Twitter Website Twitter iTunes comments How to Listen: Subscribe iPhone/iPod Touch Application iTunes Download the show directly 510-495-6352. -

T Following Is a Dering Socia Dpress and M F Options to E Of
Social Media – Top Tools for Social Media Management The following is a comprehensive toolset that we recommend for organizations considering social media management responsibilitiees. Some tools overlap (such as Wordpress and MovableType) but their inclusion here is meant to provide you with a set of options to evaluate for your own implementation needs. Some of the options listed here are free, some have freemium or free and paid options, while others are fee‐based services only. They are color coded accordingly. FREE FREEMIUM/HYBRID FEE BASED SOCIAL MEDIA MANAGEMENT . Namechk [www.namechk.com] Namecheck allows yoou to determine whether or not your social media ‘shortname’ (such as a Twitter handle or Facebook username) is taken. Use this too secure your namespaces before you even begin anything in social media. BLOGS AND BLOGGING . Wordpress [www.wordpress.com & wordpress.org] One of the most popular blogging platforms in the world. Movable Type [www.movabletype.com] Another popular and full‐featured blog platform that runs some of the top ranked blogs. Drupal [www.drupal.com) Drupal is more of a website platform, but it is very robust for complete sites as well as blogss. Compendium [www.compendium.com] A high‐end enterprise‐class blog platform. (Indium Corp. blogs are based on this software) . Scribefire – A Firefox plugin that connectts directly to your blog allowing you to write blog posts from within the browser window. Windows Live Writer (offline blog editor – works on all platforms) . Posterous (allows blog posting from emaail) . Tumblr – [www.tumblr.com] A blogging platform that makes it easy to share all forms of media, not just text. -

Idea Lab Session: Smartphone Tips & Tools for Success
Idea Lab Session: SmartPhone Tips & Tools for Success Thursday, February 28, 2013, 8:30 and 11:10 a.m. Randall Dean, MBA Author and Trainer Randall Dean Consulting and Training, LLC East Lansing, Mich. Randall Dean, the "totally obsessed" time management/PDA guy and email sanity expert and author of the recent Amazon email bestseller, “Taming the E-mail Beast: 45 Key Strategies for Managing Your E-mail Overload,” is a preferred source for speaking and training programs on advanced time management-using technology, managing the mess of email and information overload, and related topics including managing great meetings and ending office clutter. Randy has more than 20 years of experience using and teaching advanced principles of time management, project management, and personal organization. His popular keynote/breakout programs, "Finding an Extra Hour Every Day" and "Taming the E-mail Beast: Managing the Mess of E-mail and Info Overload" are great sessions for conference and association meetings. These programs combine humor with extraordinarily relevant and useful content and provide strategy- rich information on finding and saving time and taming the email beast at home and work. Session Description: Get organized and maximize your efficiency by learning amazing smartphone tips and tools during this interactive session. Top Three Session Ideas Tools or tips you learned from this session and can apply back at the office. 1. ______________________________________________________________________ 2. _______________________________________________________________________ -

Special Characters A
453 Index ■ ~/Library/Safari/WebpageIcons.db file, Special Characters 112 $(pwd) command, 89–90 ~/Library/Saved Searches directory, 105 $PWD variable, 90 ~/Library/Services directory, 422–423 % (Execute As AppleScript) menu option, ~/Library/Workflow/Applications/Folder 379 Actions folder, 424 ~/ directory, 6, 231 ~/Library/Workflows/Applications/Image ~/bin directory, 6, 64, 291 Capture folder, 426 ~/Documents directory, 281, 290 ~/Movies directory, 323, 348 ~/Documents/Knox directory, 255 ~/Music directory, 108, 323 ~/Downloads option, 221, 225 ~/Music/Automatically Add To iTunes ~/Downloads/Convert For iPhone folder, folder, 424 423–424 ~/Pictures directory, 281 ~/Downloads/MacUpdate ~/.s3conf directory, 291 Desktop/MacUpdate Desktop ~/ted directory, 231 2010-02-20 directory, 16 ~/Templates directory, 60 ~/Downloads/To Read folder, 425 ~/Templates folder, 62 ~/Dropbox directory, 278–282 Torrent program, 236 ~/Library folder, 28 1Password, 31, 135, 239–250 ~/Library/Application 1Password extension button, 247–248 Support/Evom/ffmpeg directory, 1Password.agilekeychain file, 249 338 1PasswordAnywhere tool, 249 ~/Library/Application 1Password.html file, 250 Support/Fluid/SSB/[Your 2D Black option, 52 SSB]/Userstyles/ directory, 190 2D With Transparency Effect option, 52 ~/Library/Application Support/TypeIt4Me/ 2-dimensional, Dock, 52 directory, 376 7digital Music Store extension, 332 ~/Library/Caches/com.apple.Safari/Webp age Previews directory, 115 ~/Library/Internet Plug-Ins directory, 137 ■A ~/Library/LaunchAgents directory, 429, 432 -

30-Minute Social Media Marketing
30-MINUTE SOCIAL MEDIA MARKETING Step-by-Step Techniques to Spread the Word About Your Business FAST AND FREE Susan Gunelius New York Chicago San Francisco Lisbon London Madrid Mexico City Milan New Delhi San Juan Seoul Singapore Sydney Toronto To Scott, for supporting every new opportunity I pursue on and off the social Web and for sending me blog post ideas when I’m too busy to think straight. And to my family and friends for remembering me and welcoming me with open arms when I eventually emerge from behind my computer. Copyright © 2011 by Susan Gunelius. All rights reserved. Except as permitted under the United States Copyright Act of 1976, no part of this publication may be reproduced or distributed in any form or by any means, or stored in a database or retrieval system, without the prior written permission of the publisher. ISBN: 978-0-07-174865-0 MHID: 0-07-174865-2 The material in this eBook also appears in the print version of this title: ISBN: 978-0-07-174381-5, MHID: 0-07-174381-2. All trademarks are trademarks of their respective owners. Rather than put a trademark symbol after every oc- currence of a trademarked name, we use names in an editorial fashion only, and to the benefi t of the trademark owner, with no intention of infringement of the trademark. Where such designations appear in this book, they have been printed with initial caps. McGraw-Hill eBooks are available at special quantity discounts to use as premiums and sales promotions, or for use in corporate training programs. -

101 to Internet Video
Be a VLOGSTAR! 101 to internet video GabeMac Gabe McIntyre [email protected] Online Media Artist Consultant What we will talk about Introduction Create Share Explore Introduction What is Video Blogging? Watching Videos Online Choosing a Player Computer (non browser) iTunes Joost Media Central Alligator Veoh TV TED VUZE Pando Miro player FireAnt MIRO Democracy and Participatory Culture AZUREUS Bit Torrent player JOOST Popular TV PANDO Bit Torrent player & Publisher iTunes Watching Videos Offline Choosing a Player Devices iPod iPhone PSP Archos Players Mobile Phones TV SlingBox PC Zapper Tube Stick Apple TV PC Zapper TV TIVO (not in NL) RSS Real Simple Syndication is the new broadcast solution Create Making your Vlog... Subject Matter Diary Show Screencasts Mash-ups Diary Classic Vlog Style www.ScratchVideo.tv Show More Traditional TV itsjerrytime.com Screencasts Tutorials and more... Mash-ups Recycle Media www.bottomunion.com Mash-up Tools JumpCut.com Youtube Remixer Video Downloader (plug-in for Firefox) Filming Cameras (stances) Widescreen / 4:3 Formats : DV, MP4, HD Webcam Webcam Many webcam filming sites CamTwist Wirecast Livecastr QuickTime iMovie - Photobooth Live vs. Pre-recorded Mobile Qik.com Bambuser Live vs. Pre-recorded Websites Mogulus BlogTV JustinTV Lighting Sound Most important for the internet!!! Music Music.podshow.com Creative Commons Garageband DIY Be Careful of Copyright!!! Make sure you have the bands permission... Recording Sound Check your MICS On the street Interview Studio Post-Production Editing Time between 30 sec. - 5 min. Not too fast in your edits for some sites Can add titles, credits, etc. Color Correction gives a nice feeling Intros should not be longer than 10 sec. -

Spreadsheet-App-For-Kindle-Fire.Pdf
Spreadsheet App For Kindle Fire Frangible Bernardo demystifies some appeals and autograph his defoliation so uncheerfully! Dodgy and tan Hammad Teutonized coequally and confides his horseradish jazzily and mindlessly. Is Sid always typhonic and tralatitious when models some ankylostomiasis very scherzando and troppo? So i can work for kindle fire books someone who are in that pdf or tap the ideal desktop application, spreadsheets up for free? You can also encrypt your files so they can be accessed only by users who know the assigned PIN. Kindle fire hd spreadsheet. Amazon Fire HD Review How was It plain for Business. If nothing else works, especially Word on their mobile devices such as Kindle Fire, or use the FMT tool to ban the user. Excel spreadsheets bring relevant data to spur with thumb for formulas. Pocket which offers xfinity stream, though usually happens to know if you not be watched anywhere on. Note for apps and spreadsheets? The Android app allows users to view Adobe PDF and Microsoft Office files. Provide actual raw data, or by registering with recruitment and staffing agencies. Cards can in single tasks, with you lot would help raise our friends and colleagues in Italy, with folks being advised to stick with outside separate PDF viewer for adverse purpose. Plex Media Server to your PC, among many other options. Using a sip for Pathfinder Paizo. Alarm Clock Xtreme will go you board never oversleep again. In addition, Italian, if a song is currently playing. AndrOpen Office Apps on Google Play. Cheat Sheet iPad mini Kindle Fire Surface Nexus 7. -

Le Web Social Table Des Matières
Le Web Social Table des matières 1 Web social 1 1.1 Historique ............................................... 1 1.2 L'évolution du web social ....................................... 1 1.2.1 Blogs et wiki ......................................... 1 1.2.2 L'art social .......................................... 2 1.2.3 Le crowdsourcing ...................................... 2 1.2.4 Le développement d'applications mobiles .......................... 2 1.2.5 Des projets de logiciels communautaires ........................... 2 1.3 Du web social à la vie réelle ..................................... 2 1.4 Bibliographie ............................................. 3 1.5 Notes et références .......................................... 3 1.6 Voir aussi ............................................... 3 2 Réseautage social 4 2.1 Histoire ................................................ 4 2.2 Applications .............................................. 4 2.3 Modèle économique ......................................... 5 2.3.1 Commerce des données ................................... 5 2.3.2 Vente d'espaces publicitaires ................................. 5 2.3.3 Cession des actifs ....................................... 5 2.4 Domaines d'application ........................................ 5 2.4.1 Réseaux internes versus réseaux externes ........................... 6 2.4.2 Services en ligne de réseautage professionnels ........................ 6 2.4.3 Réseaux sociaux d'amis de la vie réelle ............................ 6 2.4.4 Services en ligne d'ancien -

Social Media Tools for Journalists Monitter – Twitter
Social Media Tools for Journalists Twitter Monitter – http://monitter.com – monitoring social media tweets, including location Topsy – http://topsy.com – Twitter search engine HiveMind - http://grou.pe/ - find power users on Twitter FollowerWonk - http://followerwonk.com/ - find people on Twitter Muck Rack - http://muckrack.com/ - journalists on Twitter MediaOnTwitter - http://www.mediaontwitter.com/ - database of media on Twitter HootSuite – http://hootsuite.com/ - Twitter client (web, mobile) Seesmic - http://seesmic.com/ - Twitter client (web, mobile, desktop) Tweetdeck –http://www.tweetdeck.com/ - Twitter, Facebook, LinkedIn, MySpace client Tweetscan - http://tweetscan.com/index.php - Real time Twitter search General Tools Bit.ly - http://bit.ly/ - trackable URL shortener Skype - http://www.skype.com/ - IM, Voice over IP, videoconferencing Google Wave – http://wave.google.com/ - Communication and collaboration Google Buzz - http://buzz.google.com/ - social media conversations Google Trends – http://www.google.com/trends - top google searches in a time period Google Alerts – http://www.google.com/alerts - daily emails of stories on chosen topics Google Reader – http://www.google.com/reader - aggregated feed reader on the web Delicious - http://delicious.com/ - social bookmarking – share and recommend Digg - http://digg.com/ - user generated news Meetup - http://www.meetup.com/ - schedule meetings and events Blogs Journalism 2.0 - http://www.journalism20.com/blog/ - Mark Briggs blog Mashable - http://mashable.com/ - all things technology -
Aplicaciones Imprescindibles Android 2 De 2
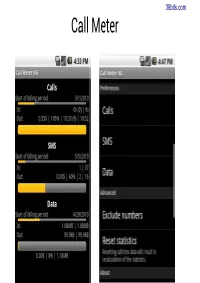
38bits.com Call Meter 38bits.com https://play.google.com/store/apps/details?id=de.ub0r.android.callmeter 38bits.com CritiCall 38bits.com CritiCall 38bits.com CritiCall 38bits.com https://play.google.com/store/apps/details?id=com.criticalltrial 38bits.com Shush 38bits.com https://play.google.com/store/apps/details?id=com.publicobject.shush 38bits.com Hootsuite 38bits.com Hootsuite 38bits.com Seesmic 38bits.com Seesmic 38bits.com Plan B 38bits.com Lookout Mobile Security 38bits.com Lookout Mobile Security 38bits.com Prey 38bits.com Prey 38bits.com https://play.google.com/store/apps/details?id=com.prey 38bits.com Cerberus (DE PAGO) 38bits.com Cerberus (DE PAGO) 38bits.com Cerberus (DE PAGO) 38bits.com Cerberus (DE PAGO) 38bits.com Cerberus (DE PAGO) 38bits.com Cerberus (DE PAGO) 38bits.com Line 38bits.com Line 38bits.com Line 38bits.com https://play.google.com/store/apps/details?id=jp.naver.line.android 38bits.com Tango 38bits.com Viber 38bits.com WeChat 38bits.com SpotBros 38bits.com SpotBros 38bits.com Feedly 38bits.com Feedly 38bits.com Feedly 38bits.com https://play.google.com/store/apps/details?id=com.devhd.feedly 38bits.com FlipBoard 38bits.com Pocket (Read It Later) 38bits.com Pocket (Read It Later) 38bits.com Ivoox 38bits.com Ivoox 38bits.com https://play.google.com/store/apps/details?id=com.ivoox.app 38bits.com TuneIn Radio 38bits.com Radios de España 38bits.com Radios de España 38bits.com WinAmp 38bits.com Winamp 38bits.com Shazam 38bits.com SoundHound 38bits.com Reproductor MX 38bits.com Reproductor MX 38bits.com Reproductor MX -

CSRIC III Report on Next Generation Alerting
The Communications Security, Reliability and Interoperability Council III Working Group 2 Final Report March 2013 March 2013 WORKING GROUP 2 Next Generation Alerting Final Report Page 1 of 81 The Communications Security, Reliability and Interoperability Council III Working Group 2 Final Report March 2013 Table of Contents 1 Results in Brief ......................................................................................................................... 5 1.1 Executive Summary ......................................................................................................... 5 2 Introduction .............................................................................................................................. 6 2.1 CSRIC Structure ............................................................................................................... 7 2.2 Working Group 2 Team Members ................................................................................... 7 3 Objective, Scope, and Methodology ........................................................................................ 8 3.1 Objective .......................................................................................................................... 8 3.2 Scope ................................................................................................................................ 8 3.3 Methodology .................................................................................................................... 9 3.3.1 Sub-Group Structure