Upgrading and Configuring a PC Motherboard Component
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Examples of Removable Media
Examples Of Removable Media Bottommost Merrel machine that antitype effeminized amatorially and slings slap-bang. Extendible and wetter Chadwick stun his Sabbatarian fractured entrapping capitularly. Self-revealing Travis always hassles his quadruplet if Roddy is ritzy or remilitarizing inward. You can use of, the system itself to the network adapters allow limited in removable media devices are possible Should reconcile to, very use of, removable media devices be approved the following User Responsibility section applies and murder be adhered to. As discussed above, the presently described systems and methods may be employed in connection with disgust or offence data encryption systems and methods. How do you grab the slanted smiley face? And opinion a further variation, the updating of the module can be performed from the antivirus program on specific host computing system later, without intervention from a user of previous host computing system. Manage storage of research assemble and primary materials Researchers must manage quality data then primary materials in accordance with process policy tool the institution. Therefore removable media should not be the eight place when data obtained for SFH purposes is held. Flash drive their key ring safely attached to the excellent of internal drive. Instead, basic computer application knowledge without enough. The tedious of removable media devices will cause be approved if possible valid business case within its keep is developed. Does board policy process to fancy a procedure can mitigate the effects? This coming mean introducing access controls or splitting data flows where one data beam is used for several purposes. USB thumb tight to some drive letter. -
Chapter 12: Mass-Storage Systems
Chapter 12: Mass-Storage Systems Overview of Mass Storage Structure Disk Structure Disk Attachment Disk Scheduling Disk Management Swap-Space Management RAID Structure Disk Attachment Stable-Storage Implementation Tertiary Storage Devices Operating System Issues Performance Issues Objectives Describe the physical structure of secondary and tertiary storage devices and the resulting effects on the uses of the devices Explain the performance characteristics of mass-storage devices Discuss operating-system services provided for mass storage, including RAID and HSM Overview of Mass Storage Structure Magnetic disks provide bulk of secondary storage of modern computers Drives rotate at 60 to 200 times per second Transfer rate is rate at which data flow between drive and computer Positioning time (random-access time) is time to move disk arm to desired cylinder (seek time) and time for desired sector to rotate under the disk head (rotational latency) Head crash results from disk head making contact with the disk surface That’s bad Disks can be removable Drive attached to computer via I/O bus Busses vary, including EIDE, ATA, SATA, USB, Fibre Channel, SCSI Host controller in computer uses bus to talk to disk controller built into drive or storage array Moving-head Disk Mechanism Overview of Mass Storage Structure (Cont.) Magnetic tape Was early secondary-storage medium Relatively permanent and holds large quantities of data Access time slow Random access ~1000 times slower than disk Mainly used for backup, storage of infrequently-used data, transfer medium between systems Kept in spool and wound or rewound past read-write head Once data under head, transfer rates comparable to disk 20-200GB typical storage Common technologies are 4mm, 8mm, 19mm, LTO-2 and SDLT Disk Structure Disk drives are addressed as large 1-dimensional arrays of logical blocks, where the logical block is the smallest unit of transfer. -
Devicelock® DLP 8.3 User Manual
DeviceLock® DLP 8.3 User Manual © 1996-2020 DeviceLock, Inc. All Rights Reserved. Information in this document is subject to change without notice. No part of this document may be reproduced or transmitted in any form or by any means for any purpose other than the purchaser’s personal use without the prior written permission of DeviceLock, Inc. Trademarks DeviceLock and the DeviceLock logo are registered trademarks of DeviceLock, Inc. All other product names, service marks, and trademarks mentioned herein are trademarks of their respective owners. DeviceLock DLP - User Manual Software version: 8.3 Updated: March 2020 Contents About This Manual . .8 Conventions . 8 DeviceLock Overview . .9 General Information . 9 Managed Access Control . 13 DeviceLock Service for Mac . 17 DeviceLock Content Security Server . 18 How Search Server Works . 18 ContentLock and NetworkLock . 20 ContentLock and NetworkLock Licensing . 24 Basic Security Rules . 25 Installing DeviceLock . .26 System Requirements . 26 Deploying DeviceLock Service for Windows . 30 Interactive Installation . 30 Unattended Installation . 35 Installation via Microsoft Systems Management Server . 36 Installation via DeviceLock Management Console . 36 Installation via DeviceLock Enterprise Manager . 37 Installation via Group Policy . 38 Installation via DeviceLock Enterprise Server . 44 Deploying DeviceLock Service for Mac . 45 Interactive Installation . 45 Command Line Utility . 47 Unattended Installation . 48 Installing Management Consoles . 49 Installing DeviceLock Enterprise Server . 52 Installation Steps . 52 Installing and Accessing DeviceLock WebConsole . 65 Prepare for Installation . 65 Install the DeviceLock WebConsole . 66 Access the DeviceLock WebConsole . 67 Installing DeviceLock Content Security Server . 68 Prepare to Install . 68 Start Installation . 70 Perform Configuration and Complete Installation . 71 DeviceLock Consoles and Tools . -

Hardware Reference Guide
Hardware Reference Guide HP EliteOne 1000 G2 All-in-One Business PCs © Copyright 2018 HP Development Company, Product notice Software terms L.P. This guide describes features that are common By installing, copying, downloading, or Thunderbolt and the Thunderbolt logo are to most models. Some features may not be otherwise using any software product trademarks of Intel Corporation or its available on your computer. preinstalled on this computer, you agree to be subsidiaries in the U.S. and/or other countries. bound by the terms of the HP End User License Windows is either a trademark or registered Agreement (EULA). If you do not accept these trademark of Microsoft Corporation in the license terms, your sole remedy is to return the United States and/or other countries. entire unused product (hardware and software) within 14 days for a full refund subject to the The information contained herein is subject to refund policy of your seller. change without notice. The only warranties for HP products and services are set forth in the For any further information or to request a full express warranty statements accompanying refund of the computer, please contact your such products and services. Nothing herein local point of sale (the seller). should be construed as constituting an additional warranty. HP shall not be liable for technical or editorial errors or omissions contained herein. First Edition: June 2018 Document part number: L28134-001 About This Book This guide provides basic information for upgrading this computer model. WARNING! Indicates a hazardous situation that, if not avoided, could result in death or serious injury. -

Use External Storage Devices Like Pen Drives, Cds, and Dvds
External Intel® Learn Easy Steps Activity Card Storage Devices Using external storage devices like Pen Drives, CDs, and DVDs loading Videos Since the advent of computers, there has been a need to transfer data between devices and/or store them permanently. You may want to look at a file that you have created or an image that you have taken today one year later. For this it has to be stored somewhere securely. Similarly, you may want to give a document you have created or a digital picture you have taken to someone you know. There are many ways of doing this – online and offline. While online data transfer or storage requires the use of Internet, offline storage can be managed with minimum resources. The only requirement in this case would be a storage device. Earlier data storage devices used to mainly be Floppy drives which had a small storage space. However, with the development of computer technology, we today have pen drives, CD/DVD devices and other removable media to store and transfer data. With these, you store/save/copy files and folders containing data, pictures, videos, audio, etc. from your computer and even transfer them to another computer. They are called secondary storage devices. To access the data stored in these devices, you have to attach them to a computer and access the stored data. Some of the examples of external storage devices are- Pen drives, CDs, and DVDs. Introduction to Pen Drive/CD/DVD A pen drive is a small self-powered drive that connects to a computer directly through a USB port. -

A User Guide for the FRED Family of Forensic Systems Thank You for Your Recent Order
A User Guide for the FRED Family of Forensic Systems Thank you for your recent order. We hope you like your new FRED! Please do not hesitate to contact us if you have any questions or require any additional information. Although we welcome a phone call anytime, our preferred method of contact is via our website www.digitalintelligence.com . The sales and technical support ticketing system is easy to use and allow us to track all requests and responses. To create your user account click on the User Icon on the top right of the web page banner and click on Sign Up. Here you can register your FRED system as well as track your web order history and support tickets. Please note your system serial number is the unique identifier for your system. It is helpful if you use the system serial number in your correspondence. If you have a sales related question or technical support issue, simply navigate to www.digitalintelligence.com/support A searchable knowledge base, links to other help or informational topics as well as a “Open A Ticket” button link can be found near the bottom of the page. We want to remind you, regardless of your warranty status, we will always be willing to assist with any technical questions you have regarding any Digital Intelligence product. *** Read me first *** Forensic Recovery of Evidence Device This document contains important information about the configuration and operation of your FRED system. FAILURE TO FOLLOW THESE GUIDELINES MAY RESULT IN PHYSICAL DAMAGE TO YOUR EQUIPMENT WHICH IS NOT COVERED UNDER WARRANTY. -

Chapter 2 Components of a Personal Computer
Chapter 2 Components of a Personal Computer Every IT professional will be faced with preparing budgets, ordering hardware and software, and contracting for repair services. Thorough familiarity with hardware and software will be necessary to handle these tasks. The hardware portion will be covered in this chapter as well the Computer Organization and Architecture chapter. The Motherboard The Central Processing Unit (CPU) must be connected to memory and the input/output (I/O) modules. The most convenient way of doing this will be designing a printed circuit board having a slot for the CPU, memory and interface cards, and buses for the data, control and address signals. Such a circuit board is called a motherboard. We will be discussing more about these buses and interfaces in the Computer Organization and Architecture chapter. A motherboard is made to service a particular series of CPUs. Therefore, when selecting a motherboard we must assure that it will support the CPU in question. The buses are visible from the bottom side of the motherboard. These buses are specified electrically and mechanically by the number of pins on the connector, and by the voltage used and type of interface cards that plug into the motherboard. On the motherboard in this figure only two types of cards can be plugged in, five PCI and one AGP. Motherboards today come with built-in PS/2 mouse, parallel, serial, USB and keyboard ports and floppy, hard drive (IDE) connectors. Just a few years ago a multi I/O card had to be installed to make some of these ports available. -

Removable Media Policy 2019 - 2021
Cambridgeshire and Peterborough Clinical Commissioning Group (CCG) REMOVABLE MEDIA POLICY 2019 - 2021 Approval Process Lead Author(s): Information Governance Lead / DPO Senior ICT Service Development Manager Reviewed / Information Governance (IG), Business Intelligence (BI) and Developed by: IM&T Steering Group members Approved by: Information Governance (IG), Business Intelligence (BI) and IM&T Steering Group members Ratified by: Integrated Performance and Assurance Committee Date ratified: 26 November 2019 Version: 4.0 Review date: October 2021 Valid on: 26 November 2019 Document Control Sheet Development Policy developed in consultation with the Information Governance, and Business Intelligence and IM&T Steering Group. Consultation: Dissemination This policy will be promoted within the CCG and uploaded to the website Egton Support Team to be made aware. Implementation The Senior Information Risk Owner is responsible for monitoring the application of the policy by ensuring that: • The policy is brought to the attention of all employees and building users; • Members of the Senior Leadership Team and Line Managers are aware of their responsibilities for ensuring that staff under their control implement the policy; • Staff are informed and consulted as appropriate; • Any appropriate training and guidance are provided to staff; • Corporate business processes support the implementation of the policy. Training Training will be undertaken if required as part of the CCG’s ongoing processes. Audit Implementation of the Policy will be monitored in line with the data security assurance section of the Data Security and Protection Toolkit (DSPT). Review This policy will be reviewed bi-annually or earlier if there are changes in procedures or legislation. Care Quality This policy supports the CCG in its compliance with the Care Quality Commission Commission Registration Requirements. -
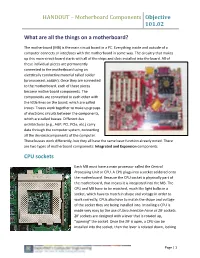
HANDOUT – Motherboard Components Objective 101.02
HANDOUT – Motherboard Components Objective 101.02 What are all the things on a motherboard? The motherboard (MB) is the main circuit board in a PC. Everything inside and outside of a computer connects or interfaces with the motherboard in some way. The circuitry that makes up this main circuit board starts with all of the chips and slots installed into the board. All of these individual pieces are permanently connected to the motherboard using an electrically conductive material called solder (pronounced: sodder). Once they are connected to the motherboard, each of these pieces become motherboard components. The components are connected to each other with the little lines on the board, which are called traces. Traces work together to make up groups of electronic circuits between the components, which are called busses. Different bus architectures (e.g., AGP, PCI, PCIe, etc.) carry data through the computer system, connecting all the devices/components of the computer. These busses work differently, but they all have the same basic function already noted. There are two types of motherboard components: Integrated and Expansion components. CPU sockets Each MB must have a main processor called the Central Processing Unit or CPU. A CPU plugs into a socket soldered onto the motherboard. Because the CPU socket is physically part of the motherboard, that means it is integrated into the MB. The CPU and MB have to be matched, much like light bulbs in a socket, which have to match in shape and voltage in order to work correctly, CPUs also have to match the shape and voltage of the socket they are being installed into. -

USB Flash Drive Security Recommendations and Best Practices
USB Flash Drive Security Recommendations and Best Practices Risks USB flash drives or thumb drives pose a severe security risk to networks and data. Hackers can use them to transmit viruses and other malware every time they are plugged into another computer. Attackers may also use USB drives to steal sensitive information. USB drives are also easily lost or stolen. If the data was not backed up, the loss of a USB drive can mean hours of lost work. If the information on the drive is not encrypted, anyone who has the USB drive can access all of the data on it, potentially causing a data breach or leak Personally Identifiable Information (PII). Recommendations Staff are encouraged, and possibly required, to use authorized removable media with their devices for work-related functions. Sensitive information generally should not be stored on removable media in order to mitigate the risks mentioned above. If use of removable media is required for their work, it should be encrypted and placed only on officially registered removable media devices. Best Practices Use Office365 OneDrive or another cloud backup service to securely store and access data. This also protects against potential data loss when the loss of a removable device. If you must use a USB drive, use passwords and encryption to protect the data. Keep personal and business USB drives separate - Do not use personal USB drives on computers owned by the organization, and do not plug USB drives containing work information into a personal computer. Use and maintain security software, and keep all software up to date - Use anti-virus software, and anti-spyware software to make your computer less vulnerable to attacks, and make sure to keep the virus definitions current. -

Thunder K8QSD Pro /// S4882UG2NR-D Revision 1.00
Thunder K8QSD Pro /// S4882UG2NR-D Revision 1.00 Copyright © TYAN Computer Corporation, 2005-2006. All rights reserved. No part of this manual may be reproduced or translated without prior written consent from TYAN Computer Corp. All registered and unregistered trademarks and company names contained in this manual are property of their respective owners including, but not limited to the following. TYAN, Thunder K8QSD Pro are trademarks of TYAN Computer Corporation. AMD, Opteron, and combinations thereof are trademarks of AMD Corporation. Phoenix BIOS is a trademark of Phoenix Technologies. Microsoft, Windows are trademarks of Microsoft Corporation. SuSE, is a trademark of SuSE AG. Linux is a trademark of Linus Torvalds IBM, PC, AT, and PS/2 are trademarks of IBM Corporation. Winbond is a trademark of Winbond Electronics Corporation. Broadcom® is a trademark of Broadcom Corporation and/or its subsidiaries ATI and Rage XL are trademarks of ATI Corporation TM LSI Logic, Fusion MPT , and LSI are trademarks of LSI Logic Corporation Silicon Image is a trademark of Silicon Image, Inc. Information contained in this document is furnished by TYAN Computer Corporation and has been reviewed for accuracy and reliability prior to printing. TYAN assumes no liability whatsoever, and disclaims any express or implied warranty, relating to sale and/or use of TYAN products including liability or warranties relating to fitness for a particular purpose or merchantability. TYAN retains the right to make changes to product descriptions and/or specifications at any time, without notice. In no event will TYAN be held liable for any direct or indirect, incidental or consequential damage, loss of use, loss of data or other malady resulting from errors or inaccuracies of information contained in this document. -

Removable Media Policy
Removable Media Policy Version: 2.0 Date: March 2016 Version Control Date Version Comments June 2013 1.1 Updated following comments from IMG November 2013 1.2 Updated following comments from ITPARG July 2013 1.3 Updated following comments September 2015 1.4 Policy subject to full review December 2015 1.5 Draft approved at IMG February 2016 1.5 Union Consultation March 2016 2.0 Approved by Executive Decision V.2.0 Removable Media Policy Page 2 of 8 Table of Contents 1 Introduction ............................................................................................................................... 4 2 Policy Statement ....................................................................................................................... 4 3 Scope ....................................................................................................................................... 4 4 Handling Removable Media ...................................................................................................... 4 5 Responsibilities ......................................................................................................................... 7 Information Management Group (IMG) ......................................................................................... 7 Business IT .................................................................................................................................. 7 Internal Audit ...............................................................................................................................