Der Eigene Email-Server …
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Oldschool E-Mail Setup Eine Freakshow
Oldschool E-mail Setup Eine Freakshow [email protected] Chemnitzer Linuxtage, 2016 (Screenshot GMX vor >15 Jahren: Waybackmachine zu www.gmx.net) (Screenshot GMX heute) (Screenshot Gmail heute) Lösungen? ● Claws ● Mutt ● Eudora ● Netscape Navigator ● Evolution ● Opera M2 ● GMX ● Outlook ● Gnus ● SquirrelMail ● Hotmail ● The Bat! ● Hushmail ● Thunderbird ● KMail ● … Flußgrafik Email Netz MTA MRA MDA MUA MSA MTA Netz Hipster! ● KISS ● YAGNI ● DRY ● NIH ● Divide And Conquer ● Everything is a file ● No vendor lock-in ● Mißtraue Autoritäten – fördere Dezentralisierung Netz Netz Emails Client, den ich Remote verwenden kann Leicht erweiterbar Emails lokal Filter Offenes Format Adressen Netz Netz Abholen Transportformat? Pull Subject 1 Email = 1 File Keine Spuren X-List-ID Mit Hierarchien am Server Beliebige Einfaches Suchen Header Verlässliches Suchen Verarbeitung mit Unix Tools Client, den ich Remote verwenden kann Leicht erweiterbar Emails lokal Filter Offenes Format Adressen Netz Netz Abholen Transportformat? Pull Subject 1 Email = 1 File Keine Spuren X-List-ID Mit Hierarchien am Server Beliebige Einfaches Suchen Header Verlässliches Suchen Verarbeitung mit Unix Tools mbox Maildir mh Client, den ich Remote verwenden kann Leicht erweiterbar Emails lokal Filter Offenes Format Adressen Netz Netz Abholen Transportformat? Pull Subject 1 Email = 1 File Keine Spuren X-List-ID Mit Hierarchien am Server Beliebige Einfaches Suchen Header Verlässliches Suchen Verarbeitung mit Unix Tools mbox Maildir mh tmp 1439306571.1269_0.elvis ~/Post/Technik/Wikitech new 1448267819.5940_0.spencer ... 1457079728.2000_0.spencer:2, cur 1456839383.9873_0.nepomuk:2,SR 1457166567.23654_0.spencer:2,S ... Client, den ich Remote verwenden kann Leicht erweiterbar Filter Adressen Netz Netz Abholen Pull Subject Maildir Keine Spuren X-List-ID am Server Beliebige Header Client, den ich Remote verwenden kann Leicht erweiterbar Filter Adressen Netz Netz Abholen Pull Subject Maildir Keine Spuren X-List-ID am Server Beliebige Header fetchmail getmail mpop .. -

Untersuchung Von Techniken Zur Persönlichen E-Mail-Postfachverschlüsselung
Fachbereich VI - Informatik und Medien Master-Arbeit von Benjamin Fichtner zur Erlangung des akademischen Grades Master of Engineering im Studiengang Technische Informatik - Embedded Systems Untersuchung von Techniken zur persönlichen E-Mail-Postfachverschlüsselung Erstprüfer: Prof. Dr. rer. nat. Thomas Scheffler Gutachter: Prof. Dr. rer. nat. Rüdiger Weis Eingereicht am: 04.03.2019 Kurzfassung E-Mails enthalten häufig sensible und schützenswerte Inhalte, die nicht für Dritte be- stimmt sind. Obwohl die E-Mail ein weit verbreiteter Kommunikationsstandard ist, er- füllt sie viele aktuelle Sicherheitsanforderungen nicht [Foster et al., 2015]. Eines der Probleme ist, dass E-Mail-Inhalte im Klartext auf den Servern des E-Mail-Providers ge- speichert sind. Dort haben berechtigte und unberechtigte Dritte eine dauerhafte Möglich- keit, auf diese zuzugreifen. Um das zu verhindern, wurde die sogenannte persönliche E- Mail-Postfachverschlüsselung entwickelt. Diese neuartige, serverseitige Schutzmaßnah- me speichert eingehende E-Mails verschlüsselt ab. Sie sorgt dafür, dass die verschlüssel- ten E-Mails ausschließlich durch den Nutzer bzw. dessen Passwort entschlüsselt werden können. In dieser Masterarbeit soll untersucht werden, ob der Einsatz von Postfachverschlüs- selungstechniken Auswirkungen auf den E-Mail-Server-Betrieb hat und wie sich die- se darstellen. Hierbei werden die vier Postfachverschlüsselungstechniken GPG-Sieve- Filter, MailCrypt, Scrambler und TREES miteinander verglichen. Dazu werden die ver- schiedenen Techniken analysiert, eine Testumgebung entwickelt, sowie eine Messreihe konzipiert und durchgeführt. Abstract In digital communication, e-mail is an indispensable means of communication. They often contain sensitive and protective content that is not intended for third parties. Alt- hough e-mail is such an important and widespread communication standard, it it does not meet modern security requirements [Foster et al., 2015]. -

22Nd International Congress on Acoustics ICA 2016
Page intentionaly left blank 22nd International Congress on Acoustics ICA 2016 PROCEEDINGS Editors: Federico Miyara Ernesto Accolti Vivian Pasch Nilda Vechiatti X Congreso Iberoamericano de Acústica XIV Congreso Argentino de Acústica XXVI Encontro da Sociedade Brasileira de Acústica 22nd International Congress on Acoustics ICA 2016 : Proceedings / Federico Miyara ... [et al.] ; compilado por Federico Miyara ; Ernesto Accolti. - 1a ed . - Gonnet : Asociación de Acústicos Argentinos, 2016. Libro digital, PDF Archivo Digital: descarga y online ISBN 978-987-24713-6-1 1. Acústica. 2. Acústica Arquitectónica. 3. Electroacústica. I. Miyara, Federico II. Miyara, Federico, comp. III. Accolti, Ernesto, comp. CDD 690.22 ISBN 978-987-24713-6-1 © Asociación de Acústicos Argentinos Hecho el depósito que marca la ley 11.723 Disclaimer: The material, information, results, opinions, and/or views in this publication, as well as the claim for authorship and originality, are the sole responsibility of the respective author(s) of each paper, not the International Commission for Acoustics, the Federación Iberoamaricana de Acústica, the Asociación de Acústicos Argentinos or any of their employees, members, authorities, or editors. Except for the cases in which it is expressly stated, the papers have not been subject to peer review. The editors have attempted to accomplish a uniform presentation for all papers and the authors have been given the opportunity to correct detected formatting non-compliances Hecho en Argentina Made in Argentina Asociación de Acústicos Argentinos, AdAA Camino Centenario y 5006, Gonnet, Buenos Aires, Argentina http://www.adaa.org.ar Proceedings of the 22th International Congress on Acoustics ICA 2016 5-9 September 2016 Catholic University of Argentina, Buenos Aires, Argentina ICA 2016 has been organised by the Ibero-american Federation of Acoustics (FIA) and the Argentinian Acousticians Association (AdAA) on behalf of the International Commission for Acoustics. -
Webfaction User Guide
WebFaction User Guide WebFaction is a service of Paragon Internet Group Limited CONTENTS 1 Introduction 3 1.1 Services..................................................3 1.2 The Complete System..........................................4 2 The Control Panel 5 2.1 Log in to the Control Panel.......................................5 2.2 Change Your Control Panel Password..................................5 2.3 What to Do About a Lost Password...................................6 2.4 Two-Step Login.............................................6 3 Finding Details About Your Server9 3.1 Finding Your Server’s Name.......................................9 3.2 Finding Your Server’s Operating System................................9 3.3 Finding Your Server’s IP Address.................................... 10 4 Accessing Your Data 11 4.1 Connecting with SSH.......................................... 11 4.2 Connecting with FTP........................................... 14 4.3 Changing Your FTP or SSH Password.................................. 14 4.4 Additional Users............................................. 15 4.5 Backups................................................. 16 5 Accounts 17 5.1 Plans and Services............................................ 17 5.2 Communicating with WebFaction.................................... 18 5.3 Payments................................................. 19 5.4 Affiliate Program............................................. 23 5.5 Canceling Your Account......................................... 24 6 Domains 25 6.1 Getting -

The Qmail Handbook by Dave Sill ISBN:1893115402 Apress 2002 (492 Pages)
< Free Open Study > The qmail Handbook by Dave Sill ISBN:1893115402 Apress 2002 (492 pages) This guide begins with a discussion of qmail s history, architecture and features, and then goes into a thorough investigation of the installation and configuration process. Table of Contents The qmail Handbook Introduction Ch apt - Introducing qmail er 1 Ch apt - Installing qmail er 2 Ch apt - Configuring qmail: The Basics er 3 Ch apt - Using qmail er 4 Ch apt - Managing qmail er 5 Ch apt - Troubleshooting qmail er 6 Ch apt - Configuring qmail: Advanced Options er 7 Ch apt - Controlling Junk Mail er 8 Ch apt - Managing Mailing Lists er 9 Ch apt - Serving Mailboxes er 10 Ch apt - Hosting Virtual Domain and Users er 11 Ch apt - Understanding Advanced Topics er 12 Ap pe ndi - How qmail Works x A Ap pe ndi - Related Packages x B Ap pe ndi - How Internet Mail Works x C Ap pe ndi - qmail Features x D Ap pe - Error Messages ndi x E Ap pe - Gotchas ndi x F Index List of Figures List of Tables List of Listings < Free Open Study > < Free Open Study > Back Cover • Provides thorough instruction for installing, configuring, and optimizing qmail • Includes coverage of secure networking, troubleshooting issues, and mailing list administration • Covers what system administrators want to know by concentrating on qmail issues relevant to daily operation • Includes instructions on how to filter spam before it reaches the client The qmail Handbook will guide system and mail administrators of all skill levels through installing, configuring, and maintaining the qmail server. -

R E F E R E N C E G U I
REFERENCE GUIDE Software Version 5.1 Document Version 1 Published March, 2000 Software.com, Inc. www.software.com 525 Anacapa Street 10 Maguire Road, Suite 400 Santa Barbara, CA 93101-1603 Lexington, MA 02421-3130 Tel: (805) 882-2470 Tel: (781) 274-7000 Fax: (805) 882-2473 Fax: (781) 674-1080 The InterMail software is a copyrighted work of Software.com, Inc. © 1993–2000 Software.com, Inc. All rights reserved. InterMail includes software that is copyright © 1990, 1993, 1994, The Regents of the University of California. All rights reserved. This code is derived from software contributed to Berkeley by Mike Olson. SmartHeap, portions copyright © 1991–1997, Compuware Corporation. InterMail incorporates a derivative work of the SSL Plus: SSL 3.0 Integration Suite Toolkit, copyright © 1996, 1997, Consensus Development Corporation. SSL Plus: SSL 3.0 Integration Suite is a trademark of Consensus Development Corporation, which reserves all rights thereto. Portions of the SSL Plus: SSL 3.0 Integration Suite Toolkit software are based on SSLRef™3.0, which is copyright © 1996, Netscape Communications Corporation. SSLRef™ was developed by Netscape Communications Corporation and Consensus Development Corporation. The MD5 Message-Digest algorithm used in InterMail is a copyrighted work of RSA Data Security, Inc., copyright © 1991–1992, RSA Data Security, Inc. All rights reserved. InterMail incorporates a derivative work of the BSAFE cryptographic toolkit, copyright © 1992–1996, RSA Data Security, Inc. All rights reserved. BSAFE is a trademark of RSA Data Security, Inc. The RSA Public Key Cryptosystem is protected by U.S. Patent #4,405,829. The Regular Expression Routines used in InterMail are copyright © 1992–94, Henry Spencer. -
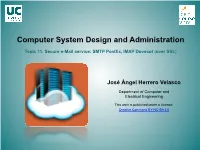
Computer System Administration. Topic 11. Secure E-Mail Service
Computer System Design and Administration Topic 11. Secure e-Mail service: SMTP Postfix, IMAP Dovecot (over SSL) José Ángel Herrero Velasco Department of Computer and Electrical Engineering This work is published under a License: Creative Commons BY-NC-SA 4.0 Computer System Design and Administration Topic 11. Secure e-Mail service: SMTP Postfix, IMAP Dovecot (over SSL) Puzzle Secure Information Server Clients Active ISC Directory DHCP Open ISC client SSL SSL LDAP DNS OpenLDAP DB LDAP ISC SSL NTP SSH IMAP (mail client) NFSv4 CIFS Secure MAIL Server Network file server/ MS Windows-Linux/UNIX interoperability SMTP IMAP (Postfix) (Dovecot) RAID/LVM SAMBA NFSv4 SSL Secure Web Server Ganglia Apache2 Hosts Core (web data) User (web data) Virtual MailLISTs Webmail pool pool (MailMan) (squirrelmail) (public_html) SSL Webmin Nagios 2 (.html, php …) WordPress José Ángel Herrero Velasco Computer System Design and Administration Topic 11. Secure e-Mail service: SMTP Postfix, IMAP Dovecot (over SSL) Target: e-Mail services • Deployment and development of an INTERNET secure e-MAIL service based on SMTP/IMAP protocols: – Sending mail using SMTP protocol: Pos(ix. – Receiving mail using IMAP protocol: Dovecot. – Management of Maildrop: Maildirs. – MUA-MTA secure communicaon (encrypted): TLS/SSL. • Installaon, configuraon and start up of a Webmail client: – Roundcube. – Mailmain. José Ángel Herrero Velasco Computer System Design and Administration Topic 11. Secure e-Mail service: SMTP Postfix, IMAP Dovecot (over SSL) The e-Mail system HTTP SMTP IMAP • Definions and basics: TCP TCP UDP – E-Mail: the electronic mail system: • Network service that enables 2 users from different computers IP to send and receive (exchange) digital messages. -

Correu Electrònic I Missatgeria
Correu electrònic i missatgeria Eduard Canet i Ricart Serveis de xarxa i Internet Serveis de xarxa i Internet Correu electrònic i missatgeria Índex Introducció 5 Resultats d’aprenentatge 7 1 Instal·lació i administració del servei de correu electrònic9 1.1 Protocols de correu electrònic..................................9 1.1.1 Format dels missatges.................................. 12 1.1.2 Bústies de correu..................................... 15 1.1.3 Funcionament de l’SMTP................................ 16 1.1.4 MIME.......................................... 20 1.2 Instal·lació d’un servidor..................................... 24 1.2.1 Instal·lació de l’aplicació servidor............................ 24 1.2.2 Usos indeguts del servidor de correu........................... 26 1.3 Accés remot al correu....................................... 27 1.3.1 Servei POP........................................ 27 1.3.2 Servei IMAP....................................... 31 1.3.3 Clients de correu..................................... 37 1.4 Correu encriptat i signat..................................... 38 1.4.1 Seguretat en el correu.................................. 39 1.4.2 Propietats de seguretat.................................. 40 1.4.3 Implementació de seguretat............................... 42 1.5 Servidor de correu segur..................................... 45 2 Instal·lació i administració de serveis de missatgeria instantània, notícies i llistes de distribució 47 2.1 Missatgeria instantània...................................... 47 2.1.1 -

LNCS 2763, Pp
A High Performance and Low Cost Cluster-Based E-mail System Woo-Chul Jeun1, Yang-Suk Kee1, Jin-Soo Kim2, and Soonhoi Ha1 1 School of Electrical Engineering and Computer Science, Seoul National University, San 56-1, Sinlim-dong, Gwanak-gu, Seoul 151-744, Korea {wcjeun, yskee, sha}@iris.snu.ac.kr 2 Division of Computer Science, KAIST, Daejeon 305-701, Korea [email protected] Abstract. A large-scale e-mail service provider requests a highly scal- able and available e-mail system to accommodate the increasing volume of e-mail traffic as well as the increasing number of e-mail users. To reduce the system development and maintenance cost, it is requested to make the system modular using off-the-shelf components. In this pa- per, we propose a cluster-based e-mail system architecture to achieve the goals of high scalability and availability, and low development and maintenance cost. We adopt the internal structure of a typical Internet e-mail system for a single server, called the MTA-MDA structure, to the proposed system architecture for the low cost requirements. We have implemented four different system configurations with the MTA-MDA structure and compare their performances. Experimental results show that the proposed system architecture achieves all the design objectives. 1 Introduction The growth of the Internet has led to an explosion in volumes of e-mail traffic and in number of the users of e-mail service. At the same time, large-scale e-mail service providers have appeared. They have hundreds of millions of subscribers and process billions of messages: for example, in May 2001, Hotmail had over 100 million users and Yahoo! Mail, in March 1999, served 45 million users with 3.6 billion mail messages [1][2]. -

International Network of Wrestling Researchers (INWR) Membership Directory
International Network of Wrestling Researchers (INWR) Membership Directory (Through June 2018) Allied with United World Wrestling and support group for their Scientific Commission www.inwr-wrestling.com Official publication is the International Journal of Wrestling Science (please send requests for membership and biographical updates to [email protected]) INWR MEMBERSHIP FRITZ BRYTING AANES Email: [email protected] 2X Olympian for Norway Areas of Interest: Coaching, Psychology ELENA ABAEVA MD [email protected] Uzbekistan UWW Medical Commission Doctor GARY ABBOTT Director of Communications & Special Projects [email protected] USA Wrestling Colorado Springs, CO Edmar Abdoulaev Board Member of the Dutch Wrestling Federation, FILA – Referee (Singapore 2010 YOG) Email: [email protected] [email protected] The Netherlands Dutch Wrestling Federation, Wrestling Club «Marshall Baarn» KSV Marshall Baarn, Goudenregenlaan 14, 3741 CB Baarn Interests: Wrestling Training, School Wrestling, Female Wrestling, Officiating BAKIYEV ZAFAR ABDUSHUKUROVICH Email: [email protected] Country: Uzbekhistan Bakiyev Zafar Abdushukurovich was born on 15 of December in 1982 in Tashkent, higher education, graduated from Uzbek State Institute of Physical Education in the direction of physical education (freestyle wrestling) in 2003, and Master's degree in sports in 2005, and post-graduate studies in 2009. Candidate of pedagogical sciences, associate professor. Since September 2009 he has been working as a head of the department of theory and methodology of the national and international kinds of wrestling in Uzbek State Institute of Physical Education. MAHMUT AĆAK [email protected] İnönü University BESYO, Turkey Dr. Açak has worked as a sportsman and trainer in wrestling and football. He worked as physiotherapist for the Turkish National Wrestling Team between 1990-1998. -
The Rise of Cloud Computing
Many of the designations used by manufacturers and sellers to distinguish their prod- Editor-in-Chief ucts are claimed as trademarks. Where those designations appear in this book, and Mark Taub the publisher was aware of a trademark claim, the designations have been printed Executive Editor with initial capital letters or in all capitals. Debra Williams Cauley The author and publisher have taken care in the preparation of this book, but make no Development Editor expressed or implied warranty of any kind and assume no responsibility for errors or omissions. No liability is assumed for incidental or consequential damages in connec- Songlin Qiu tion with or arising out of the use of the information or programs contained herein. Managing Editor The publisher offers excellent discounts on this book when ordered in quantity for Kristy Hart bulk purchases or special sales, which may include electronic versions and/or custom Project Editor covers and content particular to your business, training goals, marketing focus, and Andy Beaster branding interests. For more information, please contact: Copy Editor U.S. Corporate and Government Sales Barbara Hacha (800) 382-3419 [email protected] Indexer Heather McNeill For sales outside the United States please contact: Proofreader International Sales Language Logistics, LLC [email protected] Technical Reviewer Visit us on the Web: www.informit.com/ph Corey Burger Library of Congress Cataloging-in-Publication Data is on file Cover Designer Alan Clements Composition Copyright © 2009 Pearson Education, Inc. Bronkella Publishing, LLC All rights reserved. Printed in the United States of America. This publication is pro- tected by copyright, and permission must be obtained from the publisher prior to any prohibited reproduction, storage in a retrieval system, or transmission in any form or by any means, electronic, mechanical, photocopying, recording, or likewise. -

Lecture Notes for Web Security 2019 Part 5 — E-Mail Security Martin Hell
Lecture Notes for Web Security 2019 Part 5 | E-mail Security Martin Hell This chapter will discuss some different security aspects of emails. In order to understand these aspects, it is necessary to understand the SMTP protocol, i.e., how emails are sent from one user to another, and what the messages look like. 1 The SMTP Protocol SMTP (Simple Mail Transfer Protocol) is the most common protocol used to transfer emails. It was first defined in RFC 821 [6], which was obsoleted by RFC 2821 [4], which was again obsoleted by RFC 5321 [5]. The email architecture consists of several building blocks, see Figure 1. • MUA - Mail User Agent. This is the source and target of emails and is responsible for delivering the email to the MSA. Typical examples are Eudora, Outlook, Pine and Kmail. • MSA - Mail Submission Agent. This receives the message from the MUA and delivers it to the MTA. This is usually implemented together with the MTA instead of being a standalone program. The MSA can implement security checks on the email, e.g., checking that it is not spam, before sending it to the MTA. Message submission uses TCP port 587 and is discussed in RFC 4409 [3]. • MTA - Mail Transfer Agent. This is the building block that implements the SMTP protocol. It is responsible for both sending and receiving mes- sages. When the destination has been reached, the MTA at the end host sends the message to the MDA. Examples of MTAs are sendmail, postfix, qmail and Microsoft's Exchange Server. • MDA - Mail Delivery Agent.