HDCP 2.2 on Hdbaset Specification
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Media Gateways NX4600 Media Gateway
datasheet Media Gateways NX4600 Media Gateway The NX4600 is Nevion’s latest generation media transport and compression platform, Applications offering simultaneous H.264/AVC encoding • Professional broadcast contribution and decoding in a compact 1RU form factor. • Outside broadcast live sports & event contribution • Studio-to-studio media exchange The NX4600 is an H.264/AVC encoder, decoder and TS media gateway all built into one. • Managed media services over ASI or IP Up to four baseband SDI video signals can be Key features encoded using H.264/AVC or MPEG-2 compression • Multi-channel H.264/AVC encoder and/or decoder and transported over ASI and IP. The possibility and/or TS gateway with IP & ASI interfaces to combine encoding, decoding and TS over IP • Combine up to 4 channels of encoding and/or transport in the same unit increases flexibility in decoding in the same 1RU unit deployment of new services and gives a very • Software license approach ensures easy and tight and compact offering for outside broadcast future-proof upgrade path production applications (sports, news and other live events) and managed media services. • Best in class video quality with 4:2:2 10-bit H.264/ AVC compression up to 80 Mbit/s The Media Gateway includes Nevion’s trademark • 16-channel audio compression or pass-through advanced protection mechanisms that enable real- with full audio routing matrix built-in time transport of professional media over IP networks with extremely high availability. The NX4600 offers • Built-in TS monitoring (ETSI TR 101 290 Priority 1) of built-in aggregation of TS over IP streams on one or encoder output and decoder input, with option for multiple GbE ports. -

USB Displayport Dual View Hdbaset™ 2.0 KVM Extender (4K@100M for Single View)
CE924 USB DisplayPort Dual View HDBaseT™ 2.0 KVM Extender (4K@100m for Single View) The ATEN CE924 USB DisplayPort Dual View HDBaseT™ 2.0 KVM Extender integrates the latest HDBaseT™ 2.0 technologies to deliver 4K video, stereo audio, USB, and RS-232 signals. The HDBaseT™ 2.0 guarantees the most reliable transmission on the market as well as it provides long-reach capability that extends Full HD 1080P signals up to 150 meters. In addition, CE924 supports single 4K display or dual 1080p display for DisplayPort video output resolution up to 100m by using a single Cat6 / 2L-2910 Cat 6 cable. With an easy cable installation supporting various signals, the CE924 is ideal for applications where convenient remote access is required – such as transportation control centers, medical facilities, industrial warehouses, and extended workstations. Features Allows dual view DisplayPort access to a computer and KVM control from a remote console Supports HDBaseT 2.0 technology - Extends video, audio, USB, and RS-232 signals via a single Cat6 / 6a / 2L-2910 Cat 6 cable - Enhanced bit error detection and correction to resist signal interference during high-quality video transmissions - Status detection and LED indication for HDBaseT™ signal transmission on the remote unit EDID Buffer for smooth power-up and the highest quality display Single category cable to transmit AV and control signal - HDBaseT Standard mode up to 4K @ 100 m (via Cat 6 / 6a / 2L-2910); (single view only; dual-view resolution up to 1080p) - HDBaseT Long-Reach mode up to 1080P @ 150 m -

Calrec Network Primer V2
CALREC NETWORK PRIMER V2 Introduction to professional audio networks - 2017 edition Putting Sound in the Picture calrec.com NETWORK PRIMER V2 CONTENTS Forward 5 Introduction 7 Chapter One: The benefits of networking 11 Chapter Two: Some technical background 19 Chapter Three: Routes to interoperability 23 Chapter Four: Control, sync and metadata over IP 27 The established policy of Calrec Audio Ltd. is to seek improvements to the design, specifications and manufacture of all products. It is not always possible to provide notice outside the company of the alterations that take place continually. No part of this manual may be reproduced or transmitted in any form or by any means, Despite considerable effort to produce up to electronic or mechanical, including photocopying date information, no literature published by and scanning, for any purpose, without the prior the company nor any other material that may written consent of Calrec Audio Ltd. be provided should be regarded as an infallible Calrec Audio Ltd guide to the specifications available nor does Nutclough Mill Whilst the Company ensures that all details in this it constitute an offer for sale of any particular Hebden Bridge document are correct at the time of publication, product. West Yorkshire we reserve the right to alter specifications and England UK equipment without notice. Any changes we make Apollo, Artemis, Summa, Brio, Hydra Audio HX7 8EZ will be reflected in subsequent issues of this Networking, RP1 and Bluefin High Density Signal document. The latest version will be available Processing are registered trade marks of Calrec Tel: +44 (0)1422 842159 upon request. -

Programme Pour Développeurs AJA
Programme pour développeurs AJA KONA IP Programme pour développeurs AJA La technologie AJA est au cœur de nombreux produits. De par leur Travailler ensemble qualité supérieure et de la simplicité du kit de développement, les produits Le programme pour développeurs d’AJA permet aux entreprises partenaires d’intégrer les produits AJA AJA dédiés aux développeurs sont dans leurs systèmes. En utilisant des périphériques éprouvés d’entrée/sortie vidéo existants, les partenaires faciles à intégrer dans n’importe quel profitent de l’expertise d’AJA pour développer et soutenir ces technologies, en économisant de l’argent et en environnement Windows, Mac ou commercialisant leurs produits intégrés plus rapidement. Linux. AJA a une longue expérience en construction de périphériques vidéo davantage votre configuration. Avec des fonctionnalités allant des E/S fiables de haute qualité pour l’industrie de la vidéo. Le programme monocanal à multicanal, des flux E/S simultanés, l’intégration directe de pour développeurs AJA vous donne accès à ce niveau de qualité pour la fibre optique et les applications à large bande passante, les produits l’intégration dans vos propres produits. pour développeurs répondent à tous les besoins et couvrent toutes les gammes de prix. De nombreux produits d’AJA vendus au détail sont également disponibles pour vos développements. Que vous ayez besoin Le SDK complet et les outils de développement fournis par AJA vous d’incorporer la technologie de conversion dans un ensemble aideront à les intégrer dans tout environnement sous Windows®, OS X et préconstruit à l’aide de l’un de nos mini-convertisseurs, ou d’intégrer Linux®. -
CCSDS 766.3-R-1, Specification for RTP As Transport for Audio And
Draft Recommendation for Space Data System Standards SPECIFICATION FOR RTP AS TRANSPORT FOR AUDIO AND VIDEO OVER DTN DRAFT RECOMMENDED STANDARD CCSDS 766.3-R-1 RED BOOK December 2019 Draft Recommendation for Space Data System Standards SPECIFICATION FOR RTP AS TRANSPORT FOR AUDIO AND VIDEO OVER DTN DRAFT RECOMMENDED STANDARD CCSDS 766.3-R-1 RED BOOK December 2019 DRAFT CCSDS RECOMMENDED STANDARD FOR REAL-TIME TRANSPORT PROTOCOL OVER DELAY TOLERANT NETWORKING FOR VIDEO APPLICATIONS AUTHORITY Issue: Red Book, Issue 1 Date: December 2019 Location: Not Applicable (WHEN THIS RECOMMENDED STANDARD IS FINALIZED, IT WILL CONTAIN THE FOLLOWING STATEMENT OF AUTHORITY:) This document has been approved for publication by the Management Council of the Consultative Committee for Space Data Systems (CCSDS) and represents the consensus technical agreement of the participating CCSDS Member Agencies. The procedure for review and authorization of CCSDS documents is detailed in Organization and Processes for the Consultative Committee for Space Data Systems (CCSDS A02.1-Y-4), and the record of Agency participation in the authorization of this document can be obtained from the CCSDS Secretariat at the email address below. This document is published and maintained by: CCSDS Secretariat National Aeronautics and Space Administration Washington, DC, USA Email: [email protected] CCSDS 766.3-R-1 Page i December 2019 DRAFT CCSDS RECOMMENDED STANDARD FOR REAL-TIME TRANSPORT PROTOCOL OVER DELAY TOLERANT NETWORKING FOR VIDEO APPLICATIONS STATEMENT OF INTENT (WHEN THIS RECOMMENDED STANDARD IS FINALIZED, IT WILL CONTAIN THE FOLLOWING STATEMENT OF INTENT:) The Consultative Committee for Space Data Systems (CCSDS) is an organization officially established by the management of its members. -
Overview on IP Audio Networking Andreas Hildebrand, RAVENNA Evangelist ALC Networx Gmbh, Munich Topics
Overview on IP Audio Networking Andreas Hildebrand, RAVENNA Evangelist ALC NetworX GmbH, Munich Topics: • Audio networking vs. OSI Layers • Overview on IP audio solutions • AES67 & RAVENNA • Real-world application examples • Brief introduction to SMPTE ST2110 • NMOS • Control protocols Overview on IP Audio Networking - A. Hildebrand # 1 Layer 2 Layer 1 AVB EtherSound Layer 3 Audio over IP Audio over Ethernet ACIP TCP unicast RAVENNA AES67 multicast RTP UDP X192 Media streaming Dante CobraNet Livewire Overview on IP Audio Networking - A. Hildebrand # 3 Layer 2 Layer 1 AVB Terminology oftenEtherSound Layer 3 Audio over IP • ambiguousAudio over Ethernet ACIP TCP unicast • usedRAVENNA in wrongAES67 context multicast RTP • marketingUDP -driven X192 Media streaming • creates confusion Dante CobraNet Livewire Overview on IP Audio Networking - A. Hildebrand # 4 Layer 2 Layer 1 AVB Terminology oftenEtherSound Layer 3 Audio over IP • ambiguousAudio over Ethernet ACIP TCP Audio over IP unicast • usedRAVENNA in wrongAES67 context multicast RTP • marketingUDP -driven X192 Media streaming • creates confusion Dante CobraNet Livewire Overview on IP Audio Networking - A. Hildebrand # 5 Layer 7 Application Application Application and Layer 6 Presentation protocol-based layers Presentation HTTP, FTP, SMNP, Layer 5 Session Session POP3, Telnet, TCP, Layer 4 Transport UDP, RTP Transport Layer 3 Network Internet Protocol (IP) Network Layer 2 Data Link Ethernet, PPP… Data Link Layer 1 Physical 10011101 Physical Overview on IP Audio Networking - A. Hildebrand # 10 Physical transmission Classification by OSI network layer: Layer 1 Systems Transmit Receive Layer 1 Physical 10011101 Physical Overview on IP Audio Networking - A. Hildebrand # 12 Physical transmission Layer 1 systems: • Examples: SuperMac (AES50), A-Net Pro16/64 (Aviom), Rocknet 300 (Riedel), Optocore (Optocore), MediorNet (Riedel) • Fully proprietary systems • Make use of layer 1 physical transport (e.g. -

Cabling to Support 4K UHD Hdbaset Applications | WP00033 | BAVS BDC 0217 a AG
Cabling to Support 4K UHD Author: Ronald Tellas HDBaseT Applications Manager, Technology and Applications, Enterprise Networking Introduction Table of Contents HDBaseT™* networking technology enables HDMI signals to be transmitted over balanced Introduction 1 twisted-pair cabling. This allows AV system designers to combine the benefits of HDBaseT and category cabling by transmitting uncompressed high-definition video, audio, Ethernet, Types of Convergence 1 control, USB and remote power over a single network cable, extending reach up to 100 m IT and AV Standards 1 from the AV source to the display. White paper Goals 2 Types of Convergence HDBaseT Signals 2 Convergence can be discussed in two ways: Cabling Effects on Transfer Quality 2-3 Technology Infrastructure Measuring Cable Transfer Quality 4 Cable Transfer Quality Results 4 Technology convergence combines several autonomous networks onto a single network, working from the same system switch and backbone. VoIP phones, IP Cable Transfer Quality Analysis 5 surveillance cameras, lighting systems and building controls are all connecting to networks External Effects on Transfer Quality 6 to transfer data, receive data and adjust performance in real-time. Visual Errors 7 Infrastructure convergence uses category cabling to support different applications, Field Testing 7 such as Class 2 circuits for remote signaling, audio and video, including HDBaseT. Extender Variation 7 Channel Configurations 8 Grounding of Cable Shielding 9 IT and AV Standards Power over HDBaseT (POH) 9 Because there is no convergence of standards for IT and AV networks, both must be consulted individually. Conclusion 10 IT networking standards rely on ANSI/TIA-568-C.2 and ISO/ IEC 11801 cabling standards. -

2430RX2-10G Datasheet
2430RX2–10G Uncompressed Video Over IP to HDMI and SDI Converter The 2430RX2–10G is a versatile dual path uncompressed SDI over 10GbE to This self–contained module accepts up to two uncompressed SDI over HDMI/DVI/DisplayPort processing converter. The 2430RX2–10G can be used 10GbE streaming inputs. It decodes, processes, color corrects and converts to convert uncompressed video over IP including ASPEN, SMPTE 2022–6 and the output to an HDMI and SDI signal. The 2430RX2–10G device can drive SMPTE ST 2110 streams to HDMI and SDI. resolutions up to WUXGA (1920x1200). Features & Benefi ts • Full 4:2:2 10–bit pixel input resolution • Superior digital data transmission • Full 24–bit RGB output pixel resolution • Support dual path 10GbE to HDMI/DVI and SDI conversion. • Color correction, auto rescaling • Analog audio outputs supported • Ideal for use with high resolution LCD, plasma and projection screens • In–band control SDI Output 1 HDMI Color HDMI Input 1 Scaler Transmitter Correction OUTPUT 1 with HDCP Audio Formatter 2022–6 1 10G ASPEN Digital to Audio Audio ST 2110 Analog 2 Selector Out 10G Stream Converter Parsers Audio 3 Formatter HDMI Color HDMI Input 2 Scaler Transmitter Correction with HDCP OUTPUT 2 SDI Output 2 Control / CPU Monitoring In Band Control Serial Com Fault OK 12VDC OK SDI OUT FAULT 12 LN/ACT 1000 COM OK 2 1 3 2 1 2 1 FAULT CONTROL AUDIO OUT HDMI OUT SFP Specifi cations Input: Serial Video Output: Electrical: Format: ASPEN, SMPTE 2022–6 or Number of Outputs: 2 Voltage: 12V DC, auto–ranging 100–240V SMPTE ST 2110 over 10GbE -

Xilinx Smpte 2022 Video Over Ip Innovations: Hardware, Tools, Ip, and Reference Design Accelerate Development
BROADCAST SMPTE 2022 VIDEO OVER IP FLEXIBLE, HIGH-CAPACITY SDI-TO-ETHERNET BRIDGE FOR COST-EFFECTIVE CONVERGENCE OF BROADCAST VIDEO AND LAN/WAN NETWORKS XILINX SMPTE 2022 VIDEO OVER IP INNOVATIONS: HARDWARE, TOOLS, IP, AND REFERENCE DESIGN ACCELERATE DEVELOPMENT Broadcast Market Challenges Establishing live feeds from in-field cameras to the studio and out to audiences no longer requires complex, video-only connections and networks. High-capacity local area and wide • Economic and market conditions put high area networks have created the opportunity to packetize and carry video using Internet priority on reducing CAPEX and OPEX Protocol. Xilinx FPGAs are accelerating this convergence of data and video worlds by uniquely • Converging SDI with existing Internet enabling high-performance, high-capacity bridging between SDI and Ethernet. Protocol (IP) networks introduces Equipment manufacturers are taking advantage of the Xilinx SMPTE 2022 standard-based interoperability issues innovations and development platform to shorten time to market for next-generation, highly interoperable video over IP equipment. The resulting designs offer superior density, with the • Standards for transporting video over IP ability to carry multiple channels of video over a single link or cost-effectively carrying data are changing rapidly (moving target) along with video. The high IO capabilities of Xilinx FPGAs support more video devices, 3D • Manufacturers need to deploy quickly, to content, and higher resolutions for Super Hi Vision and 4K2K. speed convergence -
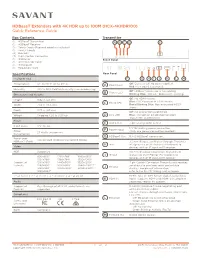
Hdbaset Extenders with 4K HDR up to 100M (HCX-4KHDR100) Quick Reference Guide
HDBaseT Extenders with 4K HDR up to 100M (HCX-4KHDR100) Quick Reference Guide Box Contents Transmitter (1) HDBaseT Transmitter A B C D E (1) HDBaseT Receiver (1) Power Cords (Regional adapters included) (1) Power Supply L R G (4) Brackets (3) 3-pin Control Connector POWER STATUS HDCP LINK AUDIO OUT (1) IR Emitter Front Panel (1) IR Connector Cable (1) IR Receiver (1) Regulatory Card IR IN IR OUT TX RX G HDMI IN TOSLINK OUT Specifications Rear Panel Environmental F G H I J K L M Off: Device is off. No power applied. Temperature 32° to 113° F (0° to 45° C) Power LED A Red: Main board is powered. Humidity 10% to 90% Relative Humidity (non-condensing) Off: HDBaseT processor is not running. B Status LED Dimensions and Weights Blinking Blue: HDBaseT processor is running. : No HDMI stream. Height 0.82 in (2.1 cm) Off Blue: HDCP present in HDMI stream. C HDCP LED Width 7.68 in (19.5 cm) Rapid Blinking Blue: Non-encrypted HDCP signal. Depth 3.73 in (9.5 cm) Off: No connection established. Weight Shipping 4.20 lb (1.91 kg) D Link LED Blue: Connection established between Transmitter and Receiver. Power E Audio Out 3-pin analog audio output Input Power 12V DC 3A 12V DC locking power connection. Power Input Power F (Only one power connection needed.) 27 Watts (maximum) Consumption G HDBaseT Out RJ-45 HDBaseT connection. Power over Can be used to power the second device. HDBaseT (PoH) 3.5 mm IR input for IR pass-through. -

Complete AV Solutions for Whole Home, Media Space and Digital Signage
2015 Issue 1 Complete AV Solutions for Whole Home, Media Space and Digital Signage 10 Year Warranty, Educational Programs, Design Services and Dedicated 7 Days a Week Support 70 Daggett Drive, San Jose, CA 95134 | Telephone: 877.536.3976 | International: 408.962.0515 | www.atlona.com © 2015 Atlona Inc. All rights reserved. “Atlona” and the Atlona logo are registered trademarks of Atlona Inc. All other brand names and trademarks or registered trademarks are the property of their respective owners. Digital Whole Home Solution Challenge Homes today have at panel TV’s in virtually every room. With all these TVs come unsightly black boxes, cables, and other equipment. Interior decorators absolutely hate it. Redundant Set Top Boxes and other sources for every room in the home is unattractive, costly, maintenance intensive, and reduces available living space. Remote controls usually come with these devices and are different for every room, that only confuses the homeowner. Solution Atlona’s matrix switchers allow any source to be routed to any television in the home. All equipment is centrally located and becomes a shared resource where it is out of sight which maintains the elegance of the home. System service is easier since all hardware is centrally located. They are available in several different sizes and with HDMI or HDBaseTTM outputs to support TVs up to 328 feet (100m) from the switch. Application Diagram & Speci cations Equipment Rack Living Room with 5.1 Channel Audio 6x6 version also available TV AT-UHD-PRO3-66M AV Receiver Cable Box 8 x 8 HDMI to HDBaseT Matrix Switcher [model no. -

HDMI Hdbaset Extender with Dual Output (4K@100M) (Hdbaset Class A)
VE814 HDMI HDBaseT Extender with Dual Output (4K@100m) (HDBaseT Class A) ATEN’s offering delivers high quality videos in dual displays over distance. With the VE814 HDMI Extender, your HDMI displays can be located up to 100 meters away from the HDMI source device. This is made possible using only one Cat 5e/6 cable, which is cheap and easily available. In addition, your video can be streamed using up to three HDMI displays – dual displays connected to the receiving unit (VE814R) and another one to the transmitter unit (VE814T). The VE814 carries an Ethernet pass-through port for Internet connectivity, making it easy to go online when necessary. It supports RS-232 and IR signaling pass-through, allowing you to control the HDMI source device from the remote unit (VE814R) while also granting access to the HDMI display device from the local unit (VE814T). The VE814 is HDMI (3D, Deep Color, 4K) and HDCP compatible, ensuring superior video quality so that you get the most out of your HDMI displays. Features Extends the distance between HDMI source and HDMI display Implements HDBaseT extension technology using only one Cat 5 cable to connect the transmitter and receiver Anti-jamming – resists signal interference during high-quality video transmissions using HDBaseT technology Supports one local and two remote displays Supports two IR channels for bi-directional IR signal transmission Extends Ethernet communication with pass-through port HDMI (3D, Deep Color,4kx2k); HDCP Compatible Long distance transmission – up to 100 m Supports wide screen