Applying Design Patterns for Web-Based Derivatives Pricing
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Ioc Containers in Spring
301AA - Advanced Programming Lecturer: Andrea Corradini [email protected] http://pages.di.unipi.it/corradini/ AP-2018-11: Frameworks and Inversion of Control Frameworks and Inversion of Control • Recap: JavaBeans as Components • Frameworks, Component Frameworks and their features • Frameworks vs IDEs • Inversion of Control and Containers • Frameworks vs Libraries • Decoupling Components • Dependency Injection • IoC Containers in Spring 2 Components: a recap A software component is a unit of composition with contractually specified interfaces and explicit context dependencies only. A software component can be deployed independently and is subject to composition by third party. Clemens Szyperski, ECOOP 1996 • Examples: Java Beans, CLR Assemblies • Contractually specified interfaces: events, methods and properties • Explicit context dependencies: serializable, constructor with no argument • Subject to composition: connection to other beans – Using connection oriented programming (event source and listeners/delegates) 3 Towards Component Frameworks • Software Framework: A collection of common code providing generic functionality that can be selectively overridden or specialized by user code providing specific functionality • Application Framework: A software framework used to implement the standard structure of an application for a specific development environment. • Examples: – GUI Frameworks – Web Frameworks – Concurrency Frameworks 4 Examples of Frameworks Web Application Frameworks GUI Toolkits 5 Examples: General Software Frameworks – .NET – Windows platform. Provides language interoperability – Android SDK – Supports development of apps in Java (but does not use a JVM!) – Cocoa – Apple’s native OO API for macOS. Includes C standard library and the Objective-C runtime. – Eclipse – Cross-platform, easily extensible IDE with plugins 6 Examples: GUI Frameworks • Frameworks for Application with GUI – MFC - Microsoft Foundation Class Library. -

Design Pattern Interview Questions
DDEESSIIGGNN PPAATTTTEERRNN -- IINNTTEERRVVIIEEWW QQUUEESSTTIIOONNSS http://www.tutorialspoint.com/design_pattern/design_pattern_interview_questions.htm Copyright © tutorialspoint.com Dear readers, these Design Pattern Interview Questions have been designed specially to get you acquainted with the nature of questions you may encounter during your interview for the subject of Design Pattern. As per my experience good interviewers hardly plan to ask any particular question during your interview, normally questions start with some basic concept of the subject and later they continue based on further discussion and what you answer: What are Design Patterns? Design patterns represent the best practices used by experienced object-oriented software developers. Design patterns are solutions to general problems that software developers faced during software development. These solutions were obtained by trial and error by numerous software developers over quite a substantial period of time. What is Gang of Four GOF? In 1994, four authors Erich Gamma, Richard Helm, Ralph Johnson and John Vlissides published a book titled Design Patterns - Elements of Reusable Object-Oriented Software which initiated the concept of Design Pattern in Software development. These authors are collectively known as Gang of Four GOF. Name types of Design Patterns? Design patterns can be classified in three categories: Creational, Structural and Behavioral patterns. Creational Patterns - These design patterns provide a way to create objects while hiding the creation logic, rather than instantiating objects directly using new opreator. This gives program more flexibility in deciding which objects need to be created for a given use case. Structural Patterns - These design patterns concern class and object composition. Concept of inheritance is used to compose interfaces and define ways to compose objects to obtain new functionalities. -
Zend Framework 3 Cookbook
Table of Contents Introduction 1.1 About the authors 1.2 Configuration zend-config for all your configuration needs 2.1 Manage your application with zend-config-aggregator 2.2 Data Manipulation Convert objects to arrays and back with zend-hydrator 3.1 Scrape Screens with zend-dom 3.2 Paginating data collections with zend-paginator 3.3 Log and Feeds Logging PHP applications 4.1 Discover and Read RSS and Atom Feeds 4.2 Create RSS and Atom Feeds 4.3 Authentication and Authorization Manage permissions with zend-permissions-rbac 5.1 Manage permissions with zend-permissions-acl 5.2 Web Services Implement JSON-RPC with zend-json-server 6.1 Implement an XML-RPC server with zend-xmlrpc 6.2 Implement a SOAP server with zend-soap 6.3 2 Security Context-specific escaping with zend-escaper 7.1 Filter input using zend-filter 7.2 Validate input using zend-validator 7.3 Validate data using zend-inputfilter 7.4 End-to-end encryption with Zend Framework 3 7.5 Deployment and Virtualization Create ZPKs the Easy Way 8.1 Using Laravel Homestead with Zend Framework Projects 8.2 Copyright Copyright note 9.1 3 Introduction Zend Framework 3 Cookbook During the year 2017, Matthew Weier O'Phinney and Enrico Zimuel started a series of blog posts on the offical Zend Framework blog covering its components. Zend Framework is composed by 60+ components covering a wide range of functionality. While the framework has typically been marketed as a full-stack MVC framework, the individual components themselves typically work independently and can be used standalone or within other frameworks. -
Design Patterns in PHP and Laravel — Kelt Dockins Design Patterns in PHP and Laravel
Design Patterns in PHP and Laravel — Kelt Dockins Design Patterns in PHP and Laravel Kelt Dockins [email protected] Design Patterns in PHP and Laravel Kelt Dockins Dolph, Arkansas USA ISBN-13 (pbk): 978-1-4842-2450-2 ISBN-13 (electronic): 978-1-4842-2451-9 DOI 10.1007/978-1-4842-2451-9 Library of Congress Control Number: 2016961807 Copyright © 2017 by Kelt Dockins This work is subject to copyright. All rights are reserved by the Publisher, whether the whole or part of the material is concerned, specifically the rights of translation, reprinting, reuse of illustrations, recitation, broadcasting, reproduction on microfilms or in any other physical way, and transmission or information storage and retrieval, electronic adaptation, computer software, or by similar or dissimilar methodology now known or hereafter developed. Trademarked names, logos, and images may appear in this book. Rather than use a trademark symbol with every occurrence of a trademarked name, logo, or image we use the names, logos, and images only in an editorial fashion and to the benefit of the trademark owner, with no intention of infringement of the trademark. The use in this publication of trade names, trademarks, service marks, and similar terms, even if they are not identified as such, is not to be taken as an expression of opinion as to whether or not they are subject to proprietary rights. While the advice and information in this book are believed to be true and accurate at the date of publication, neither the authors nor the editors nor the publisher can accept any legal responsibility for any errors or omissions that may be made. -
Process Synchronisation Background (1)
Process Synchronisation Background (1) Concurrent access to shared data may result in data inconsistency Maintaining data consistency requires mechanisms to ensure the orderly execution of cooperating processes Producer Consumer Background (2) Race condition count++ could be implemented as register1 = count register1 = register1 + 1 count = register1 count- - could be implemented as register2 = count register2 = register2 - 1 count = register2 Consider this execution interleaving with ―count = 5‖ initially: S0: producer execute register1 = count {register1 = 5} S1: producer execute register1 = register1 + 1 {register1 = 6} S2: consumer execute register2 = count {register2 = 5} S3: consumer execute register2 = register2 - 1 {register2 = 4} S4: producer execute count = register1 {count = 6 } S5: consumer execute count = register2 {count = 4} Solution: ensure that only one process at a time can manipulate variable count Avoid interference between changes Critical Section Problem Critical section: a segment of code in which a process may be changing Process structure common variables ◦ Only one process is allowed to be executing in its critical section at any moment in time Critical section problem: design a protocol for process cooperation Requirements for a solution ◦ Mutual exclusion ◦ Progress ◦ Bounded waiting No assumption can be made about the relative speed of processes Handling critical sections in OS ◦ Pre-emptive kernels (real-time programming, more responsive) Linux from 2.6, Solaris, IRIX ◦ Non-pre-emptive kernels (free from race conditions) Windows XP, Windows 2000, traditional UNIX kernel, Linux prior 2.6 Peterson’s Solution Two process solution Process Pi ◦ Mutual exclusion is preserved? ◦ The progress requirements is satisfied? ◦ The bounded-waiting requirement is met? Assumption: LOAD and STORE instructions are atomic, i.e. -
Dependency Injection in Unity3d
Dependency Injection in Unity3D Niko Parviainen Bachelor’s thesis March 2017 Technology, communication and transport Degree Programme in Software Engineering Description Author(s) Type of publication Date Parviainen, Niko Bachelor’s thesis March 2017 Language of publication: English Number of pages Permission for web publi- 57 cation: x Title of publication Dependency Injection in Unity3D Degree programme Degree Programme in Software Engineering Supervisor(s) Rantala, Ari Hämäläinen, Raija Assigned by Psyon Games Oy Abstract The objective was to find out how software design patterns and principles are applied to game development to achieve modular design. The tasks of the research were to identify the dependency management problem of a modular design, find out what the solutions offered by Unity3D are, find out what the dependency injection pattern is and how it is used in Unity3D environment. Dependency management in Unity3D and the dependency injection pattern were studied. Problems created by Unity3D’s solutions were introduced with examples. Dependency in- jection pattern was introduced with examples and demonstrated by implementing an ex- ample game using one of the available third-party frameworks. The aim of the example game was to clarify if the use of dependency injection brings modularity in Unity3D envi- ronment and what the cost of using it is. The principles of SOLID were introduced with generic examples and used to assist depend- ency injection to further increase the modularity by bringing the focus on class design. Dependency injection with the help of SOLID principles increased the modularity by loosely coupling classes even though slightly increasing the overall complexity of the architecture. -

Singleton Pattern: Motivation • Sometimes Need an Object That Is Unique – There Will Only Be a Single Instance of the Class
Singleton Pattern: Motivation • Sometimes need an object that is unique { There will only be a single instance of the class • Could be done with a global variable, BUT { Such an instance would exist for the duration of the program { If the instance were resource-intensive, this could be a problem { It would be better to create such an object only on an as-needed basis 1 Singleton Pattern: Defined • Singleton Pattern (177): Ensures a class has only one instance, and provides a global point of access to it. • The class manages a single instance of itself. • No other classes can create an instance of a singleton on their own. { I.e., another class cannot execute newInstance = new SingletonClass() • The singleton provides the means for other classes to access the instance. • Class diagram: • The question is: How to implement this so that we can insure that no more than one instance can be created? 2 Singleton Pattern: Implementation • We know that if we have a public constructor for a class, instances can be created by any other classes • But if we make the constructor private, only objects of the class could call the constructor, but then how could a first object of the class be created? { I.e., The only way to create an object of the class is to already have an object of the class (chicken and egg problem) • The trick is to have a private constructor but a static method that creates instances of the class { Since we're dealing with a singleton, the static method will include code that insures that only a single instance of the class will be created • Sample code: public class Singleton { private static Singleton uniqueInstance; private Singleton() { } public static Singleton getInstance() { if (uniqueInstance == null) uniqueInstance = new Singleton(); return uniqueInstance; } .. -

Student Website Setup
MVC in JSF and Spring Overview @author R.L. Martinez, Ph.D. Complexity is one of the primary challenges that has troubled software developers from the inception of the discipline. Software systems designed to perform multifaceted tasks are by nature complicated. Furthermore, software complexity continues to increase as we ask systems to accomplish more. With that in mind, designers are regularly pursuing techniques and methods to help reduce, or at least control, complexity growth. One such approach is known as MVC or, Model- View-Controller. Model-View-Controller MVC has its origins at Xerox’s PARC (Palo Alto Research Center) during the 1970-80’s. While there, Trygve Reenskaug, a visiting researcher from Norway, along with others such as Adele Goldberg, developed the MVC pattern for conceptualizing user interface based programs. PARC was an active site at that time for other important developments such as the graphical pointing device (mouse) and Object Oriented Programming (OOP). The first published work dealing with MVC at length was a 1988 article in The Journal of Object Technology. In software development terminology, MVC is known as an architectural pattern. A pattern is a reproducible and reusable construct which appears often enough in computer science as to be recognized. Instead of solving the same problem in a variety of sub-optimal ways, a pattern attempts to overlay a design with a common architectural solution. Developers not only become familiar with its application, but can also more easily understand a solution that uses a familiar pattern. There are a number of popular web application frameworks that offer MVC architectures which include: ASP.NET, Ruby on Rails, Zend Framework, Spring-MVC, etc. -
Dependency Injection with Unity
D EPEN DEPENDENCY INJECTION WITH UNITY Over the years software systems have evolutionarily become more and more patterns & practices D ENCY complex. One of the techniques for dealing with this inherent complexity Proven practices for predictable results of software systems is dependency injection – a design pattern that I allows the removal of hard-coded dependencies and makes it possible to Save time and reduce risk on your NJECT assemble a service by changing dependencies easily, whether at run-time software development projects by or compile-time. It promotes code reuse and loosely-coupled design which incorporating patterns & practices, I leads to more easily maintainable and flexible code. Microsoft’s applied engineering ON guidance that includes both production The guide you are holding in your hands is a primer on using dependency quality source code and documentation. W I injection with Unity – a lightweight extensible dependency injection TH DEPENDENCY INJECTION container built by the Microsoft patterns & practices team. It covers The guidance is designed to help U software development teams: various styles of dependency injection and also additional capabilities N I of Unity container, such as object lifetime management, interception, Make critical design and technology TY and registration by convention. It also discusses the advanced topics of selection decisions by highlighting WITH UNITY enhancing Unity with your custom extensions. the appropriate solution architectures, technologies, and Microsoft products The guide contains plenty of trade-off discussions and tips and tricks for for common scenarios managing your application cross-cutting concerns and making the most out of both dependency injection and Unity. These are accompanied by a Understand the most important Dominic Betts real world example that will help you master the techniques. -

Designpatternsphp Documentation Release 1.0
DesignPatternsPHP Documentation Release 1.0 Dominik Liebler and contributors Jul 18, 2021 Contents 1 Patterns 3 1.1 Creational................................................3 1.1.1 Abstract Factory........................................3 1.1.2 Builder.............................................8 1.1.3 Factory Method......................................... 13 1.1.4 Pool............................................... 18 1.1.5 Prototype............................................ 21 1.1.6 Simple Factory......................................... 24 1.1.7 Singleton............................................ 26 1.1.8 Static Factory.......................................... 28 1.2 Structural................................................. 30 1.2.1 Adapter / Wrapper....................................... 31 1.2.2 Bridge.............................................. 35 1.2.3 Composite............................................ 39 1.2.4 Data Mapper.......................................... 42 1.2.5 Decorator............................................ 46 1.2.6 Dependency Injection...................................... 50 1.2.7 Facade.............................................. 53 1.2.8 Fluent Interface......................................... 56 1.2.9 Flyweight............................................ 59 1.2.10 Proxy.............................................. 62 1.2.11 Registry............................................. 66 1.3 Behavioral................................................ 69 1.3.1 Chain Of Responsibilities................................... -
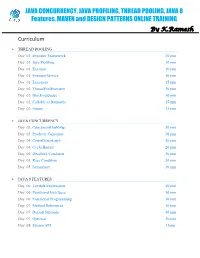
JAVA CONCURRENCY ONLINE TRAINING – Java2aspire
JAVA CONCURRENCY, JAVA PROFILING, THREAD POOLING, JAVA 8 Features, MAVEN and DESIGN PATTERNS ONLINE TRAINING By K.Ramesh Curriculum THREAD POOLING Day 01: Executor Framework 20 min Day 01: Java Profiling 10 min Day 01: Executor 10 min Day 01: ExecutorService 10 min Day 01: Executors 15 min Day 02: ThreadPoolExecutor 20 min Day 02: BlockingQueue 10 min Day 02: Callable vs Runnable 15 min Day 02: Future 15 min JAVA CONCURRENCY Day 03: ConcurrentHashMap 30 min Day 03: Producer Consumer 30 min Day 04: CountDownLatch 20 min Day 04: CyclicBarrier 20 min Day 04: Deadlock Condition 20 min Day 05: Race Condition 30 min Day 05: Semaphore 30 min JAVA 8 FEATURES Day 06: Lambda Expressions 40 min Day 06: Functional Interfaces 10 min Day 06: Functional Programming 10 min Day 07: Method References 10 min Day 07: Default Methods 40 min Day 07: Optional 10 min Day 08: Stream API 1 hour MAVEN Day 09: Project Object Model (POM) 20 min Day 09: Project Description 10 min Day 09: Public Repository 10 min Day 09: Dependency Management 10 min Day 09: Build Configuration 10 min Day 10: Installation 15 min Day 10: Dependency Scope 15 min Day 10: Proprietary Dependencies 15 min Day 10: Project Inheritance 15 min Day 11: Maven life cycle 20 min Day 11: Maven Directory Structure 20 min Day 11: Archetypes 20 min Day 12: Applications 1 hour DESIGN PATTERNS Day 13: Factory Pattern 20 min Day 13: Abstract Factory Pattern 10 min Day 13: Single Pattern 20 min Day 13: Prototype Pattern 10 min Day 14: Composite Pattern 10 min Day 14: Facade Pattern 15 min Day 14: DAO -

A Design Pattern Approach
Wright State University CORE Scholar Browse all Theses and Dissertations Theses and Dissertations 2009 Automated Transforms of Software Models: A Design Pattern Approach Brandon Adam Gump Wright State University Follow this and additional works at: https://corescholar.libraries.wright.edu/etd_all Part of the Computer Sciences Commons Repository Citation Gump, Brandon Adam, "Automated Transforms of Software Models: A Design Pattern Approach" (2009). Browse all Theses and Dissertations. 969. https://corescholar.libraries.wright.edu/etd_all/969 This Thesis is brought to you for free and open access by the Theses and Dissertations at CORE Scholar. It has been accepted for inclusion in Browse all Theses and Dissertations by an authorized administrator of CORE Scholar. For more information, please contact [email protected]. AUTOMATED TRANSFORMS OF SOFTWARE MODELS: A DESIGN PATTERN APPROACH A thesis submitted in partial fulfillment of the requirements for the degree of Master of Science By BRANDON ADAM GUMP B.S., Wright State University, 2008 2009 Wright State University WRIGHT STATE UNIVERSITY SCHOOL OF GRADUATE STUDIES November 23, 2009 I HEREBY RECOMMEND THAT THE THESIS PREPARED UNDER MY SUPERVISION BY Brandon Adam Gump ENTITLED Automated Transforms of Software Models: A Design Pattern Approach BE ACCEPTED IN PARTIAL FULFILLMENT OF THE REQUIREMENTS FOR THE DEGREE OF Master of Science . Thomas C. Hartrum, Ph.D. Thesis Co-Director Mateen M. Rizki, Ph.D. Thesis Co-Director Thomas A. Sudkamp, Ph.D. Department Chair Committee on Final Examination Thomas C. Hartrum, Ph.D. Mateen M. Rizki, Ph.D. Travis E. Doom, Ph.D. Joseph F. Thomas, Jr., Ph.D. Dean, School of Graduate Studies ABSTRACT Gump, Brandon Adam.