Applied Cryptanalysis: Breaking Ciphers in the Real World
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Mathemathics of Secrets.Pdf
THE MATHEMATICS OF SECRETS THE MATHEMATICS OF SECRETS CRYPTOGRAPHY FROM CAESAR CIPHERS TO DIGITAL ENCRYPTION JOSHUA HOLDEN PRINCETON UNIVERSITY PRESS PRINCETON AND OXFORD Copyright c 2017 by Princeton University Press Published by Princeton University Press, 41 William Street, Princeton, New Jersey 08540 In the United Kingdom: Princeton University Press, 6 Oxford Street, Woodstock, Oxfordshire OX20 1TR press.princeton.edu Jacket image courtesy of Shutterstock; design by Lorraine Betz Doneker All Rights Reserved Library of Congress Cataloging-in-Publication Data Names: Holden, Joshua, 1970– author. Title: The mathematics of secrets : cryptography from Caesar ciphers to digital encryption / Joshua Holden. Description: Princeton : Princeton University Press, [2017] | Includes bibliographical references and index. Identifiers: LCCN 2016014840 | ISBN 9780691141756 (hardcover : alk. paper) Subjects: LCSH: Cryptography—Mathematics. | Ciphers. | Computer security. Classification: LCC Z103 .H664 2017 | DDC 005.8/2—dc23 LC record available at https://lccn.loc.gov/2016014840 British Library Cataloging-in-Publication Data is available This book has been composed in Linux Libertine Printed on acid-free paper. ∞ Printed in the United States of America 13579108642 To Lana and Richard for their love and support CONTENTS Preface xi Acknowledgments xiii Introduction to Ciphers and Substitution 1 1.1 Alice and Bob and Carl and Julius: Terminology and Caesar Cipher 1 1.2 The Key to the Matter: Generalizing the Caesar Cipher 4 1.3 Multiplicative Ciphers 6 -

Polish Mathematicians Finding Patterns in Enigma Messages
Fall 2006 Chris Christensen MAT/CSC 483 Machine Ciphers Polyalphabetic ciphers are good ways to destroy the usefulness of frequency analysis. Implementation can be a problem, however. The key to a polyalphabetic cipher specifies the order of the ciphers that will be used during encryption. Ideally there would be as many ciphers as there are letters in the plaintext message and the ordering of the ciphers would be random – an one-time pad. More commonly, some rotation among a small number of ciphers is prescribed. But, rotating among a small number of ciphers leads to a period, which a cryptanalyst can exploit. Rotating among a “large” number of ciphers might work, but that is hard to do by hand – there is a high probability of encryption errors. Maybe, a machine. During World War II, all the Allied and Axis countries used machine ciphers. The United States had SIGABA, Britain had TypeX, Japan had “Purple,” and Germany (and Italy) had Enigma. SIGABA http://en.wikipedia.org/wiki/SIGABA 1 A TypeX machine at Bletchley Park. 2 From the 1920s until the 1970s, cryptology was dominated by machine ciphers. What the machine ciphers typically did was provide a mechanical way to rotate among a large number of ciphers. The rotation was not random, but the large number of ciphers that were available could prevent depth from occurring within messages and (if the machines were used properly) among messages. We will examine Enigma, which was broken by Polish mathematicians in the 1930s and by the British during World War II. The Japanese Purple machine, which was used to transmit diplomatic messages, was broken by William Friedman’s cryptanalysts. -

Analysis of Arx Round Functions in Secure Hash Functions
ANALYSIS OF ARX ROUND FUNCTIONS IN SECURE HASH FUNCTIONS by Kerry A. McKay B.S. in Computer Science, May 2003, Worcester Polytechnic Institute M.S. in Computer Science, May 2005, Worcester Polytechnic Institute A Dissertation submitted to the Faculty of The School of Engineering and Applied Science of The George Washington University in partial satisfaction of the requirements for the degree of Doctor of Science May 15, 2011 Dissertation directed by Poorvi L. Vora Associate Professor of Computer Science The School of Engineering and Applied Science of The George Washington University certifies that Kerry A. McKay has passed the Final Examination for the degree of Doctor of Science as of March 25, 2011. This is the final and approved form of the dissertation. ANALYSIS OF ARX ROUND FUNCTIONS IN SECURE HASH FUNCTIONS Kerry A. McKay Dissertation Research Committee: Poorvi L. Vora, Associate Professor of Computer Science, Dissertation Director Gabriel Parmer, Assistant Professor of Computer Science, Committee Member Rahul Simha, Associate Professor of Engineering and Applied Science, Committee Member Abdou Youssef, Professor of Engineering and Applied Science, Committee Member Lily Chen, Mathematician, National Institute of Standards and Technology, Committee Member ii Dedication To my family and friends, for all of their encouragement and support. iii Acknowledgements This work was supported in part by the NSF Scholarship for Service Program, grant DUE-0621334, and NSF Award 0830576. I would like to thank my collaborators Niels Ferguson and Stefan Lucks for our collaborative research on the analysis of the CubeHash submission to the SHA-3 competition. I would also like to thank the entire Skein team for their support. -

Bruce Schneier 2
Committee on Energy and Commerce U.S. House of Representatives Witness Disclosure Requirement - "Truth in Testimony" Required by House Rule XI, Clause 2(g)(5) 1. Your Name: Bruce Schneier 2. Your Title: none 3. The Entity(ies) You are Representing: none 4. Are you testifying on behalf of the Federal, or a State or local Yes No government entity? X 5. Please list any Federal grants or contracts, or contracts or payments originating with a foreign government, that you or the entity(ies) you represent have received on or after January 1, 2015. Only grants, contracts, or payments related to the subject matter of the hearing must be listed. 6. Please attach your curriculum vitae to your completed disclosure form. Signatur Date: 31 October 2017 Bruce Schneier Background Bruce Schneier is an internationally renowned security technologist, called a security guru by the Economist. He is the author of 14 books—including the New York Times best-seller Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World—as well as hundreds of articles, essays, and academic papers. His influential newsletter Crypto-Gram and blog Schneier on Security are read by over 250,000 people. Schneier is a fellow at the Berkman Klein Center for Internet and Society at Harvard University, a Lecturer in Public Policy at the Harvard Kennedy School, a board member of the Electronic Frontier Foundation and the Tor Project, and an advisory board member of EPIC and VerifiedVoting.org. He is also a special advisor to IBM Security and the Chief Technology Officer of IBM Resilient. -

Identifying Open Research Problems in Cryptography by Surveying Cryptographic Functions and Operations 1
International Journal of Grid and Distributed Computing Vol. 10, No. 11 (2017), pp.79-98 http://dx.doi.org/10.14257/ijgdc.2017.10.11.08 Identifying Open Research Problems in Cryptography by Surveying Cryptographic Functions and Operations 1 Rahul Saha1, G. Geetha2, Gulshan Kumar3 and Hye-Jim Kim4 1,3School of Computer Science and Engineering, Lovely Professional University, Punjab, India 2Division of Research and Development, Lovely Professional University, Punjab, India 4Business Administration Research Institute, Sungshin W. University, 2 Bomun-ro 34da gil, Seongbuk-gu, Seoul, Republic of Korea Abstract Cryptography has always been a core component of security domain. Different security services such as confidentiality, integrity, availability, authentication, non-repudiation and access control, are provided by a number of cryptographic algorithms including block ciphers, stream ciphers and hash functions. Though the algorithms are public and cryptographic strength depends on the usage of the keys, the ciphertext analysis using different functions and operations used in the algorithms can lead to the path of revealing a key completely or partially. It is hard to find any survey till date which identifies different operations and functions used in cryptography. In this paper, we have categorized our survey of cryptographic functions and operations in the algorithms in three categories: block ciphers, stream ciphers and cryptanalysis attacks which are executable in different parts of the algorithms. This survey will help the budding researchers in the society of crypto for identifying different operations and functions in cryptographic algorithms. Keywords: cryptography; block; stream; cipher; plaintext; ciphertext; functions; research problems 1. Introduction Cryptography [1] in the previous time was analogous to encryption where the main task was to convert the readable message to an unreadable format. -

Basque Mythology
Center for Basque Studies Basque Classics Series, No. 3 Selected Writings of José Miguel de Barandiarán: Basque Prehistory and Ethnography Compiled and with an Introduction by Jesús Altuna Translated by Frederick H. Fornoff, Linda White, and Carys Evans-Corrales Center for Basque Studies University of Nevada, Reno Reno, Nevada This book was published with generous financial support obtained by the Association of Friends of the Center for Basque Studies from the Provincial Government of Bizkaia. Basque Classics Series, No. Series Editors: William A. Douglass, Gregorio Monreal, and Pello Salaburu Center for Basque Studies University of Nevada, Reno Reno, Nevada 89557 http://basque.unr.edu Copyright © by the Center for Basque Studies All rights reserved. Printed in the United States of America. Cover and series design © by Jose Luis Agote. Cover illustration: Josetxo Marin Library of Congress Cataloging-in-Publication Data Barandiarán, José Miguel de. [Selections. English. ] Selected writings of Jose Miguel de Barandiaran : Basque prehistory and ethnography / compiled and with an introduction by Jesus Altuna ; transla- tion by Frederick H. Fornoff, Linda White, and Carys Evans-Corrales. p. cm. -- (Basque classics series / Center for Basque Studies ; no. ) Summary: “Extracts from works by Basque ethnographer Barandiaran on Basque prehistory, mythology, magical beliefs, rural life, gender roles, and life events such as birth, marriage, and death, gleaned from interviews and excavations conducted in the rural Basque Country in the early to mid-twentieth century. Introduction includes biographical information on Barandiaran”--Provided by publisher. Includes bibliographical references and index. ISBN ---- (pbk.) -- ISBN ---- (hardcover) . Basques--Folklore. Mythology, Basque. Basques--Social life and cus- toms. -
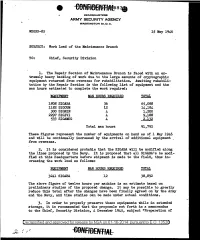
Work Load of the Maintenance Branch
HEADQUARTERS ARMY SECURITY AGENCY WASHINGTON 25, D. C. WDGSS-85 15 May 1946 SUBJECT: Work Load of the Maintenance Branch TO: Chief, Security Division 1. The Repair Section of Maintenance Branch is .faced with an ex tremely heavy backlog of' work due to the large amounts of' cryptographic equipment returned from overseas for rehabilitation. Awaiting rehabili tation by the Repair Section is the followi~g list of equipment and the man hours estimated to complete the work required.: EQUIPMENT MAN HOURS REQUIRED TOTAL 1808 SIGABA 36 65,088 1182 SIGCUM 12 14,184 300 SIGNIN 4 1,200 2297 SIGIVI 4 9,188 533 SIGAMUG 4, 2,132 Total man hours 91,792 These figures represent the number of equipments on hand as of 1 May 1946 and will be continually increased by the arrival of additional equipment . from overseas. 2. It is considered probable that the SIGABA will be modified along the lines proposed by the Navy. It is proposed that all SIGABA 1s be modi fied at this Headquarters before shipment is made to the field, thus in creasing the work load as follows: EQUIPMENT MAN HOURS REQUIRED 3241 SIGABA 12 The above figure of' twelve hours per machine is an estimate based on preliminary studies of' the proposed change. It may be possible to greatly reduce this total af'ter the changes have been f inaJ.ly agreed on by the .Army and the Navy, and time studies can be made under actual conditions. ,3. In order to properly preserve these equipments while in extended storage, it is recommended that the proposals set .forth in a memorandum to the Chief, Security Division, 4 December 1945, subject "Preparation of Declassified and approved for release by NSA on 01-16-2014 pursuantto E .0. -

SIS and Cipher Machines: 1930 – 1940
SIS and Cipher Machines: 1930 – 1940 John F Dooley Knox College Presented at the 14th Biennial NSA CCH History Symposium, October 2013 This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 3.0 United States License. 1 Thursday, November 7, 2013 1 The Results of Friedman’s Training • The initial training regimen as it related to cipher machines was cryptanalytic • But this detailed analysis of the different machine types informed the team’s cryptographic imaginations when it came to creating their own machines 2 Thursday, November 7, 2013 2 The Machines • Wheatstone/Plett Machine • M-94 • AT&T machine • M-138 and M-138-A • Hebern cipher machine • M-209 • Kryha • Red • IT&T (Parker Hitt) • Purple • Engima • SIGABA (M-134 and M-134-C) • B-211(and B-21) 3 Thursday, November 7, 2013 3 The Wheatstone/Plett Machine • polyalphabetic cipher disk with gearing mechanism rotates the inner alphabet. • Plett’s improvement is to add a second key and mixed alphabet to the inner ring. • Friedman broke this in 1918 Principles: (a) The inner workings of a mechanical cryptographic device can be worked out using a paper and pencil analog of the device. (b) if there is a cycle in the mechanical device (say for particular cipher alphabets), then that cycle can be discovered by analysis of the paper and pencil analog. 4 Thursday, November 7, 2013 4 The Army M-94 • Traces its roots back to Jefferson and Bazieres • Used by US Army from 1922 to circa 1942 • 25 mixed alphabets. Disk order is the key. -

A Complete Bibliography of Publications in Cryptologia
A Complete Bibliography of Publications in Cryptologia Nelson H. F. Beebe University of Utah Department of Mathematics, 110 LCB 155 S 1400 E RM 233 Salt Lake City, UT 84112-0090 USA Tel: +1 801 581 5254 FAX: +1 801 581 4148 E-mail: [email protected], [email protected], [email protected] (Internet) WWW URL: http://www.math.utah.edu/~beebe/ 04 September 2021 Version 3.64 Title word cross-reference 10016-8810 [?, ?]. 1221 [?]. 125 [?]. 15.00/$23.60.0 [?]. 15th [?, ?]. 16th [?]. 17-18 [?]. 18 [?]. 180-4 [?]. 1812 [?]. 18th (t; m)[?]. (t; n)[?, ?]. $10.00 [?]. $12.00 [?, ?, ?, ?, ?]. 18th-Century [?]. 1930s [?]. [?]. 128 [?]. $139.99 [?]. $15.00 [?]. $16.95 1939 [?]. 1940 [?, ?]. 1940s [?]. 1941 [?]. [?]. $16.96 [?]. $18.95 [?]. $24.00 [?]. 1942 [?]. 1943 [?]. 1945 [?, ?, ?, ?, ?]. $24.00/$34 [?]. $24.95 [?, ?]. $26.95 [?]. 1946 [?, ?]. 1950s [?]. 1970s [?]. 1980s [?]. $29.95 [?]. $30.95 [?]. $39 [?]. $43.39 [?]. 1989 [?]. 19th [?, ?]. $45.00 [?]. $5.95 [?]. $54.00 [?]. $54.95 [?]. $54.99 [?]. $6.50 [?]. $6.95 [?]. $69.00 2 [?, ?]. 200/220 [?]. 2000 [?]. 2004 [?, ?]. [?]. $69.95 [?]. $75.00 [?]. $89.95 [?]. th 2008 [?]. 2009 [?]. 2011 [?]. 2013 [?, ?]. [?]. A [?]. A3 [?, ?]. χ [?]. H [?]. k [?, ?]. M 2014 [?]. 2017 [?]. 2019 [?]. 20755-6886 [?, ?]. M 3 [?]. n [?, ?, ?]. [?]. 209 [?, ?, ?, ?, ?, ?]. 20th [?]. 21 [?]. 22 [?]. 220 [?]. 24-Hour [?, ?, ?]. 25 [?, ?]. -Bit [?]. -out-of- [?, ?]. -tests [?]. 25.00/$39.30 [?]. 25.00/839.30 [?]. 25A1 [?]. 25B [?]. 26 [?, ?]. 28147 [?]. 28147-89 000 [?]. 01Q [?, ?]. [?]. 285 [?]. 294 [?]. 2in [?, ?]. 2nd [?, ?, ?, ?]. 1 [?, ?, ?, ?]. 1-4398-1763-4 [?]. 1/2in [?, ?]. 10 [?]. 100 [?]. 10011-4211 [?]. 3 [?, ?, ?, ?]. 3/4in [?, ?]. 30 [?]. 310 1 2 [?, ?, ?, ?, ?, ?, ?]. 312 [?]. 325 [?]. 3336 [?, ?, ?, ?, ?, ?]. affine [?]. [?]. 35 [?]. 36 [?]. 3rd [?]. Afluisterstation [?, ?]. After [?]. Aftermath [?]. Again [?, ?]. Against 4 [?]. 40 [?]. 44 [?]. 45 [?]. 45th [?]. 47 [?]. [?, ?, ?, ?, ?, ?, ?, ?, ?, ?, ?, ?, ?]. Age 4in [?, ?]. [?, ?]. Agencies [?]. Agency [?, ?, ?, ?, ?, ?, ?, ?, ?, ?, ?]. -

Statistical Cryptanalysis of Block Ciphers
STATISTICAL CRYPTANALYSIS OF BLOCK CIPHERS THÈSE NO 3179 (2005) PRÉSENTÉE À LA FACULTÉ INFORMATIQUE ET COMMUNICATIONS Institut de systèmes de communication SECTION DES SYSTÈMES DE COMMUNICATION ÉCOLE POLYTECHNIQUE FÉDÉRALE DE LAUSANNE POUR L'OBTENTION DU GRADE DE DOCTEUR ÈS SCIENCES PAR Pascal JUNOD ingénieur informaticien dilpômé EPF de nationalité suisse et originaire de Sainte-Croix (VD) acceptée sur proposition du jury: Prof. S. Vaudenay, directeur de thèse Prof. J. Massey, rapporteur Prof. W. Meier, rapporteur Prof. S. Morgenthaler, rapporteur Prof. J. Stern, rapporteur Lausanne, EPFL 2005 to Mimi and Chlo´e Acknowledgments First of all, I would like to warmly thank my supervisor, Prof. Serge Vaude- nay, for having given to me such a wonderful opportunity to perform research in a friendly environment, and for having been the perfect supervisor that every PhD would dream of. I am also very grateful to the president of the jury, Prof. Emre Telatar, and to the reviewers Prof. em. James L. Massey, Prof. Jacques Stern, Prof. Willi Meier, and Prof. Stephan Morgenthaler for having accepted to be part of the jury and for having invested such a lot of time for reviewing this thesis. I would like to express my gratitude to all my (former and current) col- leagues at LASEC for their support and for their friendship: Gildas Avoine, Thomas Baign`eres, Nenad Buncic, Brice Canvel, Martine Corval, Matthieu Finiasz, Yi Lu, Jean Monnerat, Philippe Oechslin, and John Pliam. With- out them, the EPFL (and the crypto) would not be so fun! Without their support, trust and encouragement, the last part of this thesis, FOX, would certainly not be born: I owe to MediaCrypt AG, espe- cially to Ralf Kastmann and Richard Straub many, many, many hours of interesting work. -

Research Problems in Block Cipher Cryptanalysis: an Experimental Analysis Amandeep, G
International Journal of Innovative Technology and Exploring Engineering (IJITEE) ISSN: 2278-3075, Volume-8 Issue-8S3, June 2019 Research Problems in Block Cipher Cryptanalysis: An Experimental Analysis Amandeep, G. Geetha Abstract: Cryptography has always been a very concerning Organization of this paper is as follows. Section 2 lists the issue in research related to digital security. The dynamic need of Block ciphers in a chronological order in a table having six applications and keeping online transactions secure have been columns stating name of the algorithm, year of publication, giving pathways to the need of developing different its cryptographic strategies. Though a number of cryptographic structure, block size, key size, and the cryptanalysis done on algorithms have been introduced till now, but each of these algorithms has its own disadvantages or weaknesses which are that particular cipher. This table becomes the basis of the identified by the process of cryptanalysis. This paper presents a analysis done in Section 3 and tabulates the information as to survey of different block ciphers and the results of attempts to which structure has been cryptanalyzed more, thereby identify their weakness. Depending upon the literature review, establishing a trend of structures analyzed Section 4 some open research problems are being presented which the identifies the open research problems based on the analysis cryptologists can depend on to work for bettering cyber security. done in Section 3. Section 5 of the paper, presents the conclusion of this study. Index Terms: block ciphers, cryptanalysis, attacks, SPN, Feistel. II. RELATED WORK I. INTRODUCTION This paper surveys 69 block ciphers and presents, in Cryptography is the science which deals with Table I, a summarized report as per the attacks concerned. -
The Case of the “Big Seven” Basque Chefs
Keys to success in an example of inter-competitor cooperation: The Case of the “Big Seven” Innobasque Case Studies Basque Chefs In collaboration with Authors María Soledad Aguirre: [email protected] Covadonga Aldamiz-Echevarría: [email protected] Gloria Aparicio: [email protected] Coordinators Idoia Bidaurrazaga: [email protected] Lola Elejalde: [email protected] Acknowledgements The authors would like to thank Juan Mari Arzak, Pedro Subijana, Karlos Arguiñano, Hilario Arbelaitz, Martín Berasategui, Andoni Luis Aduriz and Eneko Atxa for their help in preparing this case study and to Pedro J. Moreno and José Luis Galiana for providing photographic material. Published by: Innobasque - 2011 Basque Innovation Agency Parque Tecnológico de Bizkaia Laida Bidea, 203 48170 - Zamudio www.casosinnobasque.com ISBN: 978-84-96543-43-0 The contents of this book, in this edition, are published under a Creative Commons Attribution-NonCommercial-NoDerivs 3.0 Spain licence (for more information, see http://creativecommons.org/licenses/by-nc-nd/3.0/deed.es_CO) The contents of this publication have been drawn up with the approval of Juan Mari Arzak, Pedro Subijana, Karlos Arguiñano, Hilario Arbelaitz, Martín Berasategui, Andoni Luis Aduriz and Eneko Atxa. Publication PMP Management Factory and layout: E-mail: [email protected] Website: www.pmp.es THE CASE OF T HE “BIG SEVEN ” BASQUE CHEFS 3 Contents Foreword 5 Introduction 7 1. The origins: the history of the formation of the Basque Chefs group 8 2. Current situation: from Basque “nouvelle cuisine” to Basque “haute cuisine” 12 3. Collaboration between Basque chefs and other agents: the extended value generation network 17 4.