CRYPTOLOGY Notes &
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
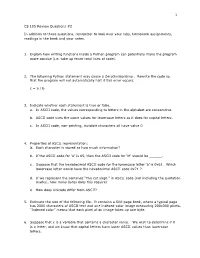
CS 105 Review Questions #2 in Addition to These Questions
1 CS 105 Review Questions #2 In addition to these questions, remember to look over your labs, homework assignments, readings in the book and your notes. 1. Explain how writing functions inside a Python program can potentially make the program more concise (i.e. take up fewer total lines of code). 2. The following Python statement may cause a ZeroDivisionError. Rewrite the code so that the program will not automatically halt if this error occurs. c = a / b 3. Indicate whether each statement is true or false. a. In ASCII code, the values corresponding to letters in the alphabet are consecutive. b. ASCII code uses the same values for lowercase letters as it does for capital letters. c. In ASCII code, non-printing, invisible characters all have value 0 4. Properties of ASCII representation: a. Each character is stored as how much information? b. If the ASCII code for ‘A’ is 65, then the ASCII code for ‘M’ should be ______. c. Suppose that the hexadecimal ASCII code for the lowercase letter ‘a’ is 0x61. Which lowercase letter would have the hexadecimal ASCII code 0x71 ? d. If we represent the sentence “The cat slept.” in ASCII code (not including the quotation marks), how many bytes does this require? e. How does Unicode differ from ASCII? 5. Estimate the size of the following file. It contains a 500-page book, where a typical page has 2000 characters of ASCII text and one indexed-color image measuring 200x300 pixels. “Indexed color” means that each pixel of an image takes up one byte. -

COS433/Math 473: Cryptography Mark Zhandry Princeton University Spring 2017 Cryptography Is Everywhere a Long & Rich History
COS433/Math 473: Cryptography Mark Zhandry Princeton University Spring 2017 Cryptography Is Everywhere A Long & Rich History Examples: • ~50 B.C. – Caesar Cipher • 1587 – Babington Plot • WWI – Zimmermann Telegram • WWII – Enigma • 1976/77 – Public Key Cryptography • 1990’s – Widespread adoption on the Internet Increasingly Important COS 433 Practice Theory Inherent to the study of crypto • Working knowledge of fundamentals is crucial • Cannot discern security by experimentation • Proofs, reductions, probability are necessary COS 433 What you should expect to learn: • Foundations and principles of modern cryptography • Core building blocks • Applications Bonus: • Debunking some Hollywood crypto • Better understanding of crypto news COS 433 What you will not learn: • Hacking • Crypto implementations • How to design secure systems • Viruses, worms, buffer overflows, etc Administrivia Course Information Instructor: Mark Zhandry (mzhandry@p) TA: Fermi Ma (fermima1@g) Lectures: MW 1:30-2:50pm Webpage: cs.princeton.edu/~mzhandry/2017-Spring-COS433/ Office Hours: please fill out Doodle poll Piazza piaZZa.com/princeton/spring2017/cos433mat473_s2017 Main channel of communication • Course announcements • Discuss homework problems with other students • Find study groups • Ask content questions to instructors, other students Prerequisites • Ability to read and write mathematical proofs • Familiarity with algorithms, analyZing running time, proving correctness, O notation • Basic probability (random variables, expectation) Helpful: • Familiarity with NP-Completeness, reductions • Basic number theory (modular arithmetic, etc) Reading No required text Computer Science/Mathematics Chapman & Hall/CRC If you want a text to follow along with: Second CRYPTOGRAPHY AND NETWORK SECURITY Cryptography is ubiquitous and plays a key role in ensuring data secrecy and Edition integrity as well as in securing computer systems more broadly. -

41760779079990.Pdf
.CONFIS~Ti;~691 BBS'l'RIOHJB· THE DISTBIBUTION OF THIS SPECIAL TEXT WILL BE RESTRICTED TO REGULARLY ENROLLED EXTENSION COURSE STUDENTS, 'l'O MILITARY PERSONNEL, AND TO OTHER PERSONS COMING WITHIN THE MEANING OF THE PHRASE "FOR OFFICIAL USE ONLY/, ·. ARMY EXTENSION COURSES ~,· ·~~cY-l~~ I!LA)f'~'~ ~ \_ -·----------;-- --·· SPECIAL TEXT No. 166 ADVANCED MILITARY CRYPTOGRAPHY Szcoxn (19'3) EDmox PREPARED UNDER THE DIRECTION OF THE CHIEF SIGNAL OFFICER FOR USE WITH 'I1fE ARMY EXTENSION COURSES .',; ,_ • RSS'fRI<ffRB document contains information affecting the nat1 defense of the United States within the meaning of die · nage Act (U.S. C. -Y,. ~:>· 50: 31, 32). The transmission o · ocument · · or the revelation of its contents in any nl:an any unauthorized person is prohibited. + UNITED STATES GOVERNMENT PRINTING OFFICE ~ (o ~ ~ WASHINGTON : 19'3 . ,. 7.~0NFIDENTIAL Peclassified and approved for release by NSA on 01-14-2014 pursuant to E.O. 1352§ REF ID:A64691 ,·J/ 30 April 1959 Th.is document is re-graded "eEm'!BBrff " of DOD Directive 5200.l dated 8 ~ UP and by autharity of the Directar '2t1:.!i Security ~ncy. ' Paul~w~ S. Willard Colonel, AOC Adjutant Ge.nera.J. • ~· WAR DEPARTMENT, • WAsmNGTON, Februa1"JI S, 1948. Tbis revision of Special Text No. 166, Advanced Milita.ry Cryptog raphy (1935), for use with the Anny Extension Courses, is published for the information and guidance of all concerned. BY ORDEB OF THE SlilCBlilTAB.Y OF wAB! :,. G. o. M.ARSHAT,T., General, Ohiejoj8f4. OFFICIAL! JAMES A. ULIO, Major Gemral, 7?i.e Adjut,ant Geneml,. (XI) • SPECIAL TEXT NO. -

Battle Management Language: History, Employment and NATO Technical Activities
Battle Management Language: History, Employment and NATO Technical Activities Mr. Kevin Galvin Quintec Mountbatten House, Basing View, Basingstoke Hampshire, RG21 4HJ UNITED KINGDOM [email protected] ABSTRACT This paper is one of a coordinated set prepared for a NATO Modelling and Simulation Group Lecture Series in Command and Control – Simulation Interoperability (C2SIM). This paper provides an introduction to the concept and historical use and employment of Battle Management Language as they have developed, and the technical activities that were started to achieve interoperability between digitised command and control and simulation systems. 1.0 INTRODUCTION This paper provides a background to the historical employment and implementation of Battle Management Languages (BML) and the challenges that face the military forces today as they deploy digitised C2 systems and have increasingly used simulation tools to both stimulate the training of commanders and their staffs at all echelons of command. The specific areas covered within this section include the following: • The current problem space. • Historical background to the development and employment of Battle Management Languages (BML) as technology evolved to communicate within military organisations. • The challenges that NATO and nations face in C2SIM interoperation. • Strategy and Policy Statements on interoperability between C2 and simulation systems. • NATO technical activities that have been instigated to examine C2Sim interoperation. 2.0 CURRENT PROBLEM SPACE “Linking sensors, decision makers and weapon systems so that information can be translated into synchronised and overwhelming military effect at optimum tempo” (Lt Gen Sir Robert Fulton, Deputy Chief of Defence Staff, 29th May 2002) Although General Fulton made that statement in 2002 at a time when the concept of network enabled operations was being formulated by the UK and within other nations, the requirement remains extant. -

Cryptography: Decoding Student Learning
ABSTRACT PATTERSON, BLAIN ANTHONY. Cryptography: Decoding Student Learning. (Under the direction of Karen Keene.) Cryptography is a content field of mathematics and computer science, developed to keep information safe both when being sent between parties and stored. In addition to this, cryptography can also be used as a powerful teaching tool, as it puts mathematics in a dramatic and realistic setting. It also allows for a natural way to introduce topics such as modular arithmetic, matrix operations, and elementary group theory. This thesis reports the results of an analysis of students' thinking and understanding of cryptog- raphy using both the SOLO taxonomy and open coding as they participated in task based interviews. Students interviewed were assessed on how they made connections to various areas of mathematics through solving cryptography problems. Analyzing these interviews showed that students have a strong foundation in number theoretic concepts such as divisibility and modular arithmetic. Also, students were able to use probabil- ity intuitively to make sense of and solve problems. Finally, participants' SOLO levels ranged from Uni-structural to Extended Abstract, with Multi-Structural level being the most common (three participants). This gives evidence to suggest that students should be given the opportunity to make mathematical connections early and often in their academic careers. Results indicate that although cryptography should not be a required course by mathematics majors, concepts from this field could be introduced -

Cryptographyorhioohulmuoft CRYPTOGRAPHY OR the HISTORY, PRINCIPLES, and PRACTICE of CIPHER-WRITING
Digitized by the Internet Archive in 2007 with funding from IVIicrosoft Corporation http://www.archive.org/details/cryptographyorhiOOhulmuoft CRYPTOGRAPHY OR THE HISTORY, PRINCIPLES, AND PRACTICE OF CIPHER-WRITING ^ w >TOGRA OR The History, Principles, and Practice OF CIPHER-WRITING e<^ BY Fl^EDWARD HULME, F.L.S., F.S.A U\ AUTHOR OF "familiar WILD FLOWERS," " MYTHLAND," " NATURAL HISTORY LORE AND LEGEND," "the birth and development OF ORNAMENT," " WAYSIDK SKETCHES," ETC Heres noiv mystery and hieroglyphic Ben Jonson— The Alchemysi. LONDON WARWICK HOUSE, SALISBURY SQUARE, E.C NEW YORK AND MELBOURNE — CONTENTS CHAPTER I PAGE Meaning of cryptography—Objections to its study—Its legitimate use and value—Historic examples of its employment—Deliglit in the mysterious—Many other ways of conveying secret information—Symbolism of action—The spoken word imprisoned and dispatched —A matter not necessarily secret because one cannot understand it — Egyptian hieroglypliics — Chinese characters—Indian mutiny Greek—Ancient Biblical cryptogram — Sheshach of Jeremiah — Sir Henry Eawlinson thereon—Statements for and against Julius Caesar's secret code—The waxed tablet of Demaratus—Difference between hidden and secret writing—The shaven head a writing tablet—Charle- magne and Alfred the Great as cryptographic experts —Mediaeval authorities—Trithemius the Benedictine " — " Steganographia —Dabbling in the black art Dr. Dee—Batista Porta's book on "Natural Majick" —Invisible writing—Chemical methods by vitriol, alum, etc. —Writing on glass or crystal—Papal In- quisition—Disappearing writing—Messages wrapped round rollers—Two methods—A slave's back the writing surface—Chemical methods of no great value ordinarily—Disadvantages of use— Action of light and heat—Chloride of cobalt, sulphate of copper, etc. -
Block Ciphers
BLOCK CIPHERS MTH 440 Block ciphers • Plaintext is divided into blocks of a given length and turned into output ciphertext blocks of the same length • Suppose you had a block cipher, E(x,k) where the input plaintext blocks,x, were of size 5-bits and a 4-bit key, k. • PT = 10100010101100101 (17 bits), “Pad” the PT so that its length is a multiple of 5 (we will just pad with 0’s – it doesn’t really matter) • PT = 10100010101100101000 • Break the PT into blocks of 5-bits each (x=x1x2x3x4) where each xi is 5 bits) • x1=10100, x2= 01010, x3=11001, x4=01000 • Ciphertext: c1c2c3c4 where • c1=E(x1,k1), c2=E(x2,k2), c3=E(x3,k3), c4=E(x4,k4) • (when I write the blocks next to each other I just mean concatentate them (not multiply) – we’ll do this instead of using the || notation when it is not confusing) • Note the keys might all be the same or all different What do the E’s look like? • If y = E(x,k) then we’ll assume that we can decipher to a unique output so there is some function, we’ll call it D, so that x = D(y,k) • We might define our cipher to be repeated applications of some function E either with the same or different keys, we call each of these applications “round” • For example we might have a “3 round” cipher: y Fk x E((() E E x, k1 , k 2)), k 3 • We would then decipher via 1 x Fk (,, y) D((() D D y, k3 k 2) k 1) S-boxes (Substitution boxes) • Sometimes the “functions” used in the ciphers are just defined by a look up table that are often referred to “S- boxes” •x1 x 2 x 3 S(x 1 x 2 x 3 ) Define a 4-bit function with a 3-bit key 000 -

Enigma Cryptanalysis - Beginnings
Enigma Cryptanalysis - Beginnings Gaurish Korpal∗ [email protected] July 15, 2015 Abstract Any message may be hidden in two basic ways. The methods of steganography conceal the very existence of the message, for example invisible inks and microdots. The methods of cryptography, on the other hand, do not conceal the presence of a secret message but render it unintelligible as ciphertext, to outsiders by various transformations of the plaintext. Breaking ciphers require ingenuity, creativity and a little math. In this article our focus will be on breaking Enigma ciphers. The skill involved in breaking ciphers is called cryptanalysis. Keywords. Enigma, cryptanalysis, cypher, Caesar, Vigen`ere,Rejewski, Zygalski, Bomba, Bombe 1 Cipher not Code A code is a mapping from some meaningful unit (word, sentence, phrase) into something else (usually a shorter group of symbols). A code requires a codebook, it is simply a list of these mappings. For example we could make up a code where the word Apple is written as 67, historical example of this is \Zimmermann Telegram Code" for more details refer [7]. Ciphers do not involve meaning. Instead they are mechanical operations (known as algorithms) which are performed on the individual or small chunks of letters. A code is stored as a mapping in a codebook, while ciphers transform individual symbols according to an algorithm. It was definitively stated in 1883 by the Dutch linguist Auguste Kerckhoffs von Nieuwenhof in his book La Cryptographie militaire: Kerckhoffs' Principle: The security of a cryptosystem must not depend on keeping secret the crypto-algorithm. The security depends only on keeping secret the key. -

Ciphers: Making and Breaking Ralph Morelli Trinity College, Hartford ([email protected])
Ciphers: Making and Breaking Ralph Morelli Trinity College, Hartford ([email protected]) Smithsonian Institute October 31, 2009 © 2009 Ralph Morelli You are free to reuse and remix this presentation under a creative commons license provided you give credit to the author. http://creativecommons.org/licenses/by/3.0/us/ This presentation was created using Open Office 3.0, free and open source software. http://www.openoffice.org/ Today's Themes • Crypto Cat vs. Mouse: Cryptographer vs. Cryptanalyst • Theoretical security vs. practical security • Implementation, implementation, implementation • The key is security. Part I: Classical Cryptology Basic Terminology Secret Writing Cryptography – making secret messages. Cryptanalysis – breaking secret messages. Cryptology – cryptography and cryptanalysis. Steganography – concealing messages. Cipher Cipher – a method for transforming a message. encipher meet me at six Cipher mmseeieaxtt plaintext ciphertext decipher Code Code – a system in which codewords replace plaintext words or symbols using a codebook. Codebook meet ... 149 me at at 15 146 15 652 six … … me 146 meet 149 … six 652 Types of Cipher Transposition hello Cipher ELOLH (rearrange) 23541 Substitution KHOOR hello Cipher (replace) Plaintext alphabet: a b c d e f g h i j k l m n o p q r s t u v w x y z Cipher alphabet: D E F G H I J K L M N O P Q R S T U V W X Y Z A B C Earliest Ciphers Herodotus (484-425 B.C.) Persian War (~480 BC), Demaratus' secret message to the Spartans was hidden under the wax on a wooden tablet (steganography). -

Introduction
ON SOME KNOWN POSSIBLE APPLICATIONS OF QUASIGROUPS IN CRYPTOLOGY Victor Shcherbacov Abstract. It is surveyed known (published) possible application of binary and n-ary quasigroups in cryptology. Mathematics Subject Classification: 20N05, 94A60. Key words and phrases: Cryptology, cryptography, cipher, key, quasigroup, n-ary quasigroup. Introduction Almost all results obtained in branch of application of quasigroups in cryptology and coding theory to the end of eighties years of the XX-th century are described in [20, 21]. In the present survey the main attention is devoted more late articles in this direction. Basic facts on quasigroup theory it is possible to find in [5, 6, 7, 64]. Information on basic fact in cryptology it is possible to find in many books see, for example, [3, 11, 60, 54]. Cryptology is a science that consists form two parts: cryptography and cryptanalysis. Cryp- tography is a science on methods of transformation (ciphering) of information with the purpose of a protection this information from an unlawful user. Cryptanalysis is a science on methods and ways of breaking down of ciphers ([32]). In some sense cryptography is a \defense", i.e. this is a science on construction of new ciphers, but cryptanalysis is an \attack", i.e. this is a science and some kind \art", a set of methods on breaking of ciphers. This situation is similar to situation with intelligence and contr-intelligence. These two objects (cryptography and cryptanalysis) are very closed and there does not exist a good cryptographer that do not know methods of cryptanalysis. It is clear, that cryptology depends from a level of development of a society and a level of development of technology. -
Cryptology: an Historical Introduction DRAFT
Cryptology: An Historical Introduction DRAFT Jim Sauerberg February 5, 2013 2 Copyright 2013 All rights reserved Jim Sauerberg Saint Mary's College Contents List of Figures 8 1 Caesar Ciphers 9 1.1 Saint Cyr Slide . 12 1.2 Running Down the Alphabet . 14 1.3 Frequency Analysis . 15 1.4 Linquist's Method . 20 1.5 Summary . 22 1.6 Topics and Techniques . 22 1.7 Exercises . 23 2 Cryptologic Terms 29 3 The Introduction of Numbers 31 3.1 The Remainder Operator . 33 3.2 Modular Arithmetic . 38 3.3 Decimation Ciphers . 40 3.4 Deciphering Decimation Ciphers . 42 3.5 Multiplication vs. Addition . 44 3.6 Koblitz's Kid-RSA and Public Key Codes . 44 3.7 Summary . 48 3.8 Topics and Techniques . 48 3.9 Exercises . 49 4 The Euclidean Algorithm 55 4.1 Linear Ciphers . 55 4.2 GCD's and the Euclidean Algorithm . 56 4.3 Multiplicative Inverses . 59 4.4 Deciphering Decimation and Linear Ciphers . 63 4.5 Breaking Decimation and Linear Ciphers . 65 4.6 Summary . 67 4.7 Topics and Techniques . 67 4.8 Exercises . 68 3 4 CONTENTS 5 Monoalphabetic Ciphers 71 5.1 Keyword Ciphers . 72 5.2 Keyword Mixed Ciphers . 73 5.3 Keyword Transposed Ciphers . 74 5.4 Interrupted Keyword Ciphers . 75 5.5 Frequency Counts and Exhaustion . 76 5.6 Basic Letter Characteristics . 77 5.7 Aristocrats . 78 5.8 Summary . 80 5.9 Topics and Techniques . 81 5.10 Exercises . 81 6 Decrypting Monoalphabetic Ciphers 89 6.1 Letter Interactions . 90 6.2 Decrypting Monoalphabetic Ciphers . -
A Brief History of Cryptography
University of Tennessee, Knoxville TRACE: Tennessee Research and Creative Exchange Supervised Undergraduate Student Research Chancellor’s Honors Program Projects and Creative Work Spring 5-2000 A Brief History of Cryptography William August Kotas University of Tennessee - Knoxville Follow this and additional works at: https://trace.tennessee.edu/utk_chanhonoproj Recommended Citation Kotas, William August, "A Brief History of Cryptography" (2000). Chancellor’s Honors Program Projects. https://trace.tennessee.edu/utk_chanhonoproj/398 This is brought to you for free and open access by the Supervised Undergraduate Student Research and Creative Work at TRACE: Tennessee Research and Creative Exchange. It has been accepted for inclusion in Chancellor’s Honors Program Projects by an authorized administrator of TRACE: Tennessee Research and Creative Exchange. For more information, please contact [email protected]. Appendix D- UNIVERSITY HONORS PROGRAM SENIOR PROJECT - APPROVAL Name: __ l1~Ui~-~-- A~5-~~± ---l(cl~-~ ---------------------- ColI e g e: _l~.:i~_~__ ~.:--...!j:.~~~ __ 0 epa r t men t: _ {~~.f_':.~::__ ~,:::..!._~_~_s,_ Fa c u 1ty Me n tor: ____Q-' _·__ ~~~~s..0_~_L __ D_~_ ~_o_~t _______________ _ PRO JE CT TITL E: ____~ __ ~c ~ :.f __ l1L~_ ~_I_x __ 9_( __( ~~- ~.t~~-.r--~~ - I have reviewed this completed senior honors thesis "\lith this student and certifv that it is a project commensurate with honors level undergraduate research in this field. Signed ~u:t2~--------------- , Facultv .'vfentor Date: --d~I-~--Q-------- Comments (Optional): A BRIEF HISTORY OF CRYPTOGRAPHY Prepared by William A. Kotas For Honors Students at the University of Tennessee May 5, 2000 ABSTRACT This paper presents an abbreviated history of cryptography.