Block Ciphers
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
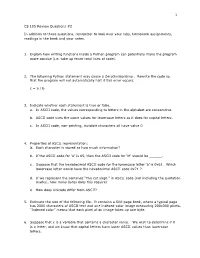
CS 105 Review Questions #2 in Addition to These Questions
1 CS 105 Review Questions #2 In addition to these questions, remember to look over your labs, homework assignments, readings in the book and your notes. 1. Explain how writing functions inside a Python program can potentially make the program more concise (i.e. take up fewer total lines of code). 2. The following Python statement may cause a ZeroDivisionError. Rewrite the code so that the program will not automatically halt if this error occurs. c = a / b 3. Indicate whether each statement is true or false. a. In ASCII code, the values corresponding to letters in the alphabet are consecutive. b. ASCII code uses the same values for lowercase letters as it does for capital letters. c. In ASCII code, non-printing, invisible characters all have value 0 4. Properties of ASCII representation: a. Each character is stored as how much information? b. If the ASCII code for ‘A’ is 65, then the ASCII code for ‘M’ should be ______. c. Suppose that the hexadecimal ASCII code for the lowercase letter ‘a’ is 0x61. Which lowercase letter would have the hexadecimal ASCII code 0x71 ? d. If we represent the sentence “The cat slept.” in ASCII code (not including the quotation marks), how many bytes does this require? e. How does Unicode differ from ASCII? 5. Estimate the size of the following file. It contains a 500-page book, where a typical page has 2000 characters of ASCII text and one indexed-color image measuring 200x300 pixels. “Indexed color” means that each pixel of an image takes up one byte. -

Block Ciphers and the Data Encryption Standard
Lecture 3: Block Ciphers and the Data Encryption Standard Lecture Notes on “Computer and Network Security” by Avi Kak ([email protected]) January 26, 2021 3:43pm ©2021 Avinash Kak, Purdue University Goals: To introduce the notion of a block cipher in the modern context. To talk about the infeasibility of ideal block ciphers To introduce the notion of the Feistel Cipher Structure To go over DES, the Data Encryption Standard To illustrate important DES steps with Python and Perl code CONTENTS Section Title Page 3.1 Ideal Block Cipher 3 3.1.1 Size of the Encryption Key for the Ideal Block Cipher 6 3.2 The Feistel Structure for Block Ciphers 7 3.2.1 Mathematical Description of Each Round in the 10 Feistel Structure 3.2.2 Decryption in Ciphers Based on the Feistel Structure 12 3.3 DES: The Data Encryption Standard 16 3.3.1 One Round of Processing in DES 18 3.3.2 The S-Box for the Substitution Step in Each Round 22 3.3.3 The Substitution Tables 26 3.3.4 The P-Box Permutation in the Feistel Function 33 3.3.5 The DES Key Schedule: Generating the Round Keys 35 3.3.6 Initial Permutation of the Encryption Key 38 3.3.7 Contraction-Permutation that Generates the 48-Bit 42 Round Key from the 56-Bit Key 3.4 What Makes DES a Strong Cipher (to the 46 Extent It is a Strong Cipher) 3.5 Homework Problems 48 2 Computer and Network Security by Avi Kak Lecture 3 Back to TOC 3.1 IDEAL BLOCK CIPHER In a modern block cipher (but still using a classical encryption method), we replace a block of N bits from the plaintext with a block of N bits from the ciphertext. -

COS433/Math 473: Cryptography Mark Zhandry Princeton University Spring 2017 Cryptography Is Everywhere a Long & Rich History
COS433/Math 473: Cryptography Mark Zhandry Princeton University Spring 2017 Cryptography Is Everywhere A Long & Rich History Examples: • ~50 B.C. – Caesar Cipher • 1587 – Babington Plot • WWI – Zimmermann Telegram • WWII – Enigma • 1976/77 – Public Key Cryptography • 1990’s – Widespread adoption on the Internet Increasingly Important COS 433 Practice Theory Inherent to the study of crypto • Working knowledge of fundamentals is crucial • Cannot discern security by experimentation • Proofs, reductions, probability are necessary COS 433 What you should expect to learn: • Foundations and principles of modern cryptography • Core building blocks • Applications Bonus: • Debunking some Hollywood crypto • Better understanding of crypto news COS 433 What you will not learn: • Hacking • Crypto implementations • How to design secure systems • Viruses, worms, buffer overflows, etc Administrivia Course Information Instructor: Mark Zhandry (mzhandry@p) TA: Fermi Ma (fermima1@g) Lectures: MW 1:30-2:50pm Webpage: cs.princeton.edu/~mzhandry/2017-Spring-COS433/ Office Hours: please fill out Doodle poll Piazza piaZZa.com/princeton/spring2017/cos433mat473_s2017 Main channel of communication • Course announcements • Discuss homework problems with other students • Find study groups • Ask content questions to instructors, other students Prerequisites • Ability to read and write mathematical proofs • Familiarity with algorithms, analyZing running time, proving correctness, O notation • Basic probability (random variables, expectation) Helpful: • Familiarity with NP-Completeness, reductions • Basic number theory (modular arithmetic, etc) Reading No required text Computer Science/Mathematics Chapman & Hall/CRC If you want a text to follow along with: Second CRYPTOGRAPHY AND NETWORK SECURITY Cryptography is ubiquitous and plays a key role in ensuring data secrecy and Edition integrity as well as in securing computer systems more broadly. -

Block Ciphers
Block Ciphers Chester Rebeiro IIT Madras CR STINSON : chapters 3 Block Cipher KE KD untrusted communication link Alice E D Bob #%AR3Xf34^$ “Attack at Dawn!!” message encryption (ciphertext) decryption “Attack at Dawn!!” Encryption key is the same as the decryption key (KE = K D) CR 2 Block Cipher : Encryption Key Length Secret Key Plaintext Ciphertext Block Cipher (Encryption) Block Length • A block cipher encryption algorithm encrypts n bits of plaintext at a time • May need to pad the plaintext if necessary • y = ek(x) CR 3 Block Cipher : Decryption Key Length Secret Key Ciphertext Plaintext Block Cipher (Decryption) Block Length • A block cipher decryption algorithm recovers the plaintext from the ciphertext. • x = dk(y) CR 4 Inside the Block Cipher PlaintextBlock (an iterative cipher) Key Whitening Round 1 key1 Round 2 key2 Round 3 key3 Round n keyn Ciphertext Block • Each round has the same endomorphic cryptosystem, which takes a key and produces an intermediate ouput • Size of the key is huge… much larger than the block size. CR 5 Inside the Block Cipher (the key schedule) PlaintextBlock Secret Key Key Whitening Round 1 Round Key 1 Round 2 Round Key 2 Round 3 Round Key 3 Key Expansion Expansion Key Key Round n Round Key n Ciphertext Block • A single secret key of fixed size used to generate ‘round keys’ for each round CR 6 Inside the Round Function Round Input • Add Round key : Add Round Key Mixing operation between the round input and the round key. typically, an ex-or operation Confusion Layer • Confusion layer : Makes the relationship between round Diffusion Layer input and output complex. -

GCM) for Confidentiality And
NIST Special Publication 800-38D Recommendation for Block DRAFT (April, 2006) Cipher Modes of Operation: Galois/Counter Mode (GCM) for Confidentiality and Authentication Morris Dworkin C O M P U T E R S E C U R I T Y Abstract This Recommendation specifies the Galois/Counter Mode (GCM), an authenticated encryption mode of operation for a symmetric key block cipher. KEY WORDS: authentication; block cipher; cryptography; information security; integrity; message authentication code; mode of operation. i Table of Contents 1 PURPOSE...........................................................................................................................................................1 2 AUTHORITY.....................................................................................................................................................1 3 INTRODUCTION..............................................................................................................................................1 4 DEFINITIONS, ABBREVIATIONS, AND SYMBOLS.................................................................................2 4.1 DEFINITIONS AND ABBREVIATIONS .............................................................................................................2 4.2 SYMBOLS ....................................................................................................................................................4 4.2.1 Variables................................................................................................................................................4 -

KLEIN: a New Family of Lightweight Block Ciphers
KLEIN: A New Family of Lightweight Block Ciphers Zheng Gong1, Svetla Nikova1;2 and Yee Wei Law3 1Faculty of EWI, University of Twente, The Netherlands fz.gong, [email protected] 2 Dept. ESAT/SCD-COSIC, Katholieke Universiteit Leuven, Belgium 3 Department of EEE, The University of Melbourne, Australia [email protected] Abstract Resource-efficient cryptographic primitives become fundamental for realizing both security and efficiency in embedded systems like RFID tags and sensor nodes. Among those primitives, lightweight block cipher plays a major role as a building block for security protocols. In this paper, we describe a new family of lightweight block ciphers named KLEIN, which is designed for resource-constrained devices such as wireless sensors and RFID tags. Compared to the related proposals, KLEIN has ad- vantage in the software performance on legacy sensor platforms, while its hardware implementation can be compact as well. Key words. Block cipher, Wireless sensor network, Low-resource implementation. 1 Introduction With the development of wireless communication and embedded systems, we become increasingly de- pendent on the so called pervasive computing; examples are smart cards, RFID tags, and sensor nodes that are used for public transport, pay TV systems, smart electricity meters, anti-counterfeiting, etc. Among those applications, wireless sensor networks (WSNs) have attracted more and more attention since their promising applications, such as environment monitoring, military scouting and healthcare. On resource-limited devices the choice of security algorithms should be very careful by consideration of the implementation costs. Symmetric-key algorithms, especially block ciphers, still play an important role for the security of the embedded systems. -

Mirror Cipher Using Feistel Network
Mirror Cipher using Feistel Network 1 2 3 Ihsan Muhammad Asnadi Ranindya Paramitha Tony 123 Informatics Department, Institut Teknologi Bandung, Bandung 40132, Indonesia 1 2 3 E-mail: 1 [email protected] 1 [email protected] 1 [email protected] Abstract. Mirror cipher is a cipher built by creativity which has a specific feature of mirrored round function. As other ciphers, mirror cipher could be used to secure messages’ confidentiality and integrity. This cipher receives message and key inputs from its user. Then, it runs 9 rounds of feistel networks in ECB modes. Each round would run a round function which consists of 5 functions in mirrored order (9 function calls in total): s-box substitution, row substitution, column substitution, column cumulative xor, and round key addition. This cipher is implemented using Python and has been tested using several message and key combinations. Mirror cipher has applied Shanon’s diffusion and confusion property and proven to be secured from bruteforce and frequency analysis attack. 1. Introduction 1.1. Background In this modern world, data or messages are exchanged anytime and anywhere. To protect confidentiality and integrity of messages, people usually encrypt their messages before sending them, and then decrypt the received messages before reading them. These encryption and decryption practices and techniques are contained under the big concept of cryptography. There are many ciphers (encryption and decryption algorithms) that have been developed since the BC period. Ciphers are then divided into 2 kinds of ciphers, based on how it treats the message: stream cipher and block cipher. -

Battle Management Language: History, Employment and NATO Technical Activities
Battle Management Language: History, Employment and NATO Technical Activities Mr. Kevin Galvin Quintec Mountbatten House, Basing View, Basingstoke Hampshire, RG21 4HJ UNITED KINGDOM [email protected] ABSTRACT This paper is one of a coordinated set prepared for a NATO Modelling and Simulation Group Lecture Series in Command and Control – Simulation Interoperability (C2SIM). This paper provides an introduction to the concept and historical use and employment of Battle Management Language as they have developed, and the technical activities that were started to achieve interoperability between digitised command and control and simulation systems. 1.0 INTRODUCTION This paper provides a background to the historical employment and implementation of Battle Management Languages (BML) and the challenges that face the military forces today as they deploy digitised C2 systems and have increasingly used simulation tools to both stimulate the training of commanders and their staffs at all echelons of command. The specific areas covered within this section include the following: • The current problem space. • Historical background to the development and employment of Battle Management Languages (BML) as technology evolved to communicate within military organisations. • The challenges that NATO and nations face in C2SIM interoperation. • Strategy and Policy Statements on interoperability between C2 and simulation systems. • NATO technical activities that have been instigated to examine C2Sim interoperation. 2.0 CURRENT PROBLEM SPACE “Linking sensors, decision makers and weapon systems so that information can be translated into synchronised and overwhelming military effect at optimum tempo” (Lt Gen Sir Robert Fulton, Deputy Chief of Defence Staff, 29th May 2002) Although General Fulton made that statement in 2002 at a time when the concept of network enabled operations was being formulated by the UK and within other nations, the requirement remains extant. -

Chapter 3 – Block Ciphers and the Data Encryption Standard
Symmetric Cryptography Chapter 6 Block vs Stream Ciphers • Block ciphers process messages into blocks, each of which is then en/decrypted – Like a substitution on very big characters • 64-bits or more • Stream ciphers process messages a bit or byte at a time when en/decrypting – Many current ciphers are block ciphers • Better analyzed. • Broader range of applications. Block vs Stream Ciphers Block Cipher Principles • Block ciphers look like an extremely large substitution • Would need table of 264 entries for a 64-bit block • Arbitrary reversible substitution cipher for a large block size is not practical – 64-bit general substitution block cipher, key size 264! • Most symmetric block ciphers are based on a Feistel Cipher Structure • Needed since must be able to decrypt ciphertext to recover messages efficiently Ideal Block Cipher Substitution-Permutation Ciphers • in 1949 Shannon introduced idea of substitution- permutation (S-P) networks – modern substitution-transposition product cipher • These form the basis of modern block ciphers • S-P networks are based on the two primitive cryptographic operations we have seen before: – substitution (S-box) – permutation (P-box) (transposition) • Provide confusion and diffusion of message Diffusion and Confusion • Introduced by Claude Shannon to thwart cryptanalysis based on statistical analysis – Assume the attacker has some knowledge of the statistical characteristics of the plaintext • Cipher needs to completely obscure statistical properties of original message • A one-time pad does this Diffusion -

A Novel Feistel Cipher Involving a Bunch of Keys Supplemented with XOR Operation
(IJACSA) International Journal of Advanced Computer Science and Applications, Vol. 3, No. 12, 2012 A Novel Feistel Cipher Involving a Bunch of Keys Supplemented with XOR Operation V.U.K Sastry K. Anup Kumar Dean R&D, Department of Computer Science and Associate Professor, Department of Computer Science Engineering, Sreenidhi Institute of Science & Tech. and Engineering, SNIST, Hyderabad, India Hyderabad, India Abstract—In this investigation, we have developed a novel block In order to satisfy (1.5), we chose ejk as an odd integer, cipher by modifying classical Feistel cipher. In this, we have used which lies in the interval [1-255], and thus we obtain djk also as a key bunched wherein each key has a multiplicative inverse. The an odd integer lying in the interval [1-255]. cryptanalysis carried out in this investigation clearly shows that this cipher cannot be broken by any attack. Here also we adopt an iterative procedure, and make use of the permutation process that consists of the interchange of the Keywords-encryption; decryption; cryptanalysis; avalanche effect; two halves of the plaintext , of course, represented in the form multiplicative inverse. of a pair of matrices. I. INTRODUCTION In the present analysis, our objective is to modify the Feistel cipher by including a bunch of keys. Here our interest is The study of the Feistel cipher [1-2] laid the foundation for to see how the different keys, occurring in the key bunch, the development of cryptography in the seventies of the last would influence the strength of the cipher. century. In the classical Feistel cipher the block size is 64 bits, and it is divided into two halves wherein each half is containing In what follows, we present the plan of the paper. -

Cryptography: Decoding Student Learning
ABSTRACT PATTERSON, BLAIN ANTHONY. Cryptography: Decoding Student Learning. (Under the direction of Karen Keene.) Cryptography is a content field of mathematics and computer science, developed to keep information safe both when being sent between parties and stored. In addition to this, cryptography can also be used as a powerful teaching tool, as it puts mathematics in a dramatic and realistic setting. It also allows for a natural way to introduce topics such as modular arithmetic, matrix operations, and elementary group theory. This thesis reports the results of an analysis of students' thinking and understanding of cryptog- raphy using both the SOLO taxonomy and open coding as they participated in task based interviews. Students interviewed were assessed on how they made connections to various areas of mathematics through solving cryptography problems. Analyzing these interviews showed that students have a strong foundation in number theoretic concepts such as divisibility and modular arithmetic. Also, students were able to use probabil- ity intuitively to make sense of and solve problems. Finally, participants' SOLO levels ranged from Uni-structural to Extended Abstract, with Multi-Structural level being the most common (three participants). This gives evidence to suggest that students should be given the opportunity to make mathematical connections early and often in their academic careers. Results indicate that although cryptography should not be a required course by mathematics majors, concepts from this field could be introduced -

A Block Cipher Algorithm to Enhance the Avalanche Effect Using Dynamic Key- Dependent S-Box and Genetic Operations 1Balajee Maram and 2J.M
International Journal of Pure and Applied Mathematics Volume 119 No. 10 2018, 399-418 ISSN: 1311-8080 (printed version); ISSN: 1314-3395 (on-line version) url: http://www.ijpam.eu Special Issue ijpam.eu A Block Cipher Algorithm to Enhance the Avalanche Effect Using Dynamic Key- Dependent S-Box and Genetic Operations 1Balajee Maram and 2J.M. Gnanasekar 1Department of CSE, GMRIT, Rajam, India. Research and Development Centre, Bharathiar University, Coimbatore. [email protected] 2Department of Computer Science & Engineering, Sri Venkateswara College of Engineering, Sriperumbudur Tamil Nadu. [email protected] Abstract In digital data security, an encryption technique plays a vital role to convert digital data into intelligible form. In this paper, a light-weight S- box is generated that depends on Pseudo-Random-Number-Generators. According to shared-secret-key, all the Pseudo-Random-Numbers are scrambled and input to the S-box. The complexity of S-box generation is very simple. Here the plain-text is encrypted using Genetic Operations and S-box which is generated based on shared-secret-key. The proposed algorithm is experimentally investigates the complexity, quality and performance using the S-box parameters which includes Hamming Distance, Balanced Output and the characteristic of cryptography is Avalanche Effect. Finally the comparison results motivates that the dynamic key-dependent S-box has good quality and performance than existing algorithms. 399 International Journal of Pure and Applied Mathematics Special Issue Index Terms:S-BOX, data security, random number, cryptography, genetic operations. 400 International Journal of Pure and Applied Mathematics Special Issue 1. Introduction In public network, several types of attacks1 can be avoided by applying Data Encryption/Decryption2.